写在最后
在结束之际,我想重申的是,学习并非如攀登险峻高峰,而是如滴水穿石般的持久累积。尤其当我们步入工作岗位之后,持之以恒的学习变得愈发不易,如同在茫茫大海中独自划舟,稍有松懈便可能被巨浪吞噬。然而,对于我们程序员而言,学习是生存之本,是我们在激烈市场竞争中立于不败之地的关键。一旦停止学习,我们便如同逆水行舟,不进则退,终将被时代的洪流所淘汰。因此,不断汲取新知识,不仅是对自己的提升,更是对自己的一份珍贵投资。让我们不断磨砺自己,与时代共同进步,书写属于我们的辉煌篇章。
需要完整版PDF学习资源私我
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
quit
int g0/0/1
port link-type access
port default vlan 14
quit
int g0/0/2
port link-type access
port default vlan 24
quit
int g0/0/4
port link-type access
port default vlan 41
quit
int g0/0/24
port link-type access
port default vlan 45
quit
int vlan 14
ipv6 enable
ipv6 address 2001:0:0:14::4 64
quit
int vlan 24
ipv6 enable
ipv6 address 2001:0:0:24::4 64
quit
int vlan 34
ipv6 enable
ipv6 address 2001:0:0:34::4 64
quit
int vlan 41
ipv6 enable
ipv6 address 2001:0:0:41::4 64
quit
int vlan 45
ipv6 enable
ipv6 address 2001:0:0:45::4 64
quit
undo stp enable
**📝LSW5**
vlan batch 15 25 35 45 51
ipv6
int g0/0/3
port link-type access
port default vlan 35
quit
int g0/0/1
port link-type access
port default vlan 15
quit
int g0/0/2
port link-type access
port default vlan 25
quit
int g0/0/24
port link-type access
port default vlan 45
quit
int g0/0/5
port link-type access
port default vlan 51
quit
int vlan 15
ipv6 enable
ipv6 address 2001:0:0:15::5 64
quit
int vlan 25
ipv6 enable
ipv6 address 2001:0:0:25::5 64
quit
int vlan 35
ipv6 enable
ipv6 address 2001:0:0:35::5 64
quit
int vlan 45
ipv6 enable
ipv6 address 2001:0:0:45::5 64
quit
int vlan 51
ipv6 enable
ipv6 address 2001:0:0:51::5 64
quit
undo stp enable
**接下来我们做一下防火墙的配置**
**📝FW1:(默认用户名:admin 密码: Admin123)**
ipv6
int g1/0/0
ipv6 enable
ipv6 add 2001:0:0:41::1 64
quit
int g1/0/1
ipv6 enable
ipv6 add 2001:0:0:51::1 64
quit
int g1/0/2
ip add 100.1.11.1 24
quit
int g1/0/3
ip add 100.1.12.1 24
quit
firewall zone trust
add interface g1/0/0
add interface g1/0/1
quit
firewall zone untrust
add interface g1/0/2
add interface g1/0/3
quit
security-policy
default action permit
Warning:Setting the default packet filtering to permit poses security risks. You are advised to configure the security policy based on the actual data flows. Are you sure you want to continue?[Y/N] y //这里为警告提示我们输入y(yes)即可.
