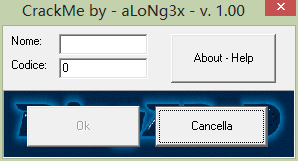
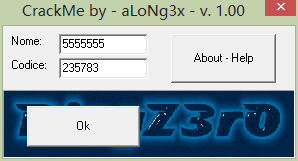
直接进入正题,有了前面几个分析Delphi程序的基础,再分析这个程序就不会没有头绪了,首先打开程序界面如下:
程序比较简单,两个输入框,三个按钮,其中一个按钮禁用,其中一个按钮有提示如下信息:
这个1.0版本的软件的目的是使 “ ok ” 和 ” Cancella “ 这两个按钮不可见,以便可以看到Ringzer0的 logo,所以你必须填入正确的代码。
如果按钮不能变得不可见,就不能完成对这个软件的破解。
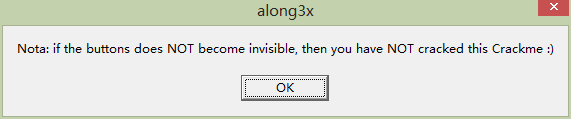
由于是Delphi程序,那么就直接打开Dark工具分析:
有几个关键的事件:密码框内容改变、用户名框内容改变、ok按钮单击、Cancella按钮单击
先来看用户名框内容改变事件:
00442E04 /. 55 push ebp ; 用户名改变函数
00442E05 |. 8BEC mov ebp,esp
00442E07 |. 6A 00 push 0x0
00442E09 |. 6A 00 push 0x0
00442E0B |. 53 push ebx
00442E0C |. 8BD8 mov ebx,eax
00442E0E |. 33C0 xor eax,eax
00442E10 |. 55 push ebp
00442E11 |. 68 9B2E4400 push aLoNg3x_.00442E9B
00442E16 |. 64:FF30 push dword ptr fs:[eax]
00442E19 |. 64:8920 mov dword ptr fs:[eax],esp
00442E1C |. 8B83 D0020000 mov eax,dword ptr ds:[ebx+0x2D0]
00442E22 |. 8078 47 00 cmp byte ptr ds:[eax+0x47],0x0 ; 右边按钮是否隐藏,0为隐
00442E26 |. 75 0F jnz short aLoNg3x_.00442E37
00442E28 |. B2 01 mov dl,0x1
00442E2A |. 8B83 CC020000 mov eax,dword ptr ds:[ebx+0x2CC] ; ok按钮的ID
00442E30 |. 8B08 mov ecx,dword ptr ds:[eax] ; aLoNg3x_.0044282C
00442E32 |. FF51 60 call dword ptr ds:[ecx+0x60] ; 激活按钮
00442E35 |. EB 49 jmp short aLoNg3x_.00442E80 ; 若隐藏了,直接激活左边按钮就返回
00442E37 |> 8D55 FC lea edx,[local.1]
00442E3A |. 8B83 E0020000 mov eax,dword ptr ds:[ebx+0x2E0]
00442E40 |. E8 7B04FEFF call aLoNg3x_.004232C0
00442E45 |. 8B45 FC mov eax,[local.1]
00442E48 |. 50 push eax
00442E49 |. 8D55 F8 lea edx,[local.2]
00442E4C |. 8B83 DC020000 mov eax,dword ptr ds:[ebx+0x2DC]
00442E52 |. E8 6904FEFF call aLoNg3x_.004232C0
00442E57 |. 8B45 F8 mov eax,[local.2] ; 输入的用户名
00442E5A |. 5A pop edx ; aLoNg3x_.0041E13E
00442E5B |. E8 DCFBFFFF call aLoNg3x_.00442A3C ; 关键call,用户名密码匹配比较
00442E60 |. 84C0 test al,al
00442E62 |. 74 0F je short aLoNg3x_.00442E73 ; 关键跳,匹配就激活,否则禁用
00442E64 |. B2 01 mov dl,0x1
00442E66 |. 8B83 CC020000 mov eax,dword ptr ds:[ebx+0x2CC]
00442E6C |. 8B08 mov ecx,dword ptr ds:[eax] ; aLoNg3x_.0044282C
00442E6E |. FF51 60 call dword ptr ds:[ecx+0x60] ; 激活按钮
00442E71 |. EB 0D jmp short aLoNg3x_.00442E80
00442E73 |> 33D2 xor edx,edx
00442E75 |. 8B83 CC020000 mov eax,dword ptr ds:[ebx+0x2CC] ; 按钮ID
00442E7B |. 8B08 mov ecx,dword ptr ds:[eax] ; aLoNg3x_.0044282C
00442E7D |. FF51 60 call dword ptr ds:[ecx+0x60] ; 禁用按钮
00442E80 |> 33C0 xor eax,eax
00442E82 |. 5A pop edx ; aLoNg3x_.0041E13E
