BR/EDR
- Prior to version 2.1 => BR/EDR legacy
- Version 2.1 => BR/EDR (uses Secure Simple Pairing)
- Version 4.2 => BR/EDR (uses Secure Connections)
LE
- Version 4.0 and 4.1 => LE legacy (uses Secure Simple Pairing)
- Version 4.2 => LE (uses Secure Connections)
Legacy
It all started with the initial security algorithms (BR/EDR legacy) for the following security features:
- pairing
- bonding
- device authentication
- message encryption
- message integrity
The algorithms used in BR/EDR legacy were not FIPS approved.
Secure Simple Pairing
This was introduced in version 2.1. Secure Simple Pairing uses FIPS-approved algorithms for pairing and message integrity and so in essence it upgraded the security of BR/EDR legacy, which is why we call this new one BR/EDR security.
Version 4.0 ported the exact same security model as BR/EDR to Low Energy (LE), with the following exceptions:
- no Numeric Comparison equivalent
- Just Works and Passkey Entry do not provide passive eavesdropping protection, because ECDH is not used in LE 4.0.
Secure Connections
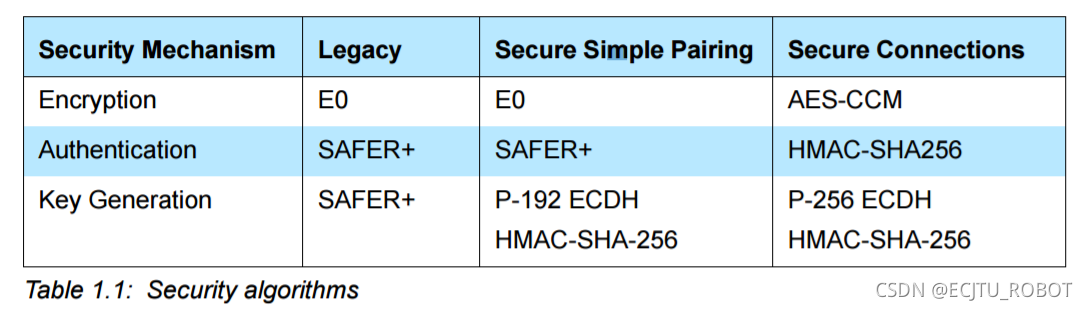
In version 4.1, the Secure Connections feature was added to BR/EDR. This was an upgrade to the existing Secure Simple Pairing algorithms for pairing, device authentication, and message integrity. See table for a comparison with the Simple Pairing method for BR/EDR (not LE!):
Version 4.2 then upgraded LE as well. One of the main improvements was the adoption of ECDH for pairing. It also modified the Numeric Comparison association model to be used on Bluetooth LE. LE pairing used in 4.0 and 4.1 is since then referred to as LE Legacy. LE Secure Connections and BR/EDR Secure Connections are functionally equal.
























 9464
9464

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