quit
int g1/0/0
service-manage ping permit
quit
int g1/0/1
service-manage ping permit
quit
int g1/0/2
service-manage ping permit
quit
int g1/0/3
service-manage ping permit
quit
ospfv3 10
router-id 100.100.100.100
quit
int g1/0/0
ospfv3 10 area 0
int g1/0/1
ospfv3 10 area 0
quit
ospfv3 10
default-route-advertise always
**下一步我们来运行ospf**
**📝LSW1**
ospfv3 10
router-id 1.1.1.1
quit
int vlan 100
ospfv3 10 area 0
int vlan 14
ospfv3 10 area 0
int vlan 15
ospfv3 10 area 0
quit
**📝LSW2**
ospfv3 10
router-id 2.2.2.2
quit
int vlan 200
ospfv3 10 area 0
int vlan 24
ospfv3 10 area 0
int vlan 25
ospfv3 10 area 0
**📝LSW3**
ospfv3 10
router-id 3.3.3.3
quit
int vlan 300
ospfv3 10 area 0
int vlan 34
ospfv3 10 area 0
int vlan 35
ospfv3 10 area 0
quit
**📝LSW4**
ospfv3 10
router-id 4.4.4.4
quit
int vlan 14
ospfv3 10 area 0
int vlan 24
ospfv3 10 area 0
int vlan 34
ospfv3 10 area 0
int vlan 45
ospfv3 10 area 0
int vlan 41
ospfv3 10 area 0
quit
**📝LSW5**
ospfv3 10
router-id 5.5.5.5
quit
int vlan 15
ospfv3 10 area 0
int vlan 25
ospfv3 10 area 0
int vlan 35
ospfv3 10 area 0
int vlan 45
ospfv3 10 area 0
int vlan 51
ospfv3 10 area 0
quit
**二、运营商**
**📝ISP1**
int g0/0/0
ip add 100.1.11.2 24
quit
int g0/0/1
ip add 100.1.100.1 24
quit
ospf 10 router-id 1.1.1.1
area 0
net 100.1.11.2 0.0.0.0
net 100.1.100.1 0.0.0.0
