文末有福利领取哦~
👉一、Python所有方向的学习路线
Python所有方向的技术点做的整理,形成各个领域的知识点汇总,它的用处就在于,你可以按照上面的知识点去找对应的学习资源,保证自己学得较为全面。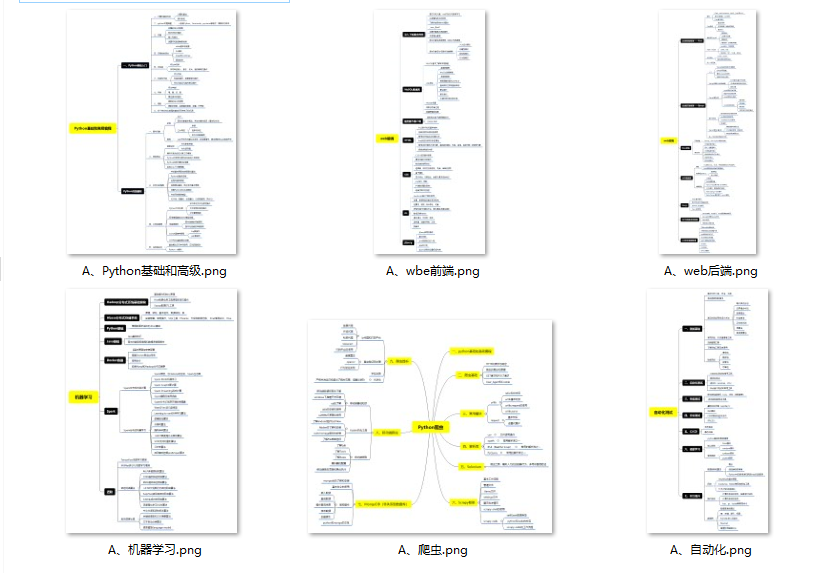
👉二、Python必备开发工具

👉三、Python视频合集
观看零基础学习视频,看视频学习是最快捷也是最有效果的方式,跟着视频中老师的思路,从基础到深入,还是很容易入门的。
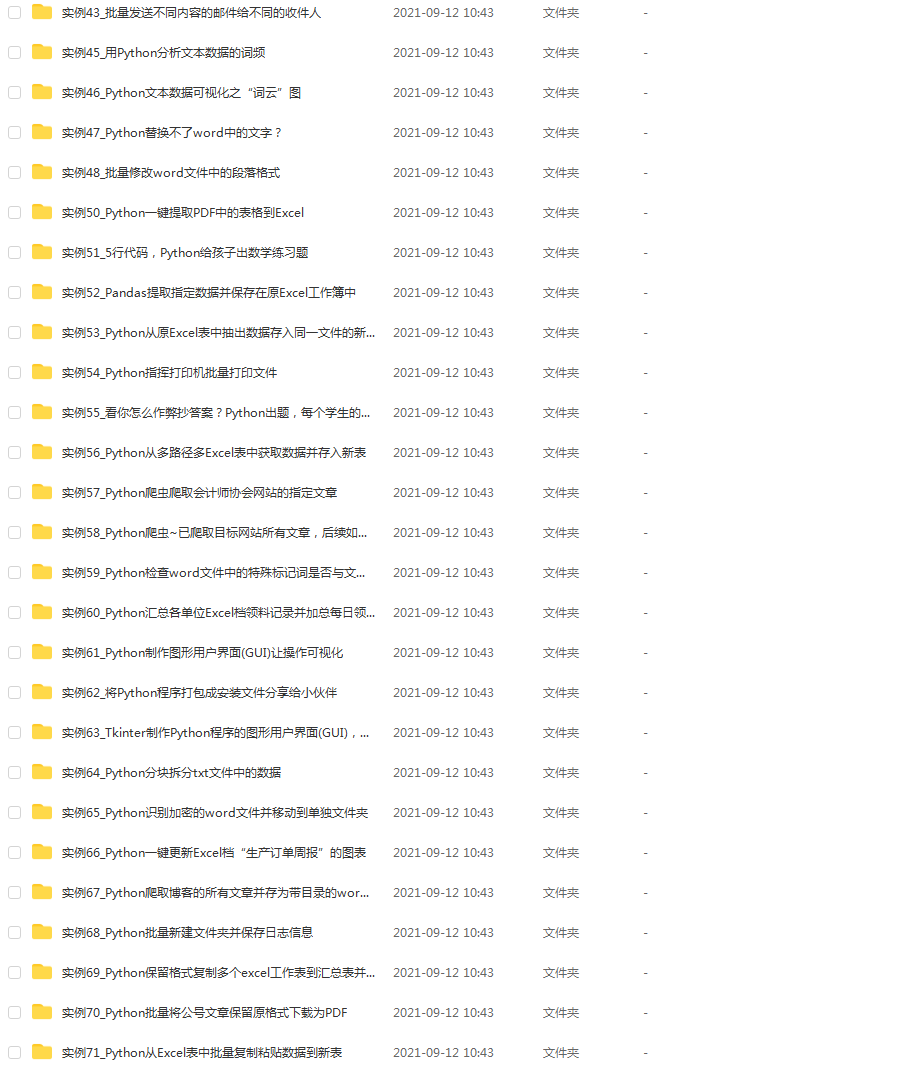
👉 四、实战案例
光学理论是没用的,要学会跟着一起敲,要动手实操,才能将自己的所学运用到实际当中去,这时候可以搞点实战案例来学习。(文末领读者福利)
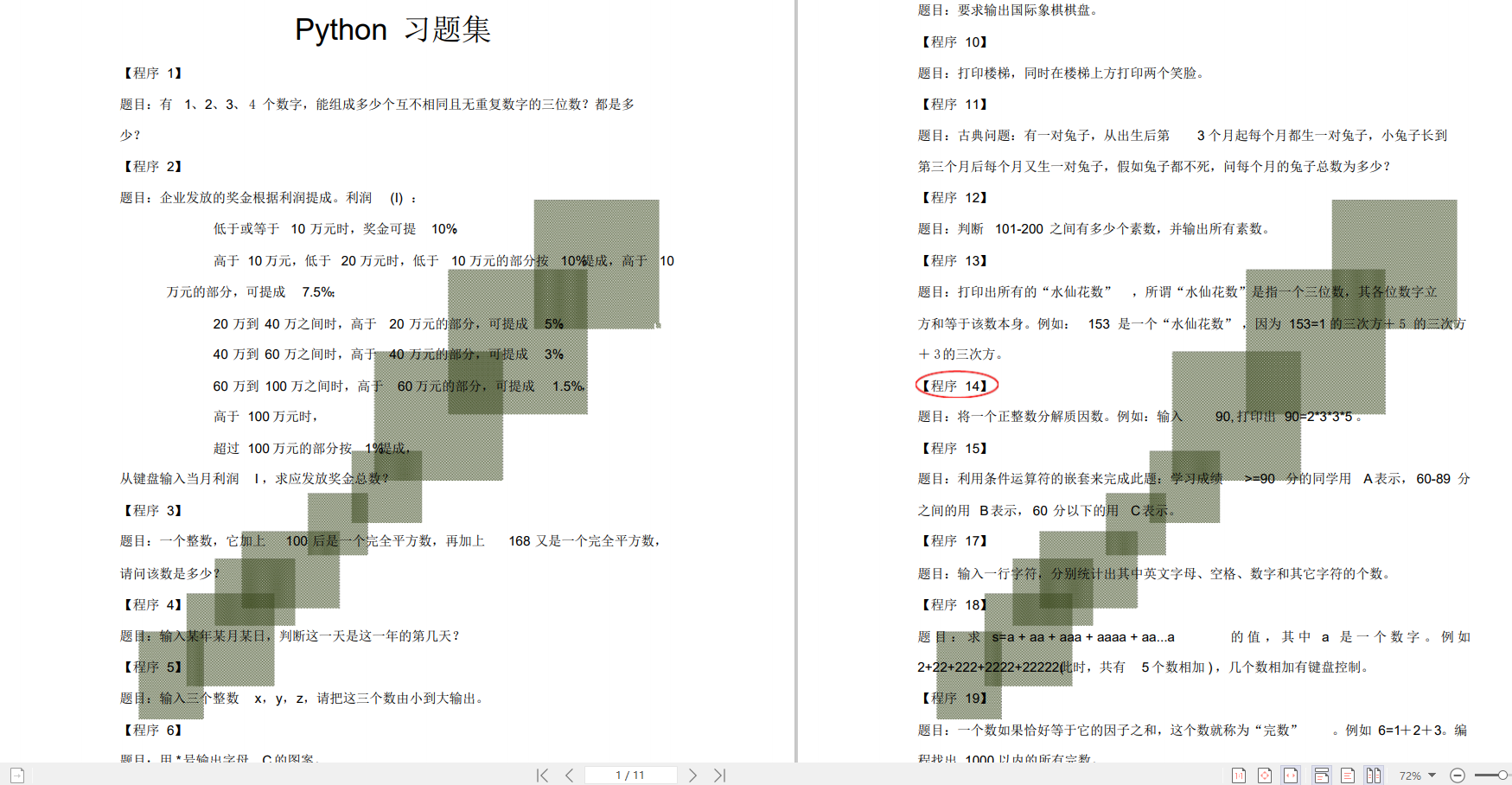
👉五、Python练习题
检查学习结果。
