目录
一、实验需求:
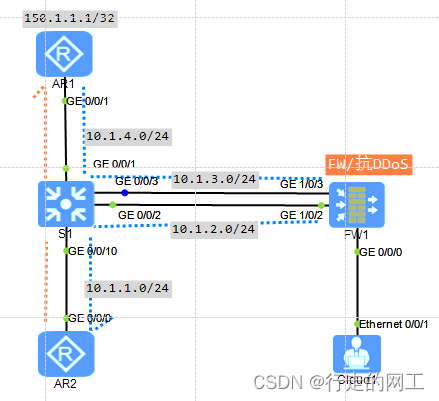
- 流量如图所示:
- AR2->AR1(150.1.1.1/32)的流量路径:AR2->S1->AR2,AR1(150.1.1.1/32)->AR2的流量路径:AR1->S1->FW1->S1->AR2;其中经过防火墙的ping和ssh流量关闭状态检测,其余流量不关闭状态检测。
二、关键配置:
-
交换机MQC配置如下:
acl number 3000
rule 5 permit ip source 150.1.1.1 0
#
traffic classifier PBR operator and
if-match acl 3000
#
traffic behavior PBR
redirect ip-nexthop 10.1.3.12
#
traffic policy PBR
classifier PBR behavior PBR
#
interface GigabitEthernet0/0/1
port link-type access
port default vlan 4
traffic-policy PBR inbound
#-
防火墙关键配置如下:
acl number 3000
rule 5 permit icmp source 150.1.1.1 0 destination 10.1.1.2 0
rule 10 permit tcp source 150.1.1.1 0 source-port eq ssh destination 10.1.1.2 0
#
firewall session link-state exclude acl 3000三、结果验证和防火墙会话表查看
- AR2结果验证:
[AR2]ping 150.1.1.1
PING 150.1.1.1: 56 data bytes, press CTRL_C to break
Reply from 150.1.1.1: bytes=56 Sequence=1 ttl=253 time=50 ms
Reply from 150.1.1.1: bytes=56 Sequence=2 ttl=253 time=50 ms
Reply from 150.1.1.1: bytes=56 Sequence=3 ttl=253 time=60 ms
Reply from 150.1.1.1: bytes=56 Sequence=4 ttl=253 time=40 ms
Reply from 150.1.1.1: bytes=56 Sequence=5 ttl=253 time=40 ms
--- 150.1.1.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 40/48/60 ms
[AR2]stelnet 150.1.1.1
Please input the username:admin
Trying 150.1.1.1 ...
Press CTRL+K to abort
Connected to 150.1.1.1 ...
Enter password:
-----------------------------------------------------------------------------