quit
silent-interface g0/0/0
quit
**📝ISP2**
int g0/0/0
ip add 100.1.12.2 24
quit
int g0/0/1
ip add 100.1.100.2 24
quit
ospf 10 router-id 2.2.2.2
area 0
net 100.1.12.2 0.0.0.0
net 100.1.100.2 0.0.0.0
quit
silent-interface g0/0/0
quit
**📝ISP3**
int g0/0/0
ip add 100.1.100.3 24
quit
int g0/0/1
ip add 100.1.23.3 24
quit
ospf 10 router-id 3.3.3.3
area 0
net 100.1.23.3 0.0.0.0
net 100.1.100.3 0.0.0.0
quit
silent-interface g0/0/1
quit
**📝ISP4**
int g0/0/0
ip add 100.1.100.4 24
quit
int g0/0/1
ip add 100.1.200.4 24
quit
ospf 10 router-id 4.4.4.4
area 0
net 100.1.200.4 0.0.0.0
net 100.1.100.4 0.0.0.0
quit
silent-interface g0/0/1
quit
**📝FW1**
nat64 enable
nat64 prefix 3001:0:0💯: 96
nat address-group 1
mode pat
section 1 100.1.11.100 100.1.11.110
nat address-group 2
mode pat
section 1 100.1.12.100 100.1.12.110
quit
nat-policy
rule name Nat64-1
source-zone trust
egress-interface g1/0/2
nat-type nat64
action source-nat address-group 1
quit
rule name Nat64-2
source-zone trust
egress-interface g1/0/3
nat-type nat64
action source-nat address-group 2
quit
quit
ip route-static 0.0.0.0 0 g1/0/2 100.1.11.2
ip route-static 0.0.0.0 0 g1/0/3 100.1.12.2
int g1/0/0
nat64 enable
int g1/0/1
nat64 enable
**分部**
**📝FW2**
ipv6
int g1/0/0
ip add 100.1.23.2 24
service-manage ping permit
quit
int g1/0/1