00442E83 |. 59 pop ecx ; aLoNg3x_.0041E13E
00442E84 |. 59 pop ecx ; aLoNg3x_.0041E13E
00442E85 |. 64:8910 mov dword ptr fs:[eax],edx
00442E88 |. 68 A22E4400 push aLoNg3x_.00442EA2
00442E8D |> 8D45 F8 lea eax,[local.2]
00442E90 |. BA 02000000 mov edx,0x2
00442E95 |. E8 4209FCFF call aLoNg3x_.004037DC
00442E9A \. C3 retn
00442E9B .^ E9 D803FCFF jmp aLoNg3x_.00403278
00442EA0 .^ EB EB jmp short aLoNg3x_.00442E8D
00442EA2 . 5B pop ebx ; aLoNg3x_.0041E13E
00442EA3 . 59 pop ecx ; aLoNg3x_.0041E13E
00442EA4 . 59 pop ecx ; aLoNg3x_.0041E13E
00442EA5 . 5D pop ebp ; aLoNg3x_.0041E13E
00442EA6 . C3 retn
代码中给出了详细的注视,首先判断Cancella按钮是否是隐藏的(不要问怎么知道的,根据前面几个的Delphi软件的分析得知的),如果是就将ok按钮激活并返回,否则判断了输入的用户名和密码是否匹配(关键call里),如果匹配就激活按钮,否则禁用按钮,关键call里的代码如下:
00442A3C /$ 55 push ebp ; 关键call,两个事件都是使用的同一个 00442A3D |. 8BEC mov ebp,esp 00442A3F |. 83C4 F8 add esp,-0x8 00442A42 |. 53 push ebx 00442A43 |. 56 push esi 00442A44 |. 8955 F8 mov [local.2],edx 00442A47 |. 8945 FC mov [local.1],eax 00442A4A |. 8B45 FC mov eax,[local.1] 00442A4D |. E8 9611FCFF call aLoNg3x_.00403BE8 00442A52 |. 8B45 F8 mov eax,[local.2] ; 密码 00442A55 |. E8 8E11FCFF call aLoNg3x_.00403BE8 00442A5A |. 33C0 xor eax,eax 00442A5C |. 55 push ebp 00442A5D |. 68 E52A4400 push aLoNg3x_.00442AE5 00442A62 |. 64:FF30 push dword ptr fs:[eax] 00442A65 |. 64:8920 mov dword ptr fs:[eax],esp 00442A68 |. 8B45 FC mov eax,[local.1] ; 用户名 00442A6B |. E8 C40FFCFF call aLoNg3x_.00403A34 ; 用户名长度 00442A70 |. 83F8 05 cmp eax,0x5 ; 应该要大于5 00442A73 |. 7E 53 jle short aLoNg3x_.00442AC8 00442A75 |. 8B45 FC mov eax,[local.1] ; 用户名 00442A78 |. E8 B70FFCFF call aLoNg3x_.00403A34 ; 长度 00442A7D |. 8BD8 mov ebx,eax ; 长度 00442A7F |. 8B45 FC mov eax,[local.1] ; 用户名 00442A82 |. E8 AD0FFCFF call aLoNg3x_.00403A34 ; 长度 00442A87 |. 8BD0 mov edx,eax ; 长度 00442A89 |. 4A dec edx 00442A8A |. 85D2 test edx,edx ; 长度大于1 00442A8C |. 7E 20 jle short aLoNg3x_.00442AAE 00442A8E |. B8 01000000 mov eax,0x1 ; eax=1 00442A93 |> 8B4D FC /mov ecx,[local.1] ; 用户名 00442A96 |. 0FB64C01 FF |movzx ecx,byte ptr ds:[ecx+eax-0x1] 00442A9B |. 8B75 FC |mov esi,[local.1] ; 用户名 00442A9E |. 0FB63406 |movzx esi,byte ptr ds:[esi+eax] 00442AA2 |. 0FAFCE |imul ecx,esi 00442AA5 |. 0FAFC8 |imul ecx,eax 00442AA8 |. 03D9 |add ebx,ecx ; user32.767A78F4 00442AAA |. 40 |inc eax 00442AAB |. 4A |dec edx 00442AAC |.