先自我介绍一下,小编浙江大学毕业,去过华为、字节跳动等大厂,目前阿里P7
深知大多数程序员,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年最新网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。



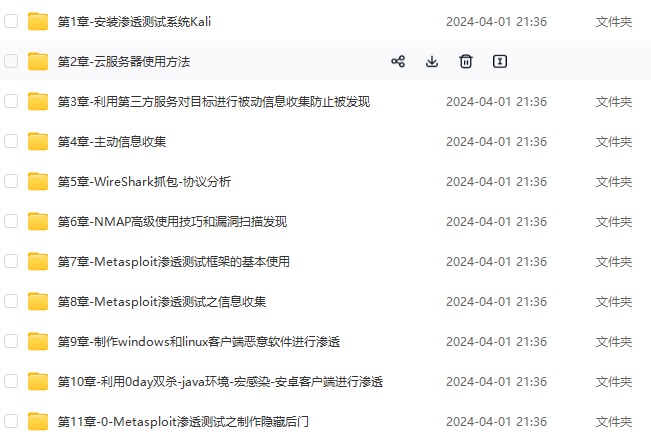
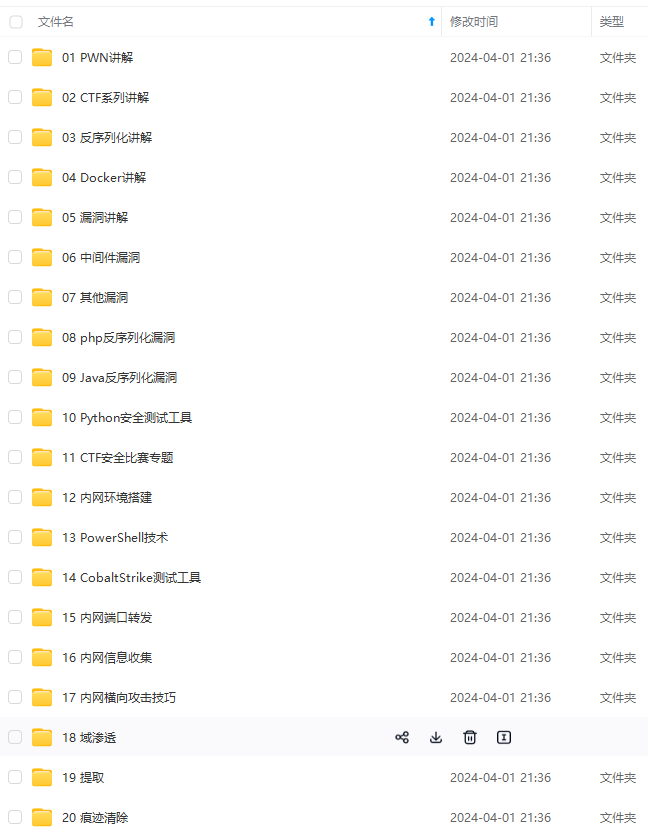
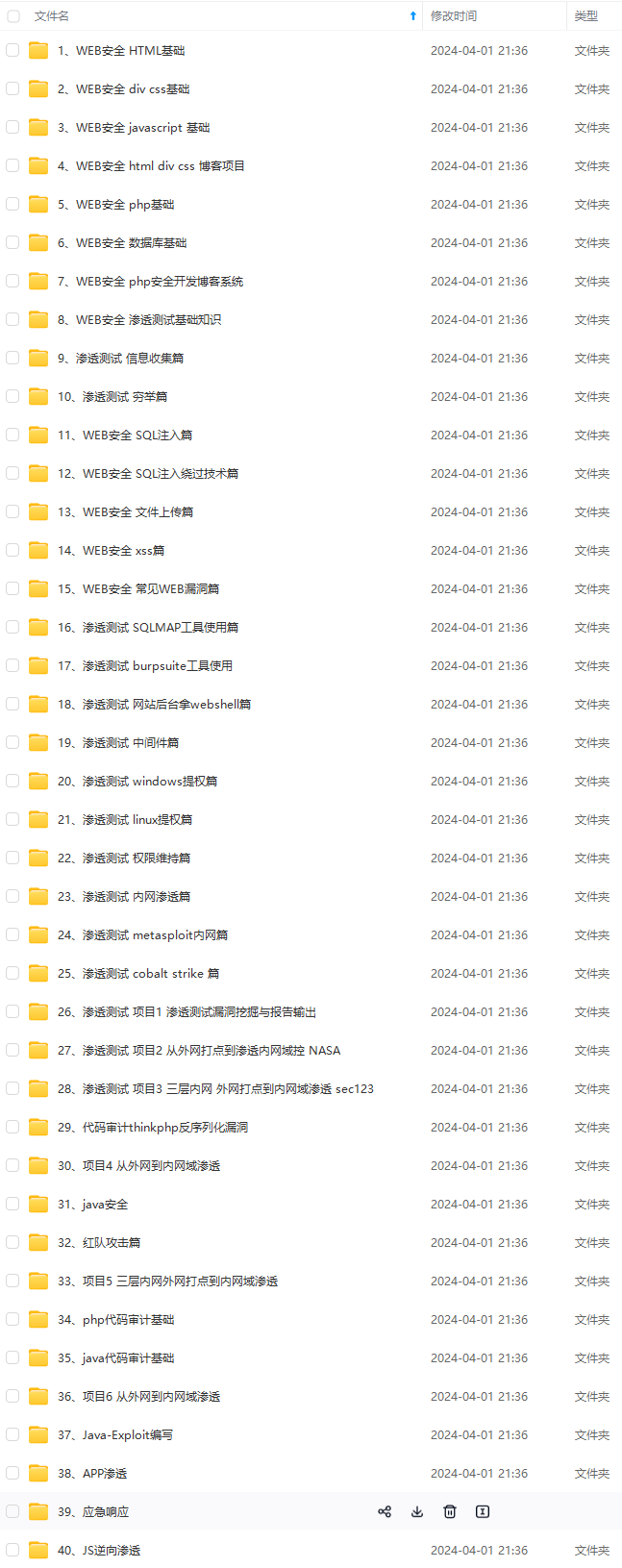
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上网络安全知识点,真正体系化!
需要体系化学习资料的朋友,可以加我V获取:vip204888 (备注网络安全)
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、讲解视频,并且后续会持续更新
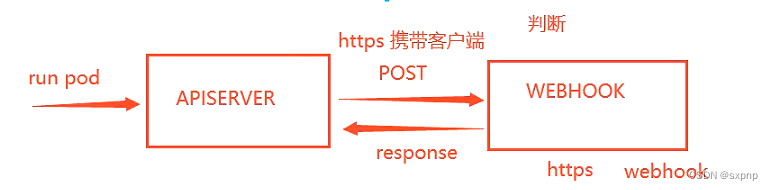
本次示例使用的方法是
通过docker 跑一个能进行api检测的python程序
通过将传给apiserver创建pod api 传到python docker 上进行检测镜像版本标签
如果不带标签则返回给apiserver拒绝语句,如果带标签则返回接收语句
启用
mkdir /etc/kubernetes/image-policy/
vim admission_configuration.yaml
apiVersion: apiserver.config.k8s.io/v1
kind: AdmissionConfiguration
plugins:
- name: ImagePolicyWebhook
configuration:
imagePolicy:
kubeConfigFile: /etc/kubernetes/image-policy/connect_webhook.yaml
# 链接镜像策略服务器配置文件
# 以秒计的时长,控制批准请求的缓存时间
allowTTL: 50
# 以秒计的时长,控制拒绝请求的缓存时间
denyTTL: 50
# 以毫秒计的时长,控制重试间隔
retryBackoff: 500
# 确定 Webhook 后端失效时的行为
defaultAllow: true
[root@master opa]# cp /root/.kube/config /etc/kubernetes/image-policy/connect_webhook.yaml
[root@master opa]# vim /etc/kubernetes/image-policy/connect_webhook.yaml
zip文件在最顶部
[root@master webhook]# unzip image-policy-webhook.zip
Archive: image-policy-webhook.zip
creating: image-policy-webhook/
inflating: image-policy-webhook/Dockerfile
inflating: image-policy-webhook/main.py
inflating: admission_configuration.yaml
inflating: connect_webhook.yaml
inflating: image-policy-certs.sh
[root@master image-policy-webhook]# docker pull library/python
Using default tag: latest
latest: Pulling from library/python
8457fd5474e7: Pull complete
13baa2029dde: Pull complete
[root@master image-policy-webhook]# docker build -t webhook-python .
