实验设备:USG5500
-
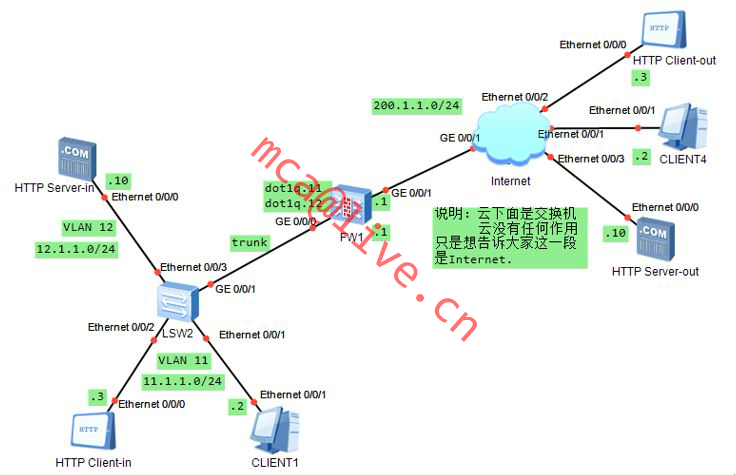
配置11.1.1.0/24网段访问Internat
-
配置DMZ区域并将DMZ区域的HTTPServer做静态NAT转换
3、将trust和DMZ放入子接口进行配置
拓扑图
DMZ配置方法
创建3个zone,分别为trust untrust dmz
L2 SW
L2sw
system-view
port-group group-member e0/0/1 to e0/0/3
port link-type access
quit
vlan 11
port e0/0/1
port e0/0/1
vlan 12
port e0/0/0
quit
int g0/0/1
port link-type trun
port trunk allow-pass vlan all
quit
配置虚拟接口IP地址
inter g0/0/0.11
dot1q termination vid 11
ip add 11.1.1.1 24
arp broadcast enable
quit
inter g/0/0/0.12
dotqq termination vid 12
ip add 12.1.1.1 24
arp broadcast enable
quit
inter g0/0/1
ip add 200.1.1.1 24
quit
将接口加入不同的zone
firewall zone trust
add inter g0/0/0/.11
quit
firewall zone dmz
add inter g0/0/0.12
quit
firewall zone untrust
add inter g0/0/1
quit
定义防火墙策略
policy1 允许11.1.1.0/24网段通过报文
trust和untrst域间:
policy interzone trust untrust outbound
policy 1
policy source 11.1.1.0 0.0.0.255
action permit
quit
quit
dmz和untrust域间:
policy2 允许目的地址为12.1.1.2,目的端口为21的报文通过
policy3 允许目的地址为12.1.1.3,目的端口为80的报文通过
policy interzone untrust dmz inbound
policy 2
policy destination 12.1.1.2 0
policy service service-set ftp
action permit
quit
policy 3
policy destination 12.1.1.3 0
policy service service-set http
action perimt
quit
quit
使用FTP的NAT ALG功能
firewall interzone dmz untrust
detect ftp
quit
配置内部服务器静态转换
nat server protocol tcp global 200.1.1.1 80 inside 12.1.1.2 www
nat server protocol tcp global 200.1.1.1 ftp inside 12.1.1.3 ftp
配置NAT地址池:
nat address-group 1 200.1.1.1 200.1.1.1
配置NAT策略:
policy1:允许网段为11.1.1.0/24的内网用户访问internet做地址转换
nat-policy interzone trust untrust outbound
policy 1
policy source 11.1.1.0 0.0.0.255
action source-nat
address-group 1
查看防火墙NAT会话列表
[SRG]display firewall session table
18:45:42 2014/09/23
Current Total Sessions : 3
icmp VPN:public --> public 11.1.1.12:256[200.1.1.1:2053]-->200.1.1.2:2048
http VPN:public --> public 11.1.1.12:2063[200.1.1.1:2055]-->200.1.1.2:80
http VPN:public --> public 11.1.1.12:2064[200.1.1.1:2056]-->200.1.1.2:80






















 380
380

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








