文章目录
安装搭建环境
首先需要安装部署docker,我们这里使用的是docker安装部署Harbor仓库。
这里我们就不安装了,点击下方连接,有详细的安装步骤。
Harbor包下载链接
docker-compose下载链接
上传所需的包
安装部署Harbor仓库时必须要有docker-compose,所以我们这上传
[root@localhost ~]# ls
docker-compose-linux-x86_64 harbor-offline-installer-v2.1.1.tgz
给docker-compose增加权限
[root@localhost ~]# mv docker-compose-linux-x86_64 /usr/local/bin/docker-compose
[root@localhost ~]# chmod +x /usr/local/bin/docker-compose
[root@localhost ~]# docker-compose -v
Docker Compose version v2.22.0
解压软件包到指定位置
[root@localhost ~]# tar -zxvf harbor-offline-installer-v2.1.1.tgz -C /usr/local/
harbor/harbor.v2.1.1.tar.gz
harbor/prepare
harbor/LICENSE
harbor/install.sh
harbor/common.sh
harbor/harbor.yml.tmpl
创建ssl证书
首先需要常见ssl证书存放目录
[root@localhost harbor]# mkdir cret
[root@localhost harbor]# cd cret/
安装所需工具
[root@localhost cret]# yum -y install openssl
Loaded plugins: fastestmirror
Loading mirror speeds from cached hostfile
* base: mirrors.aliyun.com
* epel: mirrors.tuna.tsinghua.edu.cn
* extras: mirrors.aliyun.com
* updates: mirrors.aliyun.com
Resolving Dependencies
--> Running transaction check
---> Package openssl.x86_64 1:1.0.2k-12.el7 will be updated
---> Package openssl.x86_64 1:1.0.2k-26.el7_9 will be an update
--> Processing Dependency: openssl-libs(x86-64) = 1:1.0.2k-26.el7_9 for package: 1:openssl-1.0.2k-26.el7_9.x86_64
--> Running transaction check
---> Package openssl-libs.x86_64 1:1.0.2k-12.el7 will be updated
---> Package openssl-libs.x86_64 1:1.0.2k-26.el7_9 will be an update
--> Finished Dependency Resolution
Dependencies Resolved
======================================================================================================================================================================================================
Package Arch Version Repository Size
======================================================================================================================================================================================================
Updating:
openssl x86_64 1:1.0.2k-26.el7_9 updates 494 k
Updating for dependencies:
openssl-libs x86_64 1:1.0.2k-26.el7_9 updates 1.2 M
Transaction Summary
======================================================================================================================================================================================================
Upgrade 1 Package (+1 Dependent package)
Total download size: 1.7 M
Downloading packages:
Delta RPMs disabled because /usr/bin/applydeltarpm not installed.
(1/2): openssl-1.0.2k-26.el7_9.x86_64.rpm | 494 kB 00:00:00
(2/2): openssl-libs-1.0.2k-26.el7_9.x86_64.rpm | 1.2 MB 00:00:00
------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Total 1.4 MB/s | 1.7 MB 00:00:01
Running transaction check
Running transaction test
Transaction test succeeded
Running transaction
Updating : 1:openssl-libs-1.0.2k-26.el7_9.x86_64 1/4
Updating : 1:openssl-1.0.2k-26.el7_9.x86_64 2/4
Cleanup : 1:openssl-1.0.2k-12.el7.x86_64 3/4
Cleanup : 1:openssl-libs-1.0.2k-12.el7.x86_64 4/4
Verifying : 1:openssl-libs-1.0.2k-26.el7_9.x86_64 1/4
Verifying : 1:openssl-1.0.2k-26.el7_9.x86_64 2/4
Verifying : 1:openssl-1.0.2k-12.el7.x86_64 3/4
Verifying : 1:openssl-libs-1.0.2k-12.el7.x86_64 4/4
Updated:
openssl.x86_64 1:1.0.2k-26.el7_9
Dependency Updated:
openssl-libs.x86_64 1:1.0.2k-26.el7_9
Complete!
