题目分析:
1、暴力破解;
2、MT19937「梅森旋转算法」(「Mersenne twister」)
解题
首先我们获得两个文件
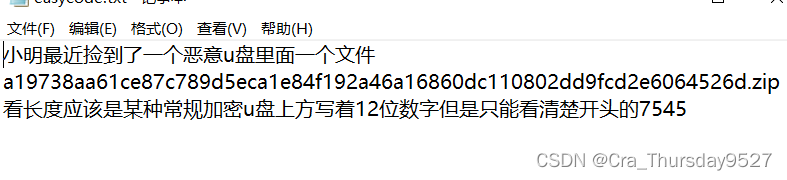
easycode.txt中含有flag.zip密码提示
对flag.zip进行暴力破解,使用Ziperello

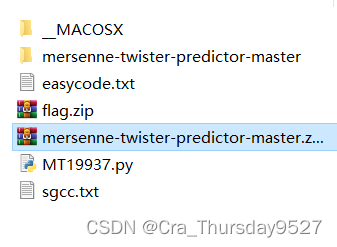
 解压得
解压得
MT19937即「梅森旋转算法」(「Mersenne twister」)是一个伪随机数生成算法。
文件MT19937.py为题目内容
import random
from hashlib import md5
from mt19937predictor import MT19937Predictor
def get_mask():
file = open("sgcc.txt", "w")
for i in range(104):
file.write(str(random.getrandbits(32)) + "\n")
file.write(str(random.getrandbits(64)) + "\n")
file.write(str(random.getrandbits(96)) + "\n")
file.write(str(random.getrandbits(128)) + "\n")
file.close()
get_mask()
flag = md5(str(random.getrandbits(32)).encode()).hexdigest()
print(flag)
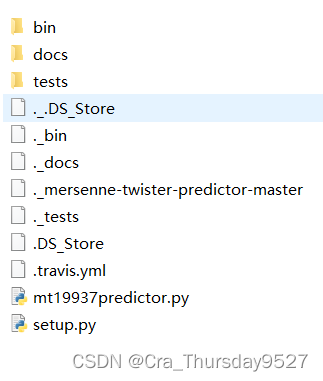
文件mt19937predictor.py为梅森旋转算法的基本程序
参考BUUCTF-CRYPTO-[V&N2020 公开赛]Backtrace
获得关于梅森旋转算法破解的最基本条件
(1)MT19937算法生产随机数的过程
1.利用seed初始化624的状态
2.对状态进行旋转
3.根据状态提取伪随机数 (2)逆向 extract_number extract_number函数,可以发现输出的伪随机数是对state[i]进行了异或,位运算后的结果。预测随机数的题型就是基于对extract_number
函数的逆向,我们可以根据题目输出的随机数逆向extract_number得到对应的n个state(n>624),实际上只需要前624个随机数恢复前624个state,就可以预测此后生成的随机数。
即已知624个随机数便可预测此后生成的随机数(向前预测同理)
解法一
使用RandCrack函数,可以直接处理并破解梅森旋转算法
梅森算法逆向需要至少623个32位随机数
本题有104*(32+64+96+128)/32=1040个随机数,符合逆向要求
但梅森算法只能生成32位随机数,我们需要解决高位随机数如何在梅森算法中如何分解逆向
参考博客[GKCTF 2021]Random(MT19973随机数破解)
from randcrack import RandCrack
from hashlib import md5
l = open('sgcc.txt','r').readlines()
l = [int(i.strip()) for i in l]
t = []
for i in range(len(l)):
if i % 4 == 0:# 32
t.append(l[i])
elif i % 4 == 1: #64
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] >> 32)
elif i % 4 == 2: #96
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] & (2 ** 64 - 1) >> 32)
t.append(l[i] >> 64)
else :#128
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] & (2 ** 64 - 1) >> 32)
t.append(l[i] & (2 ** 96 - 1) >> 64)
t.append(l[i] >> 96)
t=t[-624:] ##取后624位随机数
rc = RandCrack()
for i in t:
rc.submit(i)
flag = rc.predict_getrandbits(32)
print(md5(str(flag).encode()).hexdigest())
解法二
手动运算
将解法一中对于高位随机数逆向运算引入
参考BUUCTF-CRYPTO-[V&N2020 公开赛]Backtrace
!python3
# -*- coding: utf-8 -*-
# @Time : 2020/10/25 21:59
# @Author : A.James
# @FileName: exp2.py
from random import Random
from hashlib import md5
# right shift inverse
def inverse_right(res,shift,bits=32):
tmp = res
for i in range(bits//shift):
tmp = res ^ tmp >> shift
return tmp
# right shift with mask inverse
def inverse_right_values(res,shift,mask,bits=32):
tmp = res
for i in range(bits//shift):
tmp = res ^ tmp>>shift & mask
return tmp
# left shift inverse
def inverse_left(res,shift,bits=32):
tmp = res
for i in range(bits//shift):
tmp = res ^ tmp << shift
return tmp
# left shift with mask inverse
def inverse_left_values(res,shift,mask,bits=32):
tmp = res
for i in range(bits//shift):
tmp = res ^ tmp << shift & mask
return tmp
def backtrace(cur):
high = 0x80000000
low = 0x7fffffff
mask = 0x9908b0df
state = cur
for i in range(3,-1,-1):
tmp = state[i+624]^state[i+397]
# recover Y,tmp = Y
if tmp & high == high:
tmp ^= mask
tmp <<= 1
tmp |= 1
else:
tmp <<=1
# recover highest bit
res = tmp&high
# recover other 31 bits,when i =0,it just use the method again it so beautiful!!!!
tmp = state[i-1+624]^state[i+396]
# recover Y,tmp = Y
if tmp & high == high:
tmp ^= mask
tmp <<= 1
tmp |= 1
else:
tmp <<=1
res |= (tmp)&low
state[i] = res
return state
def recover_state(out):
state = []
for i in out:
i = inverse_right(i,18)
i = inverse_left_values(i,15,0xefc60000)
i = inverse_left_values(i,7,0x9d2c5680)
i = inverse_right(i,11)
state.append(i)
return state
l = open('sgcc.txt','r').readlines()
l = [int(i.strip()) for i in l]
#print(l)
t = []
for i in range(len(l)):
if i % 4 == 0:# 32
t.append(l[i])
elif i % 4 == 1: #64
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] >> 32)
elif i % 4 == 2: #96
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] & (2 ** 64 - 1) >> 32)
t.append(l[i] >> 64)
else :#128
t.append(l[i] & (2 ** 32 - 1))
t.append(l[i] & (2 ** 64 - 1) >> 32)
t.append(l[i] & (2 ** 96 - 1) >> 64)
t.append(l[i] >> 96)
partS = recover_state(t)
state = backtrace(partS+[0])[-624:] ##获取后624位随机数
prng = Random()
prng.setstate((3,tuple(state+[624]),None))
flag = md5(str(prng.getrandbits(32)).encode()).hexdigest()
print(flag)
























 2738
2738











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








