OpenSSH服务器
SSH (Secure Shell)协议
是一种安全通道协议
对通信数据进行了加密处理,用于远程管理
OpenSSH
服务名称: sshd
服务端主程序:/usr/sbin/sshd
服务端配置文件:/etclssh/sshd_config
客户端配置文件:letc/ssh/ssh_config
查看ssh配置文件
vim /etc/ssh/sshd.config.
查看服务端配置文件
rpm -ql openssh-server
查看客户端配置文件
rpm -ql openssh-cliente
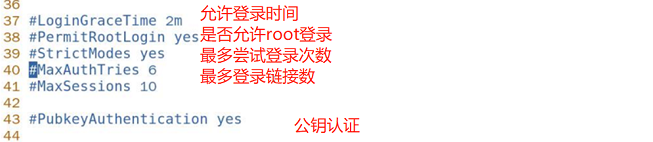
配置
vim /etc/ssh/sshd_conf
wq保存退出,重启
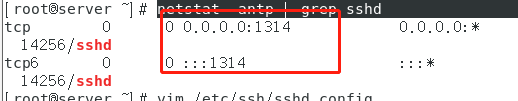
netstat -antp | grep sshd查看,确认更改成功
SSH登录验证方式
密码认证:以服务器中本地系统用户的登录名称,密码进行认证,这种方式安全性较低
密钥对验证:要求提供相匹配的密钥(公钥,私钥)来通过验证,分为两种
1)对称加密:采用单密钥系统加密方法,同一密钥用于信息的加密和解密,优点加密速度和效率很快,缺点是容易被破解,不是很安全
2)非对称加密:采用公开密钥和私有密钥两种密钥加密,两种密钥成对生成,可以互相加密解密,公钥对外公开,私钥只有持有人才知道

systemctl stop firewalld.service
setenforce 0
hostname client
bash
ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.43.130 netmask 255.255.255.0 broadcast 192.168.43.255
inet6 fe80::4066:d678:639c:dea5 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:3f:67:c5 txqueuelen 1000 (Ethernet)
RX packets 2027 bytes 136282 (133.0 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 140 bytes 15043 (14.6 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
hostname server
bash
ifconfig ens33
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.43.134 netmask 255.255.255.0 broadcast 192.168.43.255
inet6 fe80::792f:d024:3150:cf1d prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:39:c8:59 txqueuelen 1000 (Ethernet)
RX packets 596521 bytes 853526819 (813.9 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 284209 bytes 17465397 (16.6 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
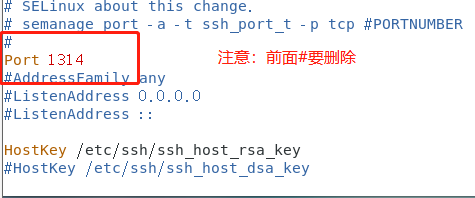
在server上更改其监听端口,然后再client上远程登录
[root@server ~]# vim /etc/ssh/sshd_config
[root@server ~]# systemctl restart sshd
[root@server ~]# sshd -t //检测ssh配置文件是否有问题
[root@client ~]# ssh root@192.168.43.134
ssh: connect to host 192.168.43.134 port 22: Connection refused
## 由于我将监听端口改了,这里登录就会提示错误
[root@client ~]# ssh root@192.168.43.134 -p 22222 //选择监听端口登录
The authenticity of host '[192.168.43.134]:22222 ([192.168.43.134]:22222)' can't be established.
ECDSA key fingerprint is SHA256:G4jGohs1sfhoMuJpM0FY5/ufm07Ja9r1KD/FJXPYB+0.
ECDSA key fingerprint is MD5:b7:6e:0f:c0:f4:96:39:6b:dc:44:6f:ee:2f:20:6c:3a.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '[192.168.43.134]:22222' (ECDSA) to the list of known hosts.
root@192.168.43.134's password: //这里输入server端root的密码
Last login: Thu Apr 1 19:13:16 2021 from 192.168.43.1
[root@server ~]# ssh root@192.168.43.130 //这里注意,上面改的是client的监听端口,server的没变,这里就不需要指定端口登录
The authenticity of host '192.168.43.130 (192.168.43.130)' can't be established.
ECDSA key fingerprint is SHA256:eovMAnt+xfqaf1Ctf+g9n4fvwFWVIGDSt7XPmuFFiu0.
ECDSA key fingerprint is MD5:45:53:86:7b:00:cd:f0:d6:a6:49:a5:e0:de:ec:44:15.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.43.130' (ECDSA) to the list of known hosts.
root@192.168.43.130's password: //一次
Permission denied, please try again. //两次
root@192.168.43.130's password:
Permission denied, please try again.
root@192.168.43.130's password: //三次
Permission denied (publickey,gssapi-keyex,gssapi-with-mic,password).
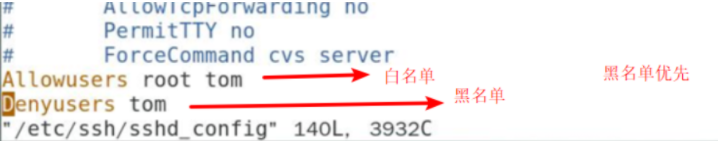
添加黑白名单,白名单存在时只能该名单内的远程登录,黑名单存在时该名单内的不能远程登录,两个名单同时存在时以黑名单为主
[root@client ~]# vim /etc/ssh/sshd_config
[root@client ~]# ssh-keygen //先生成公钥,后面可以加-t跟算法,自己选择算法
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa): //表示密钥放置位置,回车即可
Enter passphrase (empty for no passphrase):
#### 表示私钥是否需要口令,需要就输入密码即可,我这里就不设置了,回车确认
Enter same passphrase again: //回车即可
。。。。。。。。。
root@192.168.43.134's password: //输入server端root的密码
Number of key(s) added: 1
Now try logging into the machine, with: "ssh -p '22222' 'root@192.168.43.134'"
and check to make sure that only the key(s) you wanted were added.
在server上查看推送过来的公钥
[root@server ~]# cd .ssh
[root@server .ssh]# ls
authorized_keys known_hosts
cat authorized_keys //此文件记录推送过来的公钥
再次在client端远程登录server
[root@client .ssh]# ssh -p 22222 root@192.168.43.134 //下面就不需要密码了
Last login: Tue May 25 15:36:18 2021 from 192.168.43.1






















 1317
1317











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








