给大家的福利
零基础入门
对于从来没有接触过网络安全的同学,我们帮你准备了详细的学习成长路线图。可以说是最科学最系统的学习路线,大家跟着这个大的方向学习准没问题。
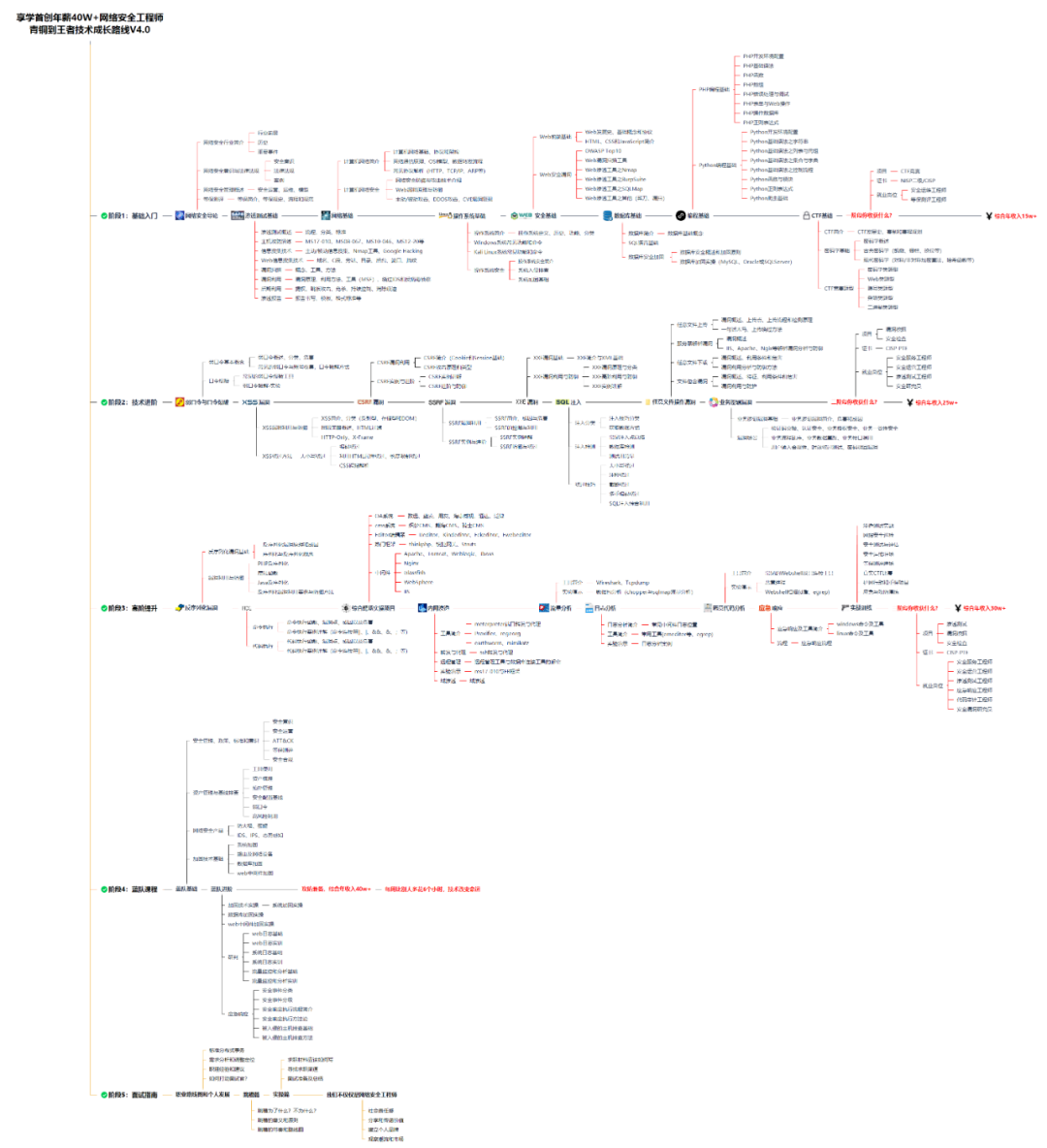
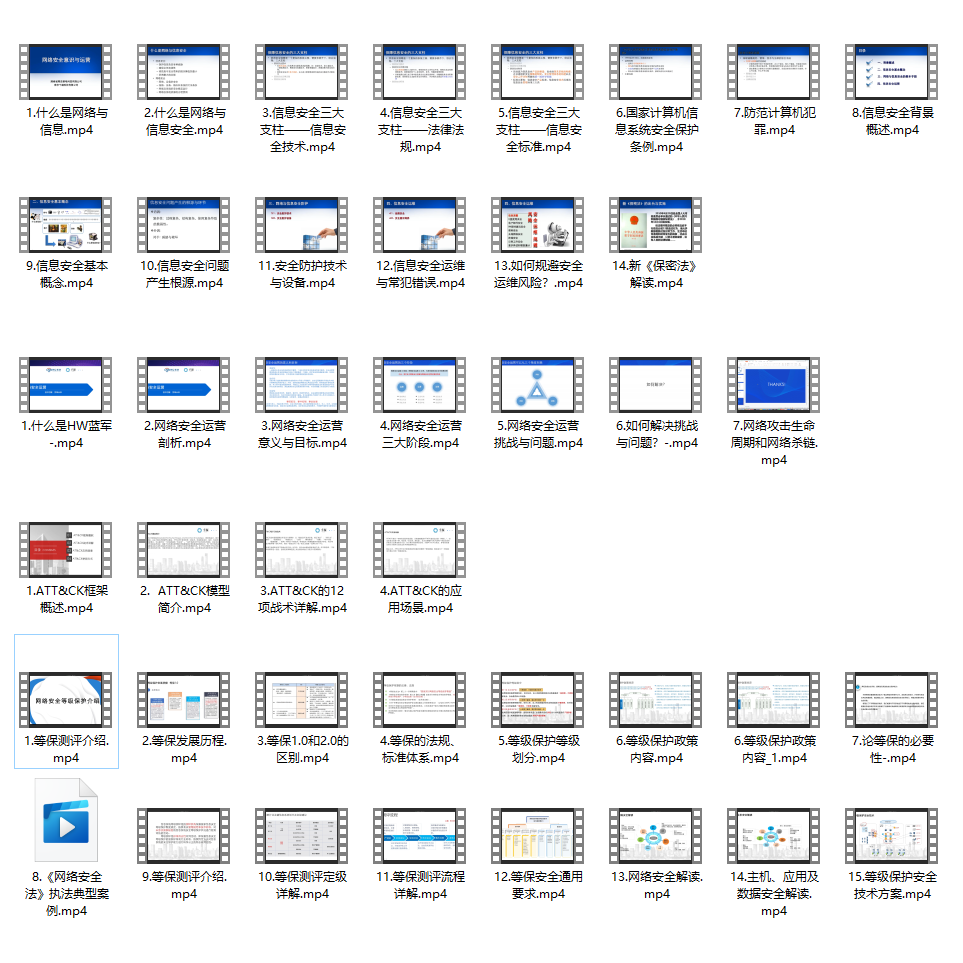
同时每个成长路线对应的板块都有配套的视频提供:
因篇幅有限,仅展示部分资料
需要体系化学习资料的朋友,可以加我V获取:vip204888 (备注网络安全)
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
这些功能在Spring-Secutiry都有
//获取当前的用户对象 Subject
Subject currentUser = SecurityUtils.getSubject();
//通过当前对象获取当前用户的Session
Session session = currentUser.getSession();
//判断当前的用户是否被认证
currentUser.isAuthenticated()
//获取当前用户信息
currentUser.getPrincipal()
//测试角色 判断当前用户是什么角色
currentUser.hasRole(“schwartz”)
currentUser.isPermitted(“lightsaber:wield”)
//注销
currentUser.logout();
6、SpringBoot整合Shiro环境搭建
导入相关依赖
org.apache.shiro
shiro-core
1.8.0
org.apache.shiro
shiro-spring
1.8.0
org.thymeleaf
thymeleaf-spring5
org.thymeleaf.extras
thymeleaf-extras-java8time
测试SpringBoot环境是否搭建成功
首页
add
update
controller层
@RequestMapping({“/”,“/index”})
public String ToIndex(Model model){
model.addAttribute(“msg”,“hello Shiro”);
return “index”;
}
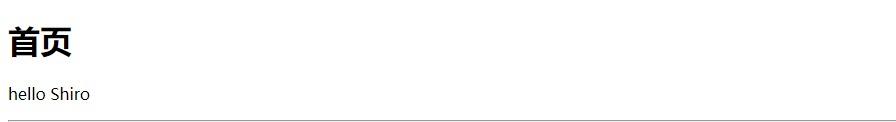
测试SpringBoot整合Shiro环境搭建成功
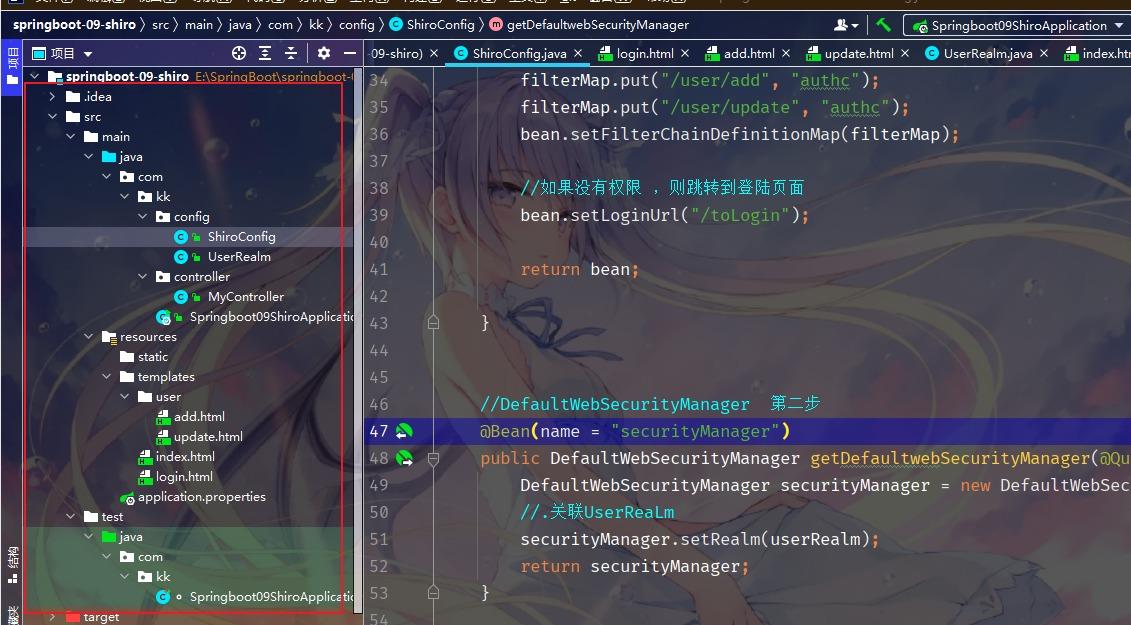
Shiro配置
package com.kk.config;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
//自定义的 UserRealm extends AuthorizingRealm
public class UserRealm extends AuthorizingRealm {
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println(“执行科=》授权doGetAuthorizationInfo”);
return null;
}
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
System.out.println(“执行科=》认证doGetAuthenticationInfo”);
return null;
}
}
ShiroConfig
package com.kk.config;
import org.apache.shiro.mgt.DefaultSecurityManager;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframework.beans.factory.annotation.Qualifier;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.HashMap;
import java.util.LinkedHashMap;
import java.util.Map;
@Configuration
public class ShiroConfig {
//ShiroFilterFactortBean 第三步
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(@Qualifier(“securityManager”) DefaultWebSecurityManager defaultWebSecurityManager) {
ShiroFilterFactoryBean bean = new ShiroFilterFactoryBean();
//设置安全管理器
bean.setSecurityManager(defaultWebSecurityManager);
return bean;
}
//DefaultWebSecurityManager 第二步
@Bean(name = “securityManager”)
public DefaultWebSecurityManager getDefaultwebSecurityManager(@Qualifier(“userRealm”) UserRealm userRealm) {
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