创建ssl证书
首先创建ca密钥
[root@localhost cret]# openssl genrsa -out ca.key 4096
Generating RSA private key, 4096 bit long modulus
.........................................................................................................................................................................++
..............................................................................................................................................................................................++
e is 65537 (0x10001)
在创建ca证书,前提是已经创建了ca密钥
中间的IP地址,修改为自己宿主机的IP地址
注意:这里的IP地址需要和配置文件中的相同。
[root@localhost cret]# openssl req -x509 -new -nodes -sha512 -days 3650 -subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=192.168.1.11" -key ca.key -out ca.crt
在创建已宿主机IP地址为名称的私钥
[root@localhost cret]# openssl genrsa -out 192.168.1.11.key 4096
Generating RSA private key, 4096 bit long modulus
...............................................................................................................................................................................................++
...........++
e is 65537 (0x10001)
[root@localhost cret]# openssl req -sha512 -new -subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=192.168.1.11" -key 192.168.1.11.key -out 192.168.1.11.csr
[root@localhost cret]# cat > v3.ext <<-EOF
> authorityKeyIdentifier=keyid,issuer
> basicConstraints=CA:FALSE
> keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
> extendedKeyUsage = serverAuth
> subjectAltName = @alt_names
>
> [alt_names]
> DNS.1=192.168.1.11
> EOF
[root@localhost cret]# openssl x509 -req -sha512 -days 3650 -extfile v3.ext -CA ca.crt -CAkey ca.key -CAcreateserial -in 192.168.1.11.csr -out 192.168.1.11.crt
Signature ok
subject=/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=192.168.1.11
Getting CA Private Key
到此我们的所有ssl正式已经创建完成,我们查看一一下
[root@localhost cret]# ll
total 28
-rw-r--r-- 1 root root 2061 Oct 24 19:35 192.168.1.11.crt
-rw-r--r-- 1 root root 1704 Oct 24 19:34 192.168.1.11.csr
-rw-r--r-- 1 root root 3243 Oct 24 19:33 192.168.1.11.key
-rw-r--r-- 1 root root 2029 Oct 24 19:30 ca.crt
-rw-r--r-- 1 root root 3243 Oct 24 19:29 ca.key
-rw-r--r-- 1 root root 17 Oct 24 19:35 ca.srl
-rw-r--r-- 1 root root 232 Oct 24 19:34 v3.ext
修改Harbor文件
修改配置文件
这里需要修改为宿主机的IP地址
这里本身没有harbor.yml文件,我们需要把harbor.yml.tmpl修改名称。
[root@localhost ~]# cd /usr/local/harbor/
[root@localhost harbor]# cp harbor.yml.tmpl harbor.yml
[root@localhost harbor]# cat harbor.yml
# Configuration file of Harbor
# The IP address or hostname to access admin UI and registry service.
# DO NOT use localhost or 127.0.0.1, because Harbor needs to be accessed by external clients.
hostname: 192.168.1.11 #这里需要修改IP地址,修改为宿主机的地址
# http related config
http:
# port for http, default is 80. If https enabled, this port will redirect to https port
port: 80
# https related config
https:
# https port for harbor, default is 443
port: 443
# The path of cert and key files for nginx
certificate: /usr/local/harbor/cret/192.168.1.11.crt #这里修改为自己ssl证书存放位置
private_key: /usr/local/harbor/cret/192.168.1.11.key #这里修改为自己ssl证书存放位置
# # Uncomment following will enable tls communication between all harbor components
# internal_tls:
# # set enabled to true means internal tls is enabled
# enabled: true
# # put your cert and key files on dir
# dir: /etc/harbor/tls/internal
# Uncomment external_url if you want to enable external proxy
# And when it enabled the hostname will no longer used
# external_url: https://reg.mydomain.com:8433
# The initial password of Harbor admin
# It only works in first time to install harbor
# Remember Change the admin password from UI after launching Harbor.
harbor_admin_password: Harbor12345 #这里是admin账户的初始密码,这里可以做修改
# Harbor DB configuration
database:
# The password for the root user of Harbor DB. Change this before any production use.
password: root123
# The maximum number of connections in the idle connection pool. If it <=0, no idle connections are retained.
max_idle_conns: 50
# The maximum number of open connections to the database. If it <= 0, then there is no limit on the number of open connections.
# Note: the default number of connections is 1024 for postgres of harbor.
max_open_conns: 1000
# The default data volume
data_volume: /data #这里是持久化数据的挂载点
# Harbor Storage settings by default is using /data dir on local filesystem
# Uncomment storage_service setting If you want to using external storage
# storage_service:
# # ca_bundle is the path to the custom root ca certificate, which will be injected into the truststore
# # of registry's and chart repository's containers. This is usually needed when the user hosts a internal storage with self signed certificate.
# ca_bundle:
# # storage backend, default is filesystem, options include filesystem, azure, gcs, s3, swift and oss
# # for more info about this configuration please refer https://docs.docker.com/registry/configuration/
# filesystem:
# maxthreads: 100
# # set disable to true when you want to disable registry redirect
# redirect:
# disabled: false
# Clair configuration
clair:
# The interval of clair updaters, the unit is hour, set to 0 to disable the updaters.
updaters_interval: 12
# Trivy configuration
#
# Trivy DB contains vulnerability information from NVD, Red Hat, and many other upstream vulnerability databases.
# It is downloaded by Trivy from the GitHub release page https://github.com/aquasecurity/trivy-db/releases and cached
# in the local file system. In addition, the database contains the update timestamp so Trivy can detect whether it
# should download a newer version from the Internet or use the cached one. Currently, the database is updated every
# 12 hours and published as a new release to GitHub.
trivy:
# ignoreUnfixed The flag to display only fixed vulnerabilities
ignore_unfixed: false
# skipUpdate The flag to enable or disable Trivy DB downloads from GitHub
#
# You might want to enable this flag in test or CI/CD environments to avoid GitHub rate limiting issues.
# If the flag is enabled you have to download the `trivy-offline.tar.gz` archive manually, extract `trivy.db` and
# `metadata.json` files and mount them in the `/home/scanner/.cache/trivy/db` path.
skip_update: false
#
# insecure The flag to skip verifying registry certificate
insecure: false
# github_token The GitHub access token to download Trivy DB
#
# Anonymous downloads from GitHub are subject to the limit of 60 requests per hour. Normally such rate limit is enough
# for production operations. If, for any reason, it's not enough, you could increase the rate limit to 5000
# requests per hour by specifying the GitHub access token. For more details on GitHub rate limiting please consult
# https://developer.github.com/v3/#rate-limiting
#
# You can create a GitHub token by following the instructions in
# https://help.github.com/en/github/authenticating-to-github/creating-a-personal-access-token-for-the-command-line
#
# github_token: xxx
jobservice:
# Maximum number of job workers in job service
max_job_workers: 10
notification:
# Maximum retry count for webhook job
webhook_job_max_retry: 10
chart:
# Change the value of absolute_url to enabled can enable absolute url in chart
absolute_url: disabled
# Log configurations
log:
# options are debug, info, warning, error, fatal
level: info
# configs for logs in local storage
local:
# Log files are rotated log_rotate_count times before being removed. If count is 0, old versions are removed rather than rotated.
rotate_count: 50
# Log files are rotated only if they grow bigger than log_rotate_size bytes. If size is followed by k, the size is assumed to be in kilobytes.
# If the M is used, the size is in megabytes, and if G is used, the size is in gigabytes. So size 100, size 100k, size 100M and size 100G
# are all valid.
rotate_size: 200M
# The directory on your host that store log
location: /var/log/harbor
# Uncomment following lines to enable external syslog endpoint.
# external_endpoint:
# # protocol used to transmit log to external endpoint, options is tcp or udp
# protocol: tcp
# # The host of external endpoint
# host: localhost
# # Port of external endpoint
# port: 5140
#This attribute is for migrator to detect the version of the .cfg file, DO NOT MODIFY!
_version: 2.0.0
# Uncomment external_database if using external database.
# external_database:
# harbor:
# host: harbor_db_host
# port: harbor_db_port
# db_name: harbor_db_name
# username: harbor_db_username
# password: harbor_db_password
# ssl_mode: disable
# max_idle_conns: 2
# max_open_conns: 0
# clair:
# host: clair_db_host
# port: clair_db_port
# db_name: clair_db_name
# username: clair_db_username
# password: clair_db_password
# ssl_mode: disable
# notary_signer:
# host: notary_signer_db_host
# port: notary_signer_db_port
# db_name: notary_signer_db_name
# username: notary_signer_db_username
# password: notary_signer_db_password
# ssl_mode: disable
# notary_server:
# host: notary_server_db_host
# port: notary_server_db_port
# db_name: notary_server_db_name
# username: notary_server_db_username
# password: notary_server_db_password
# ssl_mode: disable
# Uncomment external_redis if using external Redis server
# external_redis:
# # support redis, redis+sentinel
# # host for redis: <host_redis>:<port_redis>
# # host for redis+sentinel:
# # <host_sentinel1>:<port_sentinel1>,<host_sentinel2>:<port_sentinel2>,<host_sentinel3>:<port_sentinel3>
# host: redis:6379
# password:
# # sentinel_master_set must be set to support redis+sentinel
# #sentinel_master_set:
# # db_index 0 is for core, it's unchangeable
# registry_db_index: 1
# jobservice_db_index: 2
# chartmuseum_db_index: 3
# clair_db_index: 4
# trivy_db_index: 5
# idle_timeout_seconds: 30
# Uncomment uaa for trusting the certificate of uaa instance that is hosted via self-signed cert.
# uaa:
# ca_file: /path/to/ca
# Global proxy
# Config http proxy for components, e.g. http://my.proxy.com:3128
# Components doesn't need to connect to each others via http proxy.
# Remove component from `components` array if want disable proxy
# for it. If you want use proxy for replication, MUST enable proxy
# for core and jobservice, and set `http_proxy` and `https_proxy`.
# Add domain to the `no_proxy` field, when you want disable proxy
# for some special registry.
proxy:
http_proxy:
https_proxy:
no_proxy:
components:
- core
- jobservice
- clair
- trivy
启动harbor
我们使用的是离线安装包,直接使用./install安装部署即可
[root@localhost harbor]# ./install.sh --with-notary --with-trivy --with-chartmuseum
[Step 0]: checking if docker is installed ...
Note: docker version: 24.0.6
[Step 1]: checking docker-compose is installed ...
Note: docker-compose version: 2.22.0
[Step 2]: loading Harbor images ...
