利用已经封装好的AES加密算法,实现CBC模式解密和CTR模式解密。
(1)CBC解密
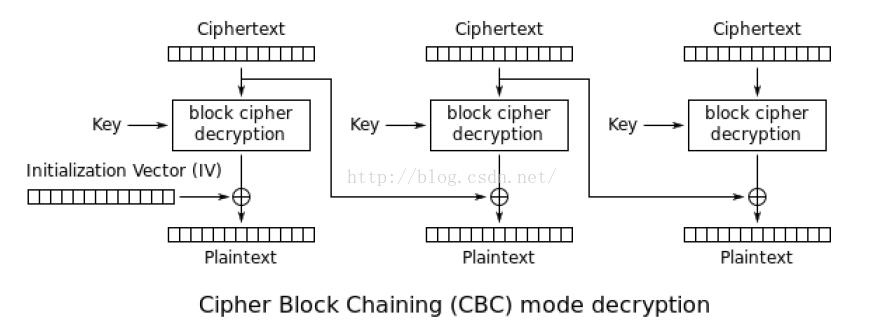
如图,CBC模式的解密,步骤主要有三个,首先是拿密文段逐一放到AES解密盒子里面得到一个结果temp(事先要把密文先裁剪成若干段);然后拿IV或者上一段密文段与temp进行异或,得到明文段;最后将明文段串合起来得到明文。注意事先所给的密文最后面有可能有若干位补码(因为非16倍数没法平均切分自然也没法放到AES解密块中解密),为了补满16的倍数补了一些奇怪的字符,这个不用管它。
(2)CTR解密
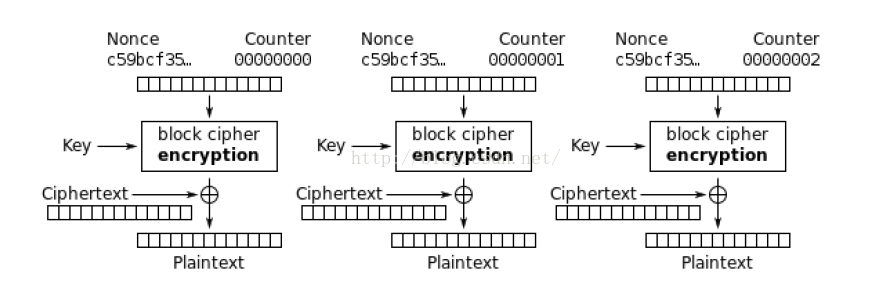
CTR的解密步骤和CBC的类似,主要的不同在于它用的是AES的加密模块来解密,而CBC用的是AES解密模块,同时CTR它是对初始向量IV每次加一之后放进AES模块里面,而不像CBC解密放进去的是密文段。最后得到的temp结果拿它和密文段进行异或即可得到明文段。所以代码跟CBC的自然也差不多,只需要进行小部分的改动即可。
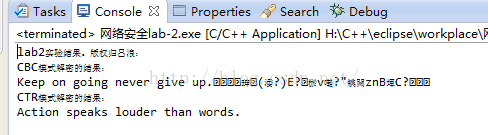
先上运行结果(eclipse)再上代码:
代码(AES.h和AES.cpp版权归小杰大神,其余归笔者):
(1)main.cpp
/*
* main.cpp
*
* Created on: 2016年3月24日
* Author: Lv_Lang
*/
#include <stdio.h>
//#include "AES.h"
#include "CBC.h"
#include "CTR.h"
void test_CBC()
{
Byte key[16] = {
0x14, 0x0b, 0x41, 0xb2, 0x2a, 0x29, 0xbe, 0xb4, 0x06, 0x1b, 0xda, 0x66, 0xb6, 0x74, 0x7e, 0x14
};
Byte IV[16] = {
0x4c, 0xa0, 0x0f, 0xf4, 0xc8, 0x98, 0xd6, 0x1e, 0x1e, 0xdb, 0xf1, 0x80, 0x06, 0x18, 0xfb, 0x28
};
Byte stream[100] = {
//0x4c, 0xa0, 0x0f, 0xf4, 0xc8, 0x98, 0xd6, 0x1e, 0x1e, 0xdb, 0xf1, 0x80, 0x06, 0x18, 0xfb, 0x28,
0x1e, 0x98, 0xca, 0xf6, 0xd3, 0xcb, 0x1b, 0xee, 0xb3, 0xbe, 0xd0, 0x5a, 0x78, 0x52, 0xf2, 0xb6,
0x78, 0x5e, 0xdd, 0x55, 0x71, 0xb8, 0x97, 0x47, 0x07, 0x20, 0xf2, 0xd4, 0x27, 0x71, 0x83, 0xab
/*0x63, 0xcb, 0x8d, 0x05, 0x3b, 0xe7, 0xfc, 0xf1, 0x11, 0xcf, 0x4a, 0x6e, 0x04, 0x43, 0x01, 0x07,
0x2a, 0x86, 0x36, 0xca, 0x9b, 0xea, 0x59, 0xa7, 0xb6, 0x50, 0x58, 0xe6, 0x52, 0xe4, 0x8a, 0xbd,
0xcd, 0x46, 0x1b, 0x97, 0x1b, 0xec, 0xdf, 0xdc, 0xb1, 0xf4, 0x4b, 0x36, 0x02, 0x25, 0x5e, 0x2d,
0x61, 0x6b, 0xdd, 0x10, 0x71, 0xa5, 0x47, 0x55, 0xc3, 0x06, 0x88, 0x79, 0x3d, 0xbf, 0x1a, 0x4a*/
};
int n = 4;//stream长度除以16
Byte *fullKey = keyExpansion(key);
cipherBlockChainingDecryption(stream, IV, fullKey, n);