//.关联UserReaLm
securityManager.setRealm(userRealm);
return securityManager;
}
//创建 realm 对象 需要自定义 第一步
@Bean
public UserRealm userRealm() {
return new UserRealm();
}
}
MyController
package com.kk.controller;
import org.springframework.jmx.export.annotation.ManagedResource;
import org.springframework.stereotype.Controller;
import org.springframework.ui.Model;
import org.springframework.web.bind.annotation.RequestMapping;
@Controller
public class MyController {
@RequestMapping({“/”,“/index”})
public String ToIndex(Model model){
model.addAttribute(“msg”,“hello Shiro”);
return “index”;
}
@RequestMapping(“/user/add”)
public String add(){
return “user/add”;
}
@RequestMapping(“/user/update”)
public String update(){
return “user/update”;
}
@RequestMapping(“/toLogin”)
public String toLogin(){
return “login”;
}
}
index.html
首页
add
update
add.html
add
update.html
update
7、shiro实现登录拦截
package com.kk.config;
import org.apache.shiro.mgt.DefaultSecurityManager;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframework.beans.factory.annotation.Qualifier;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.HashMap;
import java.util.LinkedHashMap;
import java.util.Map;
@Configuration
public class ShiroConfig {
//ShiroFilterFactortBean 第三步
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(@Qualifier(“securityManager”) DefaultWebSecurityManager defaultWebSecurityManager) {
ShiroFilterFactoryBean bean = new ShiroFilterFactoryBean();
//设置安全管理器
bean.setSecurityManager(defaultWebSecurityManager);
//添加shiro的内置过滤器
/*
anon : 无需认证就可以访问
authc:必须认证才能访问
user:必须拥有 记住我 功能才能用
perms 拥有某个资源的权限才能访问
role 拥有某个角色的权限才能访问
*/
Map<String, String> filterMap = new LinkedHashMap<>();
filterMap.put(“/user/add”, “authc”);
filterMap.put(“/user/update”, “authc”);
bean.setFilterChainDefinitionMap(filterMap);
//如果没有权限 ,则跳转到登陆页面
bean.setLoginUrl(“/toLogin”);
return bean;
}
//DefaultWebSecurityManager 第二步
@Bean(name = “securityManager”)
public DefaultWebSecurityManager getDefaultwebSecurityManager(@Qualifier(“userRealm”) UserRealm userRealm) {
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
//.关联UserReaLm
securityManager.setRealm(userRealm);
return securityManager;
}
//创建 realm 对象 需要自定义 第一步
@Bean
public UserRealm userRealm() {
return new UserRealm();
}
}
login.html
登陆
用户名:
密码:
MyController
@RequestMapping(“/toLogin”)
public String toLogin(){
return “login”;
}
8、Shiro实现用户认证
