1. argoCD
官网:https://argoproj.github.io/
github 地址:https://github.com/argoproj/argo-helm/tree/main/charts/argo-cd
1. 安装
1. Helm
1. 添加 repo
# 1. 添加
[root@localhost argo]# helm repo add argo-cd https://argoproj.github.io/argo-helm
# 2. 更新
[root@localhost argo]# helm repo update
# 3. 查看
[root@localhost argo]# helm search repo argo-cd | grep argo-cd/argo-cd
NAME CHART VERSION APP VERSION DESCRIPTION
argo-cd/argo-cd 5.52.0 v2.9.3 A Helm chart for Argo CD, a declarative, GitOps...
2. 编辑 values.yaml
根据自己的环境情况,添加、修改适应于自己环境的编排参数
[root@localhost argo]# cat values.yaml
server:
ingress:
enabled: true
annotations:
kubernetes.io/ingress.class: "nginx"
nginx.ingress.kubernetes.io/force-ssl-redirect: "true"
nginx.ingress.kubernetes.io/ssl-passthrough: "true"
# 后端默认启用 https , 如果禁用,同时需要修改:
# For the fist option, disable the HTTPS redirect, we will have to add the --insecure flag to server.extraArgs:
# server.extraArgs.- --insecure
nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"
hosts:
- argocd-test.local.com
http:
paths:
- backend:
serviceName: argocd-server
servicePort: 80
path: /
tls:
- secretName: test-http-cert
hosts:
- argocd-test.local.com
3. 安装
[root@localhost argo]# helm upgrade --install argocd argo-cd/argo-cd -f values.yaml -n argocd
Release "argocd" does not exist. Installing it now.
NAME: argocd
LAST DEPLOYED: Mon Aug 23 16:02:30 2021
NAMESPACE: argocd
STATUS: deployed
REVISION: 1
TEST SUITE: None
④、获取密码
[root@localhost ~]# kubectl -n argocd get secret argocd-initial-admin-secret -o jsonpath="{.data.password}" | base64 -d
⑤、登录 web
使用 values.yaml 定义的 ingress 地址进行登录即可:argocd-test.local.com
2. 使用
-
更新 charts version
如果 helm charts 版本发生更新,则需要先点击 helm release --> edit --> 版本。让其自动完成同步;
-
更新服务
点击相应的 chart,如 operation-board-php --> sync --> 选择一个具体的资源进行发布;
- status:
- outofsync: 同步(发布)资源失败;
- Synced:同步(发布)资源成功;
- health:
- degraded:
- Healthy: 正常
- status:
1. create app
Application -> NEW APP


3. 清除缓存
在 chart 编排(包括values文件)发生变化但版本号不变的情况下,argocd 不会拉取新的编排。这时需要执行以下步骤来删除缓存
1. 删除 server 记录
[root@localhost ~]# kubectl -n argocd exec -it argocd-repo-server-name sh
$ cd /tmp && ls
$ cd helmxxxx && ls
$ cd ../https_xxxx & ls
$ rm -f helm-charts-name
2. 删除 redis 记录
[root@localhost ~]# kubectl -n argocd exec -it argocd-redis-ha-server-xx sh
/data $ redis-cli
127.0.0.1:6379> keys *helm-charts-name | version-num
127.0.0.1:6379> del *helm-charts-name | version-num [key ...]
