目录
表(TABLE)里链(CHAIN)中规则(RULE)增删改查
规则(RULE=MATCH+TARGET+TARGET_OPTIONS)
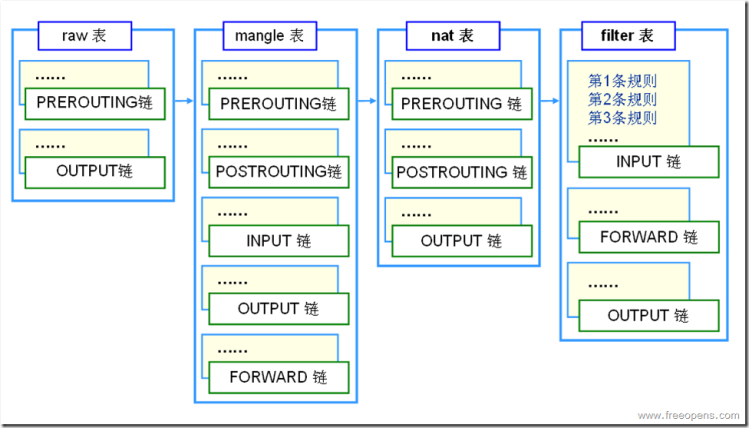
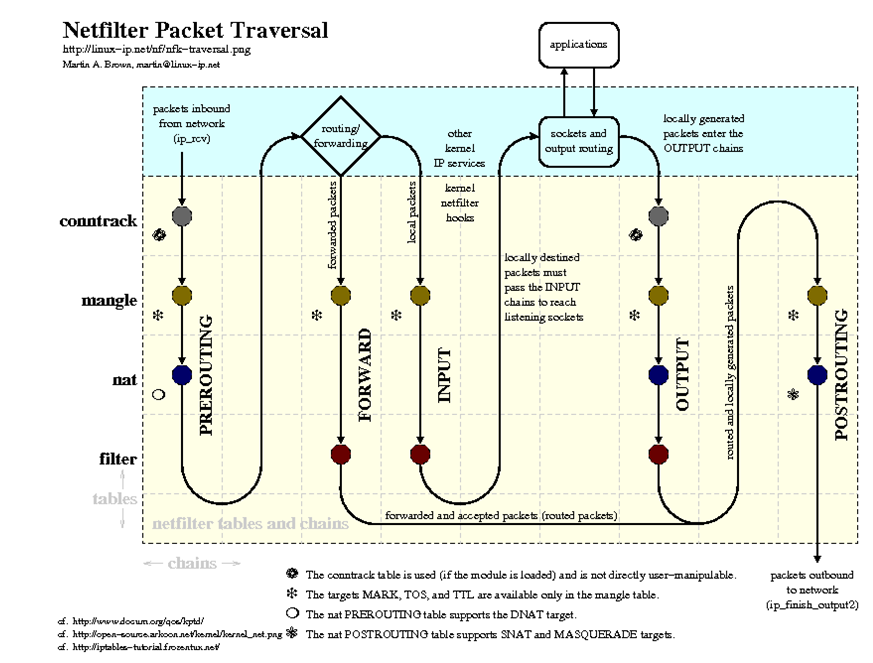
表匹配顺序 :raw->mangle->nat->filter
direction: src, dst, src or dst, src and dst, ra, ta, addr1, addr2, addr3, addr4
proto: ether, wlan, ip ip6, arp, rarp, sctp, tcp, udp
linux中的ip命令
linux中各种网络管理命令,如ifconfig, brctl route等,其中ip命令涵盖了所有功能。ip(8) - Linux manual page
man手册里非常清楚的定义了Ip命令的使用方式
ip [ OPTIONS ] OBJECT { COMMAND | help }
ip [ -force ] -batch filename
OBJECT := { link | address | addrlabel | route | rule | neigh |
ntable | tunnel | tuntap | maddress | mroute | mrule |
monitor | xfrm | netns | l2tp | tcp_metrics | token |
macsec | vrf | mptcp }
OPTIONS := { -V[ersion] | -h[uman-readable] | -s[tatistics] |
-d[etails] | -r[esolve] | -iec | -f[amily] { inet | inet6
| link } | -4 | -6 | -I | -D | -B | -0 | -l[oops] {
maximum-addr-flush-attempts } | -o[neline] | -rc[vbuf]
[size] | -t[imestamp] | -ts[hort] | -n[etns] name |
-N[umeric] | -a[ll] | -c[olor] | -br[ief] | -j[son] |
-p[retty] }
比较好用的options
ip -c a #带颜色
ip -d a #详细
ip -br a #简略
ip -s a #展示统计信息
ip -n ns_name a #在netns中运行OBJECT相当于子命令
address - protocol (IP or IPv6) address on a device. addrlabel - label configuration for protocol address selection. l2tp - tunnel ethernet over IP (L2TPv3). link - network device. maddress - multicast address. monitor - watch for netlink messages. mptcp - manage MPTCP path manager. mroute - multicast routing cache entry. mrule - rule in multicast routing policy database. neighbour - manage ARP or NDISC cache entries. netns - manage network namespaces. ntable - manage the neighbor cache's operation. route - routing table entry. rule - rule in routing policy database. tcp_metrics/tcpmetrics - manage TCP Metrics token - manage tokenized interface identifiers. tunnel - tunnel over IP. tuntap - manage TUN/TAP devices. vrf - manage virtual routing and forwarding devices. xfrm - manage IPSec policies.
ip-address(8), ip-addrlabel(8), ip-l2tp(8), ip-link(8), ip-maddress(8), ip-monitor(8), ip-mptcp(8), ip-mroute(8), ip-neighbour(8), ip-netns(8), ip-ntable(8), ip-route(8), ip-rule(8), ip-tcp_metrics(8), ip-token(8), ip-tunnel(8), ip-vrf(8), ip-xfrm(8)
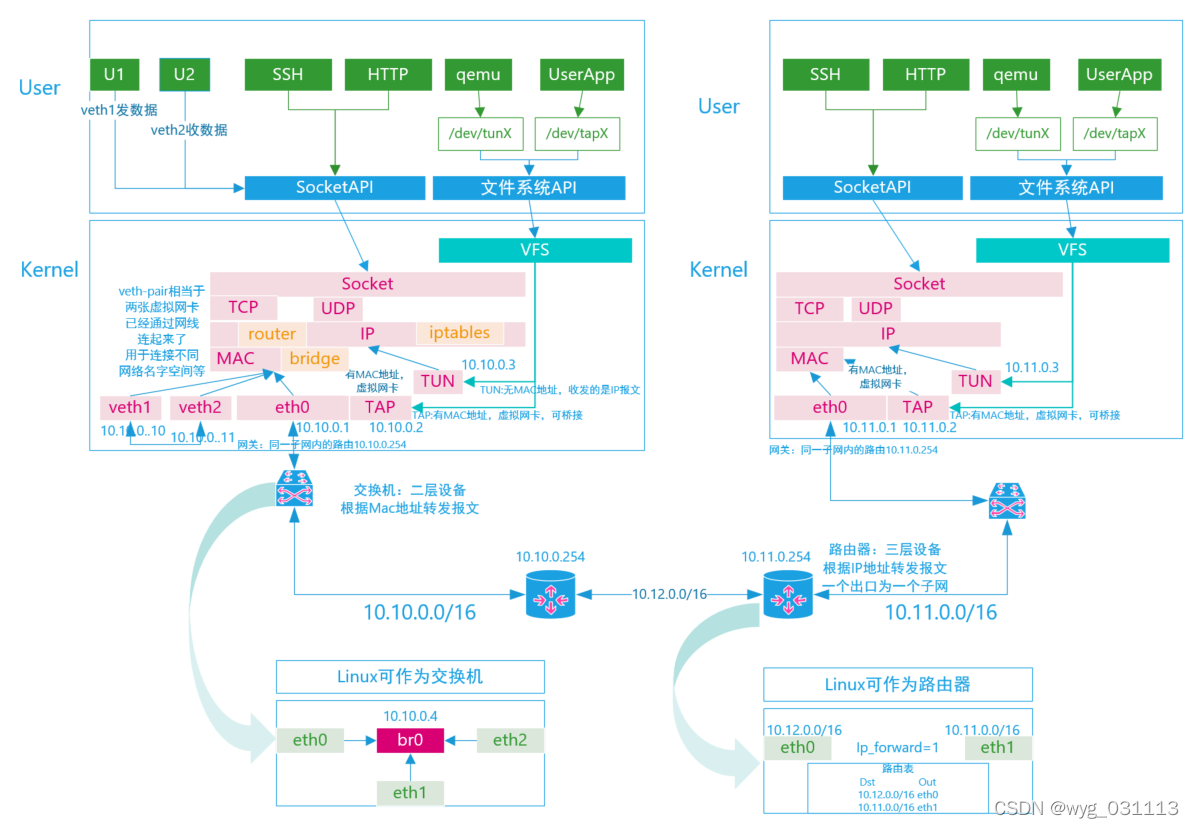
网络概念
ip命令在man手册中已经有非常详细的描述了。其设计也非常友好。关键是要理解网络概念。
ip tunnel:隧道
MODE := { ipip | gre | sit | isatap | vti | ip6ip6 | ipip6 |
ip6gre | vti6 | any }
ip address: 创建与删除interface
TYPE := [ bridge | bridge_slave | bond | bond_slave | can | dummy | hsr | ifb | ipoib | macvlan | macvtap | vcan | veth | vlan | vxlan | ip6tnl | ipip | sit | gre | gretap | erspan | ip6gre | ip6gretap | ip6erspan | vti | vrf | nlmon | ipvlan | lowpan | geneve | macsec ]
ip link: 配置interface
ip link set { DEVICE | group GROUP }
[ { up | down } ]
[ type ETYPE TYPE_ARGS ]
[ arp { on | off } ]
[ dynamic { on | off } ]
[ multicast { on | off } ]
[ allmulticast { on | off } ]
[ promisc { on | off } ]
[ protodown { on | off } ]
[ protodown_reason PREASON { on | off } ]
[ trailers { on | off } ]
[ txqueuelen PACKETS ]
[ name NEWNAME ]
[ address LLADDR ]
[ broadcast LLADDR ]
[ mtu MTU ]
[ netns { PID | NETNSNAME } ]
[ link-netnsid ID ]
[ alias NAME ]
[ vf NUM [ mac LLADDR ]
[ VFVLAN-LIST ]
[ rate TXRATE ]
[ max_tx_rate TXRATE ]
[ min_tx_rate TXRATE ]
[ spoofchk { on | off } ]
[ query_rss { on | off } ]
[ state { auto | enable | disable } ]
[ trust { on | off } ]
[ node_guid eui64 ]
[ port_guid eui64 ] ]
[ { xdp | xdpgeneric | xdpdrv | xdpoffload } { off |
object FILE [ section NAME ] [ verbose ] |
pinned FILE } ]
[ master DEVICE ]
[ nomaster ]
[ vrf NAME ]
[ addrgenmode { eui64 | none | stable_secret | random } ]
[ macaddr [ MACADDR ]
[ { flush | add | del } MACADDR ]
[ set MACADDR ] ]
ip netns
ip [ OPTIONS ] netns { COMMAND | help }
ip netns [ list ]
ip netns add NETNSNAME
ip netns attach NETNSNAME PID
ip [-all] netns del [ NETNSNAME ]
ip netns set NETNSNAME NETNSID
NETNSID := auto | POSITIVE-INT
ip netns identify [ PID ]
ip netns pids NETNSNAME
ip [-all] netns exec [ NETNSNAME ] command...
ip netns monitor
ip netns list-id [ target-nsid POSITIVE-INT ] [ nsid POSITIVE-INT]
iptables命令
iptables -t TABLE -A CHAIN MATCH -j TARGET TARGET_OPTIONS
表(TABLE)里链(CHAIN)中规则(RULE)增删改查
- TABLE: raw, mangle, nat, filter
- CHAIN: PREROUTING, INPUT, FORWARD, OUTPUT, POSTROUTING
- TARGET: ACCEPT, DROP, QUEUE, RETURN,自定义链
#设置TABLE中链的默认策略(POLICE)
iptables -P CHAIN TARGET
#在TABLE表中最后添加一条规则(RULE=MATCH ACTION)
iptables -t TABLE -A CHAIN RULE
#在TABLE表中RULE_NUM位置插入一条规则(RULE_NUM=1,2,3...)
iptables -t TABLE -I CHAIN RULE_NUM RULE
#替换TABLE表中RULE_NUM位置插的条规则(RULE_NUM=1,2,3...)
iptables -t TABLE -R CHAIN RULE_NUM RULE
#查看规则和规则的RULE_NUM(RULE_NUM=1,2,3...)
iptables -t TABLE -L -v -n --line-number #查看所有CHAIN
iptables -t TABLE -L CHAIN -v -n --line-number #查看指定CHAIN