MyController
@RequestMapping(“/login”)
public String login(String username,String password,Model model){
//获取当前的用户
Subject subject = SecurityUtils.getSubject();
//封装登陆用户的登陆数据
UsernamePasswordToken token = new UsernamePasswordToken(username, password);
try{
subject.login(token);//执行登陆方法,如果没有异常就说明ok
return “index”;
}catch (UnknownAccountException e){//用户名不存在
model.addAttribute(“msg”,“用户名错误”);
return “login”;
}catch (IncorrectCredentialsException e){//密码不存在
model.addAttribute(“msg”,“密码错误”);
return “login”;
}
}
login.html
登陆
用户名:
密码:
UserRealm
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println(“执行了=》认证doGetAuthenticationInfo”);
//用户名 密码 —数据库
String name=“root”;
String password=“123456”;
UsernamePasswordToken userToken = (UsernamePasswordToken) token;
if (!userToken.getUsername().equals(name)){
return null;//抛出异常UnknownAccountException
}
//密码认证 shiro
return new SimpleAuthenticationInfo(“”,password,“”);
}
9、Shiro整合Mybatis
导入依赖
mysql
mysql-connector-java
log4j
log4j
1.2.17
com.alibaba
druid
1.2.6
org.mybatis.spring.boot
mybatis-spring-boot-starter
2.2.0
2.连接数据库application.yml
spring:
datasource:
username: root
password: 981204
#?serverTimezone=UTC解决时区的报错
url: jdbc:mysql://localhost:3306/mybatis?serverTimezone=UTC&useUnicode=true&characterEncoding=utf-8
driver-class-name: com.mysql.jdbc.Driver
type: com.alibaba.druid.pool.DruidDataSource
#Spring Boot 默认是不注入这些属性值的,需要自己绑定
#druid 数据源专有配置
initialSize: 5
minIdle: 5
maxActive: 20
maxWait: 60000
timeBetweenEvictionRunsMillis: 60000
minEvictableIdleTimeMillis: 300000
validationQuery: SELECT 1 FROM DUAL
testWhileIdle: true
testOnBorrow: false
testOnReturn: false
poolPreparedStatements: true
#配置监控统计拦截的filters,stat:监控统计、log4j:日志记录、wall:防御sql注入
#如果允许时报错 java.lang.ClassNotFoundException: org.apache.log4j.Priority
#则导入 log4j 依赖即可,Maven 地址: https://mvnrepository.com/artifact/log4j/log4j
filters: stat,wall,log4j
maxPoolPreparedStatementPerConnectionSize: 20
useGlobalDataSourceStat: true
connectionProperties: druid.stat.mergeSql=true;druid.stat.slowSqlMillis=500
3.设置application.properties
整合mybatis
mybatis.type-aliases-package=com.kk.pojo
mybatis.mapper-locations=classpath:mapper/*.xml
4.实体类
package com.kk.pojo;
public class User {
private int id;
private String name;
private String pwd;
public User() {
}
public User(int id, String name, String pwd) {
this.id = id;
this.name = name;
this.pwd = pwd;
}
public int getId() {
