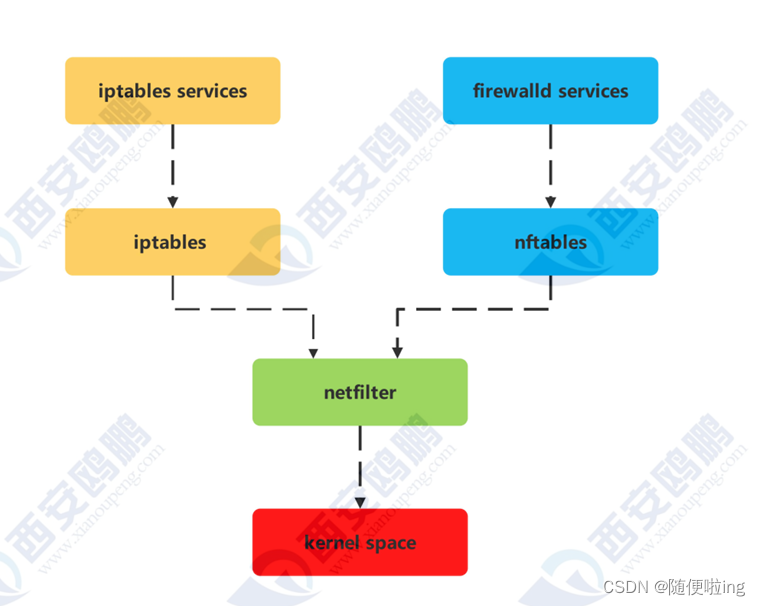
火墙拥有两套服务工具
一种是iptables另一种就是我们生活中常见的firewalld
我们主要看看iptables的工作机制及配置
iptables
- 已知node2的主机名称为node2.timinglee.org其ip为192.168.0.200,这台主机中只允许sshd,和nginx两个服务可以被访问
2.已知node1的主机名为node1.timinglee.org,此主机为双网卡主机其IP为172.25.254.200,和192.168.0.100,请在此主机中配置策略可以使node2主机访问外网
主机:node2
[root@server200 ~]# hostnamectl set-hostname node2.timinglee.org //修改主机名
[root@server200 ~]# hostname //查看主机名
node2.timinglee.org
[root@server200 ~]# ip a //网卡配置
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:a4:2e:e7 brd ff:ff:ff:ff:ff:ff
altname enp3s0
altname ens160
inet 192.168.0.200/24 brd 192.168.0.255 scope global noprefixroute eth0
valid_lft forever preferred_lft forever
inet6 fe80::1d24:d487:e06a:e4dd/64 scope link noprefixroute
valid_lft forever preferred_lft forever
关闭firewalld开启iptables
[root@server200 ~]# dnf install iptables-services -y //下载软件
[root@server200 ~]# systemctl disable --now firewalld //关闭firewalld
[root@server200~]# systemctl mask firewalld //锁住firewalld
Created symlink /etc/systemd/system/firewalld.service → /dev/null.
[root@server200 ~]# systemctl enable --now iptables.service //开启iptables
Created symlink /etc/systemd/system/multi-user.target.wants/iptables.service → /usr/lib/systemd/system/iptables.service.
[root@server200 ~]# iptables -nL //查看火墙策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED
ACCEPT icmp -- 0.0.0.0/0 0.0.0.0/0
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22
REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain FORWARD (policy ACCEPT)
target prot opt source destination
REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@server200~]# iptables -F //清空火墙策略
[root@server200 ~]# iptables -nL //查看
[root@server200 ~]# iptables -A INPUT -p tcp --dport 80 -j ACCEPT
//添加一条策略允许访问80端口nginx服务
[root@server200 ~]# iptables -A INPUT -p tcp --dport 22 -j ACCEPT
//添加一条策略允许访问22 端口sshd服务
[root@server129 ~]# iptables -nL
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:22
主机:node1
[root@server100 ~]# hostnamectl set-hostname node1.timinglee.org //修改主机名
[root@server100 ~]# hostname //查看主机名
Node1.timinglee.org
[root@server100 ~]# ip a
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:8f:0c:9d brd ff:ff:ff:ff:ff:ff
altname enp3s0
altname ens160
inet 172.25.254.100/24 brd 172.25.254.255 scope global noprefixroute eth0
valid_lft forever preferred_lft forever
inet6 fe80::a7db:2566:dc91:6001/64 scope link noprefixroute
valid_lft forever preferred_lft forever
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:8f:0c:a7 brd ff:ff:ff:ff:ff:ff
altname enp27s0
altname ens256
inet 192.168.0.100/24 brd 192.168.0.255 scope global noprefixroute eth1
valid_lft forever preferred_lft forever
inet6 fe80::a77c:6744:4c82:9f3/64 scope link noprefixroute
valid_lft forever preferred_lft forever
[root@server129 ~]# vim /etc/NetworkManager/system-connections/eth0.nmconnection
[ipv4]
address1=192.168.0.200/24,192.168.0.100
dns=114.114.114.114;
method=manual
[root@server100 ~]# vim /etc/sysctl.conf //开启内核路由功能
net.ipv4.ip_forward=1
[root@server100 ~]# sysctl -p
net.ipv4.ip_forward = 1
[root@server100 ~]# iptables -t nat -A POSTROUTING -o eth0 -j SNAT --to-source 172.25.254.100 //将内网的IP地址转换为172.25.254.100去上网
[root@server100 ~]# iptables -t nat -nL //查看策略
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
SNAT all -- 0.0.0.0/0 0.0.0.0/0 to:172.25.254.111
测试:
[root@server129 ~]# ping www.baidu.com
PING www.a.shifen.com (183.2.172.185) 56(84) 比特的数据。
64 比特,来自 183.2.172.185 (183.2.172.185): icmp_seq=1 ttl=127 时间=59.4 毫秒
--- www.a.shifen.com ping 统计 ---
已发送 3 个包, 已接收 3 个包, 0% packet loss, time 2004ms
rtt min/avg/max/mdev = 39.857/60.949/83.585/17.885 ms
[root@server100 ~]# iptables -t nat -A PREROUTING -i eth0 -j DNAT --to-dest 192.168.0.200 //外网访问内网将共有IP转换为私有的192.168.0.200
[root@server111 ~]# iptables -t nat -nL
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
DNAT all -- 0.0.0.0/0 0.0.0.0/0 to:192.168.0.200
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
SNAT all -- 0.0.0.0/0 0.0.0.0/0 to:172.25.254.111
测试:
[C:\~]$ ssh root@172.25.254.100 //用真机的ssh去链接172.25.254.100
[root@server129 ~]# ip a
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:a4:2e:e7 brd ff:ff:ff:ff:ff:ff
altname enp3s0
altname ens160
inet 192.168.0.200/24 brd 192.168.0.255 scope global noprefixroute eth0
valid_lft forever preferred_lft forever
inet6 fe80::1d24:d487:e06a:e4dd/64 scope link noprefixroute
valid_lft forever preferred_lft forever
连接的是172.25.254.100其实实际上连接的是192.168.0.200






















 1057
1057

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