3. 重新同步
执行 argocd sync 进行同步
4. 设置
1. add helm repo
Settings -> Repositories -> Connect Repo using HTTPS and submit below details
Type : helm
Name : repo 名字
Repository URL : repo 地址
非制品库域名,是具体 repo 如: https://harbor.hai.io/chartrepo/test




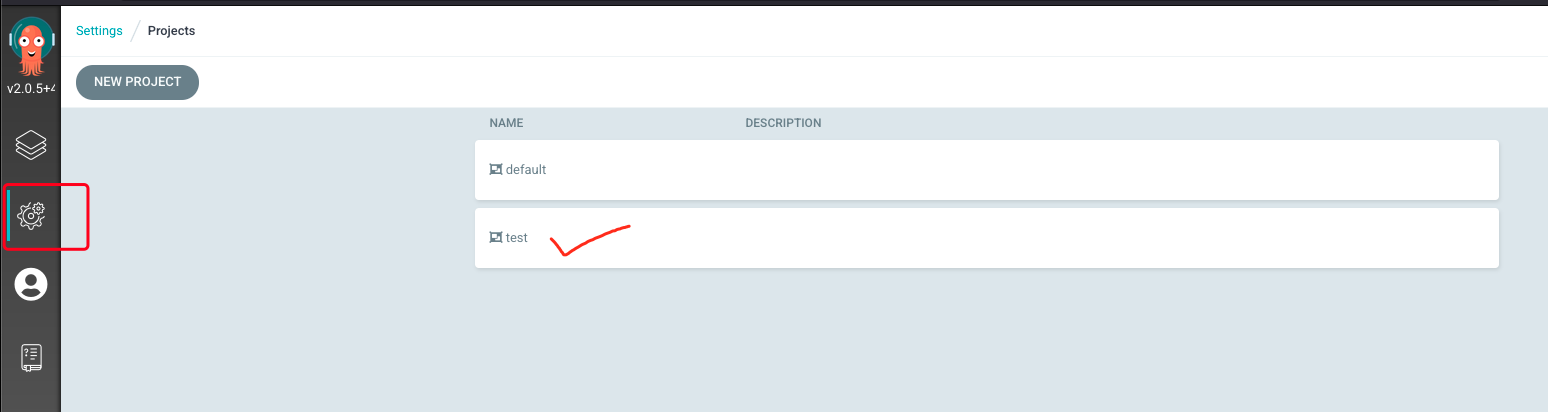
2. create project
Settings -> Projects -> NEW PROJECT

5. 客户端
1. 安装
Argo CD Git 仓库发布页面 或 使用命令获取最新版本
[root@localhost ~]# VERSION=$(curl --silent "https://api.github.com/repos/argoproj/argo-cd/releases/latest" | grep '"tag_name"' | sed -E 's/.*"([^"]+)".*/\1/')
VERSION 在下面的命令中替换为你要下载的 Argo CD 版本:
[root@localhost ~]# curl -sSL -o /usr/local/bin/argocd https://github.com/argoproj/argo-cd/releases/download/$VERSION/argocd-linux-amd64
添加执行权限
[root@localhost ~]# chmod +x /usr/local/bin/argocd
2. 服务端管理
格式:
- argocd [flags]
1. 登录
格式:
- argocd login SERVER [flags]
1. username & password
Login to Argo CD using a username and password
# 不使用 --grpc-web
[root@localhost ~]# argocd login argocd-test.hai.com
WARN[0000] Failed to invoke grpc call. Use flag --grpc-web in grpc calls. To avoid this warning message, use flag --grpc-web.
Username: admin
Password:
'admin:login' logged in successfully
Context 'argocd-test.hai.com' updated
# 使用 --grpc-web
[root@localhost ~]# argocd login argocd-test.hai.com --grpc-web
Username: admin
Password:
'admin:login' logged in successfully
Context 'argocd-test.hai.com' updated
2. SSO
Login to Argo CD using SSO
[root@localhost ~]# argocd login argocd-test.hai.com --sso
3. k8s API
Configure direct access using Kubernetes API server
[root@localhost ~]# argocd login argocd-test.hai.com --core
2. 退出
格式:
- argocd logout CONTEXT [flags]
[root@localhost ~]# argocd logout argocd-test.hai.com
Logged out from 'argocd-test.hai.com'
3. 账号
格式:
- argocd account [flags]
flags 选项:
--as string Username to impersonate for the operation --as-group stringArray Group to impersonate for the operation, this flag can be repeated to specify multiple groups. --certificate-authority string Path to a cert file for the certificate authority --client-certificate string Path to a client certificate file for TLS --client-key string Path to a client key file for TLS --cluster string The name of the kubeconfig cluster to use --context string The name of the kubeconfig context to use -h, --help help for account --insecure-skip-tls-verify If true, the server's certificate will not be checked for validity. This will make your HTTPS connections insecure --kubeconfig string Path to a kube config. Only required if out-of-cluster -n, --namespace string If present, the namespace scope for this CLI request --password string Password for basic authentication to the API server --request-timeout string The length of time to wait before giving up on a single server request. Non-zero values should contain a corresponding time unit (e.g. 1s, 2m, 3h). A value of zero means don't timeout requests. (default "0") --tls-server-name string If provided, this name will be used to validate server certificate. If this is not provided, hostname used to contact the server is used. --token string Bearer token for authentication to the API server --user string The name of the kubeconfig user to use --username string Username for basic authentication to the API server
- argocd - argocd controls a Argo CD server
- argocd account can-i - Can I
- argocd account delete-token - Deletes account token
- argocd account generate-token - Generate account token
- argocd account get - Get account details
- argocd account get-user-info - Get user info
- argocd account list - List accounts
- argocd account update-password - Update an account’s password
1. add
添加 hai 这个账号:
-
编辑 configmap
[root@localhost ~]# kubectl edit cm argocd-cm data: accounts.hai: login ## 创建了其他账号,建议禁用 admin admin.enabled: "false" -
修改密码