return id;
}
public void setId(int id) {
this.id = id;
}
public String getName() {
return name;
}
public void setName(String name) {
this.name = name;
}
public String getPwd() {
return pwd;
}
public void setPwd(String pwd) {
this.pwd = pwd;
}
@Override
public String toString() {
return “User{” +
“id=” + id +
“, name='” + name + ‘’’ +
“, pwd='” + pwd + ‘’’ +
‘}’;
}
}
5.UserMapper
package com.kk.mapper;
import org.apache.ibatis.annotations.Mapper;
import org.springframework.stereotype.Repository;
@Repository
@Mapper
public class UserMapper {
public User queryUserByName(String name);
}
6.UserMapper.xml
<?xml version="1.0" encoding="UTF-8" ?>select * from mybatis.user where name = #{name}
7.UserService
public interface UserService {
public User queryUserByName(String name);
}
8.UserServiceImpl
package com.kk.service;
import org.springframework.stereotype.Service;
@Service
public class UserServiceImp implements UserService{
@Autowired
UserMapper userMapper;
@Override
public User queryUserByName(String name) {
return userMapper.queryUserByName(name);
}
}
9.测试查出对应User
@SpringBootTest
class ShiroSpringbootApplicationTests {
@Autowired
UserServiceImpl userService;
@Test
void contextLoads() {
System.out.println(userService.queryUserByName(“雏田”));
}
}
10、测试成功后 将数据绑定到安全配置中,再次启动配置
package com.kk.config;
import com.kk.pojo.User;
import com.kk.service.UserService;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.subject.Subject;
import org.springframework.beans.factory.annotation.Autowired;
//自定义的 UserRealm extends AuthorizingRealm
public class UserRealm extends AuthorizingRealm {
@Autowired
UserService userService;
//授权
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println(“执行了=》授权doGetAuthorizationInfo”);
return null;
}
//认证
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println(“执行了=》认证doGetAuthenticationInfo”);
UsernamePasswordToken userToken = (UsernamePasswordToken) token;
//连接真实数据库
User user = userService.queryUserByName(userToken.getUsername());
if (user==null){ //没有这个用户
return null; //抛出异常UnknownAccountException
}
//密码认证 shiro
//可以加密 MD5加密 MD5盐值加密
return new SimpleAuthenticationInfo(“”,user.getPwd(),“”);
}
}
10、Shiro请求授权实现
1、授权正常的情况下,没有授权会跳转到未授权页面
package com.kk.config;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.springframework.beans.factory.annotation.Qualifier;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
import java.util.Map;