User last login information:
-----------------------------------------------------------------------------
Access Type: SSH
IP-Address : 10.1.1.2 ssh
Time : 2024-06-22 23:12:59-08:00
-----------------------------------------------------------------------------
<AR1>qui
Configuration console exit, please retry to log on
[AR2]qui
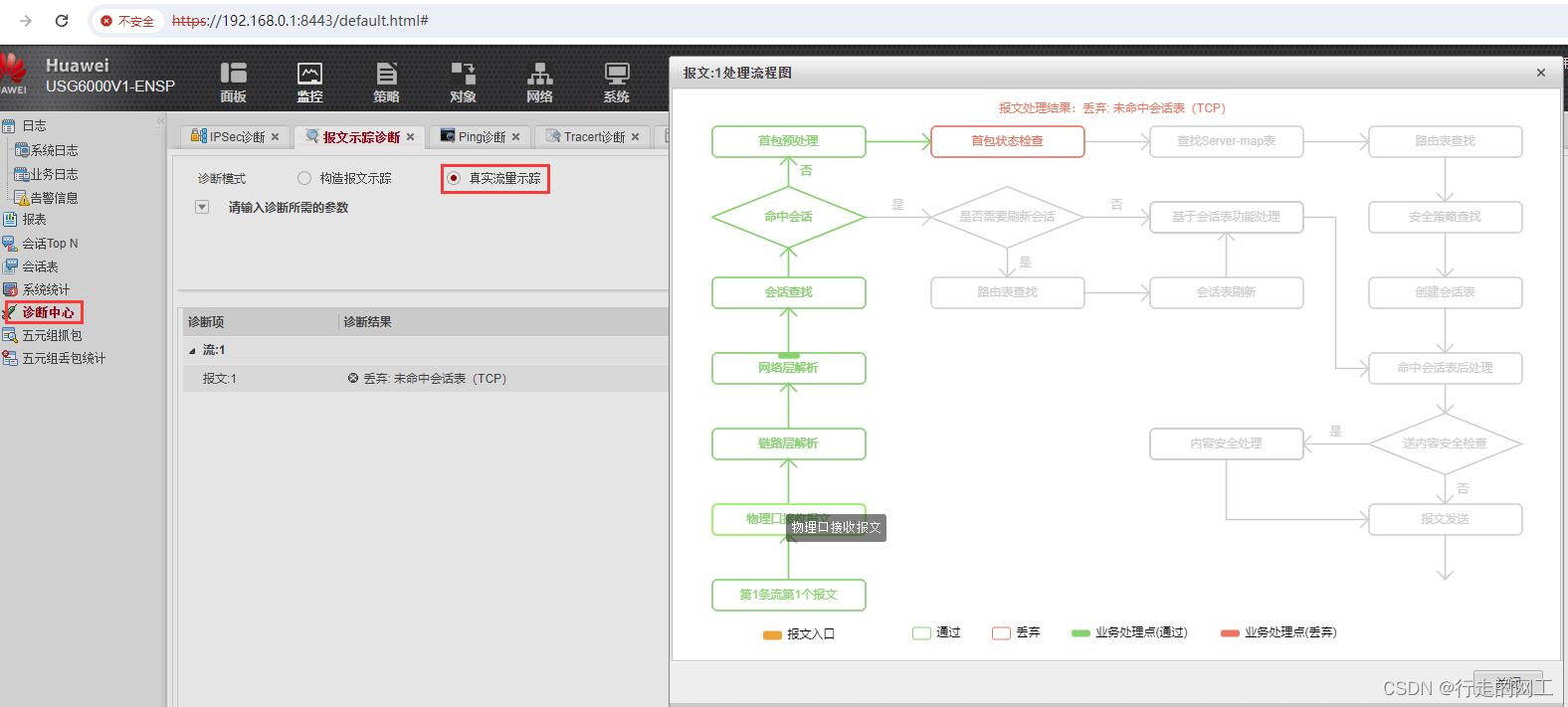
<AR2>telnet 150.1.1.1 //telnet失败且防火墙诊断中心如下图所示:
Press CTRL_] to quit telnet mode
Trying 150.1.1.1 ...
Error: Can't connect to the remote host
-
防火墙会话表:
[FW]display acl all
2024-06-22 15:14:29.490
Advanced ACL 3000, 2 rules ( Reference counter 0 )
Acl's step is 5
rule 5 permit icmp source 150.1.1.1 0 destination 10.1.1.2 0 (2 times matched)
rule 10 permit tcp source 150.1.1.1 0 source-port eq ssh destination 10.1.1.2 0 (2 times matched)
[FW]display firewall session link-state
2024-06-22 15:09:07.120
Current firewall session link-state:
------------------------------------
TCP check: on
ICMP check: on
Exclude acl: 3000
------------------------------------
[FW]display firewall session table
2024-06-22 15:12:40.070
Current Total Sessions : 1
icmp VPN: public --> public 150.1.1.1:2048 --> 10.1.1.2:52907
[FW]display firewall session table
2024-06-22 15:13:04.280
Current Total Sessions : 1
tcp VPN: public --> public 150.1.1.1:22 --> 10.1.1.2:49754





















 2496
2496

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