^ 75 E5 \jnz short aLoNg3x_.00442A93 00442AAE |> 8B45 F8 mov eax,[local.2] ; 密码 00442AB1 |. E8 BA4BFCFF call aLoNg3x_.00407670 ; 关键计算 --密码字符串转十六进制 00442AB6 |. 2BD8 sub ebx,eax 00442AB8 |. 81FB 9A020000 cmp ebx,0x29A ; 这个要相等 00442ABE |. 75 04 jnz short aLoNg3x_.00442AC4 00442AC0 |. B3 01 mov bl,0x1 00442AC2 |. EB 06 jmp short aLoNg3x_.00442ACA ; 这个要执行 00442AC4 |> 33DB xor ebx,ebx ; 这个也不能执行 00442AC6 |. EB 02 jmp short aLoNg3x_.00442ACA 00442AC8 |> 33DB xor ebx,ebx ; 这个不能执行 00442ACA |> 33C0 xor eax,eax 00442ACC |. 5A pop edx ; aLoNg3x_.00442E60 00442ACD |. 59 pop ecx ; aLoNg3x_.00442E60 00442ACE |. 59 pop ecx ; aLoNg3x_.00442E60 00442ACF |. 64:8910 mov dword ptr fs:[eax],edx 00442AD2 |. 68 EC2A4400 push aLoNg3x_.00442AEC 00442AD7 |> 8D45 F8 lea eax,[local.2] 00442ADA |. BA 02000000 mov edx,0x2 00442ADF |. E8 F80CFCFF call aLoNg3x_.004037DC 00442AE4 \. C3 retn 00442AE5 .^ E9 8E07FCFF jmp aLoNg3x_.00403278 00442AEA .^ EB EB jmp short aLoNg3x_.00442AD7 00442AEC . 8BC3 mov eax,ebx ; 要保证ebx不为0 00442AEE . 5E pop esi ; aLoNg3x_.00442E60 00442AEF . 5B pop ebx ; aLoNg3x_.00442E60 00442AF0 . 59 pop ecx ; aLoNg3x_.00442E60 00442AF1 . 59 pop ecx ; aLoNg3x_.00442E60 00442AF2 . 5D pop ebp ; aLoNg3x_.00442E60 00442AF3 . C3 retn
关键call中判断了用户名的长度要大于5,然后根据下面的一套规则计算出一个值保存在ebx中,然后ebx-密码=0x29A就可以正常激活ok按钮。这个计算规则看上面的代码就好(如用户名:221111,密码35552)。 密码框文本改变的函数和用户名框文本改变函数的内容和判断条件一样,这里就不再复述。
接下来看右边的按钮单击事件,代码如下:
00442EA8 /. 55 push ebp ; 右边按钮单击 00442EA9 |. 8BEC mov ebp,esp 00442EAB |. 6A 00 push 0x0 00442EAD |. 53 push ebx 00442EAE |. 8BD8 mov ebx,eax 00442EB0 |. 33C0 xor eax,eax 00442EB2 |. 55 push ebp 00442EB3 |. 68 322F4400 push aLoNg3x_.00442F32 00442EB8 |. 64:FF30 push dword ptr fs:[eax] 00442EBB |. 64:8920 mov dword ptr fs:[eax],esp 00442EBE |. 8D55 FC lea edx,[local.1] 00442EC1 |. 8B83 E0020000 mov eax,dword ptr ds:[ebx+0x2E0] 00442EC7 |. E8 F403FEFF call aLoNg3x_.004232C0 ; 密码长度 00442ECC |. 8B45 FC mov eax,[local.1] ; 密码 00442ECF |. E8 9C47FCFF call aLoNg3x_.00407670 00442ED4 |. 50 push eax 00442ED5 |. 8D55 FC lea edx,[local.1] 00442ED8 |. 8B83 DC020000 mov eax,dword ptr ds:[ebx+0x2DC] 00442EDE |. E8 DD03FEFF call aLoNg3x_.004232C0 00442EE3 |. 8B45 FC mov eax,[local.1] ; 用户名 00442EE6 |. 5A pop edx ; aLoNg3x_.00424640 00442EE7 |. E8 08FCFFFF call aLoNg3x_.00442AF4 ; 关键call 用户名 密码匹配检测 00442EEC |. 84C0 test al,al 00442EEE |. 74 1C je short aLoNg3x_.00442F0C ; 不能跳 00442EF0 |. 