@Configuration
public class ShiroConfig {
//ShiroFilterFactoryBean:3
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(@Qualifier(“securityManager”) DefaultWebSecurityManager defaultWebSecurityManager) {
ShiroFilterFactoryBean bean = new ShiroFilterFactoryBean();
//设置安全管理器
bean.setSecurityManager(defaultWebSecurityManager);
/*anon:无需认 证就可以访问
authc:必须认证了 才能让问
user:.必须拥有 记住我功能才能用
perms:
拥有对某个资源的权限才能访间:
role:拥有某 个角色权限才能访问
*/
Map<String, String> filterMap = new LinkedHashMap<>();
//授权,正常的情况下,没有授权会跳转到未授权页面
filterMap.put(“/user/add”, “perms[user:add]”);
filterMap.put(“/user/update”, “perms[user:update]”);
//第二个为权限,只有persm=user:add/user:update] 才可能进入相应的页面
filterMap.put(“/user/*”, “authc”);
//filterMap.put(“/user/add”, “authc”);
//filterMap.put(“/user/update”, “authc”);
bean.setFilterChainDefinitionMap(filterMap);
//设置获录的请求
bean.setLoginUrl(“/toLogin”);
//未授权页面
bean. setUnauthorizedUrl(“/noauth”);
return bean;
}
//Dafaul tWebSecurityManager:2
@Bean(name = “securityManager”)
public DefaultWebSecurityManager getDefaultwebSecurityManager(@Qualifier(“userRealm”) UserRealm userRealm) {
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
//关联UserReaLm
securityManager.setRealm(userRealm);
return securityManager;
}
//创建UserRealm对象,需要自定义类:1
@Bean
public UserRealm userRealm() {
return new UserRealm();
}
}
controller
@RequestMapping(“/noauth”)
@ResponseBody
public String unauthorized() {
return “未经授权无法访问此页面”;
}
2、授予可以访问的权限
package com.kk.config;
import com.kk.pojo.User;
import com.kk.service.UserService;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.subject.Subject;
import org.springframework.beans.factory.annotation.Autowired;
public class UserRealm extends AuthorizingRealm {
@Autowired
UserService userService;
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println(“执行了=》授权doGetAuthorizationInfo”);
//SimpleAuthorizationInfo
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
info.addStringPermission(“user:add”);
return info;
}
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println(“执行了=》验证doGetAuthorizationInfo”);
UsernamePasswordToken userToken = (UsernamePasswordToken) token;
//连接真实的数据库
User user = userService.queryUserByName(userToken.getUsername());
if (user == null) { //没有这个用户
return null; //UnknownAccountException
}
//可以加密: MD5: e10adc3949ba59abbe56e057f20f883e MD5 盐值加密: e10adc3949ba59abbe56e057f20f883eusername
//密码认证, shiro 做~
