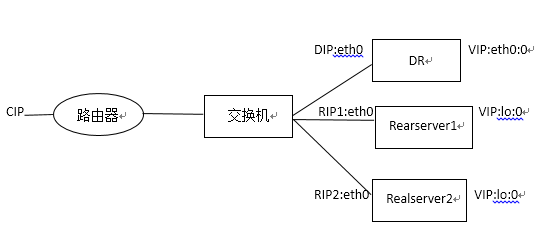
LB集群(LVS)-DR模式
实验目标:
掌握DR模式的理论和配置
实验理论:
由于NAT模式的缺点,所以引出了DR模式
DR(调度器):接收来自客户端的请求,然后通过算法把请求转发给Realserver1、2,Realserver接收到请求后,不会把信息发给DR,而是会把信息直接发给客户端
为什么要配置VIP:
为什么要配置arp_ignore
为什么要配置arp_announce
DR模式特性:
1.Realserver必须与DR在同一个网络
2.Realserver不需要是一个私有的IP地址,
3.Realserver不需要使用DR作为默认网关
4.相对与NAT模式来说,能支持更多的Realserver
内核相应级别:
Arp_ignore 定义接收到ARP请求时的相应级别
0:只要本地配置的有相应地址,就给予相应;
1:仅在请求的目标地址配置请求到达的接口上时,才给予相应;
Arp_announce 定义自己地址向外通告时的通告级别
0:将本地任何接口上的任何地址向外通告;
1:尽可能避免,试图仅向目标网络通告与其网络匹配的地址;
2:仅向与本地接口上地址匹配的网络进行通告;
实验步骤:
步骤一:DR模式配置
RealServer1:
[root@localhost ~]# cat /etc/sysconfig/network-scripts/ifcfg-eth0
# Intel Corporation 82545EM GigabitEthernet Controller (Copper)
DEVICE=eth0
BOOTPROTO=none
HWADDR=00:0c:29:3b:ad:61
ONBOOT=yes
NETMASK=255.255.255.0
IPADDR=192.168.0.11
TYPE=Ethernet
[root@localhost ~]# service network restart
Shutting down interface eth0: [ OK ]
Shutting down loopback interface: [ OK ]
Bringing up loopback interface: [ OK ]
Bringing up interface eth0: [ OK ]
[root@localhost ~]# iptables -F
[root@localhost ~]# service iptables save
Saving firewall rules to/etc/sysconfig/iptables: [ OK ]
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain RH-Firewall-1-INPUT (0 references)
target prot opt source destination
[root@localhost ~]# cat /etc/yum.repos.d/boy.repo
[base]
name=Red Hat
baseurl=file:///mnt/Server
enabled=1
gpgcheck=0
[Cluster]
name=Red Hat
baseurl=file:///mnt/Cluster
enabled=1
gpgcheck=0
[root@localhost ~]# mount /dev/cdrom /mnt
mount: block device /dev/cdrom iswrite-protected, mounting read-only
[root@localhost ~]# yum -y install httpd
[root@localhost ~]# cd /var/www/html
[root@localhost html]# vim index.html
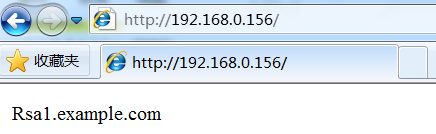
[root@localhost html]# cat index.html
Rsa1.example.com
[root@localhost ~]# service httpd restart
Stopping httpd: [FAILED]
Starting httpd: [ OK ]
[root@localhost ~]#chkconfig httpd on
[root@localhost html]# echo 1 > /proc/sys/net/ipv4/conf/lo/arp_ignore
[root@localhost html]# echo 2 >/proc/sys/net/ipv4/conf/lo/arp_announce
[root@localhost html]# echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
[root@localhost html]# echo 2 > /proc/sys/net/ipv4/conf/all/arp_announce
[root@localhost html]# ifconfig lo:0 192.168.0.156 netmask 255.255.255.255 broadcast 192.168.0.156 up
[root@localhost html]# ifconfig
eth0 Link encap:Ethernet HWaddr00:0C:29:3B:AD:61
inet addr:192.168.0.11 Bcast:192.168.0.255 Mask:255.255.255.0
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
lo:0 Link encap:LocalLoopback
inetaddr:192.168.0.156 Mask:255.255.255.255
UP LOOPBACK RUNNING MTU:16436 Metric:1
[root@localhost html]# route add -host 192.168.0.156 dev lo:0
[root@localhost html]# route
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.0.156 * 255.255.255.255 UH 0 0 0 lo
192.168.0.0 * 255.255.255.0 U 0 0 0 eth0
169.254.0.0 * 255.255.0.0 U 0 0 0 eth0
RealServer2:
[root@localhost ~]# cat /etc/sysconfig/network-scripts/ifcfg-eth0
# Advanced Micro Devices [AMD] 79c970[PCnet32 LANCE]
DEVICE=eth0
BOOTPROTO=none
ONBOOT=yes
HWADDR=00:0c:29:24:af:9b
NETMASK=255.255.255.0
IPADDR=192.168.0.12
TYPE=Ethernet
[root@localhost ~]# service network restart
正在关闭接口 eth0: [确定]
关闭环回接口: [确定]
弹出环回接口: [确定]
弹出界面 eth0: [确定]
[root@localhost ~]# iptables -F
[root@localhost ~]# service iptables save
将当前规则保存到 /etc/sysconfig/iptables: [确定]
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain RH-Firewall-1-INPUT (0 references)
target prot opt source destination
[root@localhost ~]# cat /etc/yum.repos.d/boy.repo
[base]
name=Red Hat
baseurl=file:///mnt/Server
enabled=1
gpgcheck=0
[Cluster]
name=Red Hat
baseurl=file:///mnt/Cluster
enabled=1
gpgcheck=0
[root@localhost ~]# mount /dev/cdrom /mnt
mount: block device /dev/cdrom iswrite-protected, mounting read-only
[root@localhost ~]# yum -y install httpd