for(int i = 0; i < 16 * n; i++)
printf("%c", stream[i]);
printf("\n");
}
void test_CTR()
{
Byte key[16] = {
0x36, 0xf1, 0x83, 0x57, 0xbe, 0x4d, 0xbd, 0x77, 0xf0, 0x50, 0x51, 0x5c, 0x73, 0xfc, 0xf9, 0xf2
};
Byte IV[16] = {
0x69, 0xdd, 0xa8, 0x45, 0x5c, 0x7d, 0xd4, 0x25, 0x4b, 0xf3, 0x53, 0xb7, 0x73, 0x30, 0x4e, 0xec
};
Byte stream[100] = {
0x0c, 0xf0, 0x56, 0x6a, 0x32, 0x08, 0xc8, 0xf1, 0xa7, 0x5b, 0x09, 0x03, 0xbb, 0xb2, 0x1a, 0xc3,
0x88, 0x95, 0xb7, 0xaa, 0xfc, 0x1d, 0x41, 0xfc, 0x7c, 0x70, 0x80, 0x86, 0xbf, 0x0a, 0x9a, 0x90
/*0x0e, 0xc7, 0x70, 0x23, 0x30, 0x09, 0x8c, 0xe7, 0xf7, 0x52, 0x0d, 0x1c, 0xbb, 0xb2, 0x0f, 0xc3,
0x88, 0xd1, 0xb0, 0xad, 0xb5, 0x05, 0x4d, 0xbd, 0x73, 0x70, 0x84, 0x9d, 0xbf, 0x0b, 0x88, 0xd3,
0x93, 0xf2, 0x52, 0xe7, 0x64, 0xf1, 0xf5, 0xf7, 0xad, 0x97, 0xef, 0x79, 0xd5, 0x9c, 0xe2, 0x9f,
0x5f, 0x51, 0xee, 0xca, 0x32, 0xea, 0xbe, 0xdd, 0x9a, 0xfa, 0x93, 0x29, 0x04, 0x04, 0x04, 0x04*/
};
int n = 2;
Byte *fullKey = keyExpansion(key);
counterModeDecryption(stream, IV, fullKey, n);
for(int i = 0; i < 16 * n; i++)
printf("%c", stream[i]);
printf("\n");
//counterModeEncryption(stream, IV, fullKey, 16 * 4);
/*for(int i = 0; i < 16 * 4; i++)
printf("%02X ", stream[i]);
printf("\n");*/
}
int main() {
/* Byte plainText[4][4] = {
{0x00, 0x12, 0x0C, 0x08},
{0x04, 0x04, 0x00, 0x23},
{0x12, 0x12, 0x13, 0x19},
{0x14, 0x00, 0x11, 0x19}
};
Byte key[16] = {
0x24, 0x34, 0x31, 0x13, 0x75, 0x75, 0xE2, 0xAA, 0xA2, 0x56, 0x12, 0x54, 0xB3, 0x88, 0x00, 0x87
};
Byte *fullKey = keyExpansion(key);
AES_Encryption(plainText, fullKey);
AES_Decryption(plainText, fullKey);*/
printf("lab2实验结果。版权归吕浪:\n");
printf("CBC模式解密的结果:\n");
test_CBC();
printf("CTR模式解密的结果:\n");
test_CTR();
return 0;
}
(2)AES.h
//
// AES.h
// SymmetricKeyCipher
//
// Created by szxjzhou on 3/24/15.