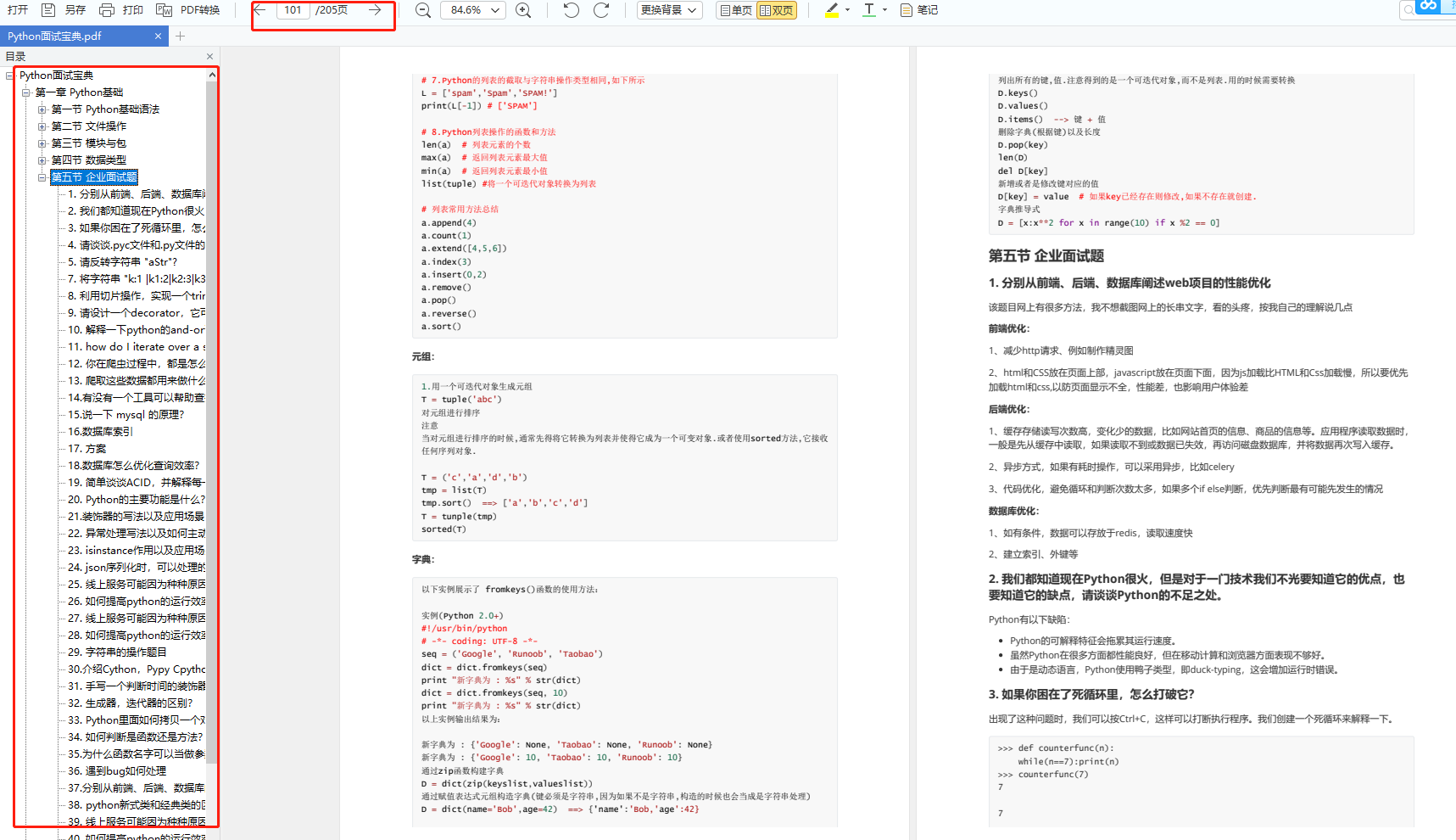
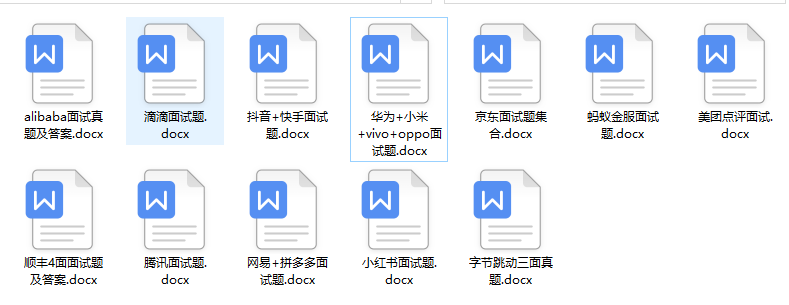
👉六、面试资料
我们学习Python必然是为了找到高薪的工作,下面这些面试题是来自阿里、腾讯、字节等一线互联网大厂最新的面试资料,并且有阿里大佬给出了权威的解答,刷完这一套面试资料相信大家都能找到满意的工作。
👉因篇幅有限,仅展示部分资料,这份完整版的Python全套学习资料已经上传
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
c
∈
Z
N
c \in \mathbb{Z}\_N
c∈ZN and a private key
(
N
,
d
)
(N,d)
(N,d), return the decrypted message
m
′
m^\prime
m′.
Your program does the following:
- Generate a textbook RSA key pair. You may use the Miller-Rabin Test algorithm to determine whether an integer is prime. Print the private key and the public key as multiple decimal strings.
- Read a decimal string representing a plaintext message
m
m
m. Raise an exception if
m
m
m is invalid.
- Encrypt the message
m
m
m. Print the encrypted message
c
c
c as a decimal string.
- Decrypt the encrypted message
c
c
c. Print the decrypted message
m
′
m^\prime
m′ as a decimal string.
- If you think the textbook RSA algorithm is secure, print
secure. Printinsecureotherwise.
Note that in this program, you may only include third-party codes or libraries for:
- Miller-Rabin Test
- Extended Euclidean Algorithm
Recall that including any third-party codes without claiming is considered as lack of academic integrity, and results in failing this course.