[root@localhost ~]# argocd account update-password --account hai *** Enter new password for user hai: *** Confirm new password for user hai: Password updated
2. get
格式:
- argocd account get [flags]
flags 选项:
-a, --account string Account name. Defaults to the current account. -h, --help help for get -o, --output string Output format. One of: json|yaml|wide|name (default "wide")
-
查看当前账号信息
[root@localhost ~]# argocd account get Name: admin Enabled: true Capabilities: login Tokens: NONE -
查看指定账号信息
[root@localhost ~]# argocd account get -a admin Name: admin Enabled: true Capabilities: login Tokens: NONE
3. list
格式:
- argocd account list [flags]
flags 选项:
-h, --help help for list -o, --output string Output format. One of: json|yaml|wide|name (default "wide")
-
列出账号
[root@localhost ~]# argocd account list NAME ENABLED CAPABILITIES admin true login
4. get-user-info
格式:
- argocd account get-user-info [flags]
flags 选项:
-h, --help help for get-user-info -o, --output string Output format. One of: yaml, json
[root@localhost ~]# argocd account get-user-info
Logged In: true
Username: admin
Issuer: argocd
Groups:
5. generate-token
格式:
- argocd account generate-token [flags]
flags 选项:
-a, --account string Account name. Defaults to the current account. -e, --expires-in string Duration before the token will expire. (Default: No expiration) (default "0s") -h, --help help for generate-token --id string Optional token id. Fall back to uuid if not value specified.
[root@localhost ~]# argocd account generate-token
FATA[0000] rpc error: code = Unknown desc = account 'admin' does not have apiKey capability
# Generate token for the currently logged in account
[root@localhost ~]# argocd account generate-token
# Generate token for the account with the specified name
[root@localhost ~]# argocd account generate-token --account <account-name>
ps: 问题:
- does not have apikey acpability
解决方案
6. delete-token
格式:
- argocd account delete-token [flags]
flags 选项:
-a, --account string Account name. Defaults to the current account. -h, --help help for delete-token
# Delete token of the currently logged in account
[root@localhost ~]# argocd account delete-token ID
# Delete token of the account with the specified name
[root@localhost ~]# argocd account delete-token --account <account-name> ID
7. update-password
格式:
- argocd account update-password [flags]
flags 选项:
--account string an account name that should be updated. Defaults to current user account --current-password string password of the currently logged on user -h, --help help for update-password --new-password string new password you want to update to
# Update the current user's password
[root@localhost ~]# argocd account update-password
# Update the password for user foobar
[root@localhost ~]# argocd account update-password --account foobar
4.权限控制
初始化时的权限:
data:
accounts.admin: apiKey
admin.enabled: "true"
application.instanceLabelKey: argocd.argoproj.io/instance
exec.enabled: "false"
server.rbac.log.enforce.enable: "false"
1. 编辑 configmap
[root@localhost ~]# kubectl edit cm argocd-rbac-cm
2. 修改权限
格式:
- p, role:用户名, 资源, 方法, 项目, 权限
- p, 用户名, 资源 , 方法, 项目, 权限
- g,
参数:
- 资源:
clusters,projects,applications,repositories,certificates,accounts,gpgkeys- 方法:
get,create,update,delete,sync,override,action- 权限:
allow,deny
data:
policy.csv: |
p, dev, applications, get, test/*, deny
p, dev_viewer, applications, get, */*, allow
p, dev_admin, *, *, */*, allow
p, dev_admin, projects, *, *, allow
p, test_admin, applications, *, test/*, allow
p, test_admin, certificates, *, *, allow
p, test_admin, clusters, *, *, allow
p, test_admin, repositories, *, *, allow
p, test_admin, projects, *, test, allow
p, test_admin, accounts, *, *, allow
p, test_admin, gpgkeys, get, *, allow
p, test_readonly, applications, get, test/*, allow
policy.default: role:readonly
案例一:
https://github.com/argoproj/argo-cd/blob/master/docs/operator-manual/argocd-rbac-cm.yaml
data:
# policy.csv is an file containing user-defined RBAC policies and role definitions (optional).
# Policy rules are in the form:
# p, subject, resource, action, object, effect
# Role definitions and bindings are in the form:
# g, subject, inherited-subject
# See https://github.com/argoproj/argo-cd/blob/master/docs/operator-manual/rbac.md for additional information.
policy.csv: |
# Grant all members of the group 'my-org:team-alpha; the ability to sync apps in 'my-project'
p, my-org:team-alpha, applications, sync, my-project/*, allow
# Grant all members of 'my-org:team-beta' admins
g, my-org:team-beta, role:admin
# policy.default is the name of the default role which Argo CD will falls back to, when
# authorizing API requests (optional). If omitted or empty, users may be still be able to login,
# but will see no apps, projects, etc...
policy.default: role:readonly
# scopes controls which OIDC scopes to examine during rbac enforcement (in addition to `sub` scope).
# If omitted, defaults to: '[groups]'. The scope value can be a string, or a list of strings.
scopes: '[cognito:groups, email]'
# matchMode configures the matchers function for casbin.
# There are two options for this, 'glob' for glob matcher or 'regex' for regex matcher. If omitted or mis-configured,
# will be set to 'glob' as default.
policy.matchMode: 'glob'
3.验证权限
https://github.com/argoproj/argo-cd/blob/master/docs/operator-manual/rbac.md
支持多种格式: csv, yaml,
- 本地
[root@localhost ~]# argocd admin settings rbac validate --policy-file somepolicy.csv
[root@localhost ~]# argocd admin settings rbac validate --namespace argocd
4. 测试权限
格式:argocd admin settings rbac can SOMEROLE ACTION RESOURCE SUBRESOURCE [flags]
[root@localhost ~]# argocd admin settings rbac can role:org-admin get applications --policy-file argocd-rbac-cm.yaml
Yes
[root@localhost ~]# argocd admin settings rbac can role:org-admin get clusters --policy-file argocd-rbac-cm.yaml
Yes
[root@localhost ~]# argocd admin settings rbac can role:org-admin create clusters 'somecluster' --policy-file argocd-rbac-cm.yaml
No
[root@localhost ~]# argocd admin settings rbac can role:org-admin create applications 'someproj/someapp' --policy-file argocd-rbac-cm.yaml
Yes
# Plain policy, without a default role defined
[root@localhost ~]# argocd admin settings rbac can role:staging-db-admins get applications --policy-file policy.csv
No
[root@localhost ~]# argocd admin settings rbac can role:staging-db-admins get applications 'staging-db-admins/*' --policy-file policy.csv
Yes
# Argo CD augments a builtin policy with two roles defined, the default role
# being 'role:readonly' - You can include a named default role to use:
[root@localhost ~]# argocd admin settings rbac can role:staging-db-admins get applications --policy-file policy.csv --default-role role:readonly
Yes
[root@localhost ~]# argocd admin settings rbac can db-admins get applications 'staging-db-admins/*' --policy-file policy.csv
Yes
5. 验证 argocd 中的权限
[root@localhost ~]# argocd admin settings rbac validate --namespace argocd
案例
3. repo 管理
格式:
- argocd repo [flags]
- argocd - argocd controls a Argo CD server
- argocd repo add - Add git repository connection parameters
- argocd repo get - Get a configured repository by URL
- argocd repo list - List configured repositories
- argocd repo rm - Remove repository credentials
1. 添加 repo
[root@localhost ~]# argocd repo add http://git.test.com/project/test.git --username admin --password 123456
2.