// Copyright (c) 2015 szxjzhou. All rights reserved.
//
#ifndef __SymmetricKeyCipher__AES__
#define __SymmetricKeyCipher__AES__
#include <stdio.h>
typedef unsigned char Byte;
// Each word is 4 Bytes
#define BYTES_IN_WORD (4)
// Each round of key is 4 words
#define WORD_IN_ROUND (4)
// Each byte has 8 bits
#define BIT_IN_BYTE (8)
// Each round of key is 4 words, say 4 * 4 = 16 Bytes
#define BYTES_IN_ROUND (16)
// Expended key length is 11 words, say 11 * 16 = 176 Bytes
#define BYTES_IN_EXPANDED_KEY (176)
// In AES128 has 10 rounds except the initialization round
#define NUM_OF_ROUNDS (10)
static Byte sBox[16][16] = {
{0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, 0x67, 0x2B, 0xFE, 0xD7, 0xAB, 0x76},
{0xCA, 0x82, 0xC9, 0x7D, 0xFA, 0x59, 0x47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0x72, 0xC0},
{0xB7, 0xFD, 0x93, 0x26, 0x36, 0x3F, 0xF7, 0xCC, 0x34, 0xA5, 0xE5, 0xF1, 0x71, 0xD8, 0x31, 0x15},
{0x04, 0xC7, 0x23, 0xC3, 0x18, 0x96, 0x05, 0x9A, 0x07, 0x12, 0x80, 0xE2, 0xEB, 0x27, 0xB2, 0x75},
{0x09, 0x83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0x52, 0x3B, 0xD6, 0xB3, 0x29, 0xE3, 0x2F, 0x84},
{0x53, 0xD1, 0x00, 0xED, 0x20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0x39, 0x4A, 0x4C, 0x58, 0xCF},
{0xD0, 0xEF, 0xAA, 0xFB, 0x43, 0x4D, 0x33, 0x85, 0x45, 0xF9, 0x02, 0x7F, 0x50, 0x3C, 0x9F, 0xA8},
{0x51, 0xA3, 0x40, 0x8F, 0x92, 0x9D, 0x38, 0xF5, 0xBC, 0xB6, 0xDA, 0x21, 0x10, 0xFF, 0xF3, 0xD2},
{0xCD, 0x0C, 0x13, 0xEC, 0x5F, 0x97, 0x44, 0x17, 0xC4, 0xA7, 0x7E, 0x3D, 0x64, 0x5D, 0x19, 0x73},
{0x60, 0x81, 0x4F, 0xDC, 0x22, 0x2A, 0x90, 0x88, 0x46, 0xEE, 0xB8, 0x14, 0xDE, 0x5E, 0x0B, 0xDB},
{0xE0, 0x32, 0x3A, 0x0A, 0x49, 0x06, 0x24, 0x5C, 0xC2, 0xD3, 0xAC, 0x62, 0x91, 0x95, 0xE4, 0x79},
{0xE7, 0xC8, 0x37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0x56, 0xF4, 0xEA, 0x65, 0x7A, 0xAE, 0x08},
{0xBA, 0x78, 0x25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0x74, 0x1F, 0x4B, 0xBD, 0x8B, 0x8A},
{0x70, 0x3E, 0xB5, 0x66, 0x48, 0x03, 0xF6, 0x0E, 0x61, 0x35, 0x57, 0xB9, 0x86, 0xC1, 0x1D, 0x9E},
{0xE1, 0xF8, 0x98, 0x11, 0x69, 0xD9, 0x8E, 0x94, 0x9B, 0x1E, 0x87, 0xE9, 0xCE, 0x55, 0x28, 0xDF},
{0x8C, 0xA1, 0x89, 0x0D, 0xBF, 0xE6, 0x42, 0x68, 0x41, 0x99, 0x2D, 0x0F, 0xB0, 0x54, 0xBB, 0x16}
};
static Byte sBoxInv[16][16] = {
{0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB},
{0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB},
{0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E},
{0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25},
{0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92},
{0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84},
{0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06},
{0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B},
{0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73},
{0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E},
{0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B},
{0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4},
{0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F},
{0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF},
{0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61},