#删除指定RULE_NUM
iptables -t TABLE -D CHAIN RULE_NUM
#清空整个TABLE/CHAIN 规则
iptables -t TABLE -F #清除所有CHAIN
iptables -t TABLE -F CHAIN #清除指定CHAIN
#清空整个TABLE/CHAIN 计数
iptables -t TABLE -Z #清除所有CHAIN
iptables -t TABLE -Z CHAIN #清除指定CHAIN
自定义链的增删改名
#table中新增链
iptable -t table -N new_chain_name
#删除table中链
iptable -t table -X new_chain_name
iptable -t table -X #删除所有非内建链(自定义链)
#修改CHAIN名字
iptable -t table -E old_chain_name new_chain_name规则(RULE=MATCH+TARGET+TARGET_OPTIONS)
一个表中多行规则,每条规则分为MATCH部分和TARGET和TARGET_OPTIONS。
- MATCH:匹配数据包(PACKET)
- TARGET+OPTIONS: 对匹配到的规则执行的动作
- 规则匹配顺序:每个表中从上到下依次进行,直到遇到能匹配的规则
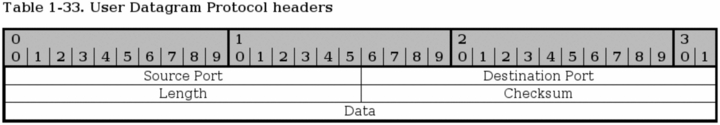
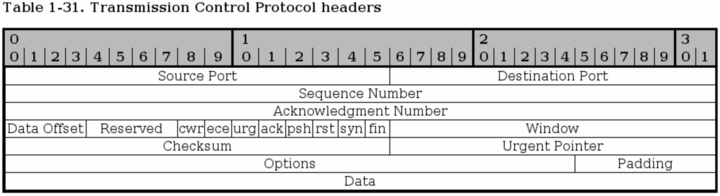
MATCH
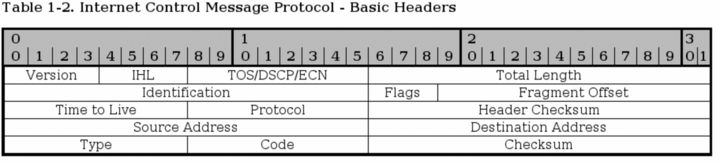
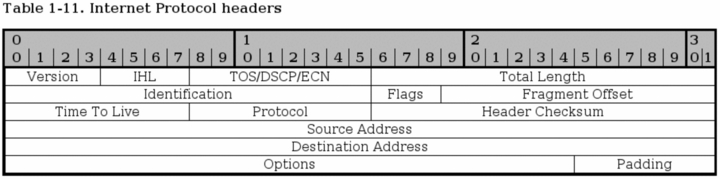
匹配数据包,其选项与数据包中的字段有关。可以匹配TCP/IP协议栈中的网络层,传输层包中的字段,可以匹配数据包的出入接口,可以匹配给数据打上去的标记,可以匹配连接追踪中contrack。Iptables Tutorial 1.2.2。多个匹配条件默认是逻辑与的关系。也可以表达逻辑非:! -p tcp表示不是TCP协议的所有协议。
| MATCH参数 | Example | 说明 |
| -p, --protocol | iptables -A INPUT -p tcp | 协议 |
| -s, --src, --source | iptables -A INPUT -s 192.168.1.1/32 | 源IP |
| -d, --dst, --destination | iptables -A INPUT -d 192.168.1.1/32 | 目的IP |
| --src-range | iptables -A INPUT -p tcp -m iprange --src-range 192.168.1.13-192.168.2.19 | 匹配源IP地址区间 |
| --dst-range | iptables -A INPUT -p tcp -m iprange --dst-range 192.168.1.13-192.168.2.19 | 匹配目的IP地址区间 |
| --length | iptables -A INPUT -p tcp -m length --length 1400:1500 | IP数据包长度 |
| --limit | iptables -A INPUT -m limit --limit 3/hour | |
| --limit-burst | iptables -A INPUT -m limit --limit-burst 5 | |
| --sport, --source-port | iptables -A INPUT -p tcp --sport 22 | 源port。-p udp可匹配UDP port |
| --dport, --destination-port | iptables -A INPUT -p tcp --dport 22 | 目的port |
| --source-port | iptables -A INPUT -p tcp -m multiport --source-port 22,53,80,110 | 多个源port |
| --destination-port | iptables -A INPUT -p tcp -m multiport --destination-port 22,53,80,110 | 多个目的port |
| --port | iptables -A INPUT -p tcp -m multiport --port 22,53,80,110 | 多个源或目的port都能匹配 |
| --tcp-flags | iptables -p tcp --tcp-flags SYN,FIN,ACK SYN | tcp FLAG字段 |
| --syn | iptables -p tcp --syn | 相当于--tcp-flags SYN,RST,ACK SYN |
| --tcp-option | iptables -p tcp --tcp-option 16 | TCP options字段匹配 |
| --icmp-type | iptables -A INPUT -p icmp --icmp-type 8 | 匹配ICMP |
| -i, --in-interface | iptables -A INPUT -i eth0 | 包进入接口 |
| -o, --out-interface | iptables -A FORWARD -o eth0 | 包输出接口 |
| --mac-source | iptables -A INPUT -m mac --mac-source 00:00:00:00:00:01 | 源MAC |
| --src-type | iptables -A INPUT -m addrtype --src-type UNICAST | 源地址类型 |
| --dst-type | iptables -A INPUT -m addrtype --dst-type UNICAST | 目的地址类型 |
| --mark | iptables -A INPUT -m connmark --mark 12 -j ACCEPT | 连接标记 |
| --mark | iptables -t mangle -A INPUT -m mark --mark 1 | |
| --ctstate | iptables -A INPUT -p tcp -m conntrack --ctstate RELATED | INVALID ESTABLISHED NEW RELATED SNAT DNAT |
通过ipset匹配
iptables里可以指定匹配ip地址,但是IP数量过多时效率较低。Linux内核支持把大量IP放入一个set进行高效查询。
ip set 可以分为以下几种类型:ip地址, 网路地址(网段),tcp/udp 端口号, mac地址, 网卡名称。或者是上述类型的组合,并保证快速的匹配。
ipset 适用于以下几种场景:
(1)一次性存储大量的ip或者端口,用以iptables匹配
(2)在不影响性能的前提下,动态更新iptables规则(针对ip或者端口)
(3)期望使用ipset的告诉匹配,或者在一条iptables规则中表达复杂的 ip/端口规则
ipset create SETNAME TYPENAME [ CREATE-OPTIONS ]
ipset add SETNAME ADD-ENTRY [ ADD-OPTIONS ]
ipset del SETNAME DEL-ENTRY [ DEL-OPTIONS ]
SET TYPES
#hash:net
ipset create foo hash:net
ipset add foo 192.168.0.0/24
ipset add foo 10.1.0.0/16
ipset add foo 192.168.0/24
ipset add foo 192.168.0/30 nomatch
#hash:net,net
ipset create foo hash:net,net
ipset add foo 192.168.0.0/24,10.0.1.0/24
ipset add foo 10.1.0.0/16,10.255.0.0/24
ipset add foo 192.168.0/24,192.168.54.0-192.168.54.255
ipset add foo 192.168.0/30,192.168.64/30 nomatch
#hash:ip,port
ipset create foo hash:ip,port
ipset add foo 192.168.1.0/24,80-82
ipset add foo 192.168.1.1,udp:53
ipset add foo 192.168.1.1,vrrp:0
ipset test foo 192.168.1.1,80
#hash:net,port
ipset create foo hash:net,port
ipset add foo 192.168.0/24,25
ipset add foo 10.1.0.0/16,80
ipset test foo 192.168.0/24,25
#hash:ip,port,ip
ipset create foo hash:ip,port,ip
ipset add foo 192.168.1.1,80,10.0.0.1
ipset test foo 192.168.1.1,udp:53,10.0.0.1
#hash:ip,port,net
ipset create foo hash:ip,port,net
ipset add foo 192.168.1,80,10.0.0/24
ipset add foo 192.168.2,25,10.1.0.0/16
ipset test foo 192.168.1,80.10.0.0/24
#hash:ip,mark
ipset create foo hash:ip,mark
ipset add foo 192.168.1.0/24,555
ipset add foo 192.168.1.1,0x63
ipset add foo 192.168.1.1,111236
#hash:net,port,net
ipset create foo hash:net,port,net
ipset add foo 192.168.1.0/24,0,10.0.0/24
ipset add foo 192.168.2.0/24,25,10.1.0.0/16
ipset test foo 192.168.1.1,80,10.0.0.1
#hash:net,iface
ipset create foo hash:net,iface
ipset add foo 192.168.0/24,eth0