再添加需要发布的项目像之前一样
[root@localhost ~]# argocd app create test --repo http://git.test.com/project/test.git --path test --dest-server https://kubernetes.default.svc --dest-namespace default
3. 查看 repo
[root@localhost ~]# argocd repo list
TYPE NAME REPO INSECURE OCI LFS CREDS STATUS MESSAGE PROJECT
git http://git.test.com/project/test/repo false false false true Successful
4. 删除 repo
[root@localhost ~]# argocd repo rm http://git.test.com/project/test/repo
4. app 管理
格式:
- argocd app [flags]
1. 创建 app
创建 app 有以下两种方式
1. git 仓库
创建一个 test-app ,指定仓库地址、应用路径、目标apiserver地址、目标namespace
argocd app create test-app --repo http://git.test.com/project/test.git --path test00 --dest-server https://kubernetes.default.svc --dest-namespace default
2. helm
- Helm Release Name 设置
apiVersion: argoproj.io/v1alpha1
kind: Application
metadata:
name: sealed-secrets
namespace: argocd
spec:
project: default
source:
chart: sealed-secrets
repoURL: http://git.test.com/project/test
targetRevision: 1.16.1
helm:
releaseName: sealed-secrets # 指定的 Release Name 值
destination:
server: "https://kubernetes.default.svc"
namespace: kubeseal
2. 查看 app
1. 所有
[root@localhost ~]# argocd app list
2. 指定
查看 test-app
[root@localhost ~]# argocd app get test-app
3. 同步 app
主要是作用是,将 app 部署到 k8s 集群中
[root@localhost ~]# argocd app sync test-app
4. 修改参数
[root@localhost ~]# argocd app set test-app -p image.tag=v1.0.1
5. 删除 app
[root@localhost ~]# argocd app delete test-app
5. cluster 管理
https://github.com/argoproj/argo-cd/blob/master/docs/user-guide/commands/argocd_cluster.md
格式:
- argocd cluster [flags]
1. 查看
[root@localhost ~]# argocd cluster list -o json
2. 添加
[root@localhost ~]# argocd cluster add example-cluster
[root@localhost ~]# argocd cluster add ${kube-context} --kubeconfig ${dev-config} --name dev
3. 删除
[root@localhost ~]# argocd cluster rm example-cluster
6. 概念
1. 架构图
https://argoproj.github.io/argo-cd/

2. 组件
1. API 服务
API 服务是一个 gRPC/REST 服务,它暴露了 Web UI、CLI 和 CI/CD 系统使用的接口,主要有以下几个功能:
- 应用程序管理和状态报告
- 执行应用程序操作(例如同步、回滚、用户定义的操作)
- 存储仓库和集群凭据管理(存储为 K8S Secrets 对象)
- 认证和授权给外部身份提供者
- RBAC
- Git webhook 事件的侦听器/转发器
2. 仓库服务
存储仓库服务是一个内部服务,负责维护保存应用程序清单 Git 仓库的本地缓存。当提供以下输入时,它负责生成并返回 Kubernetes 清单:
- 存储 URL
- revision 版本(commit、tag、branch)
- 应用路径
- 模板配置:参数、ksonnet 环境、helm values.yaml 等
3. 应用控制器
应用控制器是一个 Kubernetes 控制器,它持续 watch 正在运行的应用程序并将当前的实时状态与所期望的目标状态( repo 中指定的)进行比较。它检测应用程序的 OutOfSync 状态,并采取一些措施来同步状态,它负责调用任何用户定义的生命周期事件的钩子(PreSync、Sync、PostSync)。
3. 功能
- 自动部署应用程序到指定的目标环境
- 支持多种配置管理/模板工具(Kustomize、Helm、Ksonnet、Jsonnet、plain-YAML)
- 能够管理和部署到多个集群
- SSO 集成(OIDC、OAuth2、LDAP、SAML 2.0、GitHub、GitLab、Microsoft、LinkedIn)
- 用于授权的多租户和 RBAC 策略
- 回滚/随时回滚到 Git 存储库中提交的任何应用配置
- 应用资源的健康状况分析
- 自动配置检测和可视化
- 自动或手动将应用程序同步到所需状态
- 提供应用程序活动实时视图的 Web UI
- 用于自动化和 CI 集成的 CLI
- Webhook 集成(GitHub、BitBucket、GitLab)
- 用于自动化的 AccessTokens
- PreSync、Sync、PostSync Hooks,以支持复杂的应用程序部署(例如蓝/绿和金丝雀发布)
- 应用程序事件和 API 调用的审计
- Prometheus 监控指标
- 用于覆盖 Git 中的 ksonnet/helm 参数
4. 核心概念
- Application:应用,一组由资源清单定义的 Kubernetes 资源,这是一个 CRD 资源对象
- Application source type:用来构建应用的工具
- Target state:目标状态,指应用程序所需的期望状态,由 Git 存储库中的文件表示
- Live state:实时状态,指应用程序实时的状态,比如部署了哪些 Pods 等真实状态
- Sync status:同步状态表示实时状态是否与目标状态一致,部署的应用是否与 Git 所描述的一样?
- Sync:同步指将应用程序迁移到其目标状态的过程,比如通过对 Kubernetes 集群应用变更
- Sync operation status:同步操作状态指的是同步是否成功
- Refresh:刷新是指将 Git 中的最新代码与实时状态进行比较,弄清楚有什么不同
- Health:应用程序的健康状况,它是否正常运行?能否为请求提供服务?
- Tool:工具指从文件目录创建清单的工具,例如 Kustomize 或 Ksonnet 等
- Configuration management tool:配置管理工具
- Configuration management plugin:配置管理插件
10. 错误集
1. Unable to create application
Unable to create application: application references project dashboard which does not exist
解决方案:一
需要先创建 project, 请参考【4. 设置】节。
https://argoproj.github.io/argo-cd/user-guide/projects/
https://github.com/argoproj/argo-cd/issues/1411
2. Failed to load data
Unable to load data: Request has been terminated Possible causes: the network is offline, Origin is not allowed by Access-Control-Allow-Origin, the page is being unloaded, etc

解决方案:一
通过 argocd-server 日志进行跟踪;
[root@localhost ~]$ kubectl get po -n argocd
NAME READY STATUS RESTARTS AGE
argocd-application-controller-74cdb5d457-lblgj 1/1 Running 0 40h
argocd-dex-server-64b659bb9d-2trl6 1/1 Running 0 40h
argocd-redis-54d5b56c99-gks79 1/1 Running 0 41d
argocd-repo-server-575599bd9d-qpx9k 1/1 Running 0 40h