return new SimpleAuthenticationInfo(“”, user.getPwd(), “”);
}
}
3、一般在数据库里添加权限的字段,修改数据库,和实体类
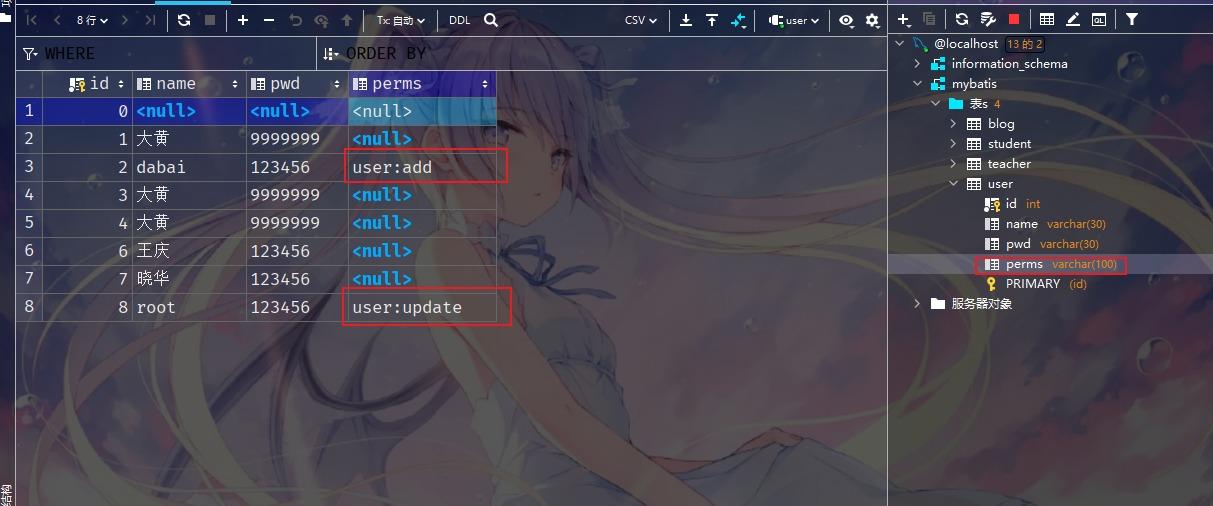
实体类
private int id;
private String name;
private String pwd;
private String perms;
UserRealm实现授权的分配
package com.kk.config;
import com.kk.pojo.User;
import com.kk.service.UserService;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.subject.Subject;
import org.springframework.beans.factory.annotation.Autowired;
public class UserRealm extends AuthorizingRealm {
@Autowired
UserService userService;
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println(“执行了=》授权doGetAuthorizationInfo”);
//SimpleAuthorizationInfo
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
//info.addStringPermission(“user:add”);
//拿到当登录 的这个对象
Subject subject = SecurityUtils.getSubject();
User currentUser = (User) subject.getPrincipal(); //拿到User对象
//设置当前用户的权限
info.addStringPermission(currentUser.getPerms());
return info;
}
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println(“执行了=》验证doGetAuthorizationInfo”);
UsernamePasswordToken userToken = (UsernamePasswordToken) token;
//连接真实的数据库
User user = userService.queryUserByName(userToken.getUsername());
if (user == null) { //没有这个用户
return null; //UnknownAccountException
}
//可以加密: MD5: e10adc3949ba59abbe56e057f20f883e MD5 盐值加密: e10adc3949ba59abbe56e057f20f883eusername
//密码认证, shiro 做~
return new SimpleAuthenticationInfo(user, user.getPwd(), “”);
}
}
3.使用shirothymeleaf
在html页面中导入
xmlns:shiro="http://www.thymeleaf.org/thymeleaf-extras-shiro
xmlns:shiro=“http://www.thymeleaf.org/thymeleaf-extras-shiro”>
首页
登录
add
update
4.测试
存在登录按钮的问题
UserRealm中添加session
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println(“执行了=》验证doGetAuthorizationInfo”);
UsernamePasswordToken userToken = (UsernamePasswordToken) token;
//连接真实的数据库
User user = userService.queryUserByName(userToken.getUsername());
if (user == null) { //没有这个用户
return null; //UnknownAccountException
}
Subject currentSubject = SecurityUtils.getSubject();
Session session = currentSubject.getSession();
session.setAttribute(“loginUser”,user);
//可以加密: MD5: e10adc3949ba59abbe56e057f20f883e MD5 盐值加密: e10adc3949ba59abbe56e057f20f883eusername
//密码认证, shiro 做~
return new SimpleAuthenticationInfo(user, user.getPwd(), “”);
}
}
index.html
xmlns:shiro=“http://www.thymeleaf.org/thymeleaf-extras-shiro”>
还有兄弟不知道网络安全面试可以提前刷题吗?费时一周整理的160+网络安全面试题,金九银十,做网络安全面试里的显眼包!
