第八章、ACL实验
一、实验扩扑
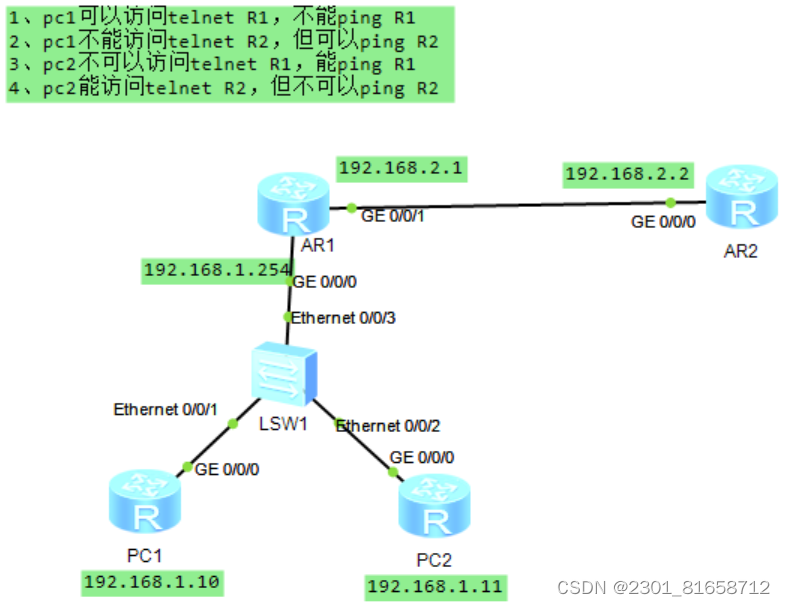
二、实验需求
1、pc1可以访问telnet R1,不能ping R1
2、pc1不能访问telnet R2,但可以ping R2
3、pc2不可以访问telnet R1,能ping R1
4、pc2能访问telnet R2,但不可以ping R2
三、实验步骤
[PC1]int g0/0/0
[PC1-GigabitEthernet0/0/0]ip add 192.168.1.10 24
[PC1]ip route-static 0.0.0.0 0 192.168.1.254
[PC2]int g0/0/0
[PC2-GigabitEthernet0/0/0]ip add 192.168.1.11 24
[PC2]ip route-static 0.0.0.0 0 192.168.1.254
[R1]int g0/0/0
[R1-GigabitEthernet0/0/0]ip add 192.168.1.254 24
[R1-GigabitEthernet0/0/0]int g0/0/1
[R1-GigabitEthernet0/0/1]ip add 192.168.2.1 24
[R2]int g0/0/0
[R2-GigabitEthernet0/0/0]ip add 192.168.2.2 24
[R2]ip route-static 192.168.1.0 24 192.168.2.1
2、配置Telnet
[R1]aaa
[R1-aaa]local-user yangyukun privilege level 15 password cipher yyk12345
[R1-aaa]local-user yangyukun service-type telnet
[R1]user-interface vty 0 4
[R1-ui-vty0-4]authentication-mode aaa
[R2]aaa
[R2-aaa]local-user zhangxuefeng privilege level 15 password cipher zxf12345
[R2-aaa]local-user zhangxuefeng service-type telnet
[R2]user-interface vty 0 4
[R2-ui-vty0-4]authentication-mode aaa
3、配置ACL
[R1]acl 3000
[R1-acl-adv-3000]rule deny icmp source 192.168.1.10 0.0.0.0 destination 192.168.2.1 0.0.0.0
[R1-acl-adv-3000]rule deny icmp source 192.168.1.10 0.0.0.0 destination 192.168.1.254 0.0.0.0
[R1-acl-adv-3000]rule deny tcp source 192.168.1.10 0.0.0.0 destination 192.168.2.2 0.0.0.0 destination-port eq 23
[R1-acl-adv-3000]rule deny tcp source 192.168.1.11 0.0.0.0 destination 192.168.2.1 0.0.0.0 destination-port eq 23
[R1-acl-adv-3000]rule deny tcp source 192.168.1.10 0.0.0.0 destinatio 192.168.1.254 0.0.0.0 destination-port eq 23
[R1-acl-adv-3000]rule deny icmp source 192.168.1.11 0.0.0.0 destination 192.168.2.2 0.0.0.0
[R1]int g0/0/0
[R1-GigabitEthernet0/0/0]traffic-filter inbound acl 3000
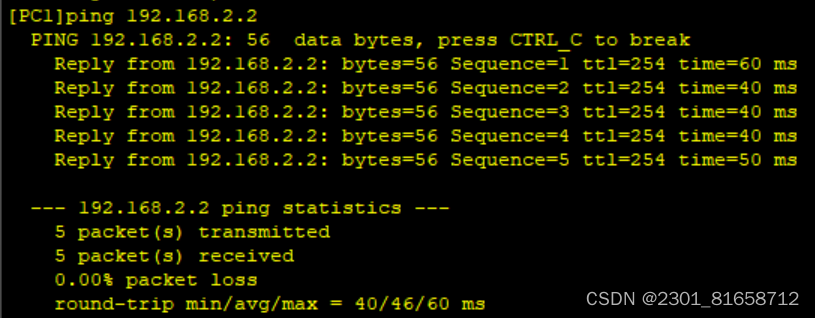
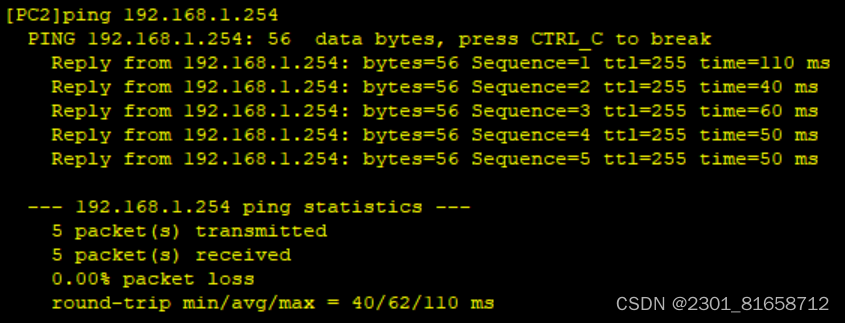
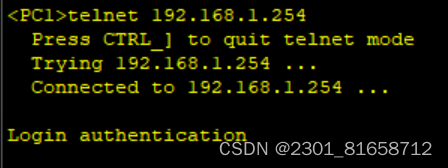
4、测试






















 3855
3855











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