{0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D}
};
static Byte constantMatrix[4][4] = {
{0x02, 0x03, 0x01, 0x01},
{0x01, 0x02, 0x03, 0x01},
{0x01, 0x01, 0x02, 0x03},
{0x03, 0x01, 0x01, 0x02}
};
static Byte constantMatrixInv[4][4] = {
{0x0E, 0x0B, 0x0D, 0x09},
{0x09, 0x0E, 0x0B, 0x0D},
{0x0D, 0x09, 0x0E, 0x0B},
{0x0B, 0x0D, 0x09, 0x0E}
};
static Byte GF_constant[8] = {0x1B, 0x36, 0x6C, 0xD8, 0xAB, 0x4D, 0x9A, 0x2F};
static Byte roundConstant[10] = {0x01, 0x02, 0x04, 0x08, 0x10, 0x20, 0x40, 0x80, 0x1B, 0x36};
Byte *keyExpansion(Byte *cipherKey);
void AES_Encryption(Byte state[][BYTES_IN_WORD], Byte* key);
void AES_Decryption(Byte state[][BYTES_IN_WORD], Byte* key);
void rotateWord(Byte *word, int offset);
void substitutionWord(Byte *word);
void substitutionWord(Byte state[][BYTES_IN_WORD]);
void substitutionWordInv(Byte state[][BYTES_IN_WORD]);
void shiftRow(Byte state[][BYTES_IN_WORD]);
void shiftRowInv(Byte state[][BYTES_IN_WORD]);
void mixColumn(Byte state[][BYTES_IN_WORD]);
void mixColumnInv(Byte state[][BYTES_IN_WORD]);
Byte GF_Multiplication(Byte a, Byte b);
void addRoundKey(Byte state[][BYTES_IN_WORD], Byte* key, int round);
void printState(Byte state[][BYTES_IN_WORD]);
#endif /* defined(__SymmetricKeyCipher__AES__) */
(3)AES.cpp
//
// AES.cpp
// SymmetricKeyCipher
//
// Created by szxjzhou on 3/24/15.
// Copyright (c) 2015 szxjzhou. All rights reserved.
//
#include <stdio.h>
#include <stdlib.h>
#include "AES.h"
Byte *keyExpansion(Byte *cipherKey) {
Byte *expandedKey = (Byte *)malloc(sizeof(Byte) * BYTES_IN_EXPANDED_KEY);
// get the key of the first round
for(int i = 0; i < BYTES_IN_ROUND; i++)
expandedKey[i] = cipherKey[i];
// get the key of other rounds
Byte *temporary_word = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 1; i <= NUM_OF_ROUNDS; i++) {
// calculate the temporary word
for(int j = 0; j < BYTES_IN_WORD; j++)
temporary_word[j] = expandedKey[i * BYTES_IN_ROUND - BYTES_IN_WORD + j];
rotateWord(temporary_word, 1);
substitutionWord(temporary_word);
temporary_word[0] = (temporary_word[0] ^ roundConstant[i - 1]);
// get the key of this round
for(int j = 0; j < BYTES_IN_WORD; j++)
expandedKey[i * BYTES_IN_ROUND + j] = temporary_word[j]
^ expandedKey[(i - 1) * BYTES_IN_ROUND + j];
for(int j = 1; j < WORD_IN_ROUND; j++) {
for(int k = 0; k < BYTES_IN_WORD; k++) {
expandedKey[i * BYTES_IN_ROUND + j * BYTES_IN_WORD + k] =
expandedKey[i * BYTES_IN_ROUND + (j - 1) * BYTES_IN_WORD + k] ^
expandedKey[(i - 1) * BYTES_IN_ROUND + j * BYTES_IN_WORD + k];
}
}
}
free(temporary_word);
return expandedKey;
}
void AES_Encryption(Byte state[][BYTES_IN_WORD], Byte* key) {
// Round 0: addRoundKey
addRoundKey(state, key, 0);
// Round 1~9: substitutionWord + shiftRow + mixColumn + addRoundKey
for(int i = 1; i < 10; i++) {
substitutionWord(state);
shiftRow(state);
mixColumn(state);
addRoundKey(state, key, i);
}
// Round 10: substitutionWord + shiftRow + addRoundKey
substitutionWord(state);
shiftRow(state);
addRoundKey(state, key, 10);
}
void AES_Decryption(Byte state[][BYTES_IN_WORD], Byte* key) {
// Inv round 10: addRoundKey + shiftRowInv + substitutionWordInv
addRoundKey(state, key, 10);