王岚嵚工程师面试题(附答案),只能帮兄弟们到这儿了!如果你能答对70%,找一个安全工作,问题不大。
对于有1-3年工作经验,想要跳槽的朋友来说,也是很好的温习资料!
【完整版领取方式在文末!!】
93道网络安全面试题
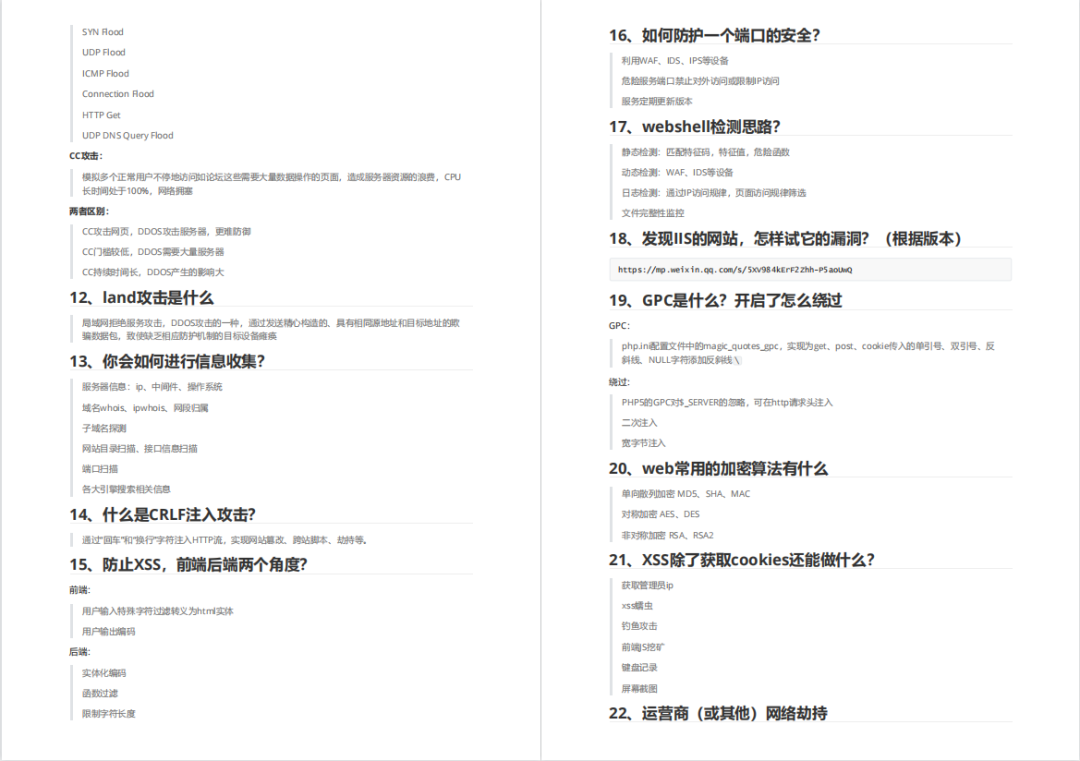
需要体系化学习资料的朋友,可以加我V获取:vip204888 (备注网络安全)
内容实在太多,不一一截图了
黑客学习资源推荐
最后给大家分享一份全套的网络安全学习资料,给那些想学习 网络安全的小伙伴们一点帮助!
