因为安全需要,要求在测试机Apache服务器配置js脚本过滤功能,参考已经配置成功其他服务器的Apache,进入如下配置
1放开
LoadModule security2_module modules/mod_security2.so
LoadModule unique_id_module modules/mod_unique_id.so
2添加配置
<IfModule security2_module>
SecRuleEngine On
#SecRequestBodyAccess On
SecRequestBodyNoFilesLimit 5242880
SecAuditEngine RelevantOnly
SecAuditLog logs/audit/audit.log
SecAuditLogParts ABCFHZ
SecDebugLog logs/sec.log
SecDebugLogLevel 1
SecAuditLogType Serial
SecAuditLogStorageDir logs/audit
SecAuditLogRelevantStatus ^(?:5|4(?!04))
SecRule REQUEST_URI "<script" nolog,deny,status:404
SecRule REQUEST_URI "<\s+script\s" nolog,deny,status:404
SecRule REQUEST_URI "<{|}*script" nolog,deny,status:404
SecRule REQUEST_URI "<.+>" nolog,deny,status:404
SecRule REQUEST_URI "'.+'" nolog,deny,status:404
SecRule REQUEST_URI "%3E.+%3C" nolog,deny,status:404
SecRule REQUEST_BODY "%3E.+%3C" nolog,deny,status:404
SecRule REQUEST_BODY "<.+>" nolog,deny,status:404
SecRule REQUEST_BODY "<{|}*script" nolog,deny,status:404
SecRule REQUEST_BODY "'.+'" nolog,deny,status:404
SecRule REQUEST_BODY "%3E" nolog,deny,status:404
SecRule REQUEST_URI "alert" nolog,deny,status:404
SecRule REQUEST_URI "onMouseOver" nolog,deny,status:404
SecRule REQUEST_URI "onmouseover" nolog,deny,status:404
SecRule REQUEST_URI "onclick" nolog,deny,status:404
SecRule REQUEST_URI "onfocus" nolog,deny,status:404
SecRule REQUEST_COOKIES "<{|}*script" nolog,deny,status:404
SecRule REQUEST_COOKIES|REQUEST_URI|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* "(?i:(\!\=|\&\&|\|\||>>|<<|>=|<=|<>|<=>|\sxor\s|\srlike\s|\sregexp\s|\sisnull)|(?:not\s+between\s+0\s+and)|(?:\sis\s+null)|(\slike\s+null)|(?:(?:^|\W)in[+\s]*\([\s\d\"]+[^()]*\))|(?:\sxor\s|<>|\srlike(?:\s+binary)?)|(?:\sregexp\s+binary\s))" "phase:2,rev:'2.2.2',capture,t:none,t:urlDecodeUni,block,msg:'SQL Injection Attack: SQL Operator Detected',id:'981212',logdata:'%{TX.0}',severity:'2',tag:'WEB_ATTACK/SQL_INJECTION',tag:'WASCTC/WASC-19',tag:'OWASP_TOP_10/A1',tag:'OWASP_AppSensor/CIE1',tag:'PCI/6.5.2',setvar:'tx.msg=%{rule.msg}',setvar:tx.sql_injection_score=+%{tx.notice_anomaly_score},setvar:tx.anomaly_score=+%{tx.notice_anomaly_score},setvar:tx.%{rule.id}-WEB_ATTACK/SQL_INJECTION-%{matched_var_name}=%{tx.0}"
执行Apache关闭命令:
./apachectl stop报错:
找不到mod_unique_id
从其他服务器的Apache文件夹下拷贝module文件夹到本服务器,再执行Apache关闭命令,报错
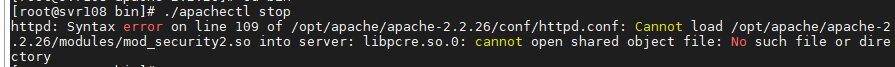
寻找libpcre.so.o 在/usr/lib64目录下找到

libpcre.so.0一直在闪烁,应该是关联的不对,删除libpcre.so.o,重新关联,执行以下命令
ln -s libpcre.so.1.2.0 libpcre.so.0然后再执行Apache关闭命令,报错
![]()
自己手动在Apache目录下创建对应的/logs/audit/audit.log
再执行Apache重启命令,成功!






















 918
918











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