shiftRowInv(state);
substitutionWordInv(state);
// Inv round 9~1: addRoundKey + mixColumnInv + shiftRowInv + substitutionWordInv
for(int i = 9; i > 0; i--) {
addRoundKey(state, key, i);
mixColumnInv(state);
shiftRowInv(state);
substitutionWordInv(state);
}
// Inv round 0: addRoundKey
addRoundKey(state, key, 0);
}
void rotateWord(Byte *word, int offset) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++)
temp[(i + BYTES_IN_WORD - offset) % 4] = word[i];
for(int i = 0; i < BYTES_IN_WORD; i++)
word[i] = temp[i];
free(temp);
}
void substitutionWord(Byte *word) {
for(int i = 0; i < BYTES_IN_WORD; i++)
word[i] = sBox[word[i] / 16][word[i] % 16];
}
void substitutionWord(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[i][j] = sBox[state[i][j] / 16][state[i][j] % 16];
}
void substitutionWordInv(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[i][j] = sBoxInv[state[i][j] / 16][state[i][j] % 16];
}
void shiftRow(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++)
rotateWord(state[i], i);
}
void shiftRowInv(Byte state[][BYTES_IN_WORD]) {
for(int i = 1; i < BYTES_IN_WORD; i++)
rotateWord(state[i], 4 - i);
}
void mixColumn(Byte state[][BYTES_IN_WORD]) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
temp[j] = state[j][i];
for(int j = 0; j < BYTES_IN_WORD; j++) {
state[j][i] = 0;
for(int k = 0; k < BYTES_IN_WORD; k++)
state[j][i] = (state[j][i] ^ GF_Multiplication(constantMatrix[j][k], temp[k]));
}
}
free(temp);
}
void mixColumnInv(Byte state[][BYTES_IN_WORD]) {
Byte *temp = (Byte *)malloc(sizeof(Byte) * BYTES_IN_WORD);
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
temp[j] = state[j][i];
for(int j = 0; j < BYTES_IN_WORD; j++) {
state[j][i] = 0;
for(int k = 0; k < BYTES_IN_WORD; k++)
state[j][i] = (state[j][i] ^ GF_Multiplication(constantMatrixInv[j][k], temp[k]));
}
}
free(temp);
}
Byte GF_Multiplication(Byte a, Byte b) {
bool *temp = (bool *)malloc(sizeof(bool) * BIT_IN_BYTE * 2);
for(int i = 0; i < BIT_IN_BYTE; i++) {
temp[i] = b % 2;
b /= 2;
}
short result = 0;
for(int i = 0; i < BIT_IN_BYTE; i++) {
result = result ^ ((temp[i] * a) << i);
}
int count = 0;
int temp_result = result;
for(int i = 0; i < BIT_IN_BYTE * 2; i++) {
temp[count++] = temp_result % 2;
temp_result /= 2;
}
for(int i = BIT_IN_BYTE; i < BIT_IN_BYTE * 2; i++)
if(temp[i] == 1)
result = result ^ GF_constant[i - BIT_IN_BYTE];
free(temp);
return (Byte)result;
}
void addRoundKey(Byte state[][BYTES_IN_WORD], Byte* key, int round) {
for(int i = 0; i < BYTES_IN_WORD; i++)
for(int j = 0; j < BYTES_IN_WORD; j++)
state[j][i] = (state[j][i] ^ key[round * BYTES_IN_ROUND + i * 4 + j]);
}
void printState(Byte state[][BYTES_IN_WORD]) {
for(int i = 0; i < BYTES_IN_WORD; i++) {
for(int j = 0; j < BYTES_IN_WORD; j++)
printf("%02X ", state[i][j]);
printf("\n");
}
printf("\n");
}(4)CBC.h
/*
* CBC.h
*
* Created on: 2016年3月24日
* Author: Lv_Lang
*/
#ifndef CBC_H_
#define CBC_H_
#include <stdio.h>
#include "AES.h"
void cipherBlockChainingDecryption(Byte *stream,Byte *IV,Byte *fullKey,int len);
void B(Byte temp[][16],Byte state[4][4],int i);
void S(Byte temp[][16],Byte state[4][4],int i);
void X(Byte p[4][16],Byte c[4][16],Byte *IV,int len);