ipset add foo 10.1.0.0/16,eth1
ipset test foo 192.168.0/24,eth0
#bitmap:ip
ipset create foo bitmap:ip range 192.168.0.0/16
ipset add foo 192.168.1/24
ipset test foo 192.168.1.1
#bitmap:ip,mac
ipset create foo bitmap:ip,mac range 192.168.0.0/16
ipset add foo 192.168.1.1,12:34:56:78:9A:BC
ipset test foo 192.168.1.1
#bitmap:port
ipset create foo bitmap:port range 0-1024
ipset add foo 80
ipset test foo 80
ipset del foo udp:[macon-udp]-[tn-tl-w2]
#hash:ip
#hash:mac
ipset create foo hash:mac
ipset add foo 01:02:03:04:05:06
ipset test foo 01:02:03:04:05:06
#hash:ip,mac
ipset create foo hash:ip,mac
ipset add foo 1.1.1.1,01:02:03:04:05:06
ipset test foo 1.1.1.1,01:02:03:04:05:06
#list:set
iptables中使用ipset
#目的ip使用ipset
iptables -I INPUT -s 192.168.100.36 -m set --match-set setname dst -j DROP
#源ip使用ipset
iptables -I INPUT -m set --match-set setname src -d 192.168.100.36 -j DROP
#源和目的都使用ipset
iptables -I INPUT -m set --match-set aaa setname1-m set --match-set setname2 dst -j DROP
地址类型
ANYCAST BLACKHOLE BROADCAST LOCAL
MULTICAST NAT PROHIBIT THROW UNICAST
UNREACHABLE UNSPEC XRESOLVE
TARGET
- ACCEPT:接受,通过防火墙
- DROP:丢弃:被防火墙过滤掉了
- QUEUE:排队:放到其他队列里,可由应用程序去处理
- RETURN:返回,停止继续匹配
- 自定义链:到自定义链中匹配,如遇RETURN会返回上一个链继续匹配
目标,即完成匹配后的动作,如可以丢弃数据包,可以修改包字段等。-j TARGET options
| target名称 | Example | Options | 说明 |
| ACCEPT | -j ACCEPT | 防火墙接收此包 | |
| DROP | -j DROP | 防火墙静默丢弃此包 | |
| REJECT | iptables -A FORWARD -p TCP --dport 22 -j REJECT --reject-with tcp-reset | --reject-with | 丢弃并返回错误 |
| RETURN | -j RETURN | 当前链下边的规则不匹配了,返回上一个列 | |
| DNAT | iptables -t nat -A PREROUTING -p tcp -d 15.45.23.67 --dport 80 -j DNAT --to-destination 192.168.1.1-192.168.1.10 | --to-destination | 目的地址转换。 可指定目的地址范围 |
| SNAT | iptables -t nat -A POSTROUTING -p tcp -o eth0 -j SNAT --to-source 194.236.50.155-194.236.50.160:1024-32000 | --to-source | 源IP地址转换 |
| MASQUERADE | iptables -t nat -A POSTROUTING -p TCP -j MASQUERADE --to-ports 1024-31000 | --to-port | 自动源IP地址转换. 并设置源端口范围 |
| REDIRECT | iptables -t nat -A PREROUTING -p tcp --dport 80 -j REDIRECT --to-ports 8080 | --to-ports | 把数据包重定向到本地的端口,用来实现proxy。只能在PREROUTING和OUTPUT链中使用 |
| NETMAP | iptables -t mangle -A PREROUTING -s 192.168.1.0/24 -j NETMAP --to 10.5.6.0/24 | 源IP与一一映射到新IP | |
| SAME | iptables -t mangle -A PREROUTING -s 192.168.1.0/24 -j SAME --to 10.5.6.7-10.5.6.9 | --to | 源地址转换时使用相同的IP |
| iptables -t mangle -A PREROUTING -s 192.168.1.0/24 -j SAME --to 10.5.6.7-10.5.6.9 --nodst | --nodst | ||
| MARK | iptables -t mangle -A PREROUTING -p tcp --dport 22 -j MARK --set-mark 2 | --set-mark | 包打标记 |
| CONNMARK | ptables -t nat -A PREROUTING -p tcp --dport 80 -j CONNMARK --set-mark 4 | --set-mark | 设置mark |
| iptables -t mangle -A PREROUTING --dport 80 -j CONNMARK --save-mark | --save-mark | 把packet mark保存到连接mark中 | |
| iptables -t mangle -A PREROUTING --dport 80 -j CONNMARK --restore-mark | --restore-mark | ||
| iptables -t mangle -A PREROUTING --dport 80 -j CONNMARK --restore-mark --mask 1 | --mask | ||
| CLASSIFY | iptables -t mangle -A POSTROUTING -p tcp --dport 80 -j CLASSIFY --set-class 20:10 | --set-class | 给包分类 |
| CLUSTERIP | iptables -A INPUT -p tcp -d 192.168.0.5 --dport 80 -j CLUSTERIP --new ... | --new | |
| iptables -A INPUT -p tcp -d 192.168.0.5 --dport 443 -j CLUSTERIP --new --hashmode sourceip ... | --hashmode | ||
| iptables -A INPUT -p tcp -d 192.168.0.5 --dport 80 -j CLUSTERIP --new --hashmode sourceip --clustermac 01:00:5e:00:00:20 ... | --clustermac | ||
| iptables -A INPUT -p tcp -d 192.168.0.5 --dport 80 -j CLUSTERIP --new --hashmode sourceip --clustermac 01:00:5e:00:00:20 --total-nodes 2 ... | --total-nodes | ||
| iptables -A INPUT -p tcp -d 192.168.0.5 --dport 80 -j CLUSTERIP --new --hashmode sourceip --clustermac 01:00:5e:00:00:20 --total-nodes 2 --local-node 1 | --local-node | ||
| iptables -A INPUT -p tcp -d 192.168.0.5 --dport 80 -j CLUSTERIP --new --hashmode sourceip --clustermac 01:00:5e:00:00:20 --hash-init 1234 | --hash-init | ||
| MIRROR | 源IP目的IP互换,再发出去 | ||
| NFQUEUE | iptables -t nat -A PREROUTING -p tcp --dport 80 -j NFQUEUE --queue-num 30 | --queue-num | 所数据包放到指定队列里 |
| QUEUE | |||
| NOTRACK | 关闭连接追踪,只能在raw表中使用 | ||
| TCPMSS | |||
| TOS | |||
| TTL | iptables -t mangle -A PREROUTING -i eth0 -j TTL --ttl-set 64 | --ttl-set | 设置TTL |
各表功能
- raw: 主要用于决定数据包是否被状态跟踪机制处理。一但匹配则不会再走其他表
- mangle: 修改数据中的字段,如mark标记,qos, ttl等
- nat: 地址转换:可以修改源IP/PORT,目的IP/PORT,或者重定向到其他端口
- filter: 包过滤,决定一个包是否通过防火墙
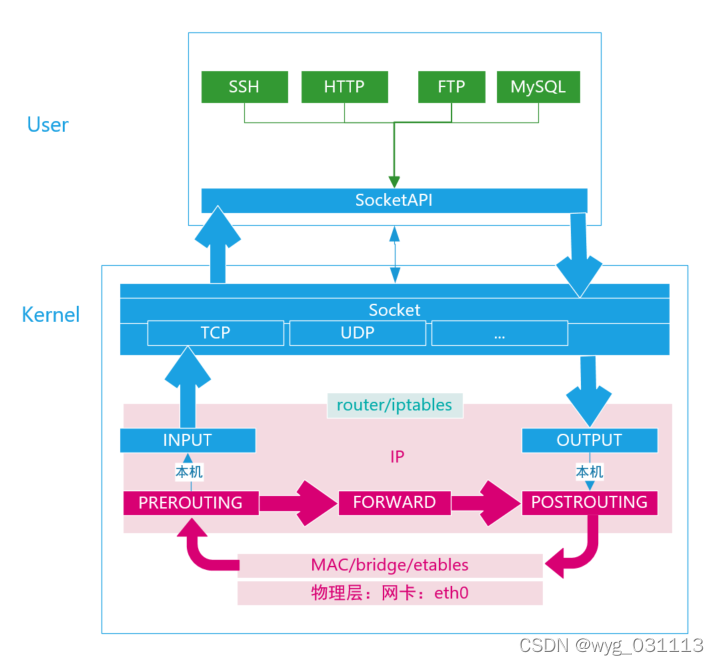
表匹配顺序 :raw->mangle->nat->filter
不是每张表都有5条链
netfilter:数据包处理流程
例子
iptables -t filter -L -v -n
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
732 72340 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 ctstate RELATED,ESTABLISHED
0 0 ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0
10 754 INPUT_direct all -- * * 0.0.0.0/0 0.0.0.0/0