33D2 xor edx,edx 00442EF2 |. 8B83 D0020000 mov eax,dword ptr ds:[ebx+0x2D0] ; 右边按钮ID 00442EF8 |. E8 B302FEFF call aLoNg3x_.004231B0 隐藏 00442EFD |. B2 01 mov dl,0x1 00442EFF |. 8B83 CC020000 mov eax,dword ptr ds:[ebx+0x2CC] ; 左边按钮ID 00442F05 |. 8B08 mov ecx,dword ptr ds:[eax] ; aLoNg3x_.0044282C 00442F07 |. FF51 60 call dword ptr ds:[ecx+0x60] ; 激活 00442F0A |. EB 10 jmp short aLoNg3x_.00442F1C 00442F0C |> BA 482F4400 mov edx,aLoNg3x_.00442F48 ; 0 00442F11 |. 8B83 E0020000 mov eax,dword ptr ds:[ebx+0x2E0] 00442F17 |. E8 D403FEFF call aLoNg3x_.004232F0 00442F1C |> 33C0 xor eax,eax 00442F1E |. 5A pop edx ; aLoNg3x_.00424640 00442F1F |. 59 pop ecx ; aLoNg3x_.00424640 00442F20 |. 59 pop ecx ; aLoNg3x_.00424640 00442F21 |. 64:8910 mov dword ptr fs:[eax],edx 00442F24 |. 68 392F4400 push aLoNg3x_.00442F39 00442F29 |> 8D45 FC lea eax,[local.1] 00442F2C |. E8 8708FCFF call aLoNg3x_.004037B8 00442F31 \. C3 retn 00442F32 .^ E9 4103FCFF jmp aLoNg3x_.00403278 00442F37 .^ EB F0 jmp short aLoNg3x_.00442F29 00442F39 . 5B pop ebx ; aLoNg3x_.00424640 00442F3A . 59 pop ecx ; aLoNg3x_.00424640 00442F3B . 5D pop ebp ; aLoNg3x_.00424640 00442F3C . C3 retn
这段代码里同样对用户名和密码进行检测,看是否符合要求,如果符合,就隐藏右边的按钮,并且将左边按钮激活,那么主要看字符串检测的关键call ,如下:
00442AF4 /$ 55 push ebp ; 右击按钮关键call 00442AF5 |. 8BEC mov ebp,esp 00442AF7 |. 83C4 F8 add esp,-0x8 00442AFA |. 53 push ebx 00442AFB |. 56 push esi 00442AFC |. 8955 F8 mov [local.2],edx 00442AFF |. 8945 FC mov [local.1],eax 00442B02 |. 8B45 FC mov eax,[local.1] 00442B05 |. E8 DE10FCFF call aLoNg3x_.00403BE8 00442B0A |. 33C0 xor eax,eax 00442B0C |. 55 push ebp 00442B0D |. 68 902B4400 push aLoNg3x_.00442B90 00442B12 |. 64:FF30 push dword ptr fs:[eax] 00442B15 |. 64:8920 mov dword ptr fs:[eax],esp 00442B18 |. 8B45 FC mov eax,[local.1] 00442B1B |. E8 140FFCFF call aLoNg3x_.00403A34 ; 用户名长度 00442B20 |. 83F8 05 cmp eax,0x5 ; 用户名长度要大于5 00442B23 |. 7E 53 jle short aLoNg3x_.00442B78 00442B25 |. 8B45 FC mov eax,[local.1] 00442B28 |. 0FB640 04 movzx eax,byte ptr ds:[eax+0x4] ; 用户名第五个字符串ASCII码 00442B2C |. B9 07000000 mov ecx,0x7 ; ecx=7 00442B31 |. 33D2 xor edx,edx 00442B33 |. F7F1 div ecx ; eax =eax /ecx 00442B35 |. 8BC2 mov eax,edx 00442B37 |. 83C0 02 add eax,0x2 00442B3A |. E8 E1FEFFFF call aLoNg3x_.00442A20 00442B3F |. 8BF0 mov esi,eax 00442B41 |. 33DB xor ebx,ebx 00442B43 |. 8B45 FC mov eax,[local.1] ; 用户名 00442B46 |. E8 E90EFCFF call aLoNg3x_.00403A34 ; 用户名长度 00442B4B |. 