argocd-server-847f4b6c59-g9zt7 1/1 Running 0 108s
[root@localhost ~]$ kubectl logs -f --tail=5 argocd-server-847f4b6c59-g9zt7 -n argocd
time="2021-09-28T02:58:14Z" level=warning msg="Failed to resync revoked tokens. retrying again in 1 minute: dial tcp 10.101.161.213:6379: i/o timeout"
6379 是 redis 服务的端口地址,因此认为是 redis 服务问题。
因为是测试环境,没有细查,直接删除 redis 容器,状态恢复。
3. Unable to create application
Unable to create application: application spec is invalid: InvalidSpecError: repository not accessible: Get “https://harbor.cpdf.io:4430/chartrepo/dashboard/index.yaml”: dial tcp: lookup harbor.cpdf.io on 10.96.0.10:53: read udp 10.244.0.4:46401->10.96.0.10:53: i/o timeout
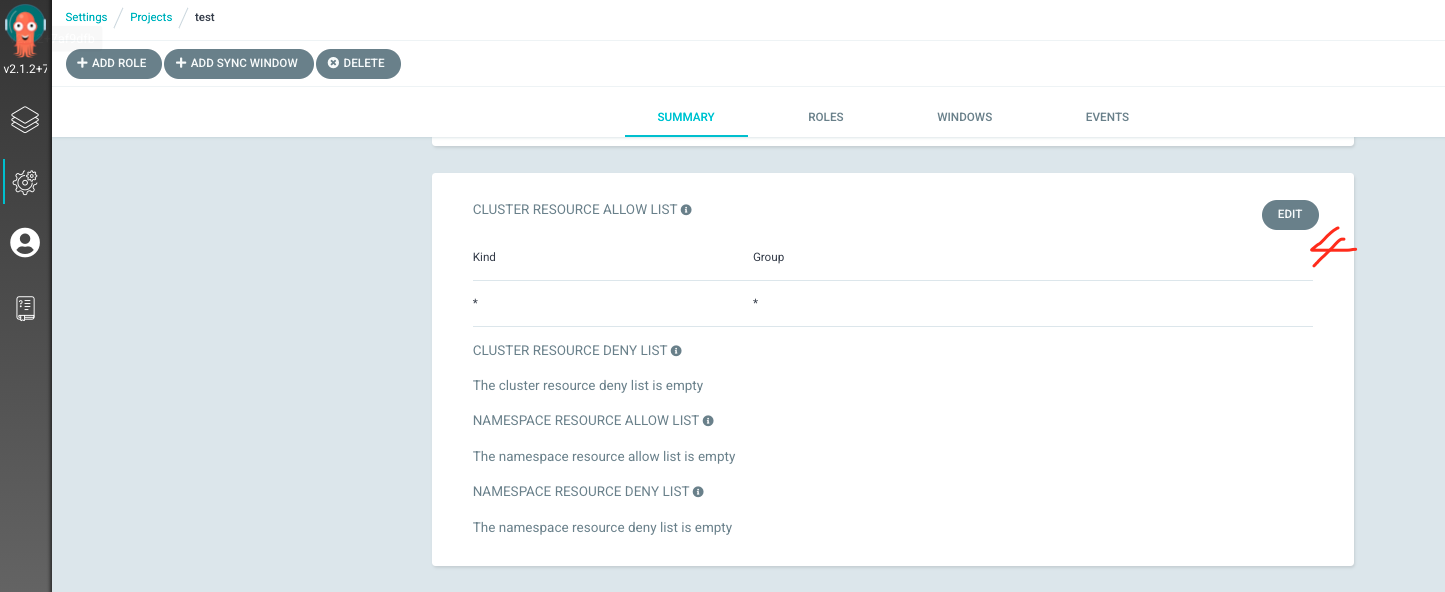
4. application destination xxx is not permitted in project ‘xxx’
Unable to create application: application spec is invalid: InvalidSpecError: application destination {https://kubernetes.default.svc test} is not permitted in project ‘test’
5. xxx is not permitted in project test.
Resource apps:Deployment is not permitted in project test.
Resource :Service is not permitted in project test.
Resource :ServiceAccount is not permitted in project test.

解决方案:一
Settings -> Projects -> proecte-name -> CLUSTER RESOURCE ALLOW LIST -> EDIT -> ADD RESOURCE
根据需要打开相应权限;



6. Unable to create application
Unable to create application: application spec for test-app is invalid: InvalidSpecError: application destination {https://kubernetes.default.svc test} is not permitted in project ‘test’
7. no session information
详细信息:
finished unary call with code Unauthenticated" error="rpc error: code = Unauthenticated desc = no session information
解决方案:一
https://github.com/argoproj/argo-cd/issues/2968
Thanks for the response @alexmt,
it might not have been obvious in my original post but that setting is
actually already in the config, as is --insecure. My config looks like:
- argocd-server
- --staticassets
- /shared/app
- --basehref
- /argo-cd
- --insecure
同时向后端的代理也需要修改为
# nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"


























 645
645











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