81af4c478a3f: Loading layer [==================================================>] 34.5MB/34.5MB
4fa475ef4cbd: Loading layer [==================================================>] 63.62MB/63.62MB
5eff830f23a7: Loading layer [==================================================>] 73.67MB/73.67MB
bff112a0a7df: Loading layer [==================================================>] 6.144kB/6.144kB
92d0354f8258: Loading layer [==================================================>] 2.56kB/2.56kB
5b672e0d5a7c: Loading layer [==================================================>] 2.56kB/2.56kB
0012b787c903: Loading layer [==================================================>] 2.56kB/2.56kB
c1d893c2c205: Loading layer [==================================================>] 2.56kB/2.56kB
63018bb28a47: Loading layer [==================================================>] 11.26kB/11.26kB
Loaded image: goharbor/harbor-db:v2.1.1
117a4b9c585f: Loading layer [==================================================>] 39.48MB/39.48MB
0b4acae09a15: Loading layer [==================================================>] 3.072kB/3.072kB
846d3bae53bd: Loading layer [==================================================>] 59.9kB/59.9kB
2c0ec6969a29: Loading layer [==================================================>] 61.95kB/61.95kB
Loaded image: goharbor/redis-photon:v2.1.1
7800c77b21f0: Loading layer [==================================================>] 8.46MB/8.46MB
ed90abbc3df2: Loading layer [==================================================>] 6.343MB/6.343MB
14d785d5e998: Loading layer [==================================================>] 14.43MB/14.43MB
1a60f4ccd1a7: Loading layer [==================================================>] 27.97MB/27.97MB
b198161fb35d: Loading layer [==================================================>] 22.02kB/22.02kB
7e4ed0ddff6a: Loading layer [==================================================>] 14.43MB/14.43MB
Loaded image: goharbor/notary-signer-photon:v2.1.1
48234182d466: Loading layer [==================================================>] 115.3MB/115.3MB
1a825d191bba: Loading layer [==================================================>] 12.59MB/12.59MB
582bbbec2032: Loading layer [==================================================>] 3.072kB/3.072kB
45afe505e59a: Loading layer [==================================================>] 49.15kB/49.15kB
f54e5a3cce60: Loading layer [==================================================>] 4.096kB/4.096kB
906e1b7ebbf0: Loading layer [==================================================>] 13.46MB/13.46MB
Loaded image: goharbor/clair-photon:v2.1.1
7c78c5b4e41d: Loading layer [==================================================>] 8.466MB/8.466MB
9706fb42af39: Loading layer [==================================================>] 4.096kB/4.096kB
412158a07706: Loading layer [==================================================>] 3.072kB/3.072kB
5a4149254af8: Loading layer [==================================================>] 9.427MB/9.427MB
ac618bd3efa5: Loading layer [==================================================>] 10.25MB/10.25MB
Loaded image: goharbor/clair-adapter-photon:v2.1.1
7621e4411b71: Loading layer [==================================================>] 12.24MB/12.24MB
88ebbde19b9a: Loading layer [==================================================>] 3.584kB/3.584kB
dd7f5fa0c20b: Loading layer [==================================================>] 2.56kB/2.56kB
61de20d88ce0: Loading layer [==================================================>] 53.05MB/53.05MB
7d03bb69f5c1: Loading layer [==================================================>] 5.632kB/5.632kB
99b674e86288: Loading layer [==================================================>] 60.42kB/60.42kB
421951bf6edd: Loading layer [==================================================>] 11.78kB/11.78kB
f0ce9f0cf59d: Loading layer [==================================================>] 53.87MB/53.87MB
adb52dc1f963: Loading layer [==================================================>] 2.56kB/2.56kB
Loaded image: goharbor/harbor-core:v2.1.1
9b74f5ada1af: Loading layer [==================================================>] 10.31MB/10.31MB
e48bb7f757c7: Loading layer [==================================================>] 8.986MB/8.986MB
9b9758ae081f: Loading layer [==================================================>] 173.6kB/173.6kB
072402c85f81: Loading layer [==================================================>] 152.6kB/152.6kB
6900a5d9558b: Loading layer [==================================================>] 67.07kB/67.07kB
4a5c5d9b23fc: Loading layer [==================================================>] 17.41kB/17.41kB
08c7bfa040bb: Loading layer [==================================================>] 15.36kB/15.36kB
Loaded image: goharbor/harbor-portal:v2.1.1
3f036012790d: Loading layer [==================================================>] 74.74MB/74.74MB
6486b9b0bea4: Loading layer [==================================================>] 3.584kB/3.584kB
fcb4207cbe8b: Loading layer [==================================================>] 3.072kB/3.072kB
f80a573a5b31: Loading layer [==================================================>] 2.56kB/2.56kB
7297e3f9a0b8: Loading layer [==================================================>] 3.072kB/3.072kB
ec743a12422d: Loading layer [==================================================>] 3.584kB/3.584kB
06af0f6c6c0a: Loading layer [==================================================>] 12.29kB/12.29kB
3a03e3162ccb: Loading layer [==================================================>] 3.584kB/3.584kB
Loaded image: goharbor/harbor-log:v2.1.1
9b886c2b88ee: Loading layer [==================================================>] 10.31MB/10.31MB
Loaded image: goharbor/nginx-photon:v2.1.1
