1.常用命令

##我们首先需要找两台主机,因为我们这块没有两台主机,只能用rhel7.6和没有装图形的rhel8.1作为两台主机进行试验操作:
##我们将rhel8.1作为操作机,将rhel7.6作为服务机(被操作机)

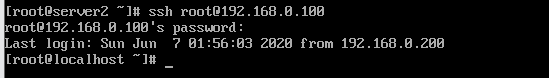
##我们先在rhel8.1上连接7.6的IPssh root@198.168.0.100,以root的身份连接,
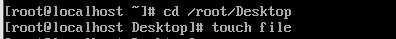
##我们进入被操作机的桌面创建个file

##可以看到rhel7.6中的桌面上已经创建好了file

##我们尝试用操作机打开被操作机的firefox,发现不能打开不存在图形连接,因此我们需要在前面连接的命令前加上-X 变成 ssh -X root@192.168.0.100,
然后我们再输入 firefox让他运行firefox,发现这个操作机上firefox运行了,但是我们查看任务管理器看不到他的进程,在rhel7.6(被操作机上发现了他的进程),我们切断(被操作机的)firefox发现操作机上的firefox页面已经被关闭了
2.密钥和密码认证
[root@localhost ~]# ssh-keygen##密钥的生成命令
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):##密钥保存的位置,我们按回车采用默认的
Enter passphrase (empty for no passphrase):##我们只要密钥认证不要密码认证按回车就行,想要密码必须输入大于4位的密码
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa.##生成的密钥就在id_rsa,
Your public key has been saved in /root/.ssh/id_rsa.pub.##通过这个文件生成公钥文件
The key fingerprint is:
SHA256:eXbRDOKKbmJuQYpNPscyDGJvjGAu1etWUyapfknwUz4 root@localhost.localdomain
The key's randomart image is:
+---[RSA 2048]----+
| . . |
| . . + |
| . . . . o |
|+oo + o.+o . |
|*O++ =.*S o . |
|ooO+*.* Eo . |
|. .Bo+o+ . |
| o=oo |
| o.. |
+----[SHA256]-----+
[root@localhost ~]# cd /root/.ssh/
[root@localhost .ssh]# ls##id rsa为私钥,谁要登录就给别人这个, id_ras.oub这个是锁头加密的,公钥的模板
id_rsa id_rsa.pub known_hosts
[root@localhost .ssh]# ssh-copy-id -i id_rsa.pub root@192.168.0.100##公钥上传到服务器,也就是本机上。锁定的用户为root
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "id_rsa.pub"
The authenticity of host '192.168.0.100 (192.168.0.100)' can't be established.
ECDSA key fingerprint is SHA256:gbwiJQP7FDiJiHRaHZrgjCnV9ZtogjioIBTP8KBLRLg.
ECDSA key fingerprint is MD5:85:5a:df:28:c7:2c:41:3e:73:1b:43:6d:5b:a0:57:08.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@192.168.0.100's password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh 'root@192.168.0.100'"
and check to make sure that only the key(s) you wanted were added.
[root@localhost .ssh]# ls##这个就是真正的ssh的公钥,并且承认可以用私钥id_rsa把这个公钥打开
authorized_keys id_rsa id_rsa.pub known_hosts
[root@localhost .ssh]# cat authorized_keys ##可以看到公钥的模板和公钥内容是一致的
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDC6NFY9o78IVMpTHkQg+3Vwd6gb0de1nxKs9HgUuAHTqIwPXPrYvRWViUnG+uEf0KwB5HDC8b7YMyISwPWr1NmBmJtkwTC4WwhTE0ir1v/p1kwSPr0OrSEXjpkE73WIlbT93vEZYEUmKdzIVfaiyxa/xQJNfo++2XjaNrajSjWD/BZyixjFSO88WDb2eukukVsFUBQQoTW1hIfFUNOyF5+Oi1rA9LYGH5JLnnRcL2C0u15m4gntHVfvLtaBdeOGJg2qpRYTarQhsrTRellxMRvD83WN878Jw1TnEItnaWIzzhx3jNpCGwT6CdKA35si+b2W/IZ6FEBqM8ZfCUtk9JB root@localhost.localdomain
[root@localhost .ssh]# cat id_rsa.pub
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDC6NFY9o78IVMpTHkQg+3Vwd6gb0de1nxKs9HgUuAHTqIwPXPrYvRWViUnG+uEf0KwB5HDC8b7YMyISwPWr1NmBmJtkwTC4WwhTE0ir1v/p1kwSPr0OrSEXjpkE73WIlbT93vEZYEUmKdzIVfaiyxa/xQJNfo++2XjaNrajSjWD/BZyixjFSO88WDb2eukukVsFUBQQoTW1hIfFUNOyF5+Oi1rA9LYGH5JLnnRcL2C0u15m4gntHVfvLtaBdeOGJg2qpRYTarQhsrTRellxMRvD83WN878Jw1TnEItnaWIzzhx3jNpCGwT6CdKA35si+b2W/IZ6FEBqM8ZfCUtk9JB root@localhost.localdomain
##这样我们这台设备的加密已经做好了,一个是生成密钥,一个是上传密钥
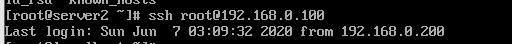
##我们在用rehl8.1作为控制机控制rhel7.6,我们刚刚对7.6的ssh密钥加密了
##但是为何还是采用密码的方式进行验证
[root@localhost .ssh]# vim /etc/ssh/sshd_config##我们在这个文件的65行对将他的yes改为no
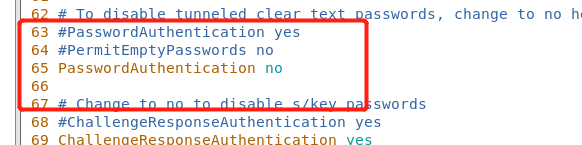
##这里下面的69行的yes也需要改为no
[root@localhost .ssh]# systemctl restart sshd.service##重新启动下sshd
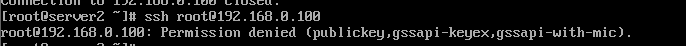
##我们再次想进入rhel7.6发现被拒绝了,这就需要我们将私钥给rhel8.1才行
[root@localhost .ssh]# scp /root/.ssh/id_rsa root@192.168.0.200:/root/.ssh/
root@192.168.0.200's password:
id_rsa 100% 1675 89.3KB/s 00:00
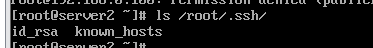
##私钥已经给rhel8.1了 ,用rhel8.1可以看到私钥
##已经可以成功连接rhel7.6了
[root@localhost .ssh]# mv authorized_keys authorized_keys.backup##我们现在将公钥修改,备份成。backup,但是rhel8.1依然有私钥的情况下依然不可以登录,这样就达到了,我随时让谁登录,就可以让谁登,不想让谁登,就不让谁登,大大提高了系统的安全性

##也可以采用非交互的方法:
我们先删除前面生成的ssh的文件
[root@localhost .ssh]# rm -fr /root/.ssh/*
[root@localhost .ssh]# ssh-keygen --help##查看ssh-keygen的帮助
unknown option -- -
usage: ssh-keygen [-q] [-b bits] [-t dsa | ecdsa | ed25519 | rsa | rsa1]
[-N new_passphrase] [-C comment] [-f output_keyfile]
ssh-keygen -p [-P old_passphrase] [-N new_passphrase] [







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 2649
2649











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








