Linux 防火墙相关命令
防火墙规则
[root@centos7 ~] systemctl start firewalld
[root@centos7 ~] systemctl stopfirewalld
[root@centos7 ~] systemctl status firewalld


- 加载,在做防火墙添加/删除/指定IP(端口)之后需要重新加载,提示success即为成功
[root@centos7 ~] firewall-cmd --reload
[root@centos7 ~] firewall-cmd --list-all

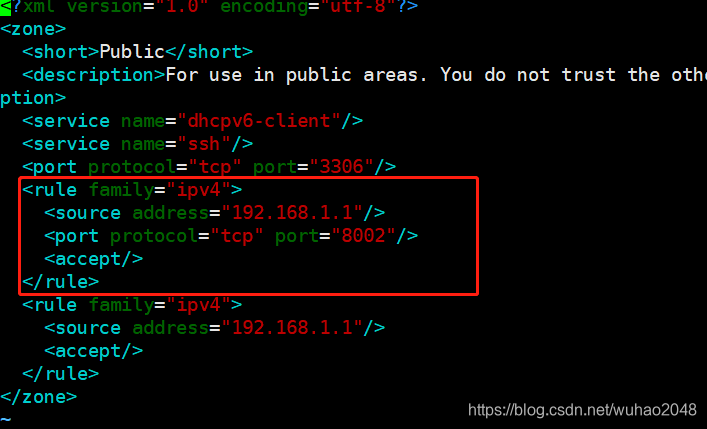
[root@centos7 ~] vim /etc/firewalld/zones/public.xml

[root@centos7 ~] firewall-cmd --zone=public --add-port=3306/tcp --permanent
success
[root@centos7 ~] firewall-cmd --reload

[root@centos7 ~] firewall-cmd --zone=public --remove-port=445/tcp --permanent
[root@centos7 ~] firewall-cmd --zone=public --permanent --add-rich-rule='rule family="ipv4" source address="192.168.1.1" accept'

[root@centos7 ~] firewall-cmd --zone=public --permanent --add-rich-rule='rule family="ipv4" source address="192.168.1.1" port protocol="tcp" port="8002" accept'```
- **禁止IP访问所有的端口**
```bash
[root@centos7 ~] firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.1.1/0" reject"

[root@centos7 ~] firewall-cmd --zone=public --permanent --add-rich-rule='rule family="ipv4" source address="192.168.1.1" port protocol="tcp" port="8002" reject'

- 抓包分析
服务器防火墙禁用80端口,用客户端使用http访问80端口,服务器上抓包如下。依然有访问的包,但会回复包不可达。






























 7643
7643











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