9557ca1fbfe7: Loading layer [==================================================>] 77.33MB/77.33MB
6fd533f8ba56: Loading layer [==================================================>] 49.89MB/49.89MB
2eb9181e5c98: Loading layer [==================================================>] 2.56kB/2.56kB
516fbf6480ef: Loading layer [==================================================>] 1.536kB/1.536kB
67687e526277: Loading layer [==================================================>] 18.43kB/18.43kB
cf31cddf7676: Loading layer [==================================================>] 4.043MB/4.043MB
4630eb98dd7a: Loading layer [==================================================>] 266.2kB/266.2kB
Loaded image: goharbor/prepare:v2.1.1
a319c7fa9a57: Loading layer [==================================================>] 8.466MB/8.466MB
866240ea7853: Loading layer [==================================================>] 4.096kB/4.096kB
0e57611ac97f: Loading layer [==================================================>] 20.51MB/20.51MB
64b6488d8b42: Loading layer [==================================================>] 3.072kB/3.072kB
e3aa629f0e54: Loading layer [==================================================>] 25.91MB/25.91MB
e1a654cccad5: Loading layer [==================================================>] 47.24MB/47.24MB
Loaded image: goharbor/harbor-registryctl:v2.1.1
aeb529371336: Loading layer [==================================================>] 15.84MB/15.84MB
3825bcdb8937: Loading layer [==================================================>] 27.97MB/27.97MB
d35ad2e83013: Loading layer [==================================================>] 22.02kB/22.02kB
4cae6ab55745: Loading layer [==================================================>] 15.84MB/15.84MB
Loaded image: goharbor/notary-server-photon:v2.1.1
03c1cfd538b9: Loading layer [==================================================>] 9.762MB/9.762MB
bb229ed4a902: Loading layer [==================================================>] 4.096kB/4.096kB
53080b277f56: Loading layer [==================================================>] 3.072kB/3.072kB
8d0c44eee93d: Loading layer [==================================================>] 23.51MB/23.51MB
6a867e399ba9: Loading layer [==================================================>] 9.432MB/9.432MB
885cf5f9a697: Loading layer [==================================================>] 33.76MB/33.76MB
Loaded image: goharbor/trivy-adapter-photon:v2.1.1
ab97c837dabc: Loading layer [==================================================>] 12.24MB/12.24MB
2b9ed339f3e9: Loading layer [==================================================>] 3.584kB/3.584kB
136a56bdcff8: Loading layer [==================================================>] 2.56kB/2.56kB
9b73d85a3395: Loading layer [==================================================>] 62.26MB/62.26MB
97eeb1c8ba34: Loading layer [==================================================>] 63.09MB/63.09MB
Loaded image: goharbor/harbor-jobservice:v2.1.1
5ad257a201da: Loading layer [==================================================>] 8.465MB/8.465MB
8d38823b6ed8: Loading layer [==================================================>] 66.44MB/66.44MB
e177bb58e2da: Loading layer [==================================================>] 3.072kB/3.072kB
0f55ea3be23d: Loading layer [==================================================>] 4.096kB/4.096kB
2c47702c1637: Loading layer [==================================================>] 67.27MB/67.27MB
Loaded image: goharbor/chartmuseum-photon:v2.1.1
ee934b038aca: Loading layer [==================================================>] 8.466MB/8.466MB
21b5c3fb5cc2: Loading layer [==================================================>] 4.096kB/4.096kB
fb579280336a: Loading layer [==================================================>] 3.072kB/3.072kB
e5a1aa8a3f60: Loading layer [==================================================>] 20.51MB/20.51MB
37db791e93fd: Loading layer [==================================================>] 21.33MB/21.33MB
Loaded image: goharbor/registry-photon:v2.1.1
[Step 3]: preparing environment ...
[Step 4]: preparing harbor configs ...
prepare base dir is set to /usr/local/harbor
Generated configuration file: /config/portal/nginx.conf
Generated configuration file: /config/log/logrotate.conf
Generated configuration file: /config/log/rsyslog_docker.conf
Generated configuration file: /config/nginx/nginx.conf
Generated configuration file: /config/core/env
Generated configuration file: /config/core/app.conf
Generated configuration file: /config/registry/config.yml
Generated configuration file: /config/registryctl/env
Generated configuration file: /config/registryctl/config.yml
Generated configuration file: /config/db/env
Generated configuration file: /config/jobservice/env
Generated configuration file: /config/jobservice/config.yml
Generated and saved secret to file: /data/secret/keys/secretkey
Successfully called func: create_root_cert
Successfully called func: create_root_cert
Successfully called func: create_cert
Copying certs for notary signer
Copying nginx configuration file for notary
Generated configuration file: /config/nginx/conf.d/notary.upstream.conf
Generated configuration file: /config/nginx/conf.d/notary.server.conf
Generated configuration file: /config/notary/server-config.postgres.json
Generated configuration file: /config/notary/server_env
Generated and saved secret to file: /data/secret/keys/defaultalias
Generated configuration file: /config/notary/signer_env
Generated configuration file: /config/notary/signer-config.postgres.json
Generated configuration file: /config/trivy-adapter/env
Generated configuration file: /config/chartserver/env
Generated configuration file: /compose_location/docker-compose.yml
Clean up the input dir
[Step 5]: starting Harbor ...