ipv6 enable
ipv6 address 2001:0:0:500::2 64
service-manage ping permit
quit
firewall zone trust
add interface g1/0/1
firewall zone trust
add interface g1/0/1
firewall zone untrust
add interface g1/0/0
quit
security-policy
default action permit
quit
先自我介绍一下,小编浙江大学毕业,去过华为、字节跳动等大厂,目前阿里P7
深知大多数程序员,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年最新网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。

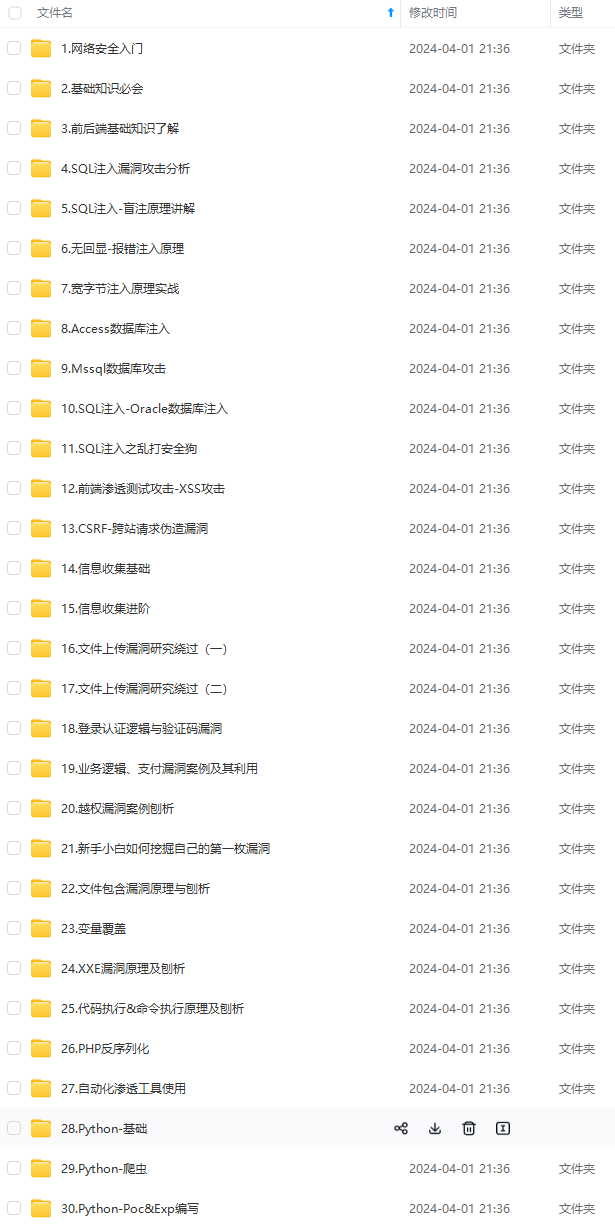

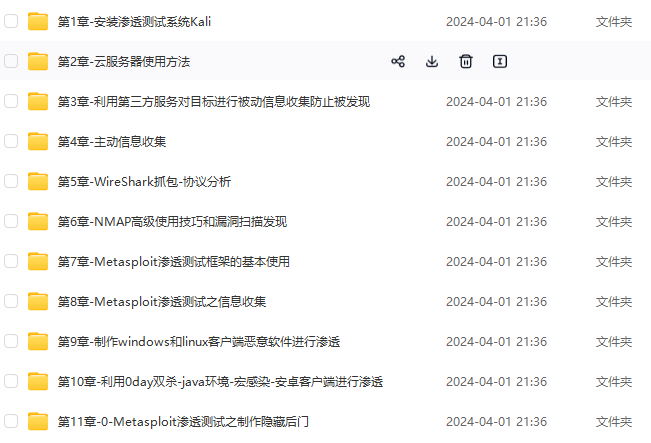
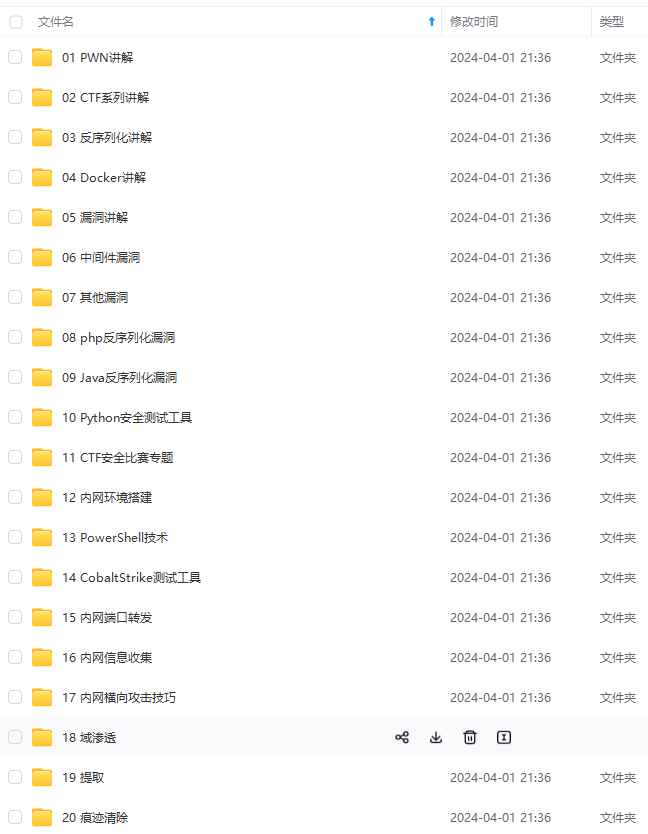
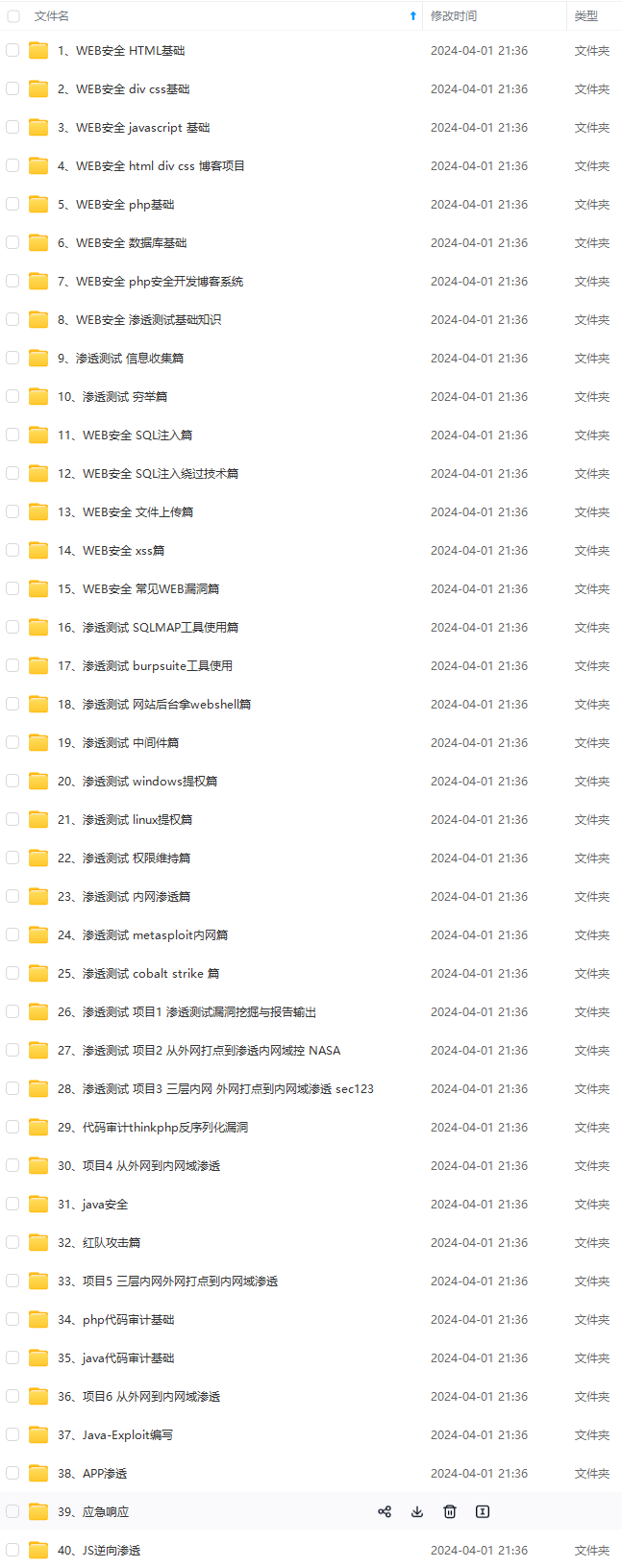
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、讲解视频,并且后续会持续更新
policy
default action permit
quit
先自我介绍一下,小编浙江大学毕业,去过华为、字节跳动等大厂,目前阿里P7
深知大多数程序员,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年最新网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。
[外链图片转存中…(img-GhH49u7Z-1715394183225)]
[外链图片转存中…(img-9pLQT2NN-1715394183227)]
[外链图片转存中…(img-CiVOOdwN-1715394183228)]
[外链图片转存中…(img-maKCFyDr-1715394183228)]
[外链图片转存中…(img-lhzK43kB-1715394183229)]
[外链图片转存中…(img-OlrI3tWD-1715394183230)]
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上网络安全知识点,真正体系化!
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、讲解视频,并且后续会持续更新






















 1962
1962

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








