第一章、小叙
微软8月份纰漏了很多漏洞,最为严重的是高达9.8分的高危漏洞TCP/IP 远程代码执行漏洞,漏洞编号CVE-2024-38063,该漏洞正在蔓延,攻击者可以向受影响的应用程序发送特制请求,触发缓冲区溢出导致远程代码执行,可远程执行入侵。请自查!
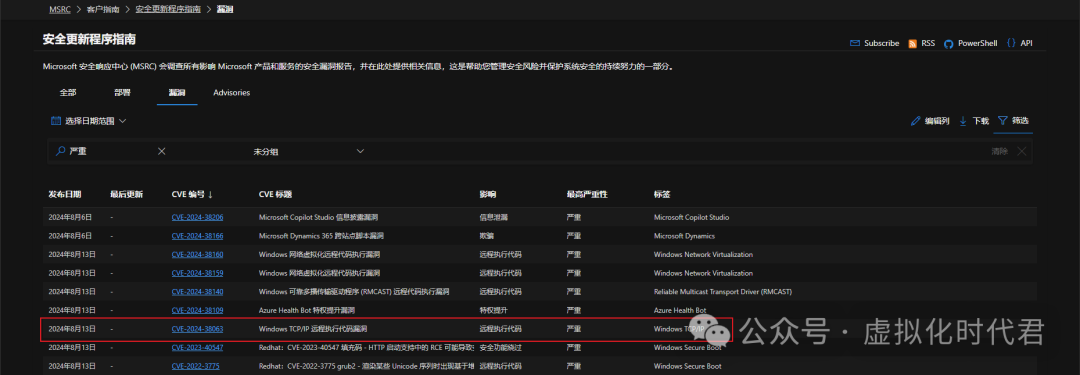
第二章、漏洞等级
严重(CVSS9.8)
第三章、漏洞风险
攻击者利用该漏洞可导致远程代码执行。无需以用户身份进行身份验证,无需文件的交互,可远程进行文件的查看、系统的设置等等。
第三章、影响范围
以下为官方提供影响版本范围
| Windows 11 Version 24H2 for x64-based Systems |
| Windows 11 Version 24H2 for ARM64-based Systems |
| Windows Server 2012 R2 (Server Core installation) |
| Windows Server 2012 R2 |
| Windows Server 2012 (Server Core installation) |
| Windows Server 2012 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) |
| Windows Server 2008 for x64-based Systems Service Pack 2 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) |
| Windows Server 2008 for 32-bit Systems Service Pack 2 |
| Windows Server 2016 (Server Core installation) |
| Windows Server 2016 |
| Windows 10 Version 1607 for x64-based Systems |
| Windows 10 Version 1607 for 32-bit Systems |
| Windows 10 for x64-based Systems |
| Windows 10 for 32-bit Systems |
| Windows Server 2022, 23H2 Edition (Server Core installation) |
| Windows 11 Version 23H2 for x64-based Systems |
| Windows 11 Version 23H2 for ARM64-based Systems |
| Windows 10 Version 22H2 for 32-bit Systems |
| Windows 10 Version 22H2 for ARM64-based Systems |
| Windows 10 Version 22H2 for x64-based Systems |
| Windows 11 Version 22H2 for x64-based Systems |
| Windows 11 Version 22H2 for ARM64-based Systems |
| Windows 10 Version 21H2 for x64-based Systems |
| Windows 10 Version 21H2 for ARM64-based Systems |
| Windows 10 Version 21H2 for 32-bit Systems |
| Windows 11 version 21H2 for ARM64-based Systems |
| Windows 11 version 21H2 for x64-based Systems |
| Windows Server 2022 (Server Core installation) |
| Windows Server 2022 |
| Windows Server 2019 (Server Core installation) |
| Windows Server 2019 |
| Windows 10 Version 1809 for ARM64-based Systems |
| Windows 10 Version 1809 for x64-based Systems |
| Windows 10 Version 1809 for 32-bit Systems |
第四章、修复建议
微软官方已发布漏洞补丁及修复版本,地址参考:
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38063(请根据自己业务情况进行评估升级)
第五章、临时修复方案
检查Windows服务器是否使用IPv6协议;
1)按打开Windows 键+R。然后键入 ncpa.cpl,然后按 Enter 键;
2)右键单击网络适配器,点击“属性”;
3)搜索 Internet协议版本6(TCP/IPv6)。如果该选项已选中,要禁用IPV6,请取消选中该选项,然后单击“确定”保存更改。
第六章、安全补丁
Windows 11 24H2 安全补丁: kb5041571
Windows 11 23H2 [kb5041585];
Windows 11 22H2 [kb5041585];
Windows 11 21H2 [kb5041592];
Windows Server 2022, 23H2 [kb5041573];
Windows 10 22H2 [kb5041580];
Windows 10 21H2 [kb5041580];
Windows 10 Version 1809 [kb5041578];
Windows 10 1607 [kb5041773];
Windows 10 [kb5041782];
Windows Server 2022 [kb5041160];
Windows Server 2019 [kb5041578];
Windows Server 2016 [kb5041773];
Windows Server 2012 R2 [kb5041828]
Windows Server 2012 [kb5041851];
Windows Server 2008 R2 [kb5041838];
Windows Server 2008 R2 for x64-based Systems Service Pack 1 [kb5041838];
Windows Server 2008 R2 for x64-based Systems Service Pack 1 [kb5041823];
Windows Server 2008 for 32-bit Systems Service Pack 2 [kb5041850];
Windows Server 2008 for 32-bit Systems Service Pack 2 [kb5041847];
第七章、往期回顾
解决方案:如何在虚拟机中扩展 Windows 11 C 盘,绕过恢复分区的限制!
探索Windows秘密:揭晓30个常用端口的神秘面纱与使用技巧
Windows Server 2019 会话远程桌面-快速部署(RemoteApp)
Windows Server 2019 WSUS补丁服务器安装图解教程
每日一句
“生活就像骑自行车,只有不断前行,才能保持平衡。”























 5146
5146

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










