一、环境搭建
在phpstudy这一集成环境中搭建此漏洞练习靶场
(1)下载链接:
https://sourceforge.net/projects/bwapp/files/latest/download
(2)安装步骤:
- 下载后解压文件,将文件放在WWW目录下
- 在admin/settings.php下更改数据库连接设置
username和password设置成自己数据库的用户名和密码

3. 运行PHPStudy,然后在浏览器打开http://127.0.0.1/bWAPP/install.php
点击here创建数据库
4. 安装成功,进入靶场主界面
输入用户名(bee)和密码(bug)

二、开始做题
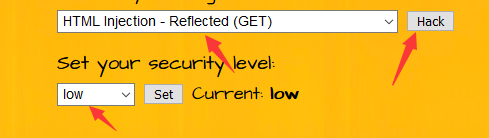
HTML Injection - Reflected (GET)
那我们直接开始第一题吧
这里有两个框让我们输入,先看看源码

这里把我们输入的fistname和lastname直接带进htmli了

Htmli是按照我们等级来给函数的,我们看看no_check函数

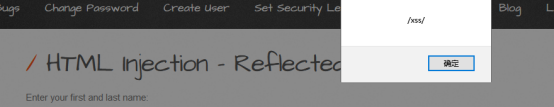
没有过滤就直接输入了,所以我们直接输入xss代码即可
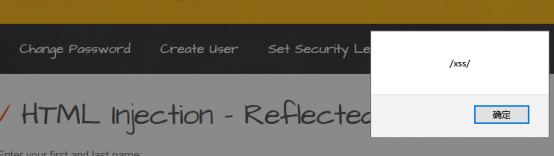
<script>alert(/xss/)</script>

我们再把难度设置成medium也就是中等难度
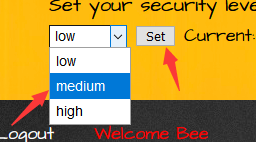
这里用了把尖括号换成实体了,但是用了urldecode函数,我们可以把代码先编码成url形式再输入进去

%3cscript%3ealert(%2fxss%2f)%3c%2fscript%3e
再把难度设置成高
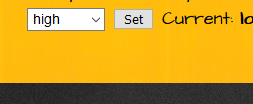
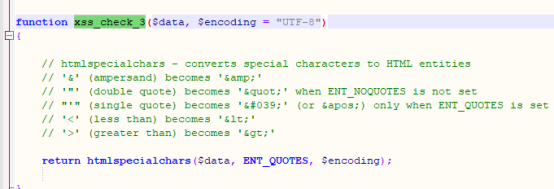
看看源码,这里把我们的符号都设置成实体了,所以这是安全的
HTML Injection - Reflected (POST)
这关和上一关是一样的就是换成了POST运输过来了,这里就不一一说明了


HTML Injection - Reflected (URL)
low
我们可以发现通关url可以传输,所以我们在url中构造语句

但是由于url栏里直接构造代码会被进行url编码,所以通过burp抓包来修改url信息进行提交请求

在burp抓到的包里修改url,如图所示


好,成功了
medium&&High
查看源代码
 这个就是过滤条件了,可以看到对发出请求的url包进了
这个就是过滤条件了,可以看到对发出请求的url包进了<script></script>>里,无法绕过,说明此过滤方式可以保证页面防御XSS攻击的安全性。
高等也是如此,中等和高等都无法绕过,是安全的
HTML Injection - Stored (Blog)
 LOW
LOW

查看源码
<?php
/*
bWAPP, or a buggy web application, is a free and open source deliberately insecure web application.
It helps security enthusiasts, developers and students to discover and to prevent web vulnerabilities.
bWAPP covers all major known web vulnerabilities, including all risks from the OWASP Top 10 project!
It is for security-testing and educational purposes only.
Enjoy!
Malik Mesellem
Twitter: @MME_IT
bWAPP is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License (http://creativecommons.org/licenses/by-nc-nd/4.0/). Copyright © 2014 MME BVBA. All rights reserved.
*/
include("security.php");
include("security_level_check.php");
include("selections.php");
include("functions_external.php");
include("connect_i.php");
$entry = "";
$owner = "";
$message = "";
function htmli($data)
{
include("connect_i.php");
switch($_COOKIE["security_level"])
{
case "0" :
$data = sqli_check_3($link, $data);
break;
case "1" :
$data = sqli_check_3($link, $data);
// $data = xss_check_4($data);
break;
case "2" :
$data = sqli_check_3($link, $data);
// $data = xss_check_3($data);
break;
default :
$data = sqli_check_3($link, $data);
break;
}
return $data;
}
if(isset($_POST["entry_add"]))
{
$entry = htmli($_POST["entry"]);
$owner = $_SESSION["login"];
if($entry == "")
{
$message = "<font color=\"red\">Please enter some text...</font>";
}
else
{
$sql = "INSERT INTO blog (date, entry, owner) VALUES (now(),'" . $entry . "','" . $owner . "')";
$recordset = $link->query($sql);
if(!$recordset)
{
die("Error: " . $link->error . "<br /><br />");
}
// Debugging
// echo $sql;
$message = "<font color=\"green\">Your entry was added to our blog!</font>";
}
}
else
{
if(isset($_POST["entry_delete"]))
{
$sql = "DELETE from blog WHERE owner = '" . $_SESSION["login"] . "'";
$recordset = $link->query($sql);
if(!$recordset)
{
die("Error: " . $link->error . "<br /><br />");
}
// Debugging
// echo $sql;
$message = "<font color=\"green\">All your entries were deleted!</font>";
}
}
?>
<!DOCTYPE html>
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<!--<link rel="stylesheet" type="text/css" href="https://fonts.googleapis.com/css?family=Architects+Daughter">-->
<link rel="stylesheet" type="text/css" href="stylesheets/stylesheet.css" media="screen" />
<link rel="shortcut icon" href="images/favicon.ico" type="image/x-icon" />
<!--<script src="//html5shiv.googlecode.com/svn/trunk/html5.js"></script>-->
<script src="js/html5.js"></script>
<title>bWAPP - HTML Injection</title>
</head>
<body>
<header>
<h1>bWAPP</h1>
<h2>an extremely buggy web app !</h2>
</header>








 本文介绍了在phpstudy环境下搭建bWAPP靶场的过程,并详细讲解了不同难度级别的HTML注入漏洞,包括Reflected (GET, POST, URL)和Stored (Blog)四种情况,探讨了过滤机制和XSS攻击的防范策略。"
91417941,7691641,使用commix进行命令注入渗透测试详解,"['命令注入', '渗透测试', '网络安全']
本文介绍了在phpstudy环境下搭建bWAPP靶场的过程,并详细讲解了不同难度级别的HTML注入漏洞,包括Reflected (GET, POST, URL)和Stored (Blog)四种情况,探讨了过滤机制和XSS攻击的防范策略。"
91417941,7691641,使用commix进行命令注入渗透测试详解,"['命令注入', '渗透测试', '网络安全']
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 2062
2062











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