10 754 INPUT_ZONES_SOURCE all -- * * 0.0.0.0/0 0.0.0.0/0
10 754 INPUT_ZONES all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 ctstate INVALID
9 702 REJECT all -- * * 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain FORWARD (policy DROP 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
0 0 DOCKER-ISOLATION all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DOCKER all -- * docker0 0.0.0.0/0 0.0.0.0/0
0 0 ACCEPT all -- * docker0 0.0.0.0/0 0.0.0.0/0 ctstate RELATED,ESTABLISHED
0 0 ACCEPT all -- docker0 !docker0 0.0.0.0/0 0.0.0.0/0
0 0 ACCEPT all -- docker0 docker0 0.0.0.0/0 0.0.0.0/0
0 0 ACCEPT all -- * * 0.0.0.0/0 0.0.0.0/0 ctstate RELATED,ESTABLISHED
0 0 ACCEPT all -- lo * 0.0.0.0/0 0.0.0.0/0
0 0 FORWARD_direct all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FORWARD_IN_ZONES_SOURCE all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FORWARD_IN_ZONES all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FORWARD_OUT_ZONES_SOURCE all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FORWARD_OUT_ZONES all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 DROP all -- * * 0.0.0.0/0 0.0.0.0/0 ctstate INVALID
0 0 REJECT all -- * * 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain OUTPUT (policy ACCEPT 523 packets, 97359 bytes)
pkts bytes target prot opt in out source destination
0 0 ACCEPT all -- * lo 0.0.0.0/0 0.0.0.0/0
541 98613 OUTPUT_direct all -- * * 0.0.0.0/0 0.0.0.0/0
Chain DOCKER (1 references)
pkts bytes target prot opt in out source destination
Chain DOCKER-ISOLATION (1 references)
pkts bytes target prot opt in out source destination
0 0 RETURN all -- * * 0.0.0.0/0 0.0.0.0/0
Chain FORWARD_IN_ZONES (1 references)
pkts bytes target prot opt in out source destination
0 0 FWDI_public all -- ens33 * 0.0.0.0/0 0.0.0.0/0 [goto]
0 0 FWDI_public all -- + * 0.0.0.0/0 0.0.0.0/0 [goto]
Chain FORWARD_IN_ZONES_SOURCE (1 references)
pkts bytes target prot opt in out source destination
Chain FORWARD_OUT_ZONES (1 references)
pkts bytes target prot opt in out source destination
0 0 FWDO_public all -- * ens33 0.0.0.0/0 0.0.0.0/0 [goto]
0 0 FWDO_public all -- * + 0.0.0.0/0 0.0.0.0/0 [goto]
Chain FORWARD_OUT_ZONES_SOURCE (1 references)
pkts bytes target prot opt in out source destination
Chain FORWARD_direct (1 references)
pkts bytes target prot opt in out source destination
Chain FWDI_public (2 references)
pkts bytes target prot opt in out source destination
0 0 FWDI_public_log all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FWDI_public_deny all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FWDI_public_allow all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 ACCEPT icmp -- * * 0.0.0.0/0 0.0.0.0/0
Chain FWDI_public_allow (1 references)
pkts bytes target prot opt in out source destination
Chain FWDI_public_deny (1 references)
pkts bytes target prot opt in out source destination
Chain FWDI_public_log (1 references)
pkts bytes target prot opt in out source destination
Chain FWDO_public (2 references)
pkts bytes target prot opt in out source destination
0 0 FWDO_public_log all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FWDO_public_deny all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 FWDO_public_allow all -- * * 0.0.0.0/0 0.0.0.0/0
Chain FWDO_public_allow (1 references)
pkts bytes target prot opt in out source destination
Chain FWDO_public_deny (1 references)
pkts bytes target prot opt in out source destination
Chain FWDO_public_log (1 references)
pkts bytes target prot opt in out source destination
Chain INPUT_ZONES (1 references)
pkts bytes target prot opt in out source destination
10 754 IN_public all -- ens33 * 0.0.0.0/0 0.0.0.0/0 [goto]
0 0 IN_public all -- + * 0.0.0.0/0 0.0.0.0/0 [goto]
Chain INPUT_ZONES_SOURCE (1 references)
pkts bytes target prot opt in out source destination
Chain INPUT_direct (1 references)
pkts bytes target prot opt in out source destination
Chain IN_public (2 references)
pkts bytes target prot opt in out source destination
10 754 IN_public_log all -- * * 0.0.0.0/0 0.0.0.0/0
10 754 IN_public_deny all -- * * 0.0.0.0/0 0.0.0.0/0
10 754 IN_public_allow all -- * * 0.0.0.0/0 0.0.0.0/0
0 0 ACCEPT icmp -- * * 0.0.0.0/0 0.0.0.0/0
Chain IN_public_allow (1 references)
pkts bytes target prot opt in out source destination
1 52 ACCEPT tcp -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:22 ctstate NEW,UNTRACKED
Chain IN_public_deny (1 references)
pkts bytes target prot opt in out source destination
Chain IN_public_log (1 references)
pkts bytes target prot opt in out source destination
Chain OUTPUT_direct (1 references)
pkts bytes target prot opt in out source destination tcpdump抓包工具
tcpdump MATCH DUMP_OPTIONS
tcpdump(1) man page | TCPDUMP & LIBPCAP