[+] Building 0.0s (0/0) docker:default
[+] Running 17/17
✔ Network harbor_harbor Created 0.0s
✔ Network harbor_harbor-notary Created 0.0s
✔ Network harbor_notary-sig Created 0.0s
✔ Network harbor_harbor-chartmuseum Created 0.0s
✔ Container harbor-log Started 0.0s
✔ Container harbor-portal Started 0.0s
✔ Container redis Started 0.0s
✔ Container registryctl Started 0.0s
✔ Container chartmuseum Started 0.0s
✔ Container registry Started 0.0s
✔ Container harbor-db Started 0.0s
✔ Container notary-signer Started 0.0s
✔ Container trivy-adapter Started 0.0s
✔ Container harbor-core Started 0.0s
✔ Container notary-server Started 0.0s
✔ Container harbor-jobservice Started 0.0s
✔ Container nginx Started 0.0s
✔ ----Harbor has been installed and started successfully.----
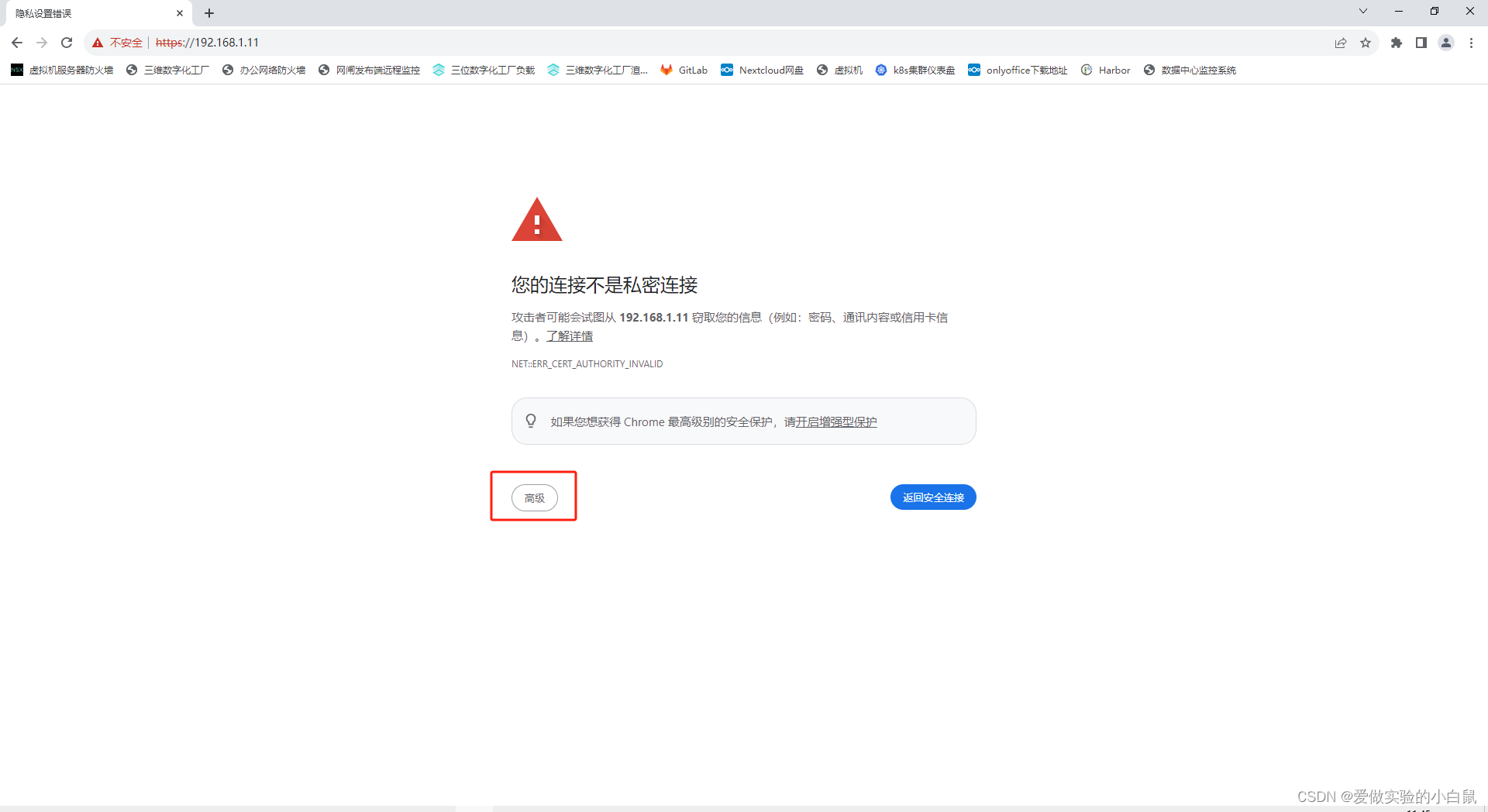
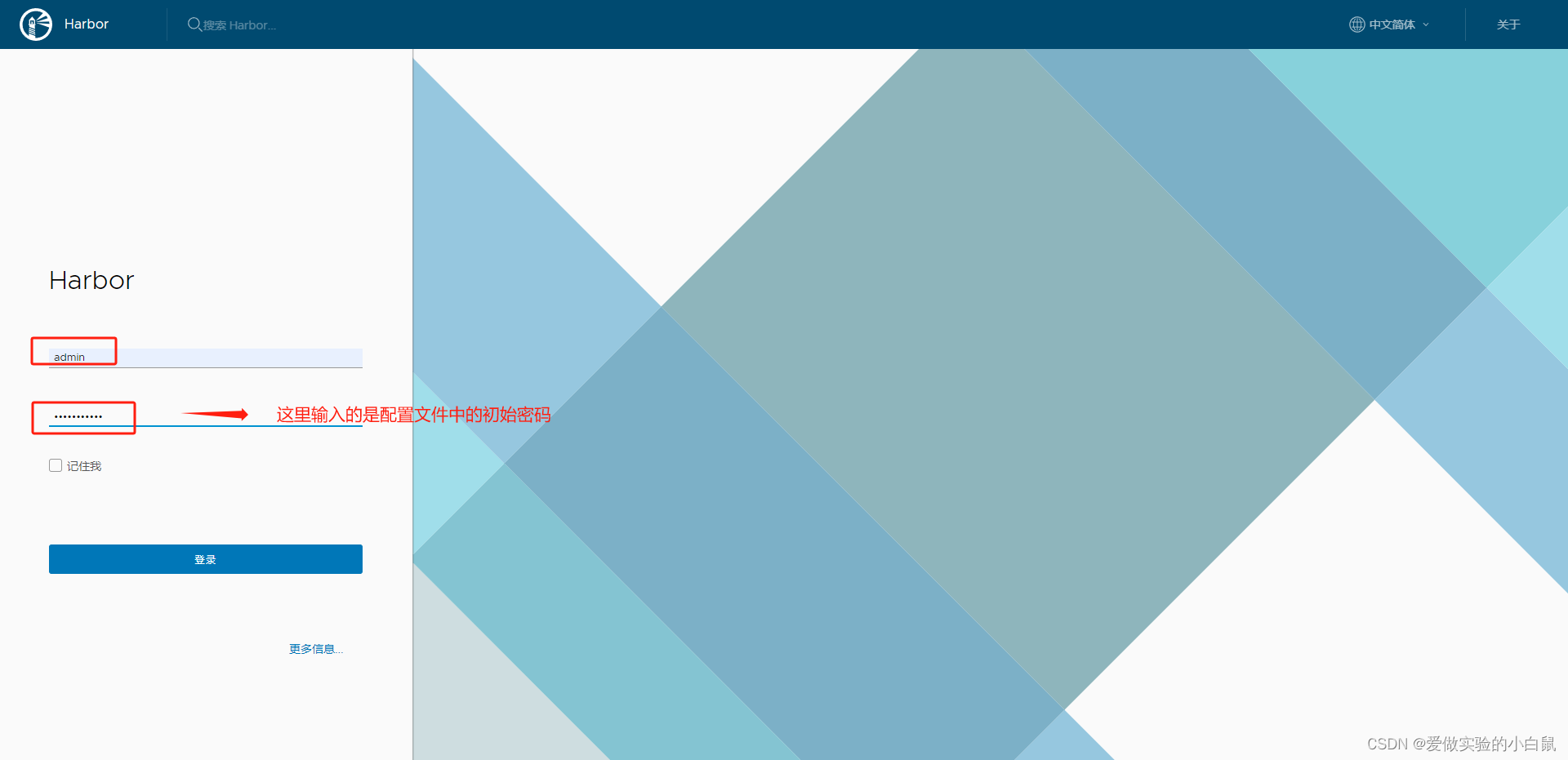
访问查看一下

上传镜像到harbor
修改docker配置文件
[root@localhost ~]# cat /usr/lib/systemd/system/docker.service
[Unit]
Description=Docker Application Container Engine
Documentation=https://docs.docker.com
After=network-online.target docker.socket firewalld.service containerd.service time-set.target
Wants=network-online.target containerd.service
Requires=docker.socket
[Service]
Type=notify
# the default is not to use systemd for cgroups because the delegate issues still
# exists and systemd currently does not support the cgroup feature set required
# for containers run by docker
ExecStart=/usr/bin/dockerd -H fd:// --containerd=/run/containerd/containerd.sock --insecure-registry=192.168.1.11 #添加harbor仓库地址