Sending build context to Docker daemon 3.584kB
Step 1/9 : FROM python
---> a5d7930b60cc
Step 2/9 : RUN useradd python
---> Running in 6a893ebbc97e
[root@master webhook]# chmod +x image-policy-certs.sh
[root@master webhook]# ./image-policy-certs.sh
2023/11/15 22:18:52 [INFO] generating a new CA key and certificate from CSR
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:52 [INFO] encoded CSR
2023/11/15 22:18:52 [INFO] signed certificate with serial number 39827921930120332354958212009020451382931127285
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:52 [INFO] encoded CSR
2023/11/15 22:18:52 [INFO] signed certificate with serial number 157085660290104533426640490732748948028109129205
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:53 [INFO] encoded CSR
2023/11/15 22:18:53 [INFO] signed certificate with serial number 20452152514611241358495370727393457709691078555
2023/11/15 22:18:53 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@master webhook]# ls
admission_configuration.yaml apiserver-client.pem ca-key.pem image-policy-webhook webhook-key.pem
apiserver-client.csr ca-config.json ca.pem image-policy-webhook.zip webhook.pem
apiserver-client-csr.json ca.csr connect_webhook.yaml webhook.csr
apiserver-client-key.pem ca-csr.json image-policy-certs.sh webhook-csr.json
[root@master webhook]# cp webhook* image-policy-webhook
[root@master webhook]# cd image-policy-webhook/
docker run -d -u root --name=webhook-python \
-v $PWD/webhook.pem:/data/www/webhook.pem \
-v $PWD/webhook-key.pem:/data/www/webhook-key.pem \
-e PYTHONUNBUFFERED=1 -p 8080:8080 \
webhook-python
[root@master image-policy-webhook]# docker ps -a | grep python
fe9713e647e8 webhook-python "/bin/sh -c 'python …" 11 seconds ago Exited (1) 9 seconds ago webhook-python
[root@master webhook]# cp /root/k8s/cks/webhook/webhook.pem /etc/kubernetes/image-policy/
[root@master webhook]# cp /root/k8s/cks/webhook/apiserver-client-key.pem /etc/kubernetes/image-policy/
[root@master webhook]# cp /root/k8s/cks/webhook/apiserver-client.pem /etc/kubernetes/image-policy/
[root@master webhook]# ls /etc/kubernetes/image-policy/
admission_configuration.yaml apiserver-client-key.pem apiserver-client.pem connect_webhook.yaml webhook.pem
下面文件的 /etc/kubernetes/image-policy 是容器内的路径
apiVersion: v1
kind: Config
clusters:
- cluster:
certificate-authority: /etc/kubernetes/image-policy/webhook.pem # 数字证书,用于验证远程服务
server: https://192.168.100.53:8080/image_policy # 镜像策略服务器地址,必须是https
name: webhook
contexts:
- context:
cluster: webhook
user: apiserver
name: webhook
current-context: webhook
preferences: {}
users:
- name: apiserver
user:
client-certificate: /etc/kubernetes/image-policy/apiserver-client.pem # webhook准入控制器使用的证书
client-key: /etc/kubernetes/image-policy/apiserver-client-key.pem # 对应私钥证书
开启插件并使用hostpath 数据卷将宿主机/etc/kubernetes/image-policy目录挂载到容器中
- --enable-admission-plugins=NodeRestriction,ImagePolicyWebhook
- --admission-control-config-file=/etc/kubernetes/image-policy/admission_configuration.yaml
# 挂载卷添加
- mountPath: /etc/kubernetes/image-policy
name: image-policy
- hostPath:
path: /etc/kubernetes/image-policy
type: DirectoryOrCreate
name: image-policy
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
需要体系化学习资料的朋友,可以加我V获取:vip204888 (备注网络安全)
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
name: image-policy
**网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。**
**需要体系化学习资料的朋友,可以加我V获取:vip204888 (备注网络安全)**
**[需要这份系统化资料的朋友,可以点击这里获取](https://bbs.csdn.net/topics/618540462)**
**一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!**






















 907
907

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