- MATCH:匹配数据包,类似iptables中的MATCH,可以匹配协议报文中的字段
- 匹配规则用pcap规则:pcap-filter(7) man page | TCPDUMP & LIBPCAP
- DUMP:匹配后执行的dump动作的选项。默认是输出到标准输出。
DUMP参数
| 参数 | example | 说明 |
| -i interface --interface=interface | -i eth0 | 监听interface上的数据包 |
| -F file | -f match_rule.txt | 从文件中读取匹配规则。忽略后续匹配规则 |
| -w file | -w data.pcap | 匹配到的数据包写入文件 |
| -r file | -r data.pcap | 从-w写入文件里读回数据 |
| 在用-w时同时输出到标准输出 | ||
| -x -xx -X | 打印数据包头 | |
| -v -vv -vvv -V | 打印并解析数据包头字段为可读字符 | |
| -t -tt -ttt -tttt -ttttt | 打印时间戳 | |
| -# --number | 打印包序号 | |
| -n | 不把IP转为域名 | |
| -I --monitor-mode | 监听方式抓WiFi | |
| -D | tcpdump -D | 打印所有可用Interface |
| -c count | 抓到count个包就退出 | |
| -A | 以ASCII打印包内容 |
MATCH规则
-
match = proto direction type
-
type: host,net,port,portrange
- host foo
- net 128.3
- port 20
- portrange 6000-6008
-
direction: src, dst, src or dst, src and dst, ra, ta, addr1, addr2, addr3, addr4
- src foo
- dst net 128.3
- src or dst port ftp-data
- 默认src or dst
- 可以加在type前限制type: src host, dst port
-
proto: ether, wlan, ip ip6, arp, rarp, sctp, tcp, udp
- 加在direction前来限制
- ether src foo
- arp net 128.3
- tcp port 21
- udp portrange 7000-7009
-
逻辑关系and or not ()
-
tcp port 80 and (((ip[2:2] - ((ip[0]&0xf)<<2)) - ((tcp[12]&0xf0)>>2)) != 0)
-
ether[0] & 1 = 0 and ip[16] >= 224
-
tcpdump -i eth0 -vv -n tcp src or dst port http and not \(tcp port telnet or udp port 53\)
-
example
tcpdump -i eth0 -vvv -tttt -n src host 172.31.7.72 and dst host 220.181.38.148 and tcp dst port 80
tcpdump 'tcp[tcpflags] & (tcp-syn|tcp-fin) != 0 and not src and dst net localnet'
tcpdump 'gateway snup and ip[2:2] > 576'
tcpdump host sundown网络综合试验
centos7中进行的测试。会清空防火墙和nat的所有规则。确保已经安装了python2.7 ssh
[root@centos100 netexp]# uname -a
Linux centos100 3.10.0-1160.el7.x86_64 #1 SMP Mon Oct 19 16:18:59 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
[root@centos100 netexp]# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 00:0c:29:cc:91:94 brd ff:ff:ff:ff:ff:ff
inet 192.168.0.100/24 brd 192.168.0.255 scope global noprefixroute ens33
valid_lft forever preferred_lft forever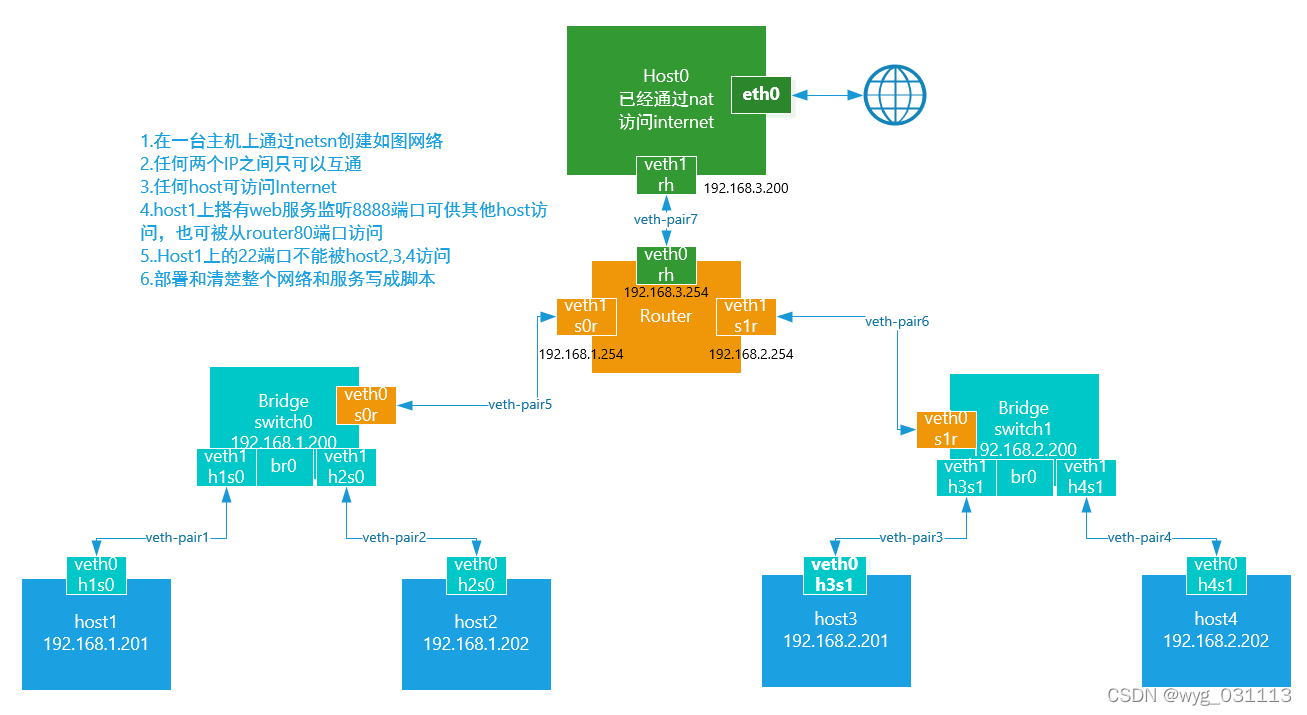
实现环境
同时在host2 host4之间实现ipip隧道
base.sh
#!/bin/bash
ns="host1 host2 host3 host4 switch0 switch1 router"
host1_ip=192.168.1.201
host2_ip=192.168.1.202
host3_ip=192.168.2.201
host4_ip=192.168.2.202
host_default_ip=192.168.3.201
switch0_ip=192.168.1.200
switch1_ip=192.168.2.200
router_s0_ip=192.168.1.254
router_s1_ip=192.168.2.254
router_h_ip=192.168.3.254
net1=192.168.1.0
net2=192.168.2.0
net3=192.168.3.0
function showns(){
for s in $ns
do
echo "---------------$s------------------"
ip netns exec $s ip -br -c link show
ip netns exec $s ip -br -c address show
ip netns exec $s ip route show
done
echo "---------------default------------------"
ip -br -c link show
ip -br -c addr show
}
function createns(){
for s in $ns
do
echo "add ns $s"
ip netns add $s
ip netns exec $s ip link set up dev lo
done
}
function delns(){
for s in $ns
do
echo "del ns $s"
ip netns del $s
done
}
function add_veth_to_ns()
{
echo "add $1 to $3, add $2 to $4"
ip link add $1 type veth peer name $2
ip link set $1 netns $3
ip link set $2 netns $4
}
function set_ip_addr() {
echo "set ns $1 $2 to $3"
ip netns exec $1 ip address add $3 dev $2
ip netns exec $1 ip link set up dev $2
}
function add_bridge() {
echo "add bridge $2 to ns $1"
ip netns exec $1 ip link add name $2 type bridge
ip netns exec $1 ip link set up dev $2
}
function add_veth_to_bridge() {
echo "add $2 to bridge $3 in $1"
ip netns exec $1 ip link set up dev $2
ip netns exec $1 ip link set $2 master $3
}
function test_connection() {
#check switch0 network
echo check: $host1_ip -- $host2_ip
ip netns exec host1 ping -c 2 ${host2_ip}
echo check: $host1_ip -- $switch0_ip
ip netns exec host1 ping -c 2 ${switch0_ip}
echo check: $host1_ip -- ${router_s0_ip}
ip netns exec host1 ping -c 2 ${router_s0_ip}
#check switch1 network
echo check: $host3_ip -- ${host4_ip}
ip netns exec host3 ping -c 2 ${host4_ip}
echo check: $host3_ip -- ${switch1_ip}
ip netns exec host3 ping -c 2 ${switch1_ip}
echo check: $host3_ip -- ${router_s1_ip}
ip netns exec host3 ping -c 2 ${router_s1_ip}
#check router host
ping -c 2 ${router_h_ip}
#check ping via different net
echo check $net1 ping $net2
ip netns exec host1 ping -c 2 ${host3_ip}
echo check $net2 ping $net1
ip netns exec host4 ping -c 2 ${host2_ip}
echo check $net1 ping $net3
ip netns exec host1 ping -c 2 ${host_default_ip}
echo check $net2 ping $net3
ip netns exec host3 ping -c 2 ${host_default_ip}
#check all net can access internet
ip netns exec router curl baidu.com
ip netns exec host1 curl baidu.com
ip netns exec host3 curl baidu.com
#check dnat
curl 192.168.3.254
ip netns exec host3 curl 192.168.3.254
#check ipip tunnel
ip netns exec host2 ping -c 2 192.168.4.102
ip netns exec host4 ping -c 2 192.168.4.101