ExecReload=/bin/kill -s HUP $MAINPID
TimeoutStartSec=0
RestartSec=2
Restart=always
# Note that StartLimit* options were moved from "Service" to "Unit" in systemd 229.
# Both the old, and new location are accepted by systemd 229 and up, so using the old location
# to make them work for either version of systemd.
StartLimitBurst=3
# Note that StartLimitInterval was renamed to StartLimitIntervalSec in systemd 230.
# Both the old, and new name are accepted by systemd 230 and up, so using the old name to make
# this option work for either version of systemd.
StartLimitInterval=60s
# Having non-zero Limit*s causes performance problems due to accounting overhead
# in the kernel. We recommend using cgroups to do container-local accounting.
LimitNOFILE=infinity
LimitNPROC=infinity
LimitCORE=infinity
# Comment TasksMax if your systemd version does not support it.
# Only systemd 226 and above support this option.
TasksMax=infinity
# set delegate yes so that systemd does not reset the cgroups of docker containers
Delegate=yes
# kill only the docker process, not all processes in the cgroup
KillMode=process
OOMScoreAdjust=-500
[Install]
WantedBy=multi-user.target
重载docker
[root@localhost ~]# systemctl daemon-reload
[root@localhost ~]# systemctl restart docker
连接测试
[root@localhost ~]# docker login 192.168.1.11
Username: admin
Password:
WARNING! Your password will be stored unencrypted in /root/.docker/config.json.