对于从来没有接触过网络安全的同学,我们帮你准备了详细的学习成长路线图。可以说是最科学最系统的学习路线,大家跟着这个大的方向学习准没问题。
😝朋友们如果有需要的话,可以联系领取~
1️⃣零基础入门
① 学习路线
对于从来没有接触过网络安全的同学,我们帮你准备了详细的学习成长路线图。可以说是最科学最系统的学习路线,大家跟着这个大的方向学习准没问题。
② 路线对应学习视频
同时每个成长路线对应的板块都有配套的视频提供:

2️⃣视频配套工具&国内外网安书籍、文档
① 工具
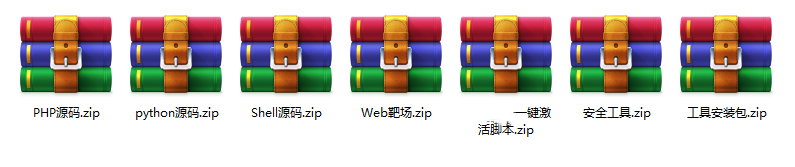
② 视频

③ 书籍
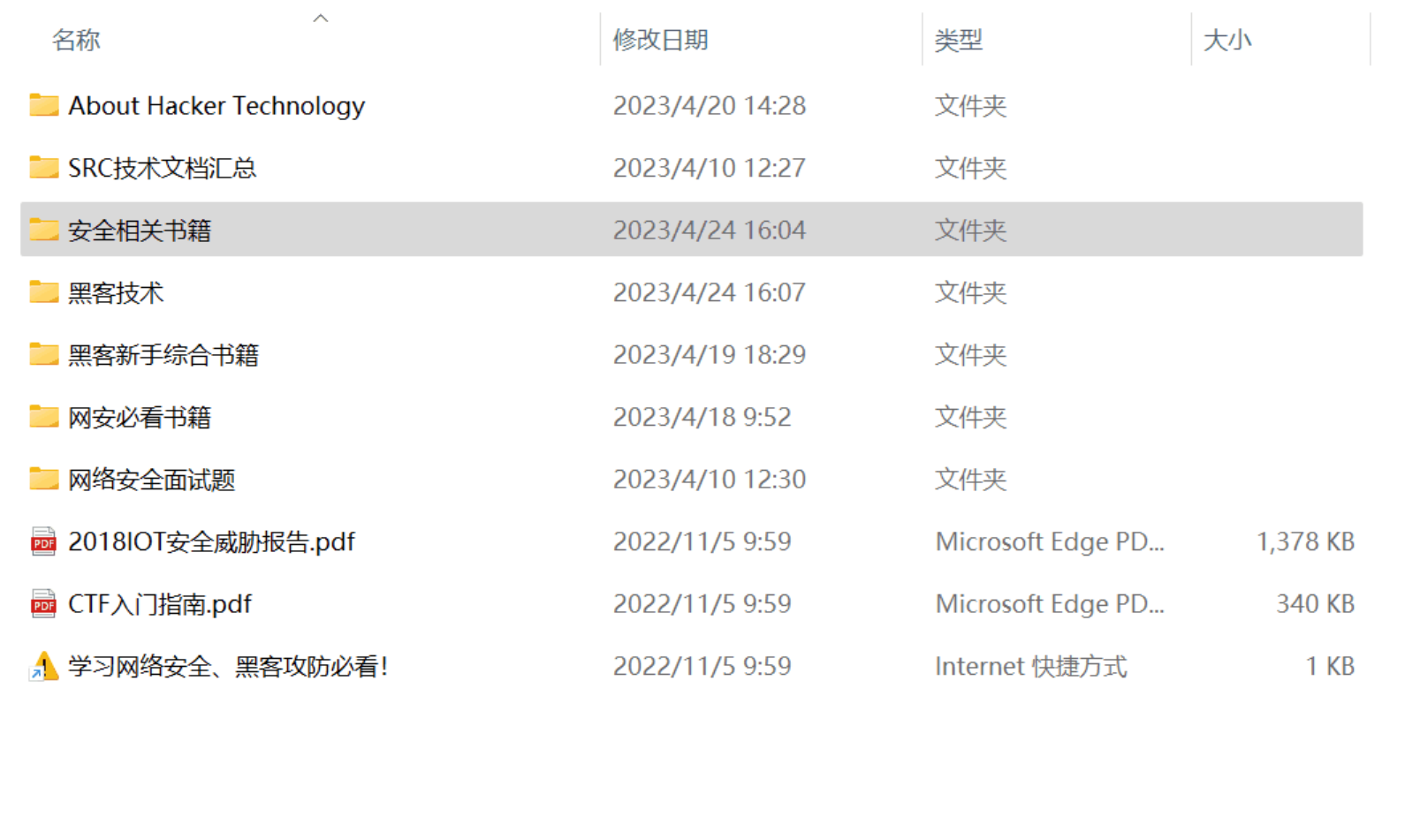
资源较为敏感,未展示全面,需要的最下面获取
② 简历模板
因篇幅有限,资料较为敏感仅展示部分资料,添加上方即可获取👆
网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。
一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!






















 1995
1995

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