}build_network.sh
#!/bin/bash
. base.sh
set -e
#create netns
echo 1 > /proc/sys/net/ipv4/ip_forward
createns
ip netns list
#create veth and put it to netns
#veth-pair1
add_veth_to_ns veth0h1s0 veth1h1s0 host1 switch0
#veth-pair2
add_veth_to_ns veth0h2s0 veth1h2s0 host2 switch0
#veth-pair3
add_veth_to_ns veth0h3s1 veth1h3s1 host3 switch1
#veth-pair4
add_veth_to_ns veth0h4s1 veth1h4s1 host4 switch1
#veth-pair5
add_veth_to_ns veth0s0r veth1s0r switch0 router
#veth-pair6
add_veth_to_ns veth0s1r veth1s1r switch1 router
#veth-pair7
echo "add veth0rh to router, add veth1rh to host"
ip link add veth0rh type veth peer name veth1rh
ip link set veth0rh netns router
#add bridge to switch0
add_bridge switch0 br
add_bridge switch1 br
#add veth to bridge
#switch0
add_veth_to_bridge switch0 veth1h1s0 br
add_veth_to_bridge switch0 veth1h2s0 br
add_veth_to_bridge switch0 veth0s0r br
#switch1
add_veth_to_bridge switch1 veth1h3s1 br
add_veth_to_bridge switch1 veth1h4s1 br
add_veth_to_bridge switch1 veth0s1r br
#config veth
set_ip_addr host1 veth0h1s0 ${host1_ip}/24
set_ip_addr host2 veth0h2s0 ${host2_ip}/24
set_ip_addr host3 veth0h3s1 ${host3_ip}/24
set_ip_addr host4 veth0h4s1 ${host4_ip}/24
set_ip_addr switch0 br ${switch0_ip}/24
set_ip_addr switch1 br ${switch1_ip}/24
set_ip_addr router veth0rh ${router_h_ip}/24
set_ip_addr router veth1s0r ${router_s0_ip}/24
set_ip_addr router veth1s1r ${router_s1_ip}/24
#host
ip address add ${host_default_ip} dev veth1rh
ip link set up dev veth1rh
ip route add 192.168.3.0/24 dev veth1rh
ip route add 192.168.2.0/24 via 192.168.3.254
ip route add 192.168.1.0/24 via 192.168.3.254
#config router switch0 switch1可互通
#default gateway
ip netns exec host1 ip route add default via ${router_s0_ip}
ip netns exec host2 ip route add default via ${router_s0_ip}
ip netns exec host3 ip route add default via ${router_s1_ip}
ip netns exec host4 ip route add default via ${router_s1_ip}
#router 默认已经建立了路由
#ip netns exec router ip route add ${net1}/24 via ${router_s0_ip}
#ip netns exec router ip route add ${net2}/24 via ${router_s1_ip}
#ip netns exec router ip route add ${net3}/24 via ${router_h_ip}
#config nat to access internet
ip netns exec router ip route add default via 192.168.3.201
iptables -F
iptables -P FORWARD ACCEPT
iptables -t nat -I POSTROUTING -s 192.168.1.0/24 -j MASQUERADE
iptables -t nat -I POSTROUTING -s 192.168.2.0/24 -j MASQUERADE
iptables -t nat -I POSTROUTING -s 192.168.3.0/24 -j MASQUERADE
#only 192.168.3.201 can access host1 22 port
ip netns exec host1 /usr/sbin/sshd
ip netns exec host1 iptables -t filter -I INPUT -p tcp ! -s 192.168.3.201 --dport 22 -j DROP
#run http server at 192.168.3.201:8888 but can access by 192.168.3.254:80
ip netns exec host1 python -m SimpleHTTPServer 8888 &
ip netns exec router iptables -t nat -I PREROUTING -p tcp --dst 192.168.3.254/32 --dport 80 -j DNAT --to-destination 192.168.1.201:8888
#build ip tunnel between host2 and host4
#host2
ip netns exec host2 modprobe ipip
ip netns exec host2 ip tunnel add tun0 mode ipip remote 192.168.2.202 local 192.168.1.202 ttl 64
ip netns exec host2 ip addr add 192.168.4.101 peer 192.168.4.102 dev tun0
ip netns exec host2 ip link set tun0 up
ip netns exec host2 ip route add 192.168.4.0/24 dev tun0
#host4
ip netns exec host4 modprobe ipip
ip netns exec host4 ip tunnel add tun0 mode ipip local 192.168.2.202 remote 192.168.1.202 ttl 64
ip netns exec host4 ip addr add 192.168.4.102 peer 192.168.4.101 dev tun0
ip netns exec host4 ip link set tun0 up
ip netns exec host4 ip route add 192.168.4.0/24 dev tun0
showns
test_connectionremove_network.sh
#!/bin/bash
. base.sh
delns
iptables -F
iptables -t nat -F
pkill python
ip netns list
ip route del 192.168.3.0/24 dev veth1rh
ip route del 192.168.2.0/24 via 192.168.3.254
ip route del 192.168.1.0/24 via 192.168.3.254
showns实际结果
[root@centos100 netexp]# ./build.sh
add ns host1
add ns host2
add ns host3
add ns host4
add ns switch0
add ns switch1
add ns router
router
switch1
switch0
host4
host3
host2
host1
add veth0h1s0 to host1, add veth1h1s0 to switch0
add veth0h2s0 to host2, add veth1h2s0 to switch0
add veth0h3s1 to host3, add veth1h3s1 to switch1
add veth0h4s1 to host4, add veth1h4s1 to switch1
add veth0s0r to switch0, add veth1s0r to router
add veth0s1r to switch1, add veth1s1r to router
add veth0rh to router, add veth1rh to host
add bridge br to ns switch0
add bridge br to ns switch1
add veth1h1s0 to bridge br in switch0
add veth1h2s0 to bridge br in switch0
add veth0s0r to bridge br in switch0
add veth1h3s1 to bridge br in switch1
add veth1h4s1 to bridge br in switch1
add veth0s1r to bridge br in switch1
set ns host1 veth0h1s0 to 192.168.1.201/24
set ns host2 veth0h2s0 to 192.168.1.202/24
set ns host3 veth0h3s1 to 192.168.2.201/24