85C0 test eax,eax 00442B4D |. 7E 16 jle short aLoNg3x_.00442B65 00442B4F |. BA 01000000 mov edx,0x1 00442B54 |> 8B4D FC /mov ecx,[local.1] 00442B57 |. 0FB64C11 FF |movzx ecx,byte ptr ds:[ecx+edx-0x1] 00442B5C |. 0FAFCE |imul ecx,esi 00442B5F |. 03D9 |add ebx,ecx ; user32.767A78F4 00442B61 |. 42 |inc edx 00442B62 |. 48 |dec eax 00442B63 |.^ 75 EF \jnz short aLoNg3x_.00442B54 00442B65 |> 2B5D F8 sub ebx,[local.2] ; ebx-密码 00442B68 |. 81FB 697A0000 cmp ebx,0x7A69 ; 相等 00442B6E |. 75 04 jnz short aLoNg3x_.00442B74 ; 不跳 00442B70 |. B3 01 mov bl,0x1 00442B72 |. EB 06 jmp short aLoNg3x_.00442B7A 00442B74 |> 33DB xor ebx,ebx 00442B76 |. EB 02 jmp short aLoNg3x_.00442B7A 00442B78 |> 33DB xor ebx,ebx 00442B7A |> 33C0 xor eax,eax 00442B7C |. 5A pop edx ; aLoNg3x_.00442EEC 00442B7D |. 59 pop ecx ; aLoNg3x_.00442EEC 00442B7E |. 59 pop ecx ; aLoNg3x_.00442EEC 00442B7F |. 64:8910 mov dword ptr fs:[eax],edx 00442B82 |. 68 972B4400 push aLoNg3x_.00442B97 00442B87 |> 8D45 FC lea eax,[local.1] 00442B8A |. E8 290CFCFF call aLoNg3x_.004037B8 00442B8F \. C3 retn 00442B90 .^ E9 E306FCFF jmp aLoNg3x_.00403278 00442B95 .^ EB F0 jmp short aLoNg3x_.00442B87 00442B97 . 8BC3 mov eax,ebx 00442B99 . 5E pop esi ; aLoNg3x_.00442EEC 00442B9A . 5B pop ebx ; aLoNg3x_.00442EEC 00442B9B . 59 pop ecx ; aLoNg3x_.00442EEC 00442B9C . 59 pop ecx ; aLoNg3x_.00442EEC 00442B9D . 5D pop ebp ; aLoNg3x_.00442EEC 00442B9E . C3 retn
代码的关键是在地址 442B54处的一段计算,然后将计算的结果与密码作差看是否等于0x7A69,如果是则eax返回非0,就可以实现右侧按钮单击时隐藏了,如下:
接下来应该就是单击ok按钮使其隐藏了,分析按钮的事件处理函数如下:
00442D64 /. 55 push ebp ; ok按钮单击 00442D65 |. 8BEC mov ebp,esp 00442D67 |. 6A 00 push 0x0 00442D69 |. 53 push ebx 00442D6A |. 8BD8 mov ebx,eax 00442D6C |. 33C0 xor eax,eax 00442D6E |. 55 push ebp 00442D6F |. 68 ED2D4400 push aLoNg3x_.00442DED 00442D74 |. 64:FF30 push dword ptr fs:[eax] 00442D77 |. 64:8920 mov dword ptr fs:[eax],esp 00442D7A |. 8B83 D0020000 mov eax,dword ptr ds:[ebx+0x2D0] 00442D80 |. 8078 47 01 cmp byte ptr ds:[eax+0x47],0x1 ; 判断右边按钮是否存在 00442D84 |. 75 12 jnz short aLoNg3x_.00442D98 ; 跳过 00442D86 |. BA 002E4400 mov edx,aLoNg3x_.00442E00 ; 0 00442D8B |. 8B83 E0020000 mov eax,dword ptr ds:[ebx+0x2E0] 00442D91 |. E8 5A05FEFF call aLoNg3x_.004232F0 00442D96 |. EB 3F jmp short aLoNg3x_.00442DD7 00442D98 |> 8D55 FC lea edx,[local.1] 00442D9B |. 