Configure a credential helper to remove this warning. See
https://docs.docker.com/engine/reference/commandline/login/#credentials-store
Login Succeeded
上传镜像
[root@localhost ~]# docker tag centos 192.168.1.11/library/centos
[root@localhost ~]# docker push 192.168.1.11/library/centos
Using default tag: latest
The push refers to repository [192.168.1.11/library/centos]
74ddd0ec08fa: Pushed
latest: digest: sha256:a1801b843b1bfaf77c501e7a6d3f709401a1e0c83863037fa3aab063a7fdb9dc size: 529
查看一下
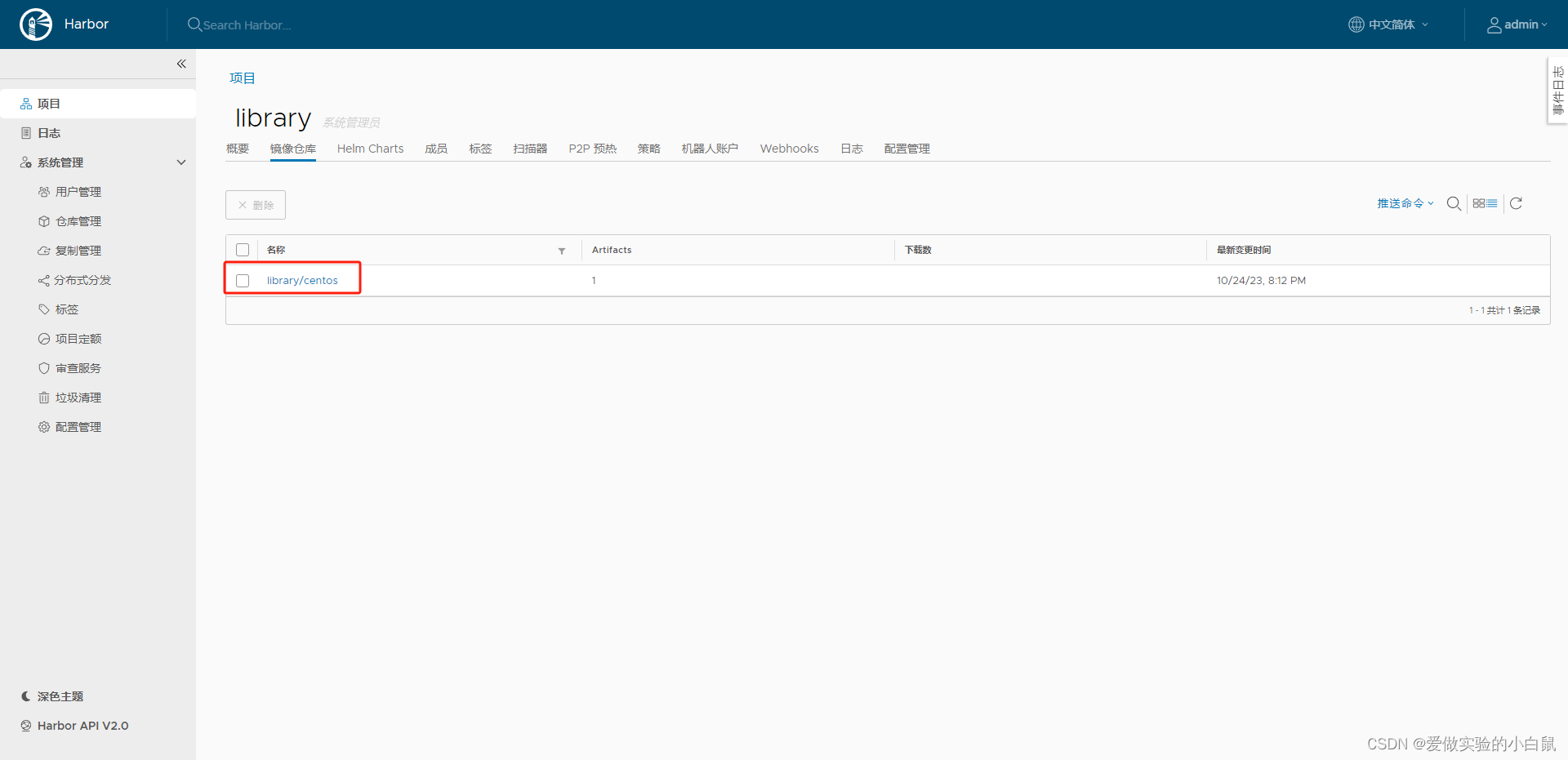
此时我们看见镜像已经上传成功了。






















 541
541











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