[root@localhost ~]# cd /var/www/html
[root@localhost html]# vim index.html
[root@localhost html]# cat index.html
Rsa2.example.com
[root@localhost html]# service httpd restart
停止 httpd: [失败]
启动 httpd:
[root@localhost html]# echo 1 > /proc/sys/net/ipv4/conf/lo/arp_ignore
[root@localhost html]# echo 2 >/proc/sys/net/ipv4/conf/lo/arp_announce
[root@localhost html]# echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
[root@localhost html]# echo 2 > /proc/sys/net/ipv4/conf/all/arp_announce
[root@localhost html]# ifconfig lo:0 192.168.0.156 netmask 255.255.255.255 broadcast 192.168.0.156 up
[root@localhost html]# ifconfig
eth0 Link encap:Ethernet HWaddr00:0C:29:24:AF:9B
inet addr:192.168.0.12 Bcast:192.168.0.255 Mask:255.255.255.0
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
lo:0 Link encap:LocalLoopback
inet addr:192.168.0.156 Mask:255.255.255.255
UP LOOPBACK RUNNING MTU:16436 Metric:1
[root@localhost html]#route add -host 192.168.0.156 dev lo:0
[root@localhost html]# route
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.0.156 * 255.255.255.255 UH 0 0 0 lo
192.168.0.0 * 255.255.255.0 U 0 0 0 eth0
169.254.0.0 * 255.255.0.0 U 0 0 0 eth0
Director:
[root@localhost ~]# cat /etc/sysconfig/network-scripts/ifcfg-eth0
# Intel Corporation 82545EM GigabitEthernet Controller (Copper)
DEVICE=eth0
BOOTPROTO=none
HWADDR=00:0c:29:ca:37:ae
ONBOOT=yes
NETMASK=255.255.255.0
IPADDR=192.168.0.100
TYPE=Ethernet
[root@localhost ~]# service network restart
Shutting down interface eth0: [ OK ]
Shutting down loopback interface: [ OK ]
Bringing up loopback interface: [ OK ]
Bringing up interface eth0: [ OK ]
[root@localhost ~]# iptables -F
[root@localhost ~]# service iptables save
Saving firewall rules to/etc/sysconfig/iptables: [ OK ]
[root@localhost ~]# iptables -L
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain RH-Firewall-1-INPUT (0 references)
target prot opt source destination
[root@localhost ~]# ifconfig eth0:0 192.168.0.156 netmask 255.255.255.255 broadcast 192.168.0.156 up
[root@localhost ~]# ifconfig
eth0 Link encap:Ethernet HWaddr00:0C:29:CA:37:AE
inet addr:192.168.0.100 Bcast:192.168.0.255 Mask:255.255.255.0
eth0:0 Linkencap:Ethernet HWaddr00:0C:29:CA:37:AE
inetaddr:192.168.0.156 Bcast:192.168.0.156 Mask:255.255.255.255
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
[root@localhost ~]# route add -host 192.168.0.156 dev eth0:0
[root@localhost ~]# route
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
192.168.0.156 * 255.255.255.255 UH 0 0 0 eth0
192.168.0.0 * 255.255.255.0 U 0 0 0 eth0
169.254.0.0 * 255.255.0.0 U 0 0 0 eth0
[root@localhost ~]# cat /etc/yum.repos.d/boy.repo
[base]
name=Red Hat
baseurl=file:///mnt/Server
enabled=1
gpgcheck=0
[Cluster]
name=Red Hat
baseurl=file:///mnt/Cluster
enabled=1
gpgcheck=0
[root@localhost ~]# mount /dev/cdrom /mnt
mount: block device /dev/cdrom iswrite-protected, mounting read-only
[root@localhost ~]# yum -y install ipvsadm
[root@localhost ~]# ipvsadm -A -t 192.168.0.156:80 -s wlc
[root@localhost ~]# ipvsadm -a -t 192.168.0.156:80 -r 192.168.0.11 -g -w 1
[root@localhost ~]# ipvsadm -a -t 192.168.0.156:80 -r 192.168.0.12 -g -w 2
[root@localhost ~]# ipvsadm -L
IP Virtual Server version 1.2.1 (size=4096)
Prot LocalAddress:Port Scheduler Flags
->RemoteAddress:Port ForwardWeight ActiveConn InActConn
TCP 192.168.0.156:http wlc
-> 192.168.0.12:http Route 1 0 0
-> 192.168.0.11:http Route 1 0 0
[root@localhost ~]# service ipvsadm save
Saving IPVS table to/etc/sysconfig/ipvsadm: [ OK ]
[root@localhost ~]# cat /etc/sysconfig/ipvsadm
-A -t 192.168.0.156:80 -s wlc
-a -t 192.168.0.156:80 -r 192.168.0.12:80-g -w 1
-a -t 192.168.0.156:80 -r 192.168.0.11:80-g -w 1
客户端访问:
























 516
516











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








