按照spring websocket的教材搭建了一个websocket的测试程序,但是自定义的HandshakeInterceptor 类型拦截器,始终获取不到httpsession,如下图,获取到得httpsession始终为null,
public class WebSocketHandshakeInterceptor implements HandshakeInterceptor {
private static Log logger = LogFactory.getLog(HandshakeInterceptor.class);
@Override
public boolean beforeHandshake(ServerHttpRequest request, ServerHttpResponse response, WebSocketHandler wsHandler, Map<String, Object
> attributes) throws Exception {
logger.debug("beforeHandshake start.....");
logger.debug(request.getClass().getName());
if (request instanceof ServletServerHttpRequest) {
ServletServerHttpRequest servletRequest = (ServletServerHttpRequest) request;
HttpSession session = servletRequest.getServletRequest().getSession(false);
if (session != null) {
//使用userName区分WebSocketHandler,以便定向发送消息
String userName = (String) session.getAttribute(Constants.SESSION_USERNAME);
logger.info(userName+" login");
attributes.put(Constants.WEBSOCKET_USERNAME,userName);
}else{
logger.debug("httpsession is null");
}
}
return true;
}
@Override
public void afterHandshake(ServerHttpRequest request, ServerHttpResponse response, WebSocketHandler wsHandler, Exception exception) {
}
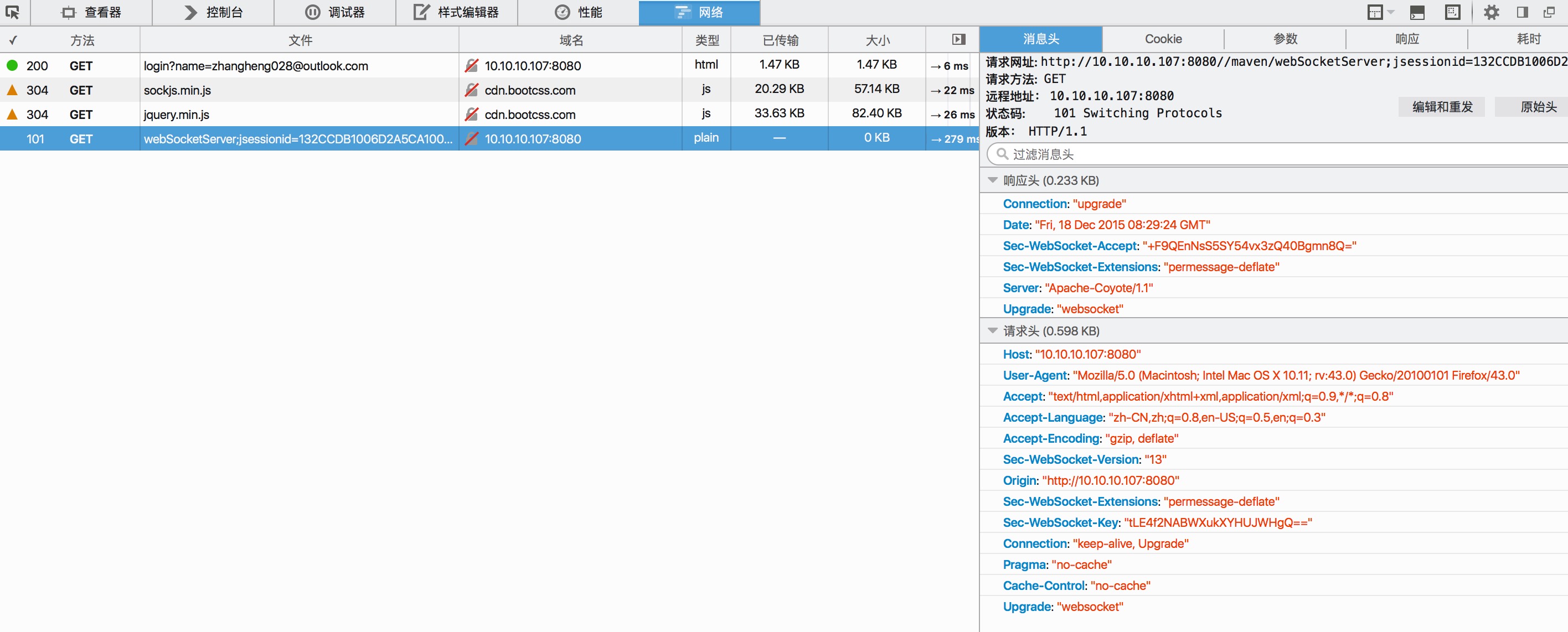
}查看浏览器的http请求
发现websocket的握手请求没有携带cookie信息,没有cookie。。。 就没有sessionId,那服务器怎么可能识别到是哪个httpsession呢,
所以在websocket链接后加上jsessionid,这样服务器就可以根据sessionid获取到httpsession了,
http://10.10.10.107:8080//maven/webSocketServer;jsessionid=132CCDB1006D2A5CA1002368647D3672
虽然url携带jsessionid是个不太安全的做法,但是无奈只想到这种方式处理,姑且用之,
哪位大神有更加可靠的方式,望指点,不胜感激。
附上源代码,代码在tomcat8下测试通过





















 3767
3767

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