set ns host4 veth0h4s1 to 192.168.2.202/24
set ns switch0 br to 192.168.1.200/24
set ns switch1 br to 192.168.2.200/24
set ns router veth0rh to 192.168.3.254/24
set ns router veth1s0r to 192.168.1.254/24
set ns router veth1s1r to 192.168.2.254/24
Serving HTTP on 0.0.0.0 port 8888 ...
---------------host1------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
veth0h1s0@if75 UP 8e:6f:27:a7:e8:a5 <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
veth0h1s0@if75 UP 192.168.1.201/24 fe80::8c6f:27ff:fea7:e8a5/64
default via 192.168.1.254 dev veth0h1s0
192.168.1.0/24 dev veth0h1s0 proto kernel scope link src 192.168.1.201
---------------host2------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
tun0@NONE UNKNOWN 192.168.1.202 <POINTOPOINT,NOARP,UP,LOWER_UP>
veth0h2s0@if77 UP ee:9d:0c:c2:76:52 <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
tun0@NONE UNKNOWN 192.168.4.101 peer 192.168.4.102/32 fe80::5efe:c0a8:1ca/64
veth0h2s0@if77 UP 192.168.1.202/24 fe80::ec9d:cff:fec2:7652/64
default via 192.168.1.254 dev veth0h2s0
192.168.1.0/24 dev veth0h2s0 proto kernel scope link src 192.168.1.202
192.168.4.0/24 dev tun0 scope link
192.168.4.102 dev tun0 proto kernel scope link src 192.168.4.101
---------------host3------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
veth0h3s1@if79 UP aa:25:4e:8d:f2:3a <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
veth0h3s1@if79 UP 192.168.2.201/24 fe80::a825:4eff:fe8d:f23a/64
default via 192.168.2.254 dev veth0h3s1
192.168.2.0/24 dev veth0h3s1 proto kernel scope link src 192.168.2.201
---------------host4------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
tun0@NONE UNKNOWN 192.168.2.202 <POINTOPOINT,NOARP,UP,LOWER_UP>
veth0h4s1@if81 UP ae:45:3d:71:4c:bf <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
tun0@NONE UNKNOWN 192.168.4.102 peer 192.168.4.101/32 fe80::5efe:c0a8:2ca/64
veth0h4s1@if81 UP 192.168.2.202/24 fe80::ac45:3dff:fe71:4cbf/64
default via 192.168.2.254 dev veth0h4s1
192.168.2.0/24 dev veth0h4s1 proto kernel scope link src 192.168.2.202
192.168.4.0/24 dev tun0 scope link
192.168.4.101 dev tun0 proto kernel scope link src 192.168.4.102
---------------switch0------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
br UP 72:b8:53:09:20:56 <BROADCAST,MULTICAST,UP,LOWER_UP>
veth1h1s0@if76 UP 72:b8:53:09:20:56 <BROADCAST,MULTICAST,UP,LOWER_UP>
veth1h2s0@if78 UP ca:0a:f5:7d:a0:78 <BROADCAST,MULTICAST,UP,LOWER_UP>
veth0s0r@if83 UP ea:d2:48:91:ed:6c <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
br UP 192.168.1.200/24 fe80::84ba:26ff:fea2:f6bf/64
veth1h1s0@if76 UP fe80::70b8:53ff:fe09:2056/64
veth1h2s0@if78 UP fe80::c80a:f5ff:fe7d:a078/64
veth0s0r@if83 UP fe80::e8d2:48ff:fe91:ed6c/64
192.168.1.0/24 dev br proto kernel scope link src 192.168.1.200
---------------switch1------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
br UP 12:bf:92:82:0d:1e <BROADCAST,MULTICAST,UP,LOWER_UP>
veth1h3s1@if80 UP 12:bf:92:82:0d:1e <BROADCAST,MULTICAST,UP,LOWER_UP>
veth1h4s1@if82 UP 4a:e3:37:1e:9d:4f <BROADCAST,MULTICAST,UP,LOWER_UP>
veth0s1r@if85 UP c6:4f:b6:cf:27:a0 <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
br UP 192.168.2.200/24 fe80::b88e:b5ff:fe40:6126/64
veth1h3s1@if80 UP fe80::10bf:92ff:fe82:d1e/64
veth1h4s1@if82 UP fe80::48e3:37ff:fe1e:9d4f/64
veth0s1r@if85 UP fe80::c44f:b6ff:fecf:27a0/64
192.168.2.0/24 dev br proto kernel scope link src 192.168.2.200
---------------router------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
veth1s0r@if84 UP b2:49:00:de:bd:8b <BROADCAST,MULTICAST,UP,LOWER_UP>
veth1s1r@if86 UP 36:30:be:64:de:7e <BROADCAST,MULTICAST,UP,LOWER_UP>
veth0rh@if87 UP fe:e6:4a:12:9a:f2 <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
tunl0@NONE DOWN
veth1s0r@if84 UP 192.168.1.254/24 fe80::b049:ff:fede:bd8b/64
veth1s1r@if86 UP 192.168.2.254/24 fe80::3430:beff:fe64:de7e/64
veth0rh@if87 UP 192.168.3.254/24 fe80::fce6:4aff:fe12:9af2/64
default via 192.168.3.201 dev veth0rh
192.168.1.0/24 dev veth1s0r proto kernel scope link src 192.168.1.254
192.168.2.0/24 dev veth1s1r proto kernel scope link src 192.168.2.254
192.168.3.0/24 dev veth0rh proto kernel scope link src 192.168.3.254
---------------default------------------
lo UNKNOWN 00:00:00:00:00:00 <LOOPBACK,UP,LOWER_UP>
ens33 UP 00:0c:29:c2:fc:1c <BROADCAST,MULTICAST,UP,LOWER_UP>
docker0 DOWN 02:42:62:c1:b1:e3 <NO-CARRIER,BROADCAST,MULTICAST,UP>
tunl0@NONE DOWN 0.0.0.0 <NOARP>
veth1rh@if88 UP ce:b0:8a:4a:e4:d9 <BROADCAST,MULTICAST,UP,LOWER_UP>
lo UNKNOWN 127.0.0.1/8 ::1/128
ens33 UP 192.168.50.100/24 fe80::4a0c:6495:e803:ae76/64
docker0 DOWN 172.17.0.1/16
tunl0@NONE DOWN
veth1rh@if88 UP 192.168.3.201/32 fe80::ccb0:8aff:fe4a:e4d9/64
check: 192.168.1.201 -- 192.168.1.202
PING 192.168.1.202 (192.168.1.202) 56(84) bytes of data.