8B83 E0020000 mov eax,dword ptr ds:[ebx+0x2E0] 00442DA1 |. E8 1A05FEFF call aLoNg3x_.004232C0 00442DA6 |. 8B45 FC mov eax,[local.1] 00442DA9 |. E8 C248FCFF call aLoNg3x_.00407670 00442DAE |. 50 push eax 00442DAF |. 8D55 FC lea edx,[local.1] 00442DB2 |. 8B83 DC020000 mov eax,dword ptr ds:[ebx+0x2DC] 00442DB8 |. E8 0305FEFF call aLoNg3x_.004232C0 00442DBD |. 8B45 FC mov eax,[local.1] ; 用户名 00442DC0 |. 5A pop edx ; aLoNg3x_.00424640 00442DC1 |. E8 DAFDFFFF call aLoNg3x_.00442BA0 ; 关键call 密码检测 00442DC6 |. 84C0 test al,al 00442DC8 |. 74 0D je short aLoNg3x_.00442DD7 ; 这里不能跳转 00442DCA |. 33D2 xor edx,edx 00442DCC |. 8B83 CC020000 mov eax,dword ptr ds:[ebx+0x2CC] 00442DD2 |. E8 D903FEFF call aLoNg3x_.004231B0 00442DD7 |> 33C0 xor eax,eax 00442DD9 |. 5A pop edx ; aLoNg3x_.00424640 00442DDA |. 59 pop ecx ; aLoNg3x_.00424640 00442DDB |. 59 pop ecx ; aLoNg3x_.00424640 00442DDC |. 64:8910 mov dword ptr fs:[eax],edx 00442DDF |. 68 F42D4400 push aLoNg3x_.00442DF4 00442DE4 |> 8D45 FC lea eax,[local.1] 00442DE7 |. E8 CC09FCFF call aLoNg3x_.004037B8 00442DEC \. C3 retn 00442DED .^ E9 8604FCFF jmp aLoNg3x_.00403278 00442DF2 .^ EB F0 jmp short aLoNg3x_.00442DE4 00442DF4 . 5B pop ebx ; aLoNg3x_.00424640 00442DF5 . 59 pop ecx ; aLoNg3x_.00424640 00442DF6 . 5D pop ebp ; aLoNg3x_.00424640 00442DF7 . C3 retn
这里的处理与上面的类似,关键在于地址442DC1处的关键call,这个call的代码如下:
00442BA0 /$ 55 push ebp ; 用户名检测 密码检测 -- ok按钮单击 00442BA1 |. 8BEC mov ebp,esp 00442BA3 |. 6A 00 push 0x0 00442BA5 |. 6A 00 push 0x0 00442BA7 |. 6A 00 push 0x0 00442BA9 |. 53 push ebx 00442BAA |. 56 push esi 00442BAB |. 8BF2 mov esi,edx 00442BAD |. 8945 FC mov [local.1],eax 00442BB0 |. 8B45 FC mov eax,[local.1] 00442BB3 |. E8 3010FCFF call aLoNg3x_.00403BE8 00442BB8 |. 33C0 xor eax,eax 00442BBA |. 55 push ebp 00442BBB |. 68 672C4400 push aLoNg3x_.00442C67 00442BC0 |. 64:FF30 push dword ptr fs:[eax] 00442BC3 |. 64:8920 mov dword ptr fs:[eax],esp 00442BC6 |. 33DB xor ebx,ebx 00442BC8 |. 8D55 F8 lea edx,[local.2] 00442BCB |. 8BC6 mov eax,esi 00442BCD |. E8 6E4AFCFF call aLoNg3x_.00407640 00442BD2 |. 8D45 F4 lea eax,[local.3] 00442BD5 |. 8B55 F8 mov edx,[local.2] ; 密码 00442BD8 |. E8 730CFCFF call aLoNg3x_.00403850 00442BDD |. 8B45 F8 mov eax,[local.2] ; 密码 00442BE0 |. E8 4F0EFCFF call aLoNg3x_.00403A34 ; 密码长度 00442BE5 |. 83F8 05 cmp eax,0x5 00442BE8 |. 7E 60 jle short aLoNg3x_.00442C4A ; 不能跳 00442BEA |. 8B45 F8 mov eax,[local.2] 00442BED |. E8 420EFCFF call aLoNg3x_.00403A34 00442BF2 |. 