题目: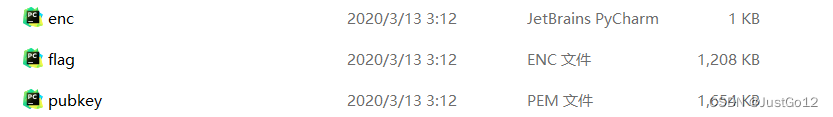
首先,审计题目,题目给了我们四个文件,打开enc文件,可看到rsa生成的数据代码:
import sys
import Crypto.PublicKey.RSA as RSA
def enc(msg, pubkey):
(n,e) = pubkey
m = int.from_bytes(msg, byteorder = 'little')
c = pow(m, e, n)
ctxt = (c).to_bytes(c.bit_length() // 8 + 1, byteorder = 'little')
return ctxt
with open("pubkey.pem", "r") as f:
ciph = RSA.importKey(f.read()) # chill out, Crypto.RSA takes its sweet time... (minutes)
pubkey = (ciph.n, ciph.e)
with open("flag.txt", "rb") as f:
flag = f.read()
sys.stdout.buffer.write(enc(flag, pubkey))
我们将pubkey提取出来,并将我们希望得到的n,e输出,结果发现e为65537,但n的位数大于(4300),所以无法输出,于是我们知道n为应该很大的值,相比于n值,e取值表较小,于是我们判断出这是一道典型的小明文爆破问题:(数值较大,运行需要12min左右)
from Crypto.Util.number import *
from Crypto.PublicKey import RSA
n=0;e=0
with open("flag.enc", "rb") as f:
flag =f.read()
print(flag)
c = int.from_bytes(flag, byteorder = 'little')
pubkey=()
with open ('pubkey.pem','r')as f:
con=RSA.importKey(f.read())
n=con.n
e=con.e
pubkey = (con.n, con.e)
import gmpy2
print(long_to_bytes(gmpy2.iroot(c,e)[0]))
得到:
b'}f00Rp_3RutUf!{ftcp'我们发现这就是我们所需的flag倒叙输出:
a='}f00Rp_3RutUf!{ftcp'
print(a[::-1])最终:pctf{!fUtuR3_pR00f}






















 930
930











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








