题目给了三个文件:enc.py加密程序,flag加密结果,pubkey公钥文件
import sys
import Crypto.PublicKey.RSA as RSA
def enc(msg, pubkey):
(n,e) = pubkey
m = int.from_bytes(msg, byteorder = 'little') #这里涉及一个逆向知识,小端存储
c = pow(m, e, n)
ctxt = (c).to_bytes(c.bit_length() // 8 + 1, byteorder = 'little')
return ctxt
with open("pubkey.pem", "r") as f:
ciph = RSA.importKey(f.read()) # chill out, Crypto.RSA takes its sweet time... (minutes)
pubkey = (ciph.n, ciph.e) #公钥文件给了 n 和 e
with open("flag.txt", "rb") as f:
flag = f.read()
sys.stdout.buffer.write(enc(flag, pubkey))
通过分析加密代码和附件,我们可以知道,pubkey文件很大,所以要么是n非常大,要么是e非常大。
通过下面的程序可以解出公钥 n,e 来(但因为pubkey文件太大了,所以跑的时间比较长):
import Crypto.PublicKey.RSA as RSA
with open("pubkey.txt", "r") as f:
ciph = RSA.importKey(f.read()) # chill out, Crypto.RSA takes its sweet time... (minutes)
n = ciph.n
e = ciph.e
print (n)
print (e)

由结果可知,n极大,所以我们直接对c开e次方即可得到flag:
from gmpy2 import*
from libnum import*
f = open('flag','rb').read()
e = 65537
tmp = int.from_bytes(f, byteorder = 'little')
m = iroot(tmp,e)[0]
print(n2s(m))
print(n2s(m)[::-1])
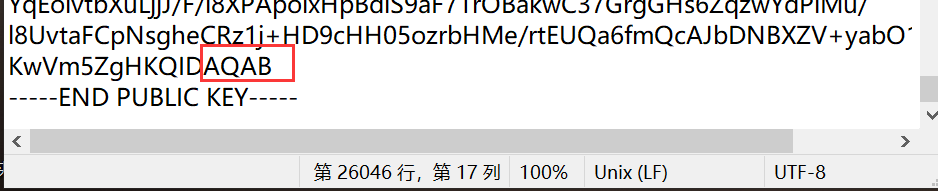
还有一种更简单的方法,就是pubkey的最后一段是存储 e 的:
from Crypto.Util.number import*
from libnum import*
import base64
s = 'KwVm5ZgHKQIDAQAB'
m = base64.b64decode(s)
m = bytes_to_long(m)
print(hex(m))
输出结果:
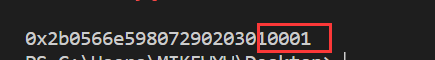
这里应该是涉及pubkey公钥格式的问题,但是我现在还没去研究这个,所以这个方法我感觉不靠谱(纯粹靠猜 )。(还是我tcl)






















 922
922











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








