
下载解压:
发现图片大小过大,说明可能有文件嵌入,使用binwalk分离,binwalk -e 221B.png
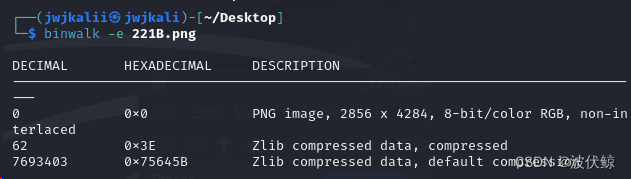
生成zlib文件
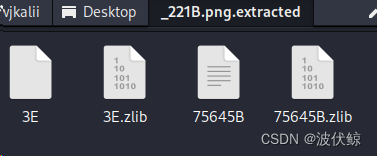
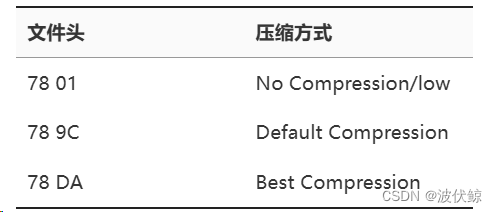
按一位大佬说的,不同zlib压缩方式对应不同文件头,但010打开这四个文件并没有789C字符
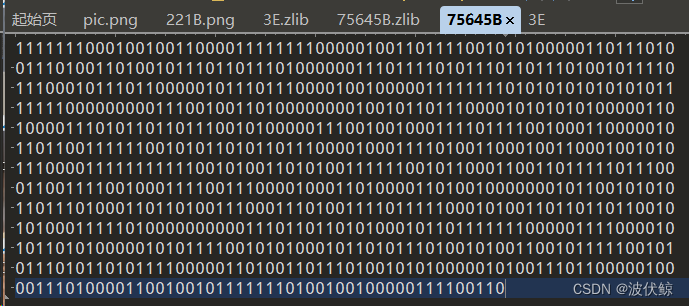
发现7564B文件中是一串二进制,长度为841,841=29*29,可能是个二维码,使用python将其转化为图片,1对应黑,0对应白:
from PIL import Image
MAX = 29
img = Image.new("RGB",(MAX, MAX))
str = "1111111000100100110000111111110000010011011110010101000001101110100111010011010010111011011101000000111011110101110110111010010111101110001011101100000101110111000010010000011111111010101010101010111111100000000011100100110100000000100101101110000101010101000001101000011101011011011100101000001110010010001111011110010001100000101101100111111001010110101101110000100011110100110001001100010010101110000111111111110010100110101001111110010110001100110111110111000110011110010001111001110000100011010000110100100000001011001010101101110100011011010011100011101001111011111000101001101101101100101010001111101000000000011101101101010001011011111110000011110000101011010100000101011110010101000101101011101001010011001011111001010111010110101111000001101001101110100101010000010100111011000001000011101000011001001011111110100100100000111100110"
i=0
for y in range (0,MAX):
for x in range (0,MAX):
if(str[i] == '1'):
img.putpixel([x,y],(0, 0, 0))
else:
img.putpixel([x,y],(255,255,255))
i = i+1
img.show()
img.save("flag.png")

得到二维码,扫描得到flag。
参考:
https://www.cnblogs.com/ainsliaea/p/15780903.html
https://blog.csdn.net/song123sh/article/details/117038590






















 1225
1225

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