8BF0 mov esi,eax 00442BF4 |. 83FE 01 cmp esi,0x1 00442BF7 |. 7C 2F jl short aLoNg3x_.00442C28 00442BF9 |> 8D45 F4 /lea eax,[local.3] 00442BFC |. E8 0310FCFF |call aLoNg3x_.00403C04 00442C01 |. 8D4430 FF |lea eax,dword ptr ds:[eax+esi-0x1] 00442C05 |. 50 |push eax 00442C06 |. 8B45 F8 |mov eax,[local.2] 00442C09 |. 0FB64430 FF |movzx eax,byte ptr ds:[eax+esi-0x1] 00442C0E |. F7E8 |imul eax 00442C10 |. 0FBFC0 |movsx eax,ax 00442C13 |. F7EE |imul esi 00442C15 |. B9 19000000 |mov ecx,0x19 00442C1A |. 99 |cdq 00442C1B |. F7F9 |idiv ecx 00442C1D |. 83C2 41 |add edx,0x41 00442C20 |. 58 |pop eax 00442C21 |. 8810 |mov byte ptr ds:[eax],dl 00442C23 |. 4E |dec esi 00442C24 |. 85F6 |test esi,esi 00442C26 |.^ 75 D1 \jnz short aLoNg3x_.00442BF9 00442C28 |> 8B45 F4 mov eax,[local.3] ; 一个变化的字符串 00442C2B |. 8B55 FC mov edx,[local.1] ; 用户名 00442C2E |. E8 110FFCFF call aLoNg3x_.00403B44 00442C33 |. 75 17 jnz short aLoNg3x_.00442C4C 00442C35 |. 8B45 FC mov eax,[local.1] 00442C38 |. 8B55 F4 mov edx,[local.3] 00442C3B |. E8 040FFCFF call aLoNg3x_.00403B44 ; 关键call 00442C40 |. 75 04 jnz short aLoNg3x_.00442C46 ; 不能跳 00442C42 |. B3 01 mov bl,0x1 00442C44 |. EB 06 jmp short aLoNg3x_.00442C4C ; 跳 00442C46 |> 33DB xor ebx,ebx 00442C48 |. EB 02 jmp short aLoNg3x_.00442C4C 00442C4A |> 33DB xor ebx,ebx 00442C4C |> 33C0 xor eax,eax 00442C4E |. 5A pop edx 00442C4F |. 59 pop ecx 00442C50 |. 59 pop ecx 00442C51 |. 64:8910 mov dword ptr fs:[eax],edx 00442C54 |. 68 6E2C4400 push aLoNg3x_.00442C6E 00442C59 |> 8D45 F4 lea eax,[local.3] 00442C5C |. BA 03000000 mov edx,0x3 00442C61 |. E8 760BFCFF call aLoNg3x_.004037DC 00442C66 \. C3 retn 00442C67 .^ E9 0C06FCFF jmp aLoNg3x_.00403278 00442C6C .^ EB EB jmp short aLoNg3x_.00442C59 00442C6E . 8BC3 mov eax,ebx 00442C70 . 5E pop esi 00442C71 . 5B pop ebx 00442C72 . 8BE5 mov esp,ebp 00442C74 . 5D pop ebp 00442C75 . C3 retn
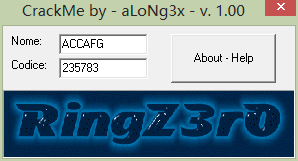
从这个代码里可以看到,在后面有一个和某个字符串对比的call,如果用户名是这个字符串就可以通过了,而这个字符串是上面的循环中根据密码字符串计算得到,因此只要输入的用户名和密码对应就可以计算出来。注册后的效果如下:
破解总结如下:
1、先输入一段用户名与密码,点击右侧的按钮,即可以使右侧的按钮消失,并且左侧的按钮激活,用 户名和密码的匹配规则在代码中有,就是按钮事件里的关键call里,不难。(如输入 5555555与 235783)。
2、输入一段用户名与密码,点击左侧的按钮即可以使左侧的按钮消失,破解成功,代码中先根据输入的密码计算得到一个字符串,再与用户名比较(计算的过程见代码,不难),如果一致则成功(如输入ACCAFG 与 235783)






















 1042
1042

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