void combine(Byte p[4][16],Byte *stream,int len);
#endif /* CBC_H_ */
(5)CBC.cpp
/*
* CBC.cpp
*
* Created on: 2016年3月24日
* Author: Lv_Lang
*/
#include "CBC.h"
//16=4x4拆开
void S(Byte temp[][16],Byte state[4][4],int i)//i表示对第几块进行操作
{
int k = 0;
for(int col = 0;col < 4;col++)
{
for(int row = 0;row < 4;row++)
{
state[row][col] = temp[i][k++];
}
}
}
//4x4=16连合
void B(Byte temp[][16],Byte state[4][4],int i)
{
int k = 0;
for(int col = 0;col < 4;col++)
{
for(int row = 0;row < 4;row++)
{
temp[i][k++] = state[row][col];
}
}
}
//异或
void X(Byte p[4][16],Byte c[4][16],Byte *IV,int len)
{
for(int i=0;i<len;i++)
{
if(i == 0)
{
for(int j=0;j<16;j++)
p[0][j] ^= IV[j];
}
else
{
for(int j=0;j<16;j++)
p[i][j] ^= c[i-1][j];
}
}
}
//合并
void combine(Byte p[4][16],Byte *stream,int len)
{
int k=0;
for(int row=0;row < 4;row++)
{
for(int col=0;col < 16;col++)
{
stream[k++] = p[row][col];
}
}
}
void cipherBlockChainingDecryption(Byte *stream,Byte *IV,Byte *fullKey,int len)
{
//密文切分成四块
Byte c[4][16];
//明文也是四块
Byte p[4][16];
int t = 0;
for(int i=0;i<len;i++)
{
for(int j=0;j < 16;j++)
{
c[i][j] = stream[t++];
}
}
//每块都进行AES解密,得到解密后的明文块
for(int i=0;i<len;i++)
{
Byte state[4][4];
S(c,state,i);//16=4x4拆开
AES_Decryption(state,fullKey);
B(p,state,i);//4x4=16连合
}
//异或
X(p,c,IV,len);
//合并明文块
combine(p,stream,len);
/*for(int i = 0;i<16;i++)
{
printf("%c",p[1][i]);
}
printf("\n");*/
}
(6)CTR.h
/*
* CTR.h
*
* Created on: 2016年3月24日
* Author: Lv_Lang
*/
#ifndef CTR_H_
#define CTR_H_
#include <stdio.h>
#include "AES.h"
void _B(Byte temp[][16],Byte state[4][4],int i);
void _S(Byte *IV,Byte state[4][4]);
void _X(Byte p[4][16],Byte c[4][16],int len);
void _combine(Byte p[4][16],Byte *stream,int len);
void counterModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int len);
#endif /* CTR_H_ */
(7)CTR.cpp
/*
* CTR.cpp
*
* Created on: 2016年3月24日
* Author: Lv_Lang
*/
#include "CTR.h"
//16=4x4拆开
void _S(Byte *IV,Byte state[4][4])//i表示对第几块进行操作
{
int k = 0;
for(int col = 0;col < 4;col++)
{
for(int row = 0;row < 4;row++)
{
state[row][col] = IV[k++];
}
}
}
//4x4=16连合
void _B(Byte temp[][16],Byte state[4][4],int i)
{
int k = 0;
for(int col = 0;col < 4;col++)
{
for(int row = 0;row < 4;row++)
{
temp[i][k++] = state[row][col];
}
}
}
//异或
void _X(Byte p[4][16],Byte c[4][16],int len)
{
for(int i=0;i<len;i++)
{
for(int j=0;j<16;j++)
p[i][j] ^= c[i][j];
}
}
//合并
void _combine(Byte p[4][16],Byte *stream,int len)
{
int k=0;
for(int row=0;row < 4;row++)
{
for(int col=0;col < 16;col++)
{
stream[k++] = p[row][col];
}
}
}
void counterModeDecryption(Byte *stream,Byte *IV,Byte *fullKey,int len)
{
//密文切分成四块
Byte c[4][16];
//明文也是四块
Byte p[4][16];
int t = 0;
for(int i=0;i<len;i++)
{
for(int j=0;j < 16;j++)
{
c[i][j] = stream[t++];
}
}
//每块都进行AES解密,得到解密后的明文块
for(int i=0;i<len;i++)
{
//首先要给IV加i
IV[15] += i;
Byte state[4][4];
_S(IV,state);//16=4x4拆开
AES_Encryption(state,fullKey);
_B(p,state,i);//4x4=16连合
}
//异或
_X(p,c,len);
//合并明文块
_combine(p,stream,len);
/*for(int i = 0;i<16;i++)
{
printf("%c",p[0][i]);
}
printf("\n");*/
}
其实笔者只是实现了这两种解密模式的外框架,真正核心和更有难度的在于AES加解密的实现。这里有几个讲AES和几种加解密模型的链接:





















 3865
3865











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