Example Input & Output
Input:
34862844108815430278935886114814204661242105806196134451262421197958661737288465541172280522822644267285105893266043422314800759306377373320298160258654603531159702663926160107285223145666239673833817786345065431976764139550904726039902450456522584204556470321705267433321819673919640632299889369457498214445
Output:
Private key:
N: 72480887416135972061737686062889407161759160887103574047817069443537714713215543172947835307344891172810092267953794611202591069661157992794959838750479208506005687981686025809332691431473809292764988868581099330149458758861391108410825625141738698507086062910615219209815042032904395035912581683751821198857
d: 32680572261276319950892386078453159129961789301515586779730994965995850002546722461272347997633819895532355760655076469284315213156424132333399966484423792583164625536594707257030835906698882316535262007407891728303620471604461013849133230965147690242465484589704113381685121927918786879123393719930911981301
Public key:
N: 72480887416135972061737686062889407161759160887103574047817069443537714713215543172947835307344891172810092267953794611202591069661157992794959838750479208506005687981686025809332691431473809292764988868581099330149458758861391108410825625141738698507086062910615219209815042032904395035912581683751821198857
e: 33917284234023552492304328018336609591997179645740843023623954792230653601864281593260663435095146463818240660159742130550887732511002455913550343095875105353898810744096024635824071115264943251609500722062745618030825015239681817073644641294390347390699708726562812289026328860966096616801710266920990047581
Ciphertext:
c: 15537860445392860627791921113547942268433746816211127779088849816425871267717435366808469771763672942339306019626033112604790279521256018388004503987281369444308463737059894900987688503037651823759352061264031327006538524035092808762774686406194114456168335939404457164139055755834030978327226465998086412320
Plaintext:
m': 34862844108815430278935886114814204661242105806196134451262421197958661737288465541172280522822644267285105893266043422314800759306377373320298160258654603531159702663926160107285223145666239673833817786345065431976764139550904726039902450456522584204556470321705267433321819673919640632299889369457498214445
insecure
solution code
import random
import math
import secrets
from random import randrange
# 模N大数的幂乘的快速算法
def fastExpMod(b, e, m): # 底数,幂,大数N
result = 1
e = int(e)
while e != 0:
if e % 2 != 0:
e -= 1
result = (result \* b) % m
continue
e >>= 1
b = (b \* b) % m
return result
def is\_probably\_prime\_miller\_rabin(n: int, k: int = 10) -> bool:
# Miller-Rabin 素数判定
# https://gist.github.com/bnlucas/5857478
if n == 2 or n == 3:
return True
if not n & 1:
return False
def check(a: int, s: int, d: int, n: int) -> bool:
x = pow(a, d, n)
if x == 1:
return True
for _ in range(s - 1):
if x == n - 1:
return True
x = pow(x, 2, n)
return x == n - 1
s: int = 0
d: int = n - 1
while d % 2 == 0:
d >>= 1
s += 1
for _ in range(k):
a: int = randrange(2, n - 1)
if not check(a, s, d, n):
return False
return True
def get\_big\_prime(nbits: int = 512) -> int:
# http://ju.outofmemory.cn/entry/93761
# 返回一个可能是素数的大整数
while True:
p: int = 2 \*\* (nbits - 1) | secrets.randbits(nbits)
if p % 2 == 0:
p = p + 1
if is_probably_prime_miller_rabin(p):
return p
# Generate a textbook RSA key pair
def create\_keys(keyLength):
p = get_big_prime(keyLength)
q = get_big_prime(keyLength)
n = p \* q
fn = (p - 1) \* (q - 1)
e = selectE(fn)
d = match_d(e, fn)
return n, e, d
# 随机在(1,fn)选择一个e, 满足gcd(e,fn)=1
def selectE(fn):
while True:
e = random.randint(0, fn)
if math.gcd(e, fn) == 1:
return e
# 根据e求出其逆元d
def match\_d(e, fn):
d = 0
while True:
if (e \* d) % fn == 1:
return d
d += 1
# Given a plaintext message and a public key , return the encrypted message.
def encrypt(M, e, n):
return fastExpMod(M, e, n)
# Given a ciphertext message and a private key , return the decrypted message.
def decrypt(C, d, m):
return fastExpMod(C, d, m)
def encrypt\_m(in_mess):
c = ''
for ch in in_mess:
s = str(encrypt(ord(ch), e, n))
c += s
return c
def decrypt\_m(in_cipher):
p = ''
for ch in in_cipher:
c: str = str(decrypt(ord(ch), d, n))
p += c
return p
if __name__ == '\_\_main\_\_':
# Read a decimal string representing a plaintext message.
**网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。**
**[需要这份系统化学习资料的朋友,可以戳这里获取](https://bbs.csdn.net/topics/618317507)**
**一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!**






















 859
859











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