64 bytes from 192.168.1.202: icmp_seq=1 ttl=64 time=1.03 ms
64 bytes from 192.168.1.202: icmp_seq=2 ttl=64 time=0.204 ms
--- 192.168.1.202 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.204/0.621/1.039/0.418 ms
check: 192.168.1.201 -- 192.168.1.200
PING 192.168.1.200 (192.168.1.200) 56(84) bytes of data.
64 bytes from 192.168.1.200: icmp_seq=1 ttl=64 time=0.637 ms
64 bytes from 192.168.1.200: icmp_seq=2 ttl=64 time=0.165 ms
--- 192.168.1.200 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1000ms
rtt min/avg/max/mdev = 0.165/0.401/0.637/0.236 ms
check: 192.168.1.201 -- 192.168.1.254
PING 192.168.1.254 (192.168.1.254) 56(84) bytes of data.
64 bytes from 192.168.1.254: icmp_seq=1 ttl=64 time=0.642 ms
64 bytes from 192.168.1.254: icmp_seq=2 ttl=64 time=0.730 ms
--- 192.168.1.254 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 0.642/0.686/0.730/0.044 ms
check: 192.168.2.201 -- 192.168.2.202
PING 192.168.2.202 (192.168.2.202) 56(84) bytes of data.
64 bytes from 192.168.2.202: icmp_seq=1 ttl=64 time=0.121 ms
64 bytes from 192.168.2.202: icmp_seq=2 ttl=64 time=0.155 ms
--- 192.168.2.202 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.121/0.138/0.155/0.017 ms
check: 192.168.2.201 -- 192.168.2.200
PING 192.168.2.200 (192.168.2.200) 56(84) bytes of data.
64 bytes from 192.168.2.200: icmp_seq=1 ttl=64 time=0.361 ms
64 bytes from 192.168.2.200: icmp_seq=2 ttl=64 time=0.175 ms
--- 192.168.2.200 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1000ms
rtt min/avg/max/mdev = 0.175/0.268/0.361/0.093 ms
check: 192.168.2.201 -- 192.168.2.254
PING 192.168.2.254 (192.168.2.254) 56(84) bytes of data.
64 bytes from 192.168.2.254: icmp_seq=1 ttl=64 time=0.118 ms
64 bytes from 192.168.2.254: icmp_seq=2 ttl=64 time=0.210 ms
--- 192.168.2.254 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.118/0.164/0.210/0.046 ms
PING 192.168.3.254 (192.168.3.254) 56(84) bytes of data.
64 bytes from 192.168.3.254: icmp_seq=1 ttl=64 time=0.113 ms
64 bytes from 192.168.3.254: icmp_seq=2 ttl=64 time=0.158 ms
--- 192.168.3.254 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.113/0.135/0.158/0.025 ms
check 192.168.1.0 ping 192.168.2.0
PING 192.168.2.201 (192.168.2.201) 56(84) bytes of data.
64 bytes from 192.168.2.201: icmp_seq=1 ttl=63 time=0.882 ms
64 bytes from 192.168.2.201: icmp_seq=2 ttl=63 time=0.247 ms
--- 192.168.2.201 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 0.247/0.564/0.882/0.318 ms
check 192.168.2.0 ping 192.168.1.0
PING 192.168.1.202 (192.168.1.202) 56(84) bytes of data.
64 bytes from 192.168.1.202: icmp_seq=1 ttl=63 time=0.386 ms
64 bytes from 192.168.1.202: icmp_seq=2 ttl=63 time=0.870 ms
--- 192.168.1.202 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 0.386/0.628/0.870/0.242 ms
check 192.168.1.0 ping 192.168.3.0
PING 192.168.3.201 (192.168.3.201) 56(84) bytes of data.
64 bytes from 192.168.3.201: icmp_seq=1 ttl=63 time=0.126 ms
64 bytes from 192.168.3.201: icmp_seq=2 ttl=63 time=0.137 ms
--- 192.168.3.201 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1000ms
rtt min/avg/max/mdev = 0.126/0.131/0.137/0.012 ms
check 192.168.2.0 ping 192.168.3.0
PING 192.168.3.201 (192.168.3.201) 56(84) bytes of data.
64 bytes from 192.168.3.201: icmp_seq=1 ttl=63 time=0.103 ms
64 bytes from 192.168.3.201: icmp_seq=2 ttl=63 time=0.251 ms
--- 192.168.3.201 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1000ms
rtt min/avg/max/mdev = 0.103/0.177/0.251/0.074 ms
<html>
<meta http-equiv="refresh" content="0;url=http://www.baidu.com/">
</html>
<html>
<meta http-equiv="refresh" content="0;url=http://www.baidu.com/">
</html>
<html>
<meta http-equiv="refresh" content="0;url=http://www.baidu.com/">
</html>
192.168.3.201 - - [27/Feb/2022 10:39:29] "GET / HTTP/1.1" 200 -
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 3.2 Final//EN"><html>
<title>Directory listing for /</title>
<body>
<h2>Directory listing for /</h2>
<hr>
<ul>
<li><a href="base.sh">base.sh</a>
<li><a href="build.sh">build.sh</a>
<li><a href="remove.sh">remove.sh</a>
</ul>
<hr>
</body>
</html>
192.168.2.201 - - [27/Feb/2022 10:39:29] "GET / HTTP/1.1" 200 -
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 3.2 Final//EN"><html>
<title>Directory listing for /</title>
<body>
<h2>Directory listing for /</h2>
<hr>
<ul>
<li><a href="base.sh">base.sh</a>
<li><a href="build.sh">build.sh</a>
<li><a href="remove.sh">remove.sh</a>
</ul>
<hr>
</body>
</html>
PING 192.168.4.102 (192.168.4.102) 56(84) bytes of data.
64 bytes from 192.168.4.102: icmp_seq=1 ttl=64 time=0.130 ms
64 bytes from 192.168.4.102: icmp_seq=2 ttl=64 time=0.902 ms
--- 192.168.4.102 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1001ms
rtt min/avg/max/mdev = 0.130/0.516/0.902/0.386 ms
PING 192.168.4.101 (192.168.4.101) 56(84) bytes of data.
64 bytes from 192.168.4.101: icmp_seq=1 ttl=64 time=0.124 ms
64 bytes from 192.168.4.101: icmp_seq=2 ttl=64 time=0.307 ms
--- 192.168.4.101 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 0.124/0.215/0.307/0.092 ms






 本文详细解读Linux中的ip命令及其子命令,包括网络概念、iptunnel隧道、接口配置、iptables规则操作等,还展示了如何在iptables中使用ipset提高效率。实例演示了网络配置与iptables策略的综合应用。
本文详细解读Linux中的ip命令及其子命令,包括网络概念、iptunnel隧道、接口配置、iptables规则操作等,还展示了如何在iptables中使用ipset提高效率。实例演示了网络配置与iptables策略的综合应用。
















 511
511

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








