
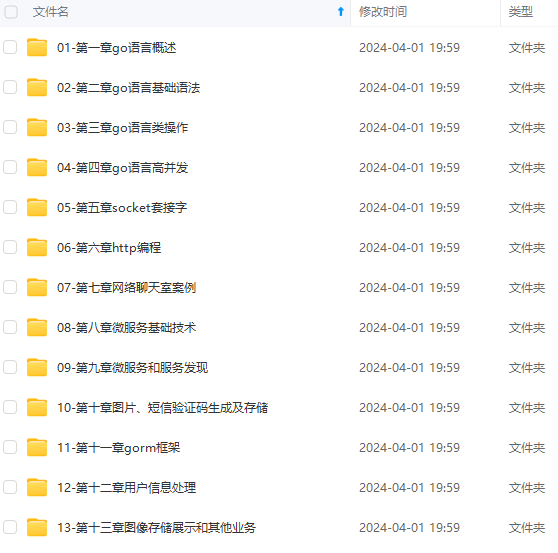

既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,涵盖了95%以上Go语言开发知识点,真正体系化!
由于文件比较多,这里只是将部分目录截图出来,全套包含大厂面经、学习笔记、源码讲义、实战项目、大纲路线、讲解视频,并且后续会持续更新
tls.TLS_RSA_WITH_AES_256_CBC_SHA,
}
}
在 NewClientTLSConfig 方法里面增加如下内容
if caPath != “” {
pool, err := newCertPool(caPath)
if err != nil {
return nil, err
}
base.RootCAs = pool
base.InsecureSkipVerify = false
//20240206 TLS CVE-2016-2183
base.PreferServerCipherSuites = false
base.MinVersion = tls.VersionTLS12
base.CipherSuites = []uint16{
tls.TLS_RSA_WITH_AES_128_GCM_SHA256,
tls.TLS_RSA_WITH_AES_256_GCM_SHA384,
tls.TLS_RSA_WITH_AES_128_CBC_SHA,
tls.TLS_RSA_WITH_AES_256_CBC_SHA,
}
} else {
base.InsecureSkipVerify = true
}
重新编译frp即可
go build -trimpath -ldflags "-s -w" -buildvcs=false -o bin/frps ./cmd/frps
go build -trimpath -ldflags "-s -w" -buildvcs=false -o bin/frpc ./cmd/frpc
效果检查 :
修复前进行扫描:
root@armbian:~# nmap -sV -p 7000 --script ssl-enum-ciphers X.X.X.X
Starting Nmap 7.80 ( https://nmap.org ) at 2024-02-06 12:47 CST
Nmap scan report for X.X.X.X
Host is up (0.0060s latency).
PORT STATE SERVICE VERSION
7000/tcp open ssl/unknown
| ssl-enum-ciphers:
| TLSv1.0:
| ciphers:
| TLS\_RSA\_WITH\_AES\_128\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_3DES\_EDE\_CBC\_SHA (rsa 2048) - C
| compressors:
| NULL
| cipher preference: server
| warnings:
| 64-bit block cipher 3DES vulnerable to SWEET32 attack
| Forward Secrecy not supported by any cipher
| TLSv1.1:
| ciphers:
| TLS\_RSA\_WITH\_AES\_128\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_3DES\_EDE\_CBC\_SHA (rsa 2048) - C
| compressors:
| NULL
| cipher preference: server
| warnings:
| 64-bit block cipher 3DES vulnerable to SWEET32 attack
| Forward Secrecy not supported by any cipher
| TLSv1.2:
| ciphers:
| TLS\_RSA\_WITH\_AES\_128\_GCM\_SHA256 (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_GCM\_SHA384 (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_128\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_3DES\_EDE\_CBC\_SHA (rsa 2048) - C
| compressors:
| NULL
| cipher preference: server
| warnings:
| 64-bit block cipher 3DES vulnerable to SWEET32 attack
| Forward Secrecy not supported by any cipher
|\_ least strength: C
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.19 seconds
修复隐患后重新扫描:
root@armbian:~# nmap -sV -p 7000 --script ssl-enum-ciphers X.X.X.X
Starting Nmap 7.80 ( https://nmap.org ) at 2024-02-06 13:19 CST
Nmap scan report for X.X.X.X
Host is up (0.0039s latency).
PORT STATE SERVICE VERSION
7000/tcp open ssl/unknown
| ssl-enum-ciphers:
| TLSv1.2:
| ciphers:
| TLS\_RSA\_WITH\_AES\_128\_GCM\_SHA256 (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_GCM\_SHA384 (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_128\_CBC\_SHA (rsa 2048) - A
| TLS\_RSA\_WITH\_AES\_256\_CBC\_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: server
| warnings:
| Forward Secrecy not supported by any cipher
|\_ least strength: A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 21.06 seconds
可以看到,修复效果非常明显,相信不会再被扫描出漏洞了。


**网上学习资料一大堆,但如果学到的知识不成体系,遇到问题时只是浅尝辄止,不再深入研究,那么很难做到真正的技术提升。**
**[需要这份系统化的资料的朋友,可以添加戳这里获取](https://bbs.csdn.net/topics/618658159)**
**一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!**
获取](https://bbs.csdn.net/topics/618658159)**
**一个人可以走的很快,但一群人才能走的更远!不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!**






















 624
624